David Routin retweetledi

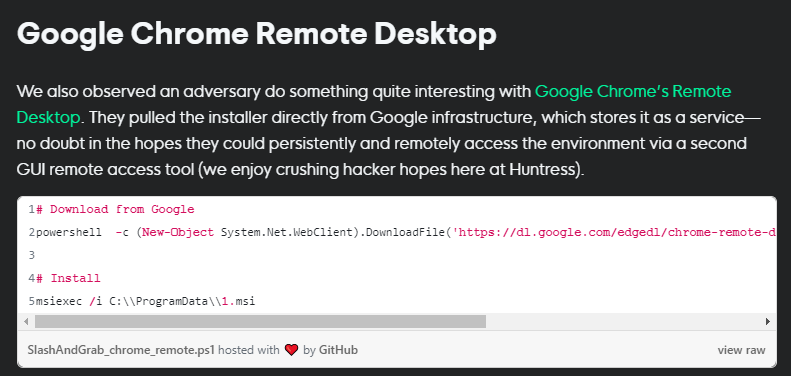
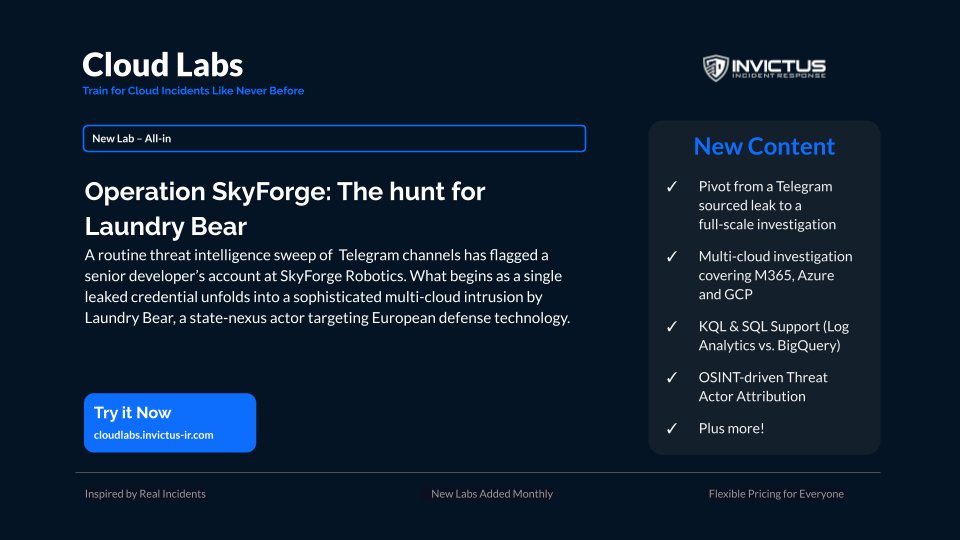
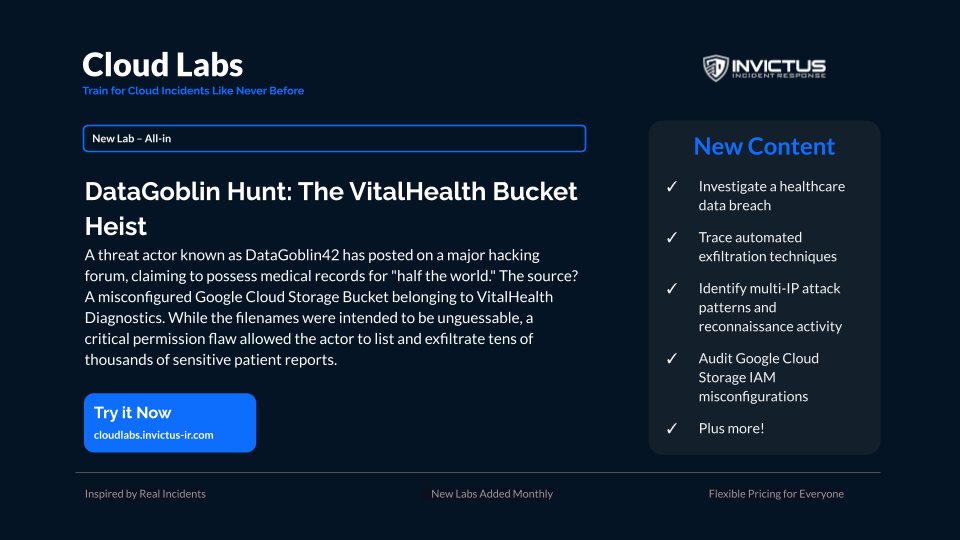
🚀 Introducing 𝐀𝐥𝐥-𝐈𝐧 access for Cloud Labs
Most cloud security training happens in a vacuum. Real-world attacks don't.
We are incredibly excited to announce the launch of our All-in level for Cloud Labs. Here is what makes this scenario unique:
🌐 Cross-Cloud Attacks: You will trace sophisticated threats that pivot across different cloud environments, mimicking the true complexity of modern, multi-layered breaches.
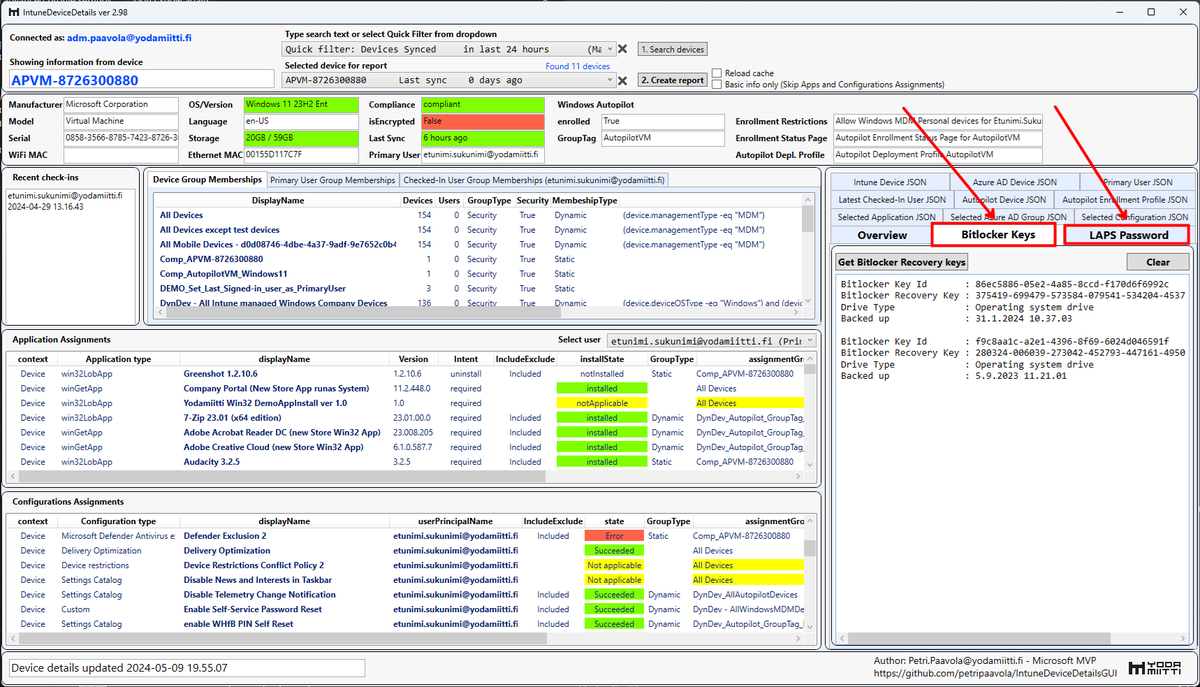
🛠️ Live Environment Access: You get real, hands-on access to investigate active threat scenarios directly within live Google Workspace and Google Cloud environments.
It is time to test your cloud incident response skills for real!
#stayInvictus #CloudIncidentResponse #CloudLabs
English