Marcus Holloway
616 posts


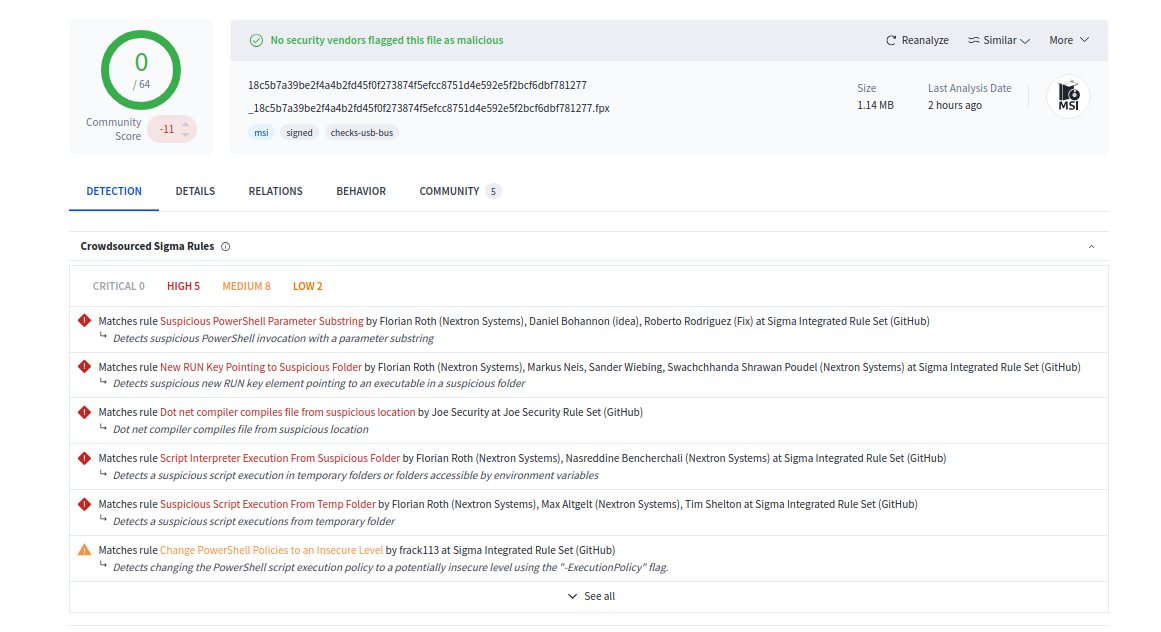
The DFIR Report recently observed MEOWBACKCONN again in the wild: ➡️ Initial Access: Malicious Microsoft Teams MSI Installer ➡️ Execution: Encrypted PowerShell backdoor ➡️ Discovery: PowerShell Cmdlets, WMI, and whoami ➡️ Credential Access: SAM Registry Dump ➡️ Exfil: Curl to temp[.]sh ➡️ Lateral Movement: SOCKS proxy dropped to enable RDP 🐱 MEOWBACKCONN dropped on domain controllers The last time we observed this malware was from a GOOTLOADER case in Nov 2025.










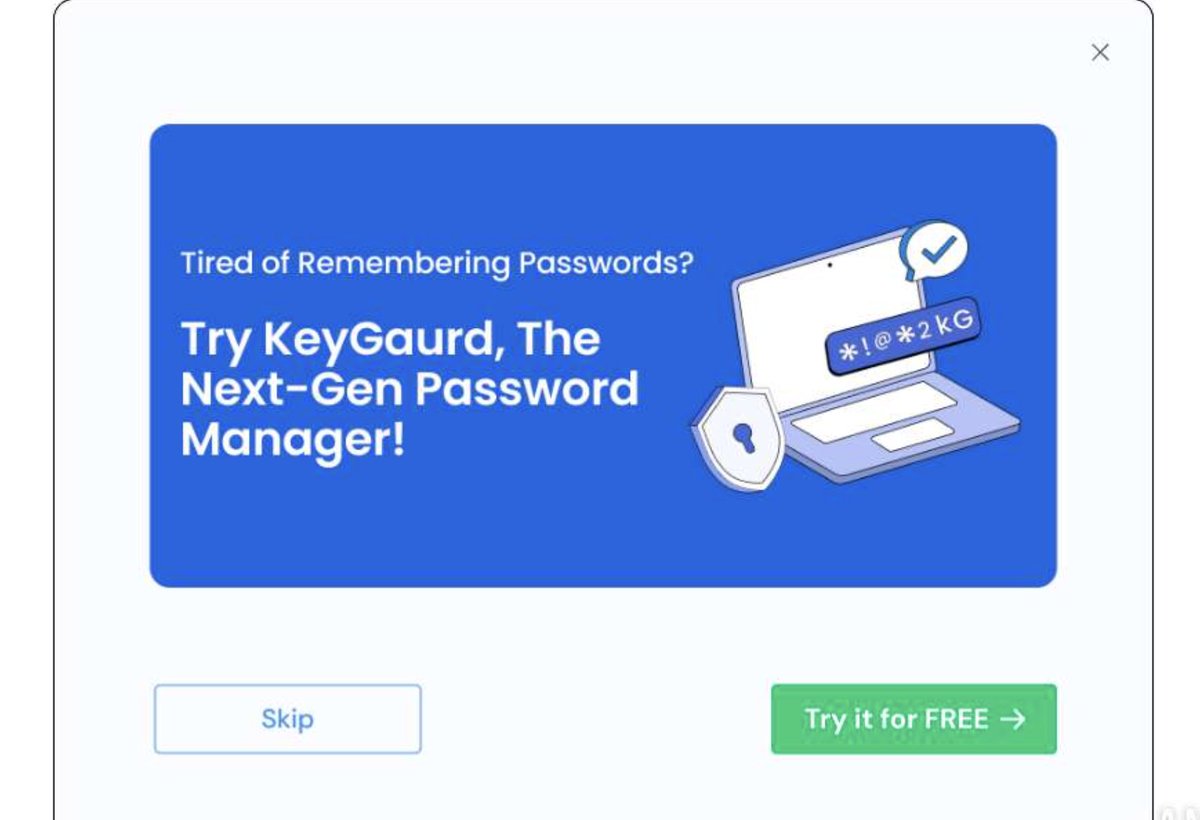
Fake PDF software recommended KeyGuard password manager, Per SecurityAnnex (@tuckner ), the password manager encrypts with the key "secret key 123". SecurityAnnex made this really easy to investigate. Please don't use free PDF software. 🧵

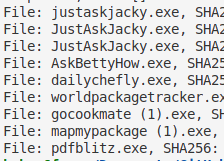

🔍New Blog: JustAskJacky -- AI brings back classical trojan horse malware 🔗gdatasoftware.com/blog/2025/08/3… #GDATA @GDATA #GDATATechblog