


TCM Security
7.3K posts


@TCMSecurity
Come learn to hack at TCM Security Academy! Veteran owned. Quality results.






















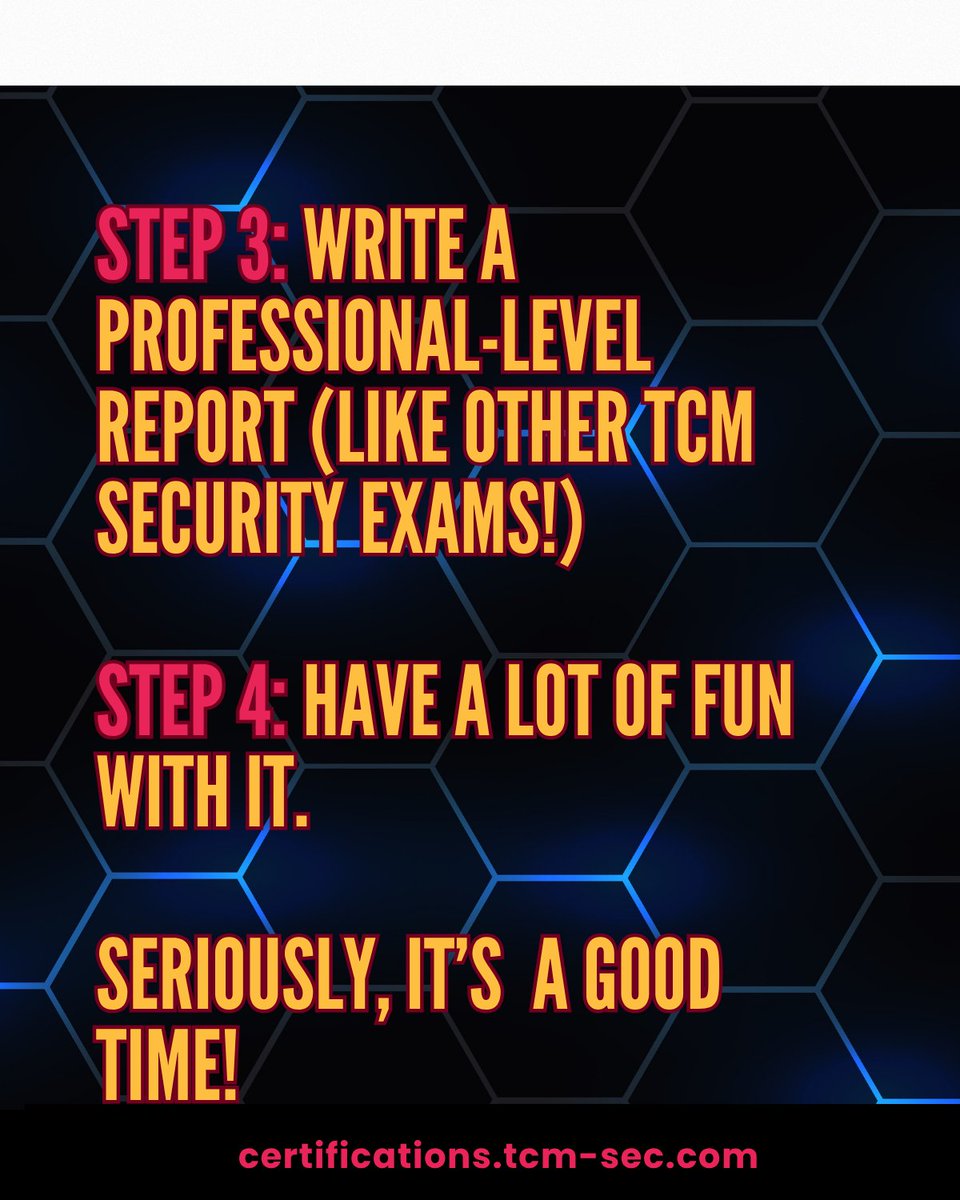
Become a certified AI hacker with TCM Security. You can earn a PAPA (Practical #AI Pentest Associate) certification by doing the following: - 𝗧𝗮𝗸𝗲 𝘁𝗵𝗲 𝗮𝗰𝗰𝗼𝗺𝗽𝗮𝗻𝘆𝗶𝗻𝗴 𝘁𝗿𝗮𝗶𝗻𝗶𝗻𝗴 (𝗔𝗜 𝗙𝘂𝗻𝗱𝗮𝗺𝗲𝗻𝘁𝗮𝗹𝘀 𝟭𝟬𝟬 & 𝗔𝗜 𝗛𝗮𝗰𝗸𝗶𝗻𝗴 𝟭𝟬𝟭) - 𝗦𝗶𝘁 𝗳𝗼𝗿 𝘁𝗵𝗲 𝗣𝗔𝗣𝗔 𝗲𝘅𝗮𝗺, 𝘄𝗵𝗲𝗿𝗲 𝘆𝗼𝘂'𝗹𝗹 𝗵𝗮𝗰𝗸 𝗮𝗻 𝗮𝗴𝗲𝗻𝘁𝗶𝗰 𝗔𝗜 𝗮𝗽𝗽𝗹𝗶𝗰𝗮𝘁𝗶𝗼𝗻 - 𝗪𝗿𝗶𝘁𝗲 𝗮 𝗽𝗿𝗼𝗳𝗲𝘀𝘀𝗶𝗼𝗻𝗮𝗹-𝗹𝗲𝘃𝗲𝗹 𝗿𝗲𝗽𝗼𝗿𝘁 𝗱𝗲𝘁𝗮𝗶𝗹𝗶𝗻𝗴 𝘁𝗵𝗲 𝗽𝗿𝗼𝗰𝗲𝘀𝘀 & 𝗳𝗶𝗻𝗱𝗶𝗻𝗴𝘀 - 𝗔𝗻𝗱 𝗵𝗮𝘃𝗲 𝘀𝗼𝗺𝗲 𝗳𝘂𝗻 𝘄𝗶𝘁𝗵 𝗶𝘁! Get the PAPA package today: hubs.la/Q04g6zc00









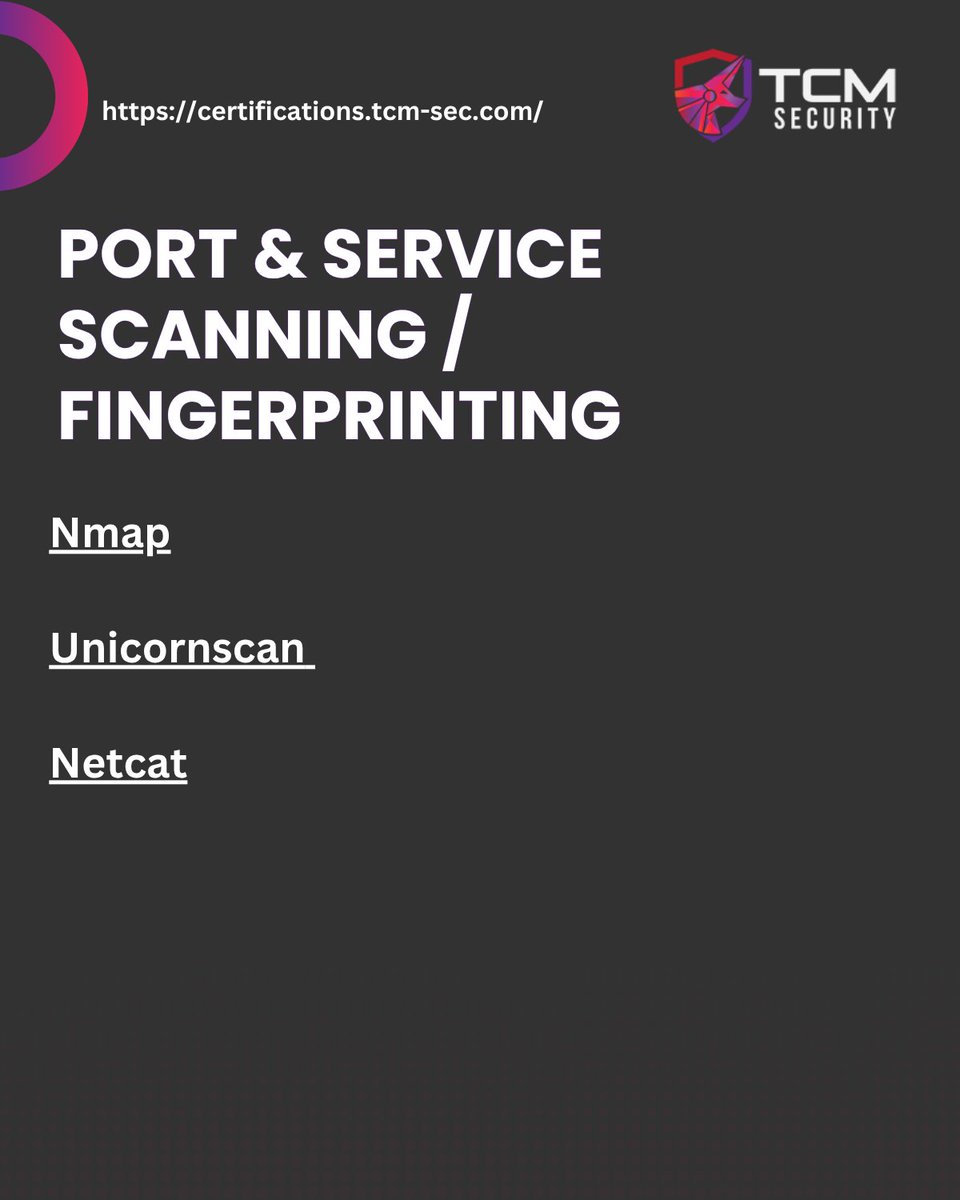
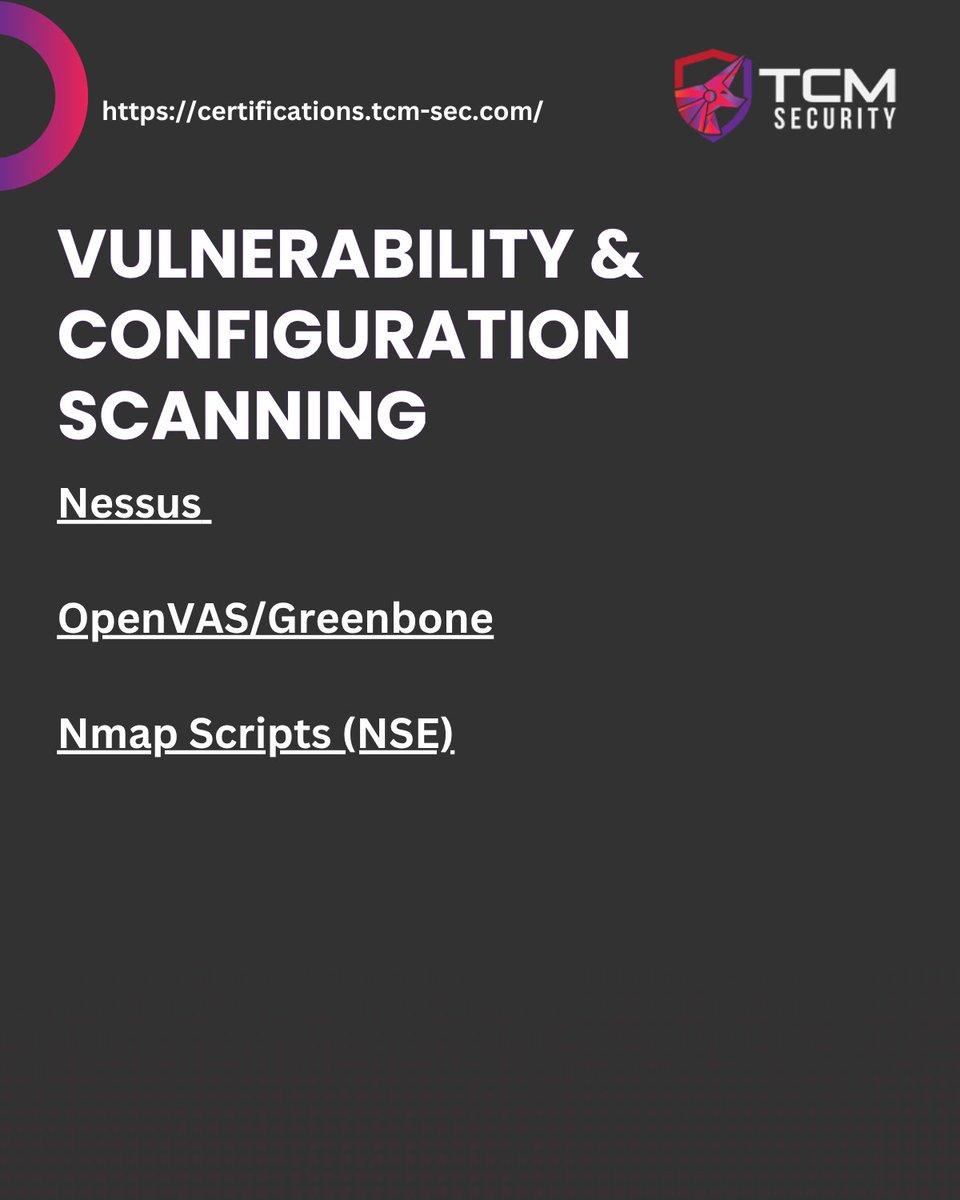
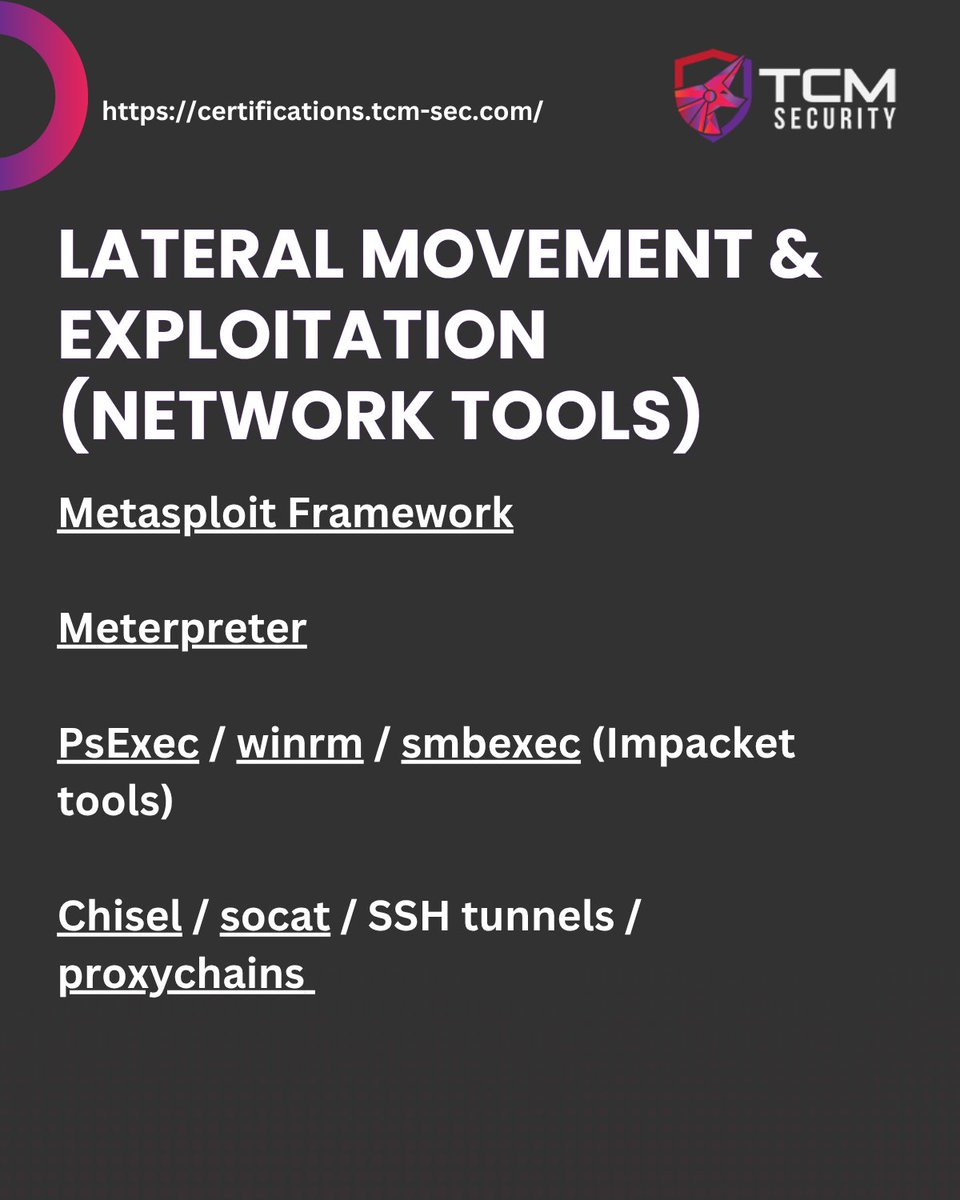
If you're just starting to immerse yourself in #cybersecurity, consider joining the TCM Security Academy! Take a course like Practical Ethical Hacking, which will help you build a robust foundation as a pentester: hubs.la/Q04f_JK60 Are you new to penetration testing and trying to master the basics of #networking? You'll need to understand #networking to be successful. So, here are some core concepts to start with: 𝐓𝐡𝐞 𝐎𝐒𝐈 𝐌𝐨𝐝𝐞𝐥. This serves as the standard language for discussing different network layers. Understanding the OSI Model can allow you to be more precise in your pentest findings. 𝐈𝐏 𝐀𝐝𝐝𝐫𝐞𝐬𝐬𝐞𝐬. Although this might seem silly at first, if you aren't prepared to define what an IP address is, you may need to do some studying or risk running into issues when it comes to recon and scope. 𝐌𝐚𝐜 𝐀𝐝𝐝𝐫𝐞𝐬𝐬𝐞𝐬. The more you know, the better. Knowing more about the devices running on a specific network will only benefit you in your testing. 𝐓𝐂𝐏 & 𝐭𝐡𝐞 𝐓𝐡𝐫𝐞𝐞-𝐖𝐚𝐲 𝐇𝐚𝐧𝐝𝐬𝐡𝐚𝐤𝐞. Understanding how a three-way handshake works helps make sense of how the network is interacting with your scan. 𝐂𝐨𝐦𝐦𝐨𝐧 𝐏𝐨𝐫𝐭𝐬 & 𝐏𝐫𝐨𝐭𝐨𝐜𝐨𝐥𝐬. This knowledge will become your secret weapon during recon - allowing you to identify attack vectors and vulnerabilities. 𝐒𝐮𝐛𝐧𝐞𝐭𝐭𝐢𝐧𝐠. Don't let the math scare you away! Subnetting is useful for several reasons: It can help you stay in your engagement scope and allow you to pivot effectively to other internal networks once you are inside a network.