Saso Virag retweetledi
Saso Virag
19.4K posts

Saso Virag
@VS_
Been there, done that, didn't get a t-shirt because I'm too old to be bought by vendor-ware. Security; risk; information use, misuse, and abuse.
Katılım Şubat 2009
718 Takip Edilen1.2K Takipçiler
Saso Virag retweetledi

Now, I just send those people to read this excellent piece philvenables.com/post/defense-i… by @philvenables but I am uncertain if it cures them of their delusions or not....
English
Saso Virag retweetledi

Yes, I still see people who equate "defense in depth" with "using two firewalls of two different brands in series." YES, THEY STILL EXIST, these people. #random
English
Saso Virag retweetledi

This is probably why I don't get invited to do more panels. Right after the audience applauds the speaker who said "be suspicious of suspicious things", I go on a rant how they are all wrong.
twitter.com/ErrataRob/stat…
Robert Graham@robertgraham
This last item is what really gets me. I'm in a room full of cyber experts and somebody says something like be "wary of suspicious" things and everyone nods their heads like this is a real thing. IT'S NOT A REAL THING. THIS ISN'T MEANINGFUL ENGLISH. CAN'T YOU PEOPLE SEE IT??
English
Saso Virag retweetledi

@anton_chuvakin Also because “buried in concrete and sunk” lacks availability, so, by definition, not secure 😂 I always hated that phrase!
English
Saso Virag retweetledi

Are there technologies that are "inevitably secure", defined as secure no matter what the user does with it?
Please don't use "buried in concrete, then sunk to the ocean floor" examples, I mean the tech that is actually used... #random
English

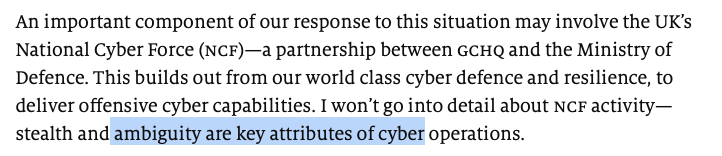
Indeed. Especially since “cyber” now includes EW, IO, kinetic attacks of critical infrastructure, and everything else that used to be included under the “information warfare” umbrella.
“I can’t define ‘cyber’, but I know it when I see it.” twitter.com/TheEconomist/s…
The Economist@TheEconomist
“It is a fallacy to say that cyber has not been a factor in the war in Ukraine,” Sir Jeremy Fleming, the director of @GCHQ, wrote earlier this year. “It is a very modern digital and cyber war, as much as it is a brutal and destructive physical one” econ.st/3WlwiWJ
English
Saso Virag retweetledi
Saso Virag retweetledi
More on the deficits in current European legal frameworks & oversight practice on this topic and a nascent agenda for positive change: stiftung-nv.de/sites/default/…
English
Saso Virag retweetledi
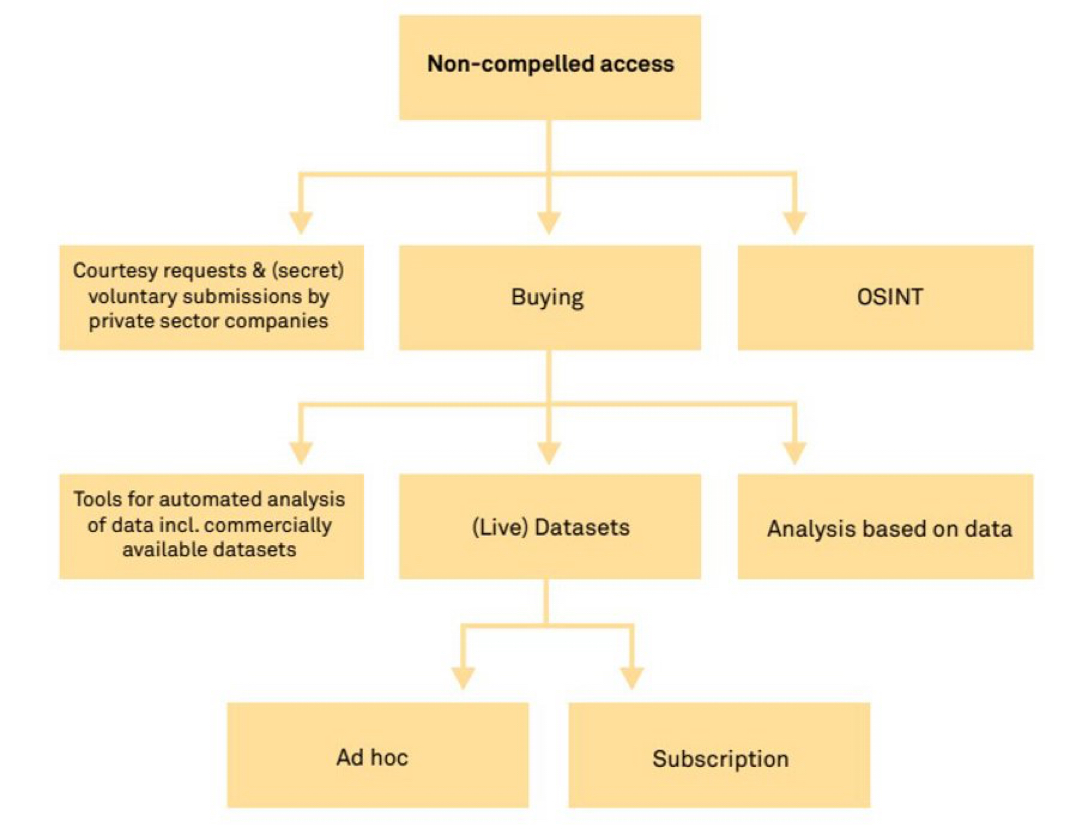
Having discussed this further w/ oversight practitioners & reviewing several legal frameworks @dietricharlotte and I argue that there is a pressing need in Europe to curb the risk of disproportionate use of such data by intel services.
English
Saso Virag retweetledi
Saso Virag retweetledi
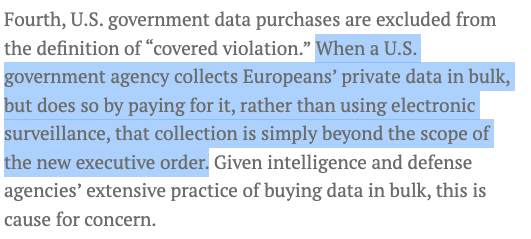
Yet, non-compulsory modes of government access to personal data are missing from the discussion. They are a non-topic in the EU-US DPF and - as argued by @ashgorski - are also beyond the scope of the U.S. Executive Order 14086 . Source: justsecurity.org/83927/the-bide…
English
Saso Virag retweetledi
Saso Virag retweetledi
The @EU_Commision published a comprehensive draft decision “on the adequate level of protection of personal data under EU-US Data Privacy Framework” today. #surveillance commission.europa.eu/system/files/2…
English
Saso Virag retweetledi
Saso Virag retweetledi

This project will be led by 3 experts: Andy Penn, Rachael Falk and Mel Hupfeld. In addition, some of the biggest cyber guns from around the world have agreed to help. @ciaranmartinoxf will lead a global cyber expert panel, who will ensure our work really is world-leading. #NPC
English
Saso Virag retweetledi

The Cyber Security Strategy will:
-Bring the whole nation into the fight to protect our citizens & economy
-Strengthen critical infrastructure & gov networks
-Build sovereign capabilities
-Strengthen our international engagement so we can be a global cyber-leader
#NPC
English