Sabitlenmiş Tweet

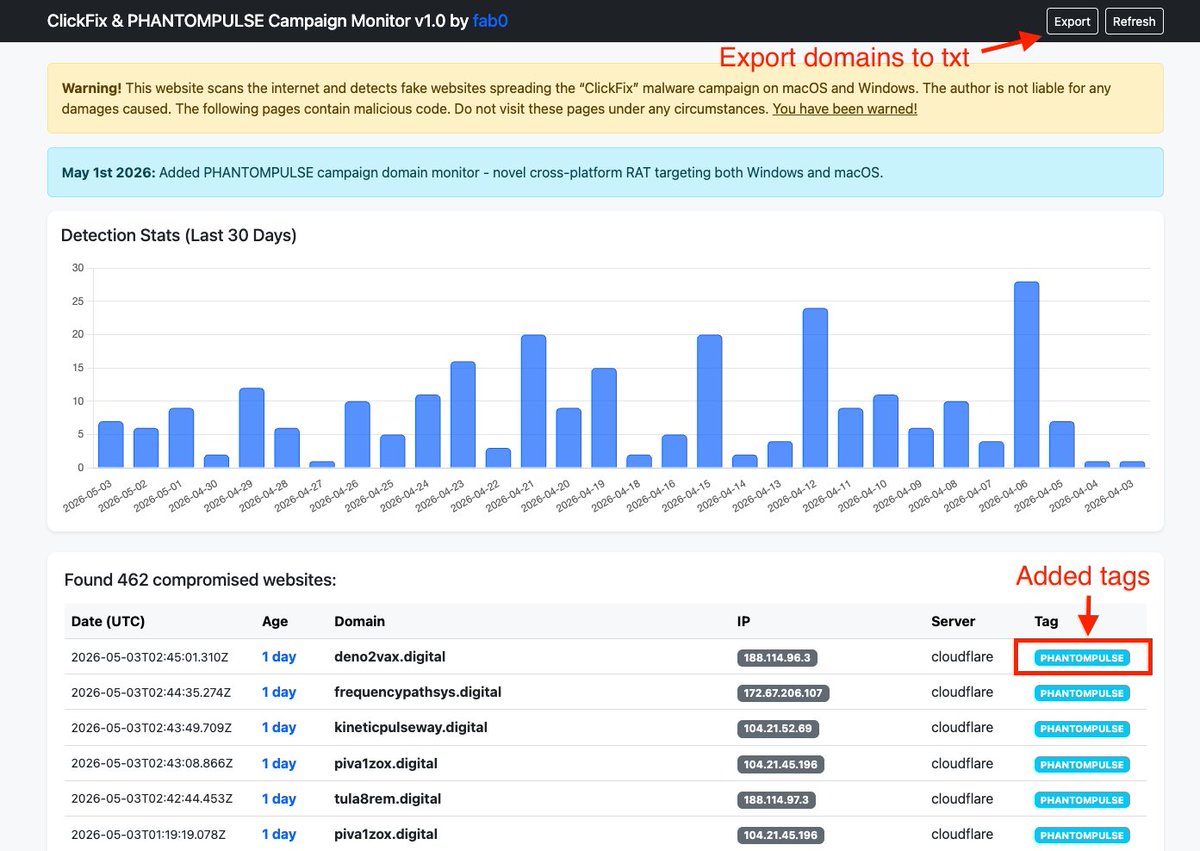
Apparent WordPress compromise of popular restaurant chain #TGIFridays observed with #clickfix infection chain delivering malicious MSI disguised as "Microsoft Endpoint DLP Module"
TGIF? 👾
#malware #clickfix
@executemalware

English