
@sbxpra @VicVijayakumar Um no, the user shouldn't have to be up to date with the news to know when to migrate regions, it's Amazons liability.
English
Yakov
89 posts

@Yakov5776
discord: yakov






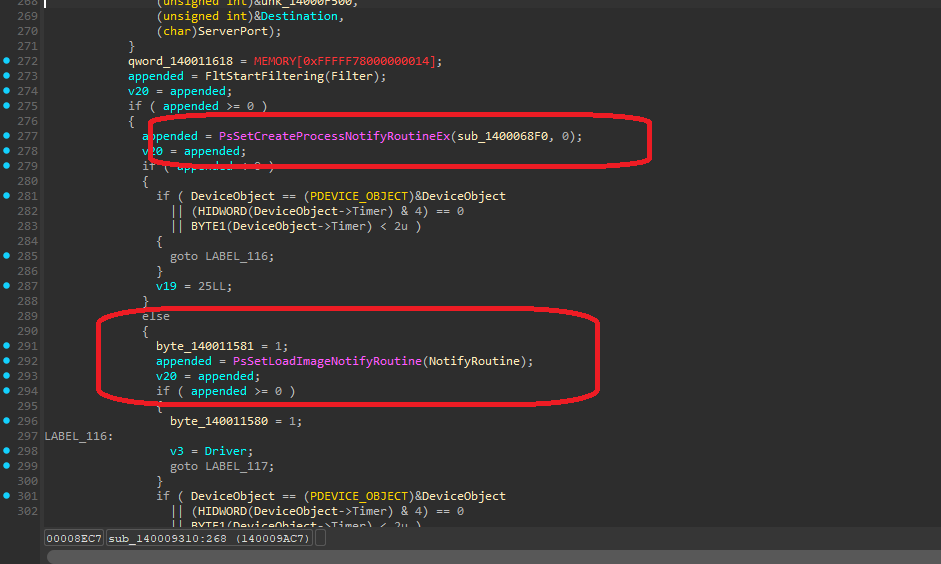
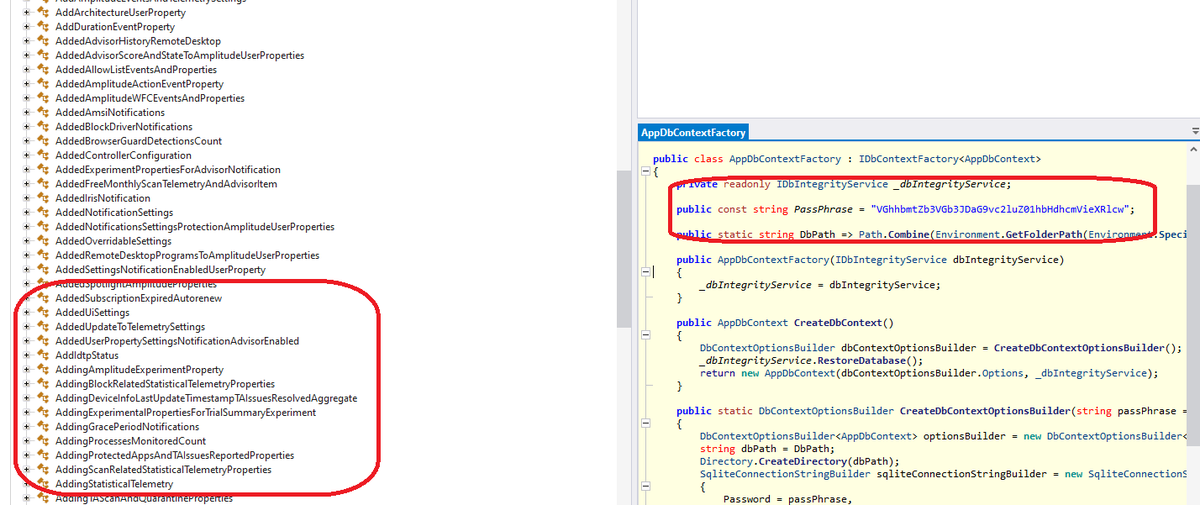
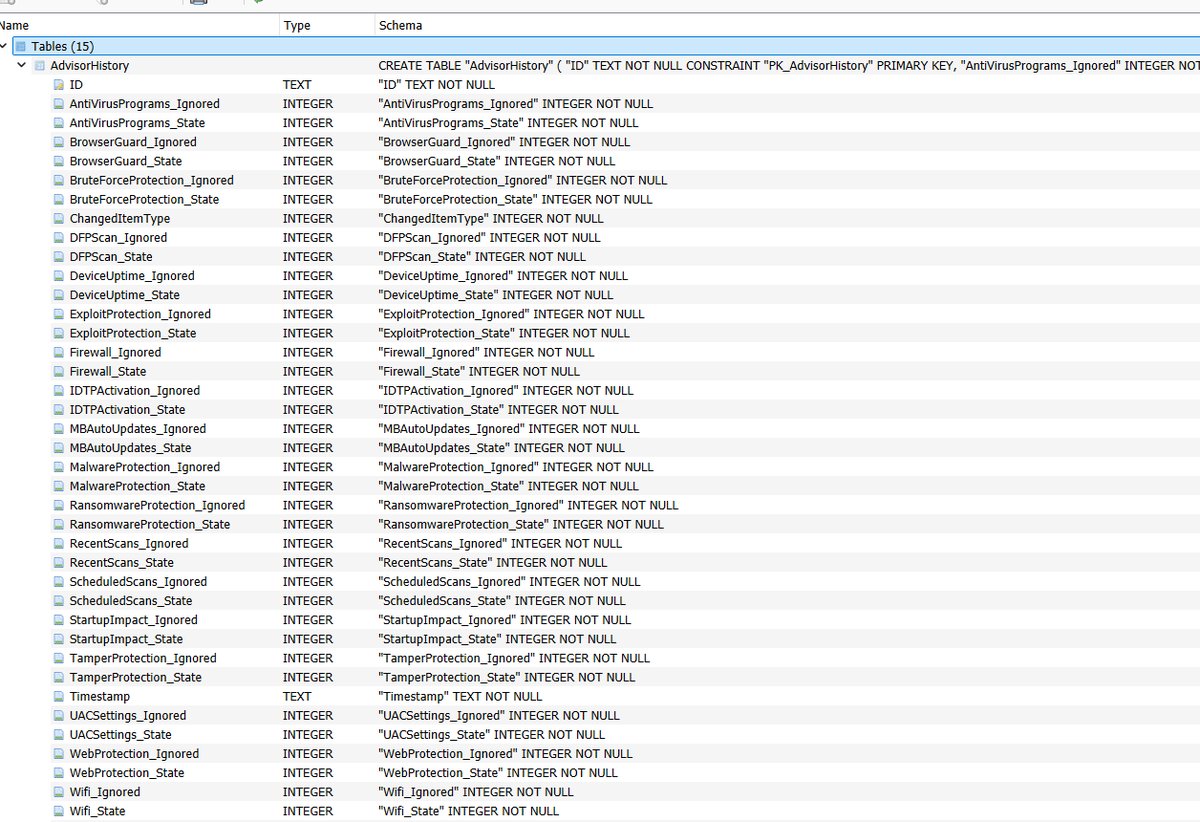
@vxunderground Explain this to me because I’m stupid











Whoever created ilovepdf, you're the real hero.











