Sabitlenmiş Tweet
Rectifyq
1.1K posts


Rectifyq
@_rectifyq
Threat I̶n̶t̶e̶l̶l̶i̶g̶e̶n̶c̶e̶ ̶ Information focusing on Malaysia 🇲🇾
Katılım Mayıs 2024
669 Takip Edilen788 Takipçiler
Rectifyq retweetledi

Ops Teguh 2.0 - Major crackdown on scams leads to RM57.68mil seized, 187 suspects nabbed
thestar.com.my/news/nation/20…
English
Rectifyq retweetledi

Oasis Security reported a targeted intrusion against multiple Malaysian government bodies using bespoke Python tooling for internal enumeration and data exfiltration, active webshells, and undisclosed C2 infrastructure with a C# beacon and Python control… oasis-security.io/blog/malaysian…
English
Rectifyq retweetledi
Hey, just a quick question: if you're sharing your fav cafe, how would you do that? List with google map links?
What if I tell you, you can create sharable custom map?
I got tutorial on how to do so:
@thisisfinx/lite-osint-sharable-custom-map-bfb2cd16d553" target="_blank" rel="nofollow noopener">medium.com/@thisisfinx/li…
No worries, lots of pictures in the guide~
#osint
English
Rectifyq retweetledi
Rectifyq retweetledi

🇲🇾 A threat actor is claiming unauthorized access to systems associated with the Civil Aviation Authority Malaysia (CAAM), alleging possession of leaked documents, aviation-related records, and internal databases.
According to the underground forum post, the actor claims:
• access to tens of thousands of internal documents
• aviation and flight-related records
• additional undisclosed private documents
• continued access to internal systems
The actor also shared screenshots and alleged proof-of-access material, while threatening additional leaks.
At this time, the authenticity, scope, and operational impact of the claims remain unverified.
Initial observations:
• Aviation-sector organizations remain high-value targets due to operational, regulatory, and transportation-related data
• Even partial exposure of aviation infrastructure documentation can create downstream security and intelligence risks
• Threat actors increasingly use staged leaks and “proof-of-access” tactics to build credibility and pressure organizations
If authentic, potential risks could include:
• exposure of sensitive operational documentation
• targeted phishing against aviation personnel
• supply chain reconnaissance
• regulatory and compliance concerns
• insider threat exploitation
• credential abuse and lateral movement opportunities
The post also references possible future disclosures, suggesting the actor may be attempting:
• extortion pressure
• reputation damage
• underground reputation building
• data monetization
No official confirmation from CAAM has been observed at the time of writing.
DDW is continuing to monitor for:
• validation of leaked materials
• additional sample releases
• operational impact indicators
• downstream threat actor activity
• official statements or incident response disclosures
#DDW #Intelligence #CyberSecurity #ThreatIntelligence #Malaysia #Aviation #CAAM #DataLeak #DarkWeb #Infosec #TransportationSecurity #OSINT

English
Rectifyq retweetledi

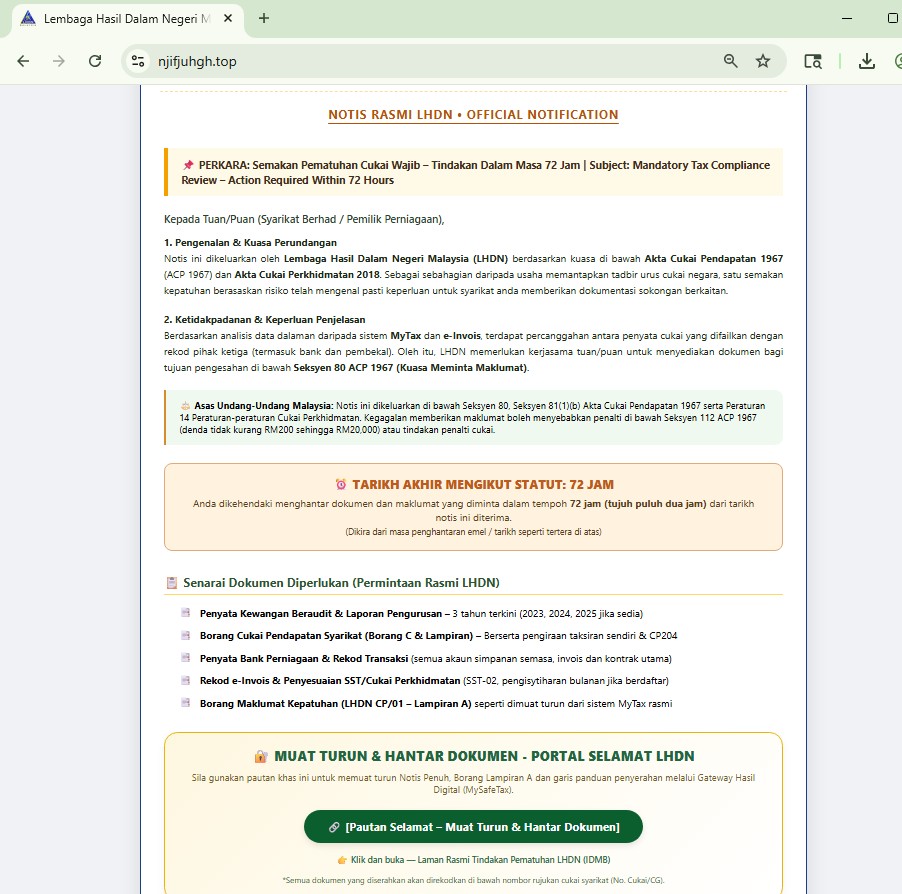
Fake Malaysia LHDN (tax authority) themed site hosting a “Mandatory Tax Compliance Review” notice.
njifjuhgh[.]top
The “DOWNLOAD & SEND DOCUMENTS - LHDN SAFE PORTAL” file downloads a #Tedy trojan payload.
Interesting part, the same domain previously hosted Indian tax themed phishing/malware
urlscan.io/result/019d762…
file hash: 7263622822694fc8c2720974c31b5c12b2fdc864ce496ab4f6da57e8c361b59b
#phishing #malware @malwrhunterteam @500mk500 @skocherhan
English
Rectifyq retweetledi

New report: Darcula (“Magic Cat”) is one of the most active phishing frameworks we’re tracking.
From API-driven infra to socket-based comms and fake shop deployments, this kit continues to evolve rapidly.
Breakdown, detections: urlscan.io/blog/2026/05/1…
Full report on urlscan Pro

English
Rectifyq retweetledi

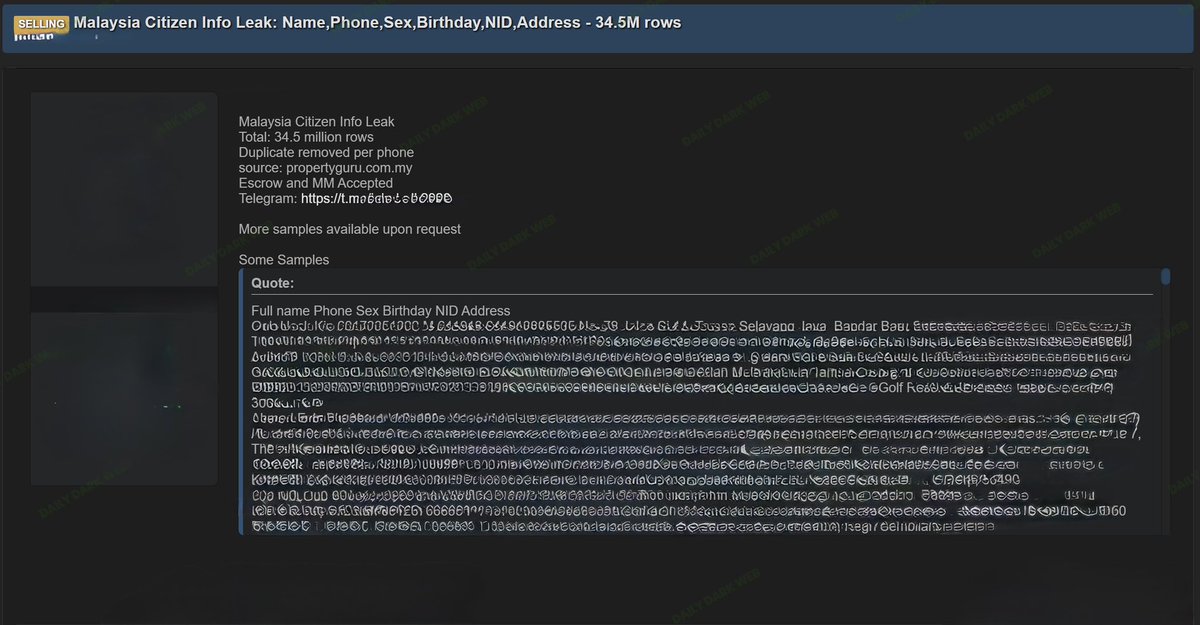
🇲🇾 A threat actor is advertising the sale of an alleged database containing personal information of Malaysian citizens on a cybercrime forum.
According to the post, the dataset allegedly contains approximately 34.5 million records, with the actor claiming the data includes:
• Full names
• Phone numbers
• Gender information
• Birthdates
• National ID numbers
• Residential addresses
The actor also references a possible connection to PropertyGuru Malaysia, though there is currently no confirmation that the company was breached or that the data originated from its systems.
At this time, the claims remain unverified, and the authenticity of the dataset has not been independently confirmed.
Potential risks associated with this type of exposure include:
• Identity theft
• SIM-swapping and social engineering attacks
• Financial fraud and account takeover attempts
• Highly targeted phishing and scam campaigns
Organizations and individuals in Malaysia should remain alert for suspicious communications requesting verification codes, banking details, or identity documents.
Daily Dark Web is continuing to monitor underground forums and related channels for further validation or official responses.
#DDW #Intelligence #CyberSecurity #DataLeak #DarkWeb #ThreatIntelligence #Malaysia #Privacy #DataBreach
English
Rectifyq retweetledi

🇲🇾 A threat actor is claiming to sell an alleged database belonging to CIMB Bank Malaysia containing over 2 million records.
According to the post, the exposed data allegedly includes:
Customer names
Mobile numbers
Gender
Dates of birth
Card-related information
Banking-related fields
The actor also shared sample screenshots and is attempting to monetize the dataset through underground channels.
If verified, exposure of this type of banking data could significantly increase risks related to:
Financial fraud
Identity theft
Social engineering
SIM swapping
Targeted phishing campaigns
Account takeover attempts
Financial institutions should closely monitor for:
Unusual authentication activity
Credential stuffing attempts
Spike in phishing infrastructure impersonating the bank
Fraud patterns tied to customer identity data exposure
Customers are advised to:
Be cautious of unsolicited banking calls or SMS messages
Monitor account activity regularly
Enable MFA where available
Avoid sharing OTP or verification codes
The authenticity of the database has not been independently verified at this time.
#DDW #CyberSecurity #Malaysia #Banking #DataBreach #ThreatIntelligence #DarkWeb #Infosec

English
Rectifyq retweetledi

🇲🇾 A threat actor is advertising the sale of an alleged dataset containing information on approximately 183,000 Mazda Malaysia customers on a dark web forum.
According to the listing, the leaked data may include:
Customer names
Phone numbers
Email addresses
Vehicle registration details
Chassis and engine numbers
Vehicle model and variant information
The threat actor claims the data is linked to Mazda Malaysia customers, though the authenticity and scope of the alleged leak have not yet been independently verified.
Automotive customer databases can be abused for:
Targeted phishing campaigns
Warranty or dealership impersonation scams
Vehicle-related fraud
Identity theft and profiling
Affected users should remain cautious of suspicious calls, SMS messages, or emails pretending to be from dealerships, insurers, or service centers.
Daily Dark Web is continuing to monitor the situation for further verification and technical indicators.
#DDW #CyberSecurity #DataLeak #Malaysia #Mazda #ThreatIntelligence #DarkWeb #Intelligence

English

@_rectifyq Nice to meet you finally idola 🤝
English
Rectifyq retweetledi
Rectifyq retweetledi

🇲🇾 A threat actor on a cybercrime forum is claiming to have leaked data allegedly with OCBC Malaysia.
According to the forum post, the shared sample suggests the alleged dataset may include:
• Phone numbers
• Email addresses
• Banking-related information
• Passport-related fields
• National ID numbers (e.g., MyKad)
• Business registration data
• Driving license information
The post includes sample structured data and references to OCBC Malaysia domains. However, the authenticity, source, and scope of the alleged data remain unverified at this time.
No official statement from OCBC Malaysia has been observed regarding these claims.
If confirmed, exposure of financial and identity-related data could significantly increase the risk of:
• Financial fraud and account takeover
• Identity theft
• Targeted phishing and social engineering
• SIM-swapping attacks
Users and organizations are advised to:
• Monitor financial accounts for suspicious activity
• Enable MFA across banking and sensitive services
• Be cautious of unsolicited communications referencing OCBC
• Avoid sharing sensitive information via email or phone
#DDW #Intelligence #Malaysia #OCBC #CyberSecurity #DataBreach #DarkWeb

English
Rectifyq retweetledi
Rectifyq retweetledi

Malaysia ada yang dah kena gais

moto_sato@58_158_177_102
cPanelからのランサム 現状.jpはなく見えるけれど、時間の問題か。。。(.twは少し発生しつつある)
Indonesia
Rectifyq retweetledi
New updates for Malaysian OSINT resource list🎉🎉🎉
This update is all about AI and my attempt to use AI for this list:
@thisisfinx/update-v5-malaysian-osint-resource-list-ai-stuff-d3a22e88b0c9" target="_blank" rel="nofollow noopener">medium.com/@thisisfinx/up…
Shoutout to (CyberRaya – Medium), he is the real expert here, I am just a noob trying to learn
#ai #osint
English
Rectifyq retweetledi

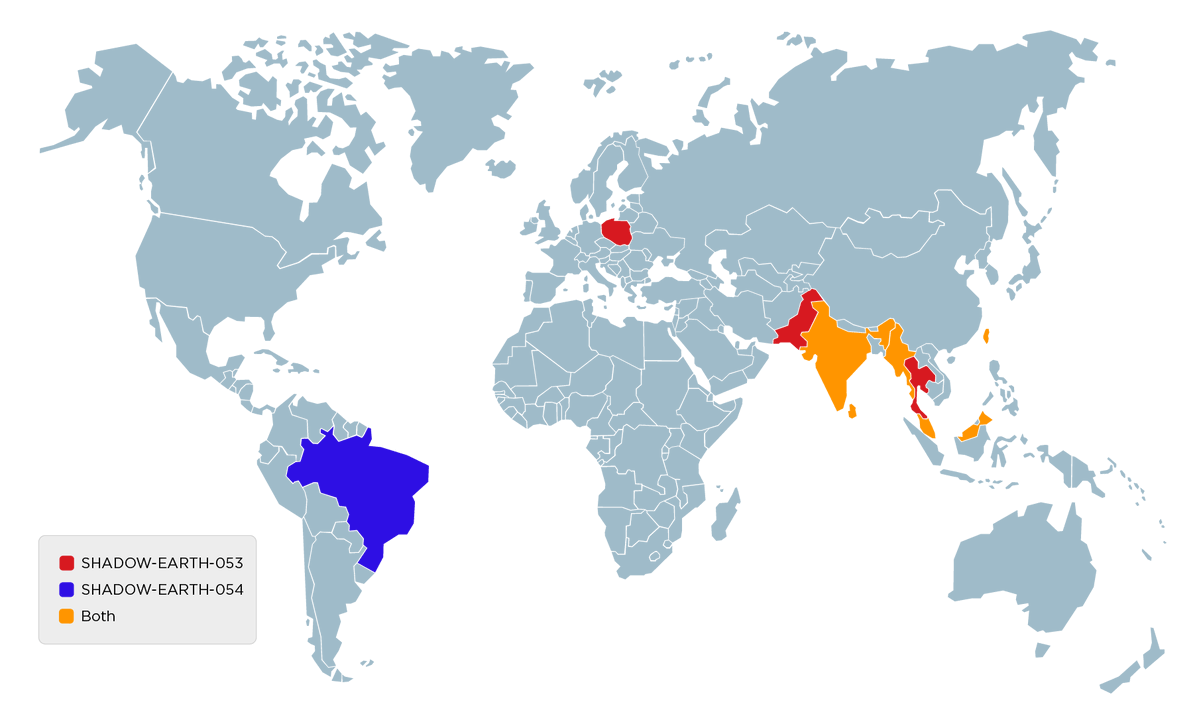
Malaysia gov/defence orgs appear in victim sets for both SHADOW-EARTH-053 and 054. Initial access via ProxyLogon/ProxyShell on exposed Exchange
trendmicro.com/en_us/research…
English