Zaolin
3.2K posts


Zaolin
@_zaolin_
Head of Solution Engineering @Binarly, IT-Consultant @ Niche Systems. Ex-CEO of @immune_gmbh. Founder of @9eSec, President of the @osfw_foundation.


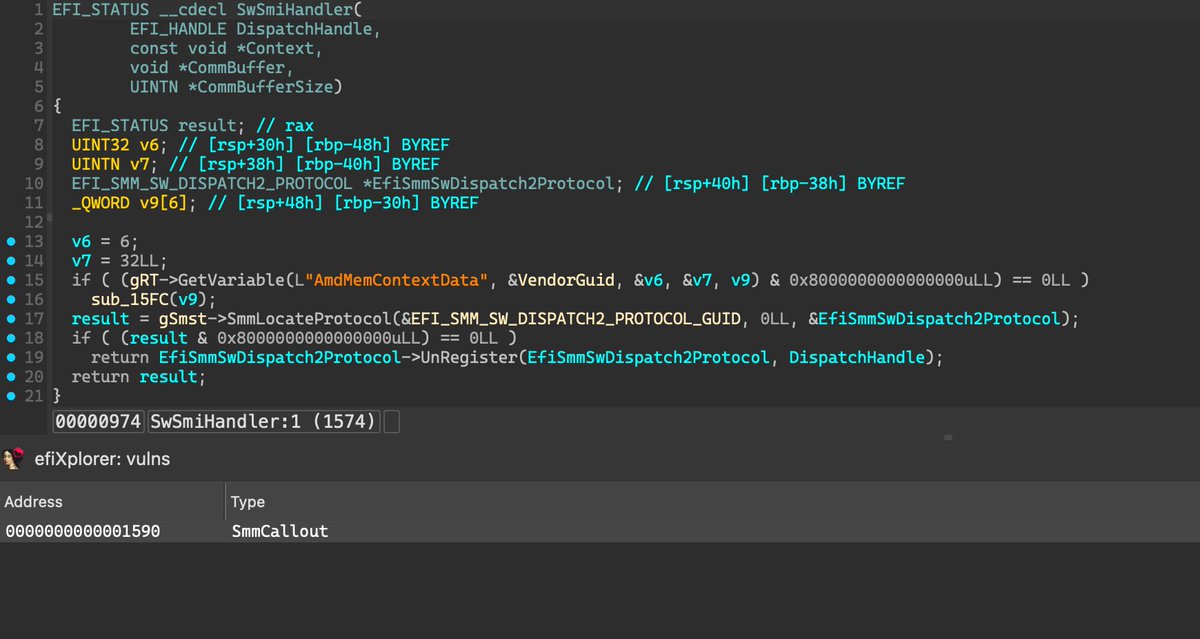



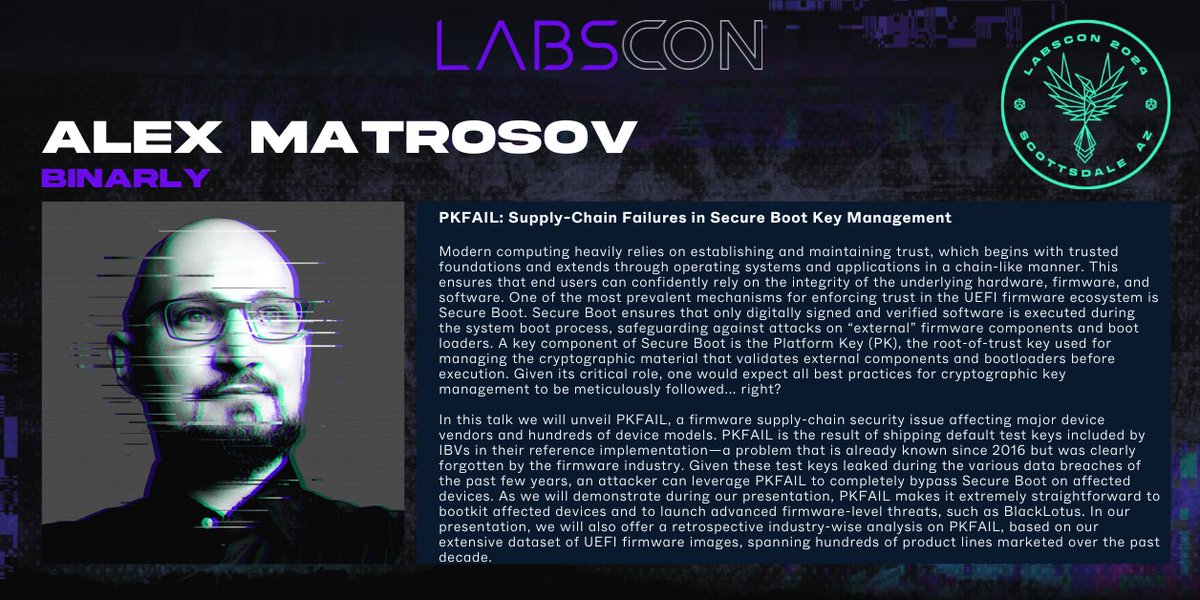
🚨In just a few hours at #LABScon, we’ll be unveiling a high-impact vulnerability and a critical security discovery affecting platform trust on Supermicro servers. Stay tuned and watch our REsearch blog!

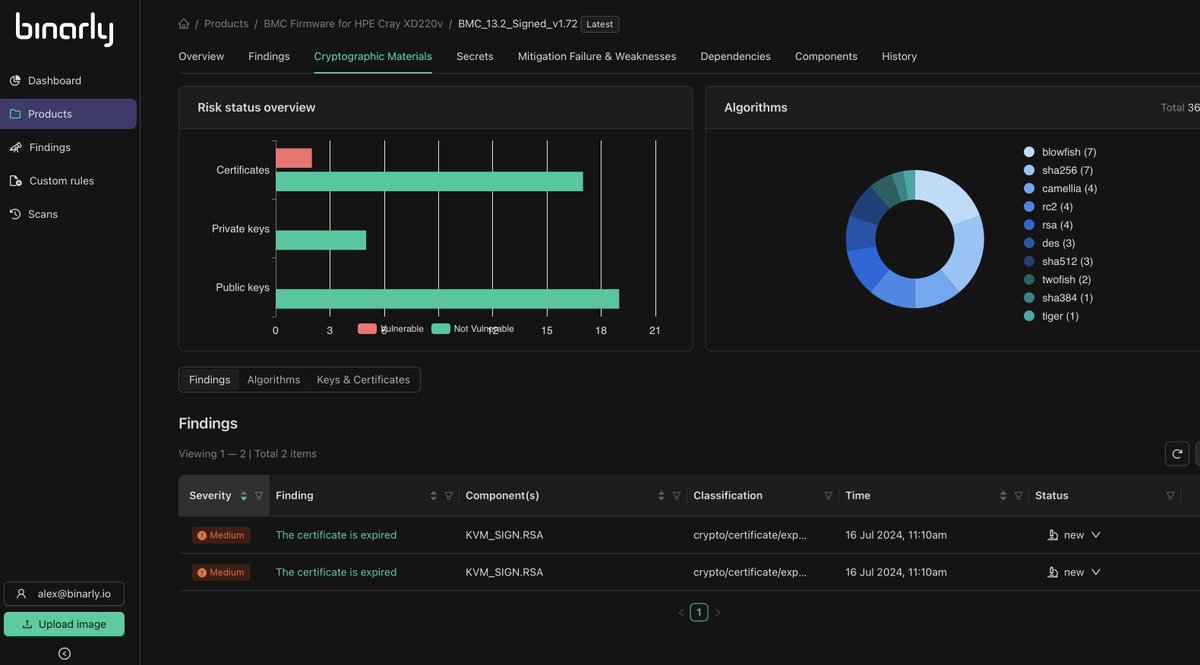
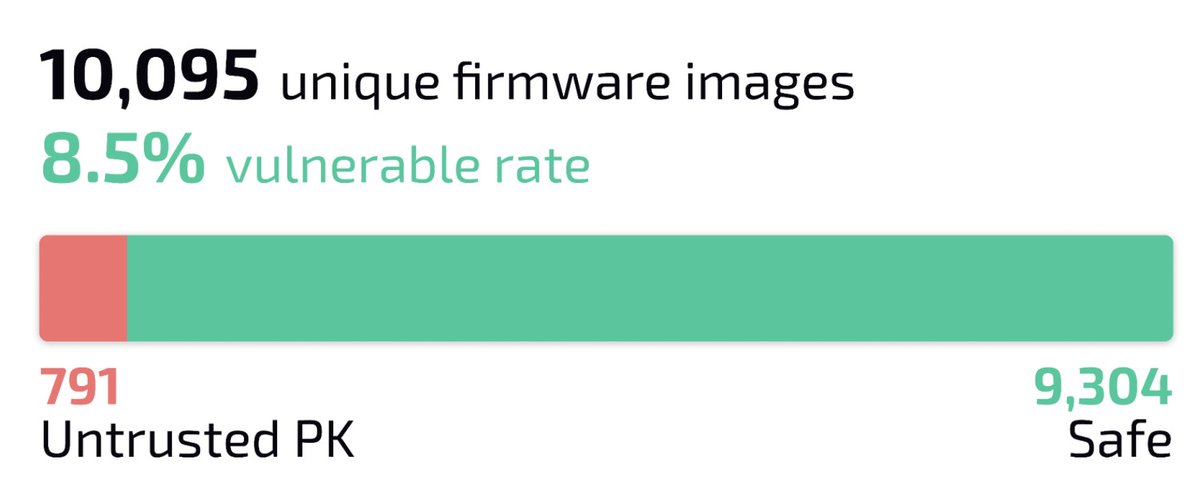
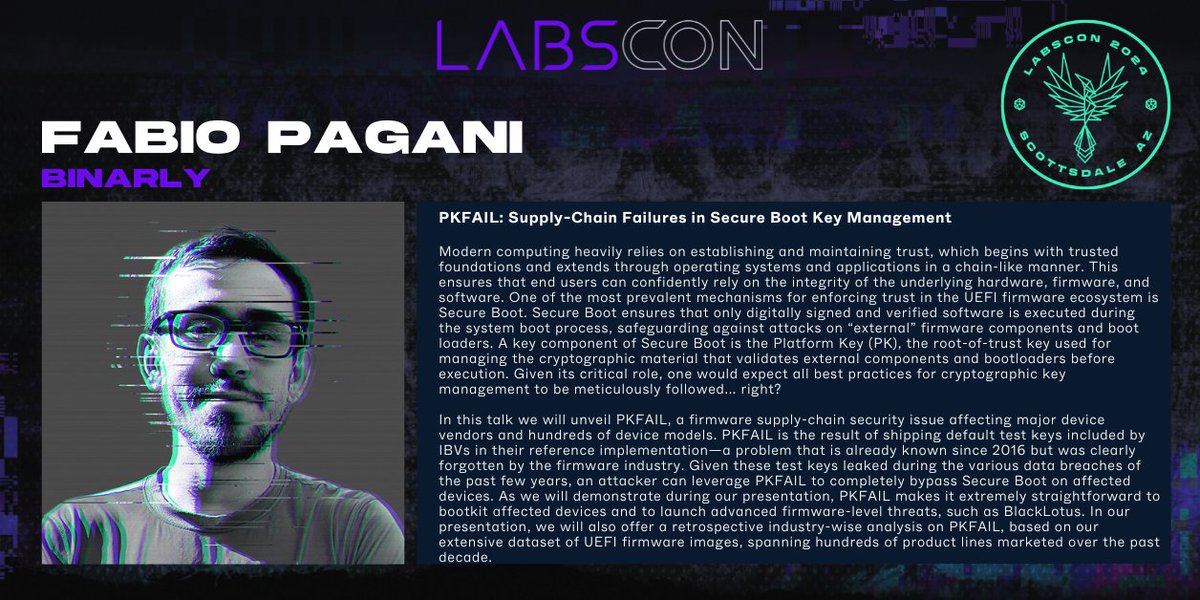
🚨NEW: "PKfail Two Months Later: Reflecting on the Impact." by @pagabuc Based on pk.fail data 📈 🖥️10,095 unique firmware images uploaded 🔥791 of which contained an untrusted PK 🛟9304 is safe 💥8.5% vulnerable rate 🔬Full report: binarly.io/blog/pkfail-tw…






Thanks to @binarly_io for Sponsoring #OST2 at the Gold🥇 level! Learn more about them here: binarly.io




Wohoo! @binarly_io has just released 2.5 of their platform with some major new capabilities like reachability analysis, custom rules , secret discovery and cryptographic asset discovery, and container support. youtu.be/4TG6X1WjWH4?si…



Intel HW is too complex to be absolutely secure! After years of research we finally extracted Intel SGX Fuse Key0, AKA Root Provisioning Key. Together with FK1 or Root Sealing Key (also compromised), it represents Root of Trust for SGX. Here's the key from a genuine Intel CPU😀