Sean 🏴 retweetledi

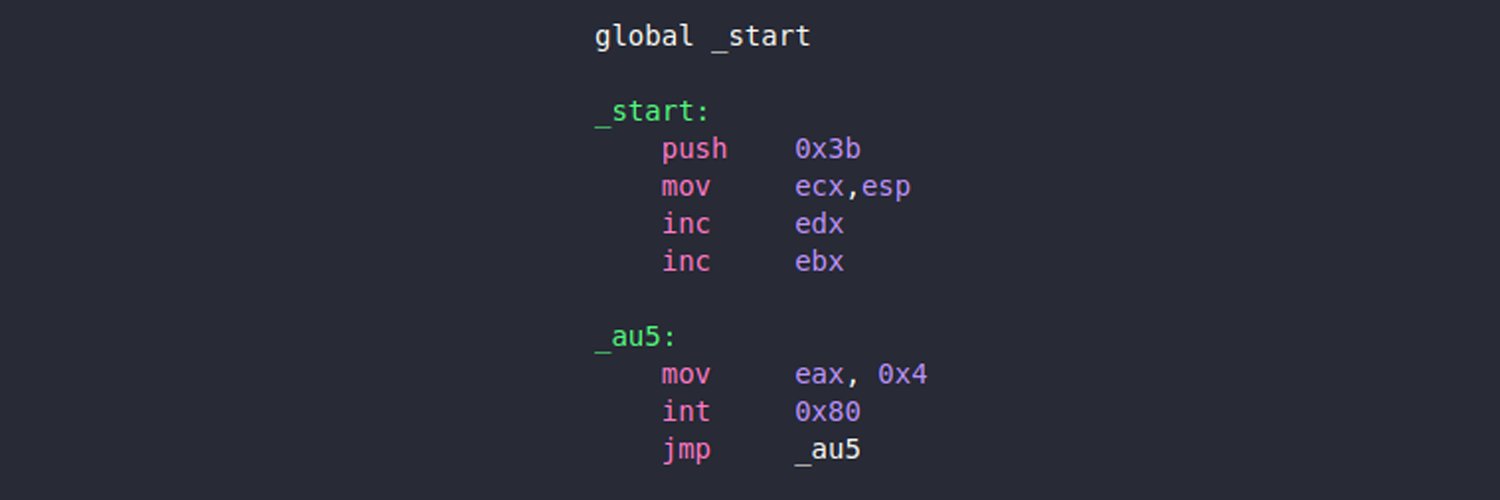
spend some time rewriting stardust to be more minimalist and easier to use! I needed a generic minimal shellcode template that works for both x86 and x64 out of the box so I rewrote stardust to do so.
It is now written in C++20 and utilizing some of its language features. The template can be used to easily write shellcode fast in a more modern and less painful way.
The project can be compiled in release or debug mode, where as debug mode will just allow the use of DBG_PRINTF, which calls DbgPrint under the hood to print out strings to the currently attached debugger.
There are more things i have added so consider checking it out. I removed global variable access since i no longer use it nor require it (went for diff design heh). If u still need that feature I would recommend to change the branch to "globals-support" where the old version is hosted.
github.com/Cracked5pider/…
English