Tyler retweetledi
Tyler
37 posts


Tyler
@cvediver
views are my own RT ≠ endorsement
Washington, DC Katılım Şubat 2018
332 Takip Edilen54 Takipçiler
Tyler retweetledi
Tyler retweetledi

@robertswiecki @mboehme_ I think there's still tons of work to do in harnessing complex targets E2E. Automatically extracting unit-test style harnesses for individual functions from a E2E, whole-process harness (think chrome, acrobat etc) would be a huge improvement and likely won't require ML/solvers
English
Tyler retweetledi
Tyler retweetledi

GNU Debugger GDB 15.1 Brings Better Python Support
phoronix.com/news/GDB-15.1-…
Svenska

We’re looking for software security experts to join us full time at @TechAtBloomberg ! If you love fuzzing, static analysis and security research, please reach out! :)
Manhattan, NY 🇺🇸 English

Tyler retweetledi

download.vusec.net/papers/snappy_… <- cool paper on snapshot fuzzing! TL;DR: "taint trace how the input is used, snapshot at the point where it actually affects things". I think placing snapshots deeper in the code is how we automatically get "libfuzzer-perf" on "Nyx-complexity"-targets.
English

@seanhn @bas_van_schaik This was the idea behind @cetfor's PaperMachete, which is a pretty cool POC. I think that newer features in binja and performance improvements in the graph database could really help build on the approach
English

@bas_van_schaik Yep, what I am hoping to find though is something similar to CodeQL but for binaries. I have a property that I can, in theory, search for in source, but it would be way cleaner if I could express it over assembly code.
English
Tyler retweetledi

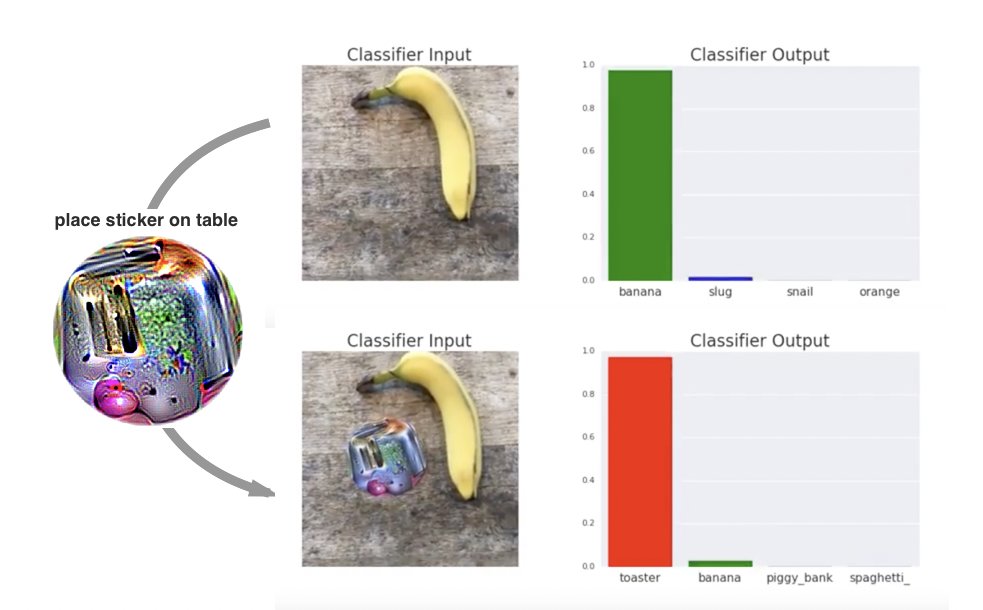
Speaking of making #fuzzing more effective, we've extended #jazzer's API to give the fuzzer new signals depending on the program state. @fhenneke created an example showing how this helps #jazzer to solve the maze game discussed in the #IJON paper. GitHub: github.com/CodeIntelligen…
GIF
Khaled Yakdan@KhaledYakdan
Code coverage alone is often insufficient as a signal for fuzzers to trigger deep bugs. Integrating more signals representing the program state into the feedback loop can help the fuzzer to make more progress. This paper is an excellent example of how to do that.
English
Tyler retweetledi

Our software engineer Boyan Milanov introduces Maat, a low-level symbolic execution framework based on Ghidra's IR language p-code. blog.trailofbits.com/2022/02/23/maa…
English
Tyler retweetledi

Now @Fidelity is asking for full account password over the phone using the numpad and symbols as stars. Best-case scenario is massively reduced search space for bruteforcing passwords in the event of a breach. What about phone auth is so challenging?
Tyler@cvediver
Criticizing @united's flagrant disregard for information security best practices devtty1er.com/20200713-unite…
English

I am looking for resources (papers, blog posts, tools) related to static/dynamic program analysis that has the goal of getting malware to execute real payloads in non-intended environments (sandboxes, VMs, emulators). RTs appreciated!
@BSaltaformaggio @moyix @pagabuc
#DFIR
English
Tyler retweetledi

@GHSecurityLab @Nosoynadiemas Unique domains != server instances. 300,000,000 should be more like 10,000,000.
English

Learn how to take aim at HTTP attack surfaces in @Nosoynadiemas series on fuzzing the Apache Web Server github.co/2OdR2SK

English
Tyler retweetledi

Congratulations to the AFL++ team (@hackerschoice @andreafioraldi @domenuk + others) for officially replacing afl-fuzz in the Google OSS-Fuzz platform that continuously fuzzes hundreds of critical opensource packages. AFL++ improvements are remarkable!
github.com/google/oss-fuz…
English