Nguyen The Duc
1.3K posts


@ducnt_
Just another web warrior ⚔️ Security Researcher ۞ Principal Security Engineer @Verichains ۞ Pwn2Own 2023 ۞@vnsec squad ۞ 💰https://t.co/wuyz6IfAbA ۞ nano 💻








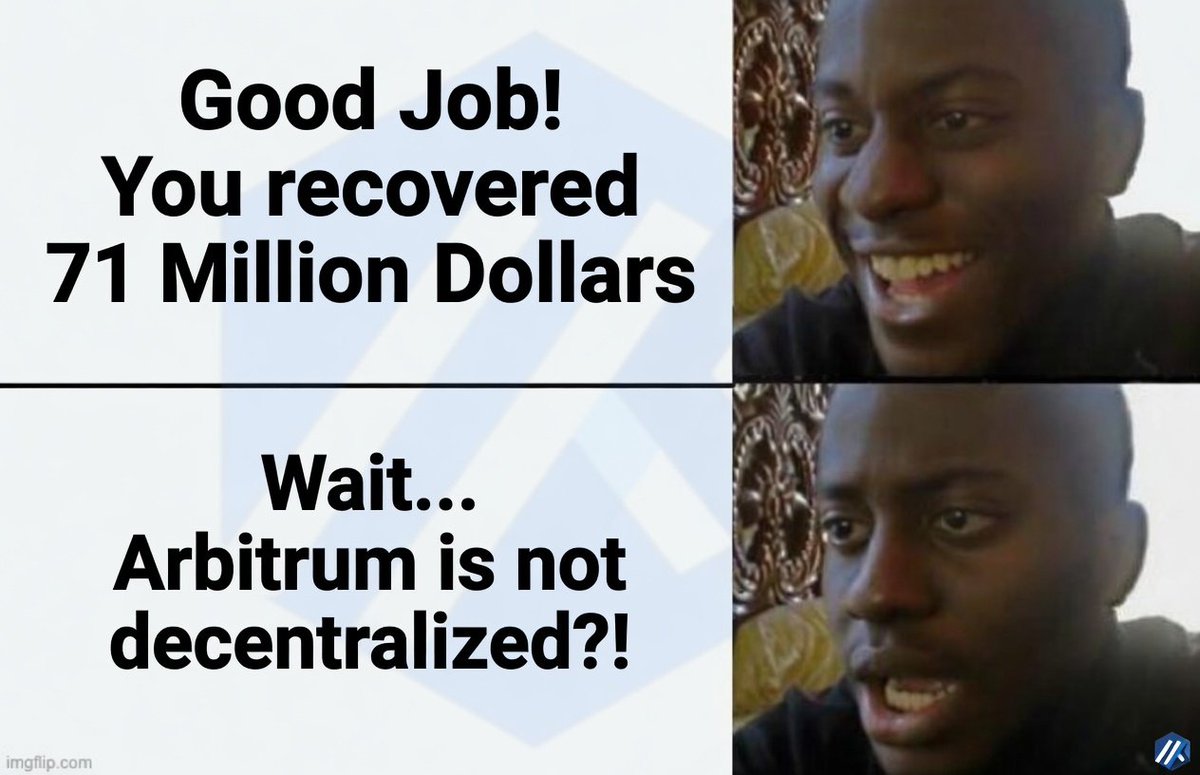
The Arbitrum Security Council has taken emergency action to freeze the 30,766 ETH being held in the address on Arbitrum One that is connected to the KelpDAO exploit. The Security Council acted with input from law enforcement as to the exploiter’s identity, and, at all times, weighed its commitment to the security and integrity of the Arbitrum community without impacting any Arbitrum users or applications. After significant technical diligence and deliberation, the Security Council identified and executed a technical approach to move funds to safety without affecting any other chain state or Arbitrum users. As of April 20 11:26pm ET the funds have been successfully transferred to an intermediary frozen wallet. They are no longer accessible to the address that originally held the funds, and can only be moved by further action by Arbitrum governance, which will be coordinated with relevant parties.