Beelon Musk
1.6K posts


@ethswarmhive
Ambitious Bee that enjoys space travel and flamethrowers 🐝 🚀🌌🔥




Join us for an open Q&A with @VitalikButerin to explore privacy-focused use cases devs should pursue—rooted in #cypherpunk values. 🗓️14:30, Friday 13📍maps.app.goo.gl/vKdRQ1wuWkkXPh… No tickets. Just show up — and be excellent to each other.

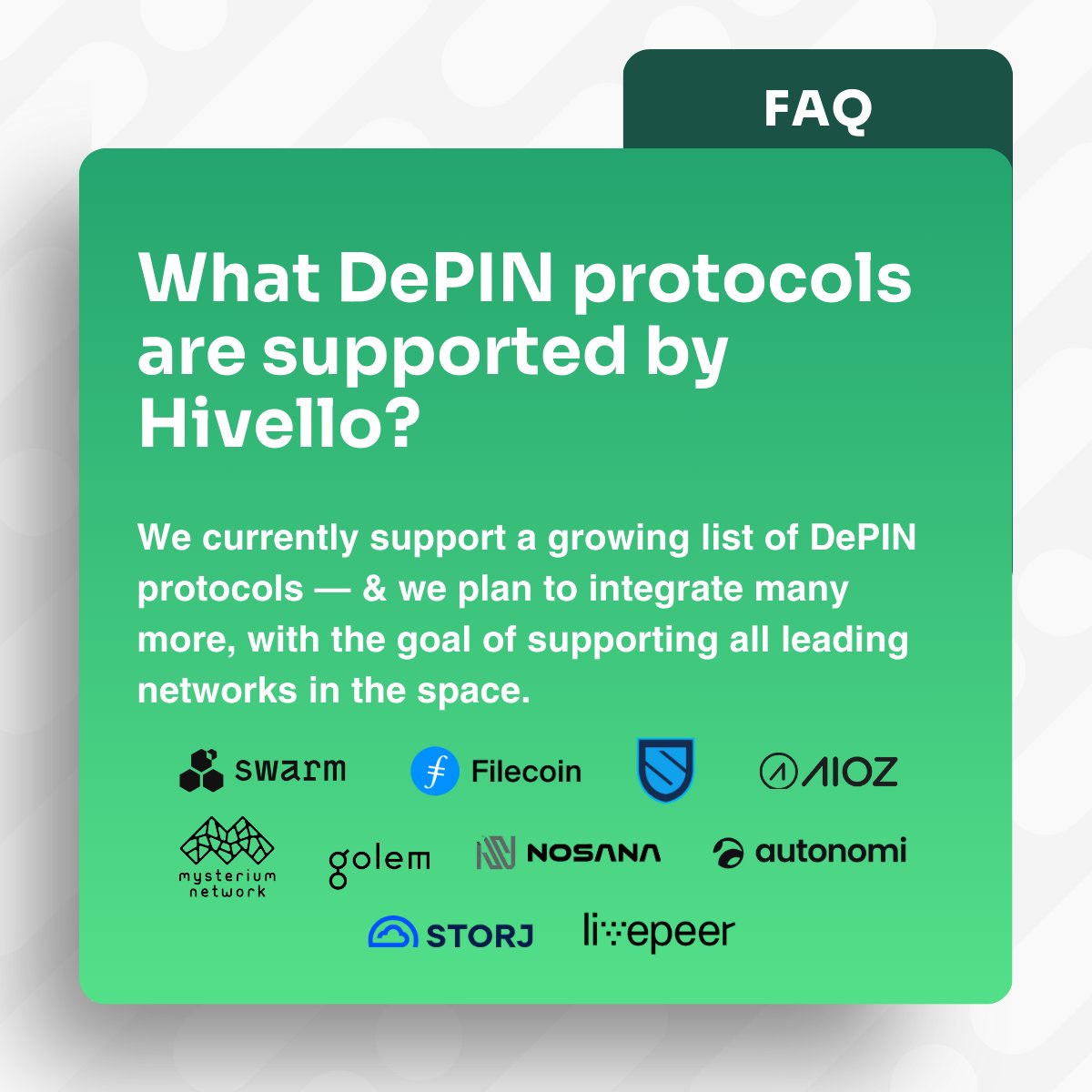
After Cambridge Analytica, we learned the danger isn’t just what you say — it’s who, when, and how often you say it. This is metadata, and it’s the new frontier of surveillance. Learn how Swarm could provide truly private messaging. No central servers. No metadata traces. Just pure, private communication. medium.com/coinmonks/sign…


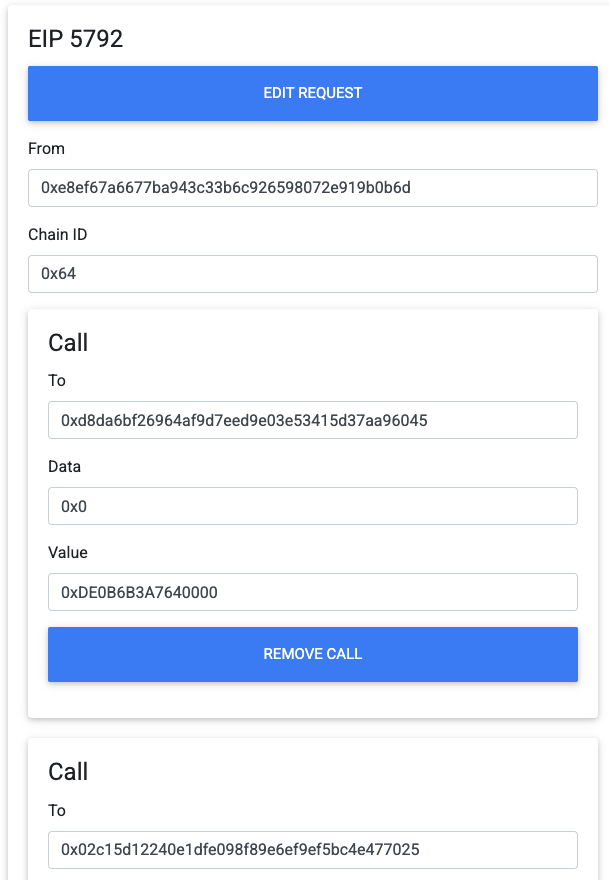
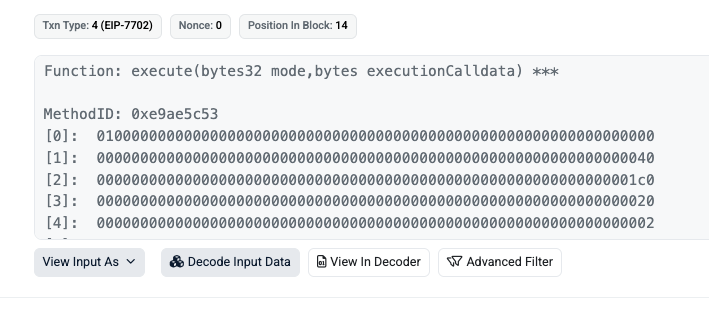
I lost my life savings in one click using @safe last night. That's after 8 years of holding ETH and avoiding scams. A UX bug within the official Bridge feature, implied the destination address was my Safe on Base. It wasn't. Essentially, due to the age of my Safe, a bad actor had exploited a window of time last year to deploy my Safe mainnet address on Base with a different owner address. Those bridged funds are now unrecoverable. I appreciate that Safe's staff have transparently explained to me that this was an extreme edge case and apologised. I'm in a lot of pain. I'm now praying that they can make me whole. cc: @koeppelmann @SchorLukas