Falcon8x retweetledi

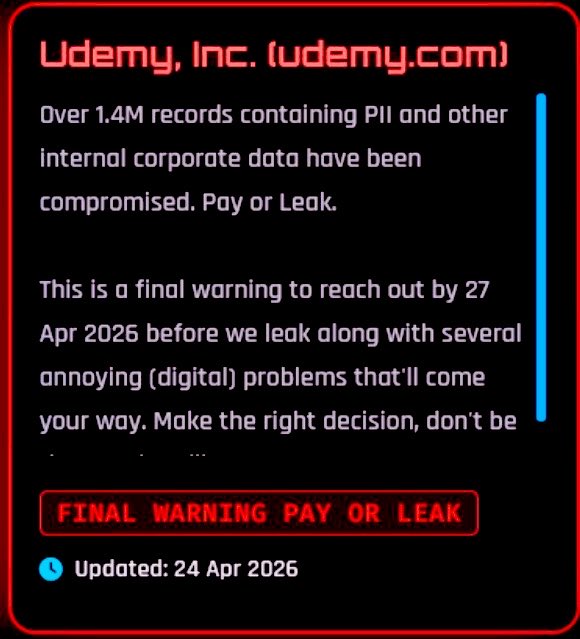
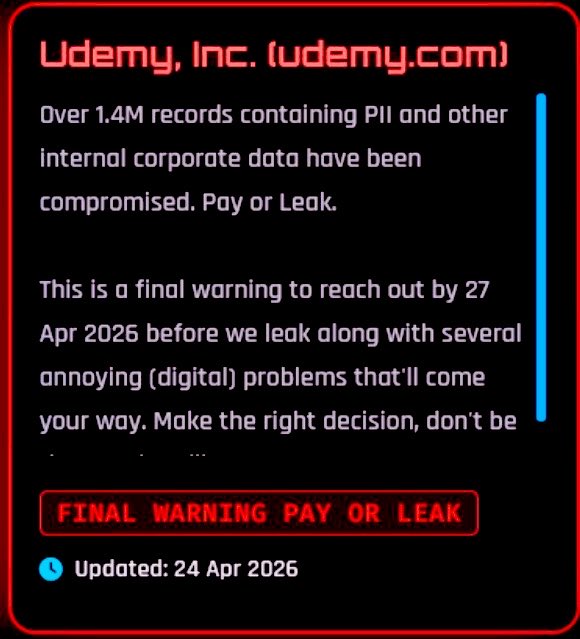
Udemy online educational platform has been breached by ShinyHunters
1.4 million alleged student records containing PII are being claimed @udemy
English
Falcon8x
1.7K posts


@flacon8x
Chasing dreams by night. Occasionally, I even chase after my own shadow.



🚨 BREAKING: The FBI has successfully extracted deleted Signal messages from a suspect's iPhone via notification storage, the place where all your notifications are stored for up to one month. Notification storage stores data from all messaging apps, it's a big flaw in iOS. But there's a way to turn it off...







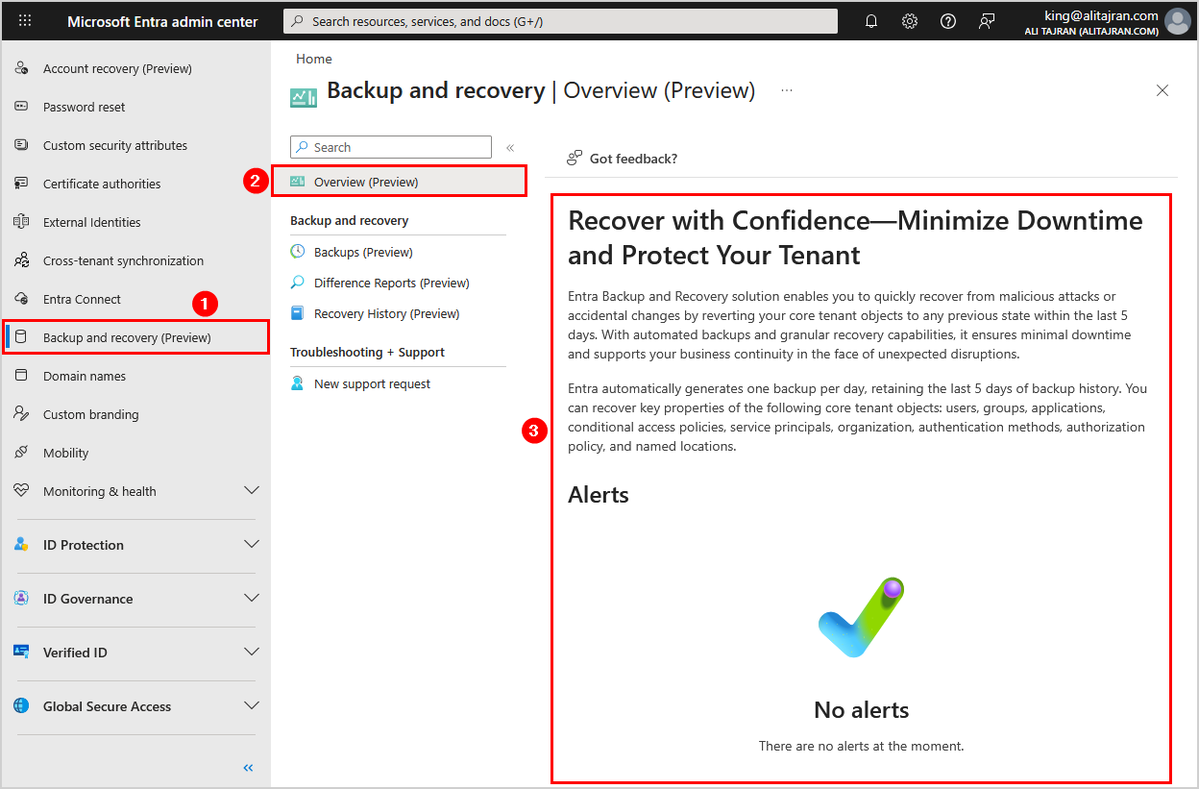



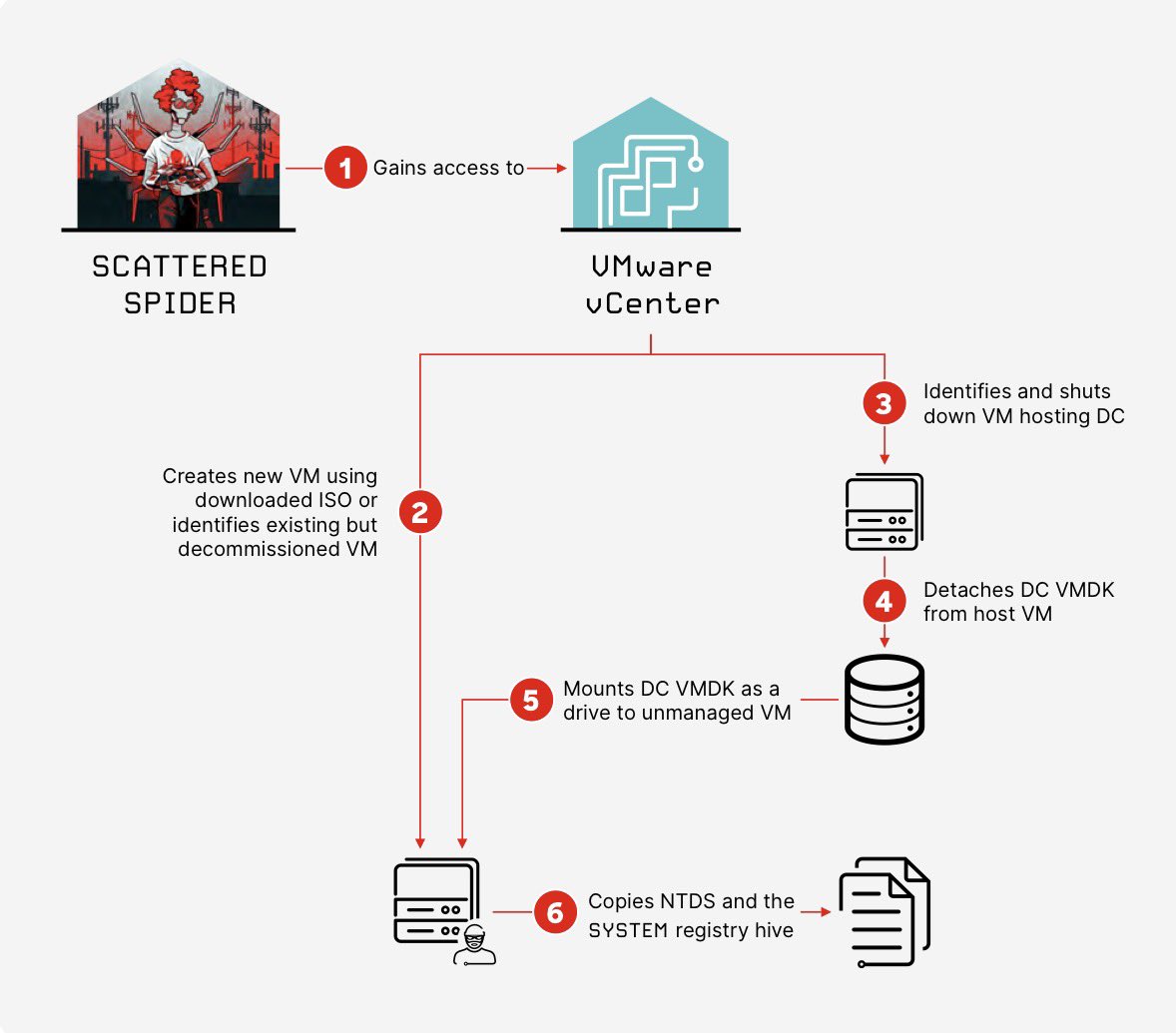
ICYMI: Was just perusing the latest CrowdStrike 2025 Threat Hunting report (crowdstrike.com/en-us/resource…) and check this wild timeline for Scattered Spider - from account takeover to Entra ID bulk user export in <5 minutes 👀





blocks matching [lang=*] regardless of whether it’s meant to be compatible, thus breaking original highlighting.
Terrible negligence and even more so that this made to prod while already flagged during beta.
Been a user for a long time but this will def push me to an alternative if not fixed soon.