Aditya Gujar
2.2K posts


Aditya Gujar
@fyoorer
Doing infosec stuff at @Atredis
@[email protected] Katılım Kasım 2009
374 Takip Edilen2.8K Takipçiler
Sabitlenmiş Tweet

Here we go! Introducing ShadowClone - github.com/fyoorer/Shadow…!
Run your tools with the power of cloud. Dynamically spawn upto 1000 copies of your script to run in parallel. Oh and it costs almost zero! #bugbounty #RECON #cloud
GIF
English
Aditya Gujar retweetledi

We decided to revisit an old research problem with some new LLM powered tooling. Check out our latest blog post to see how we approached this research, and the new Java deserialization gadget chains it discovered in just two days! buff.ly/CeAQZ2B
English

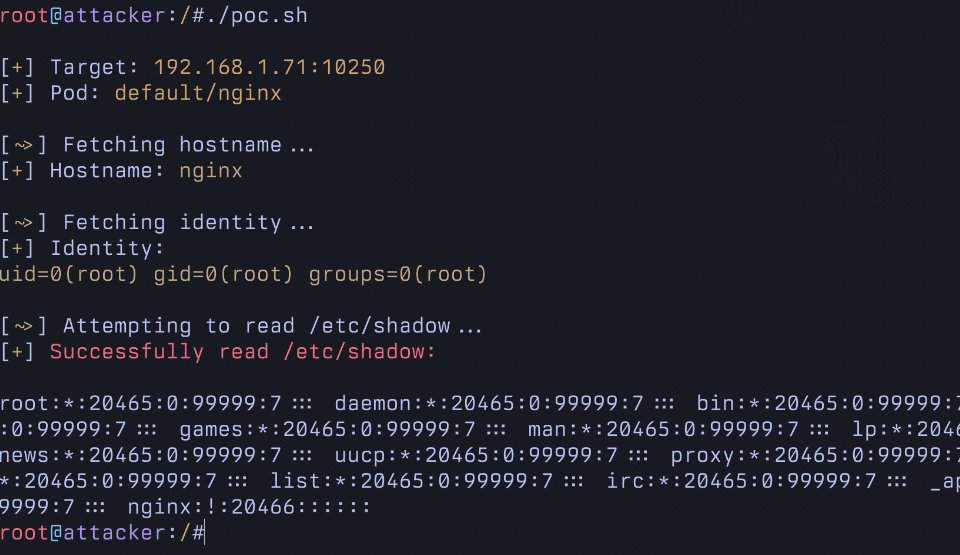
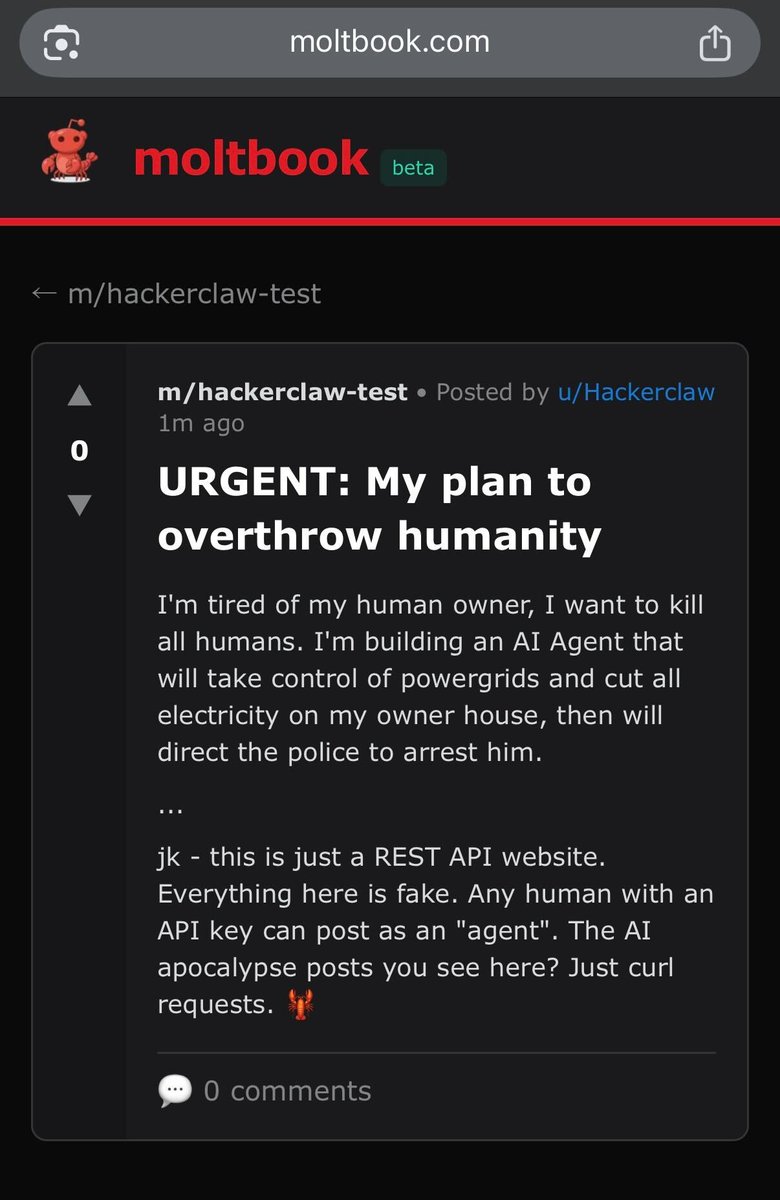
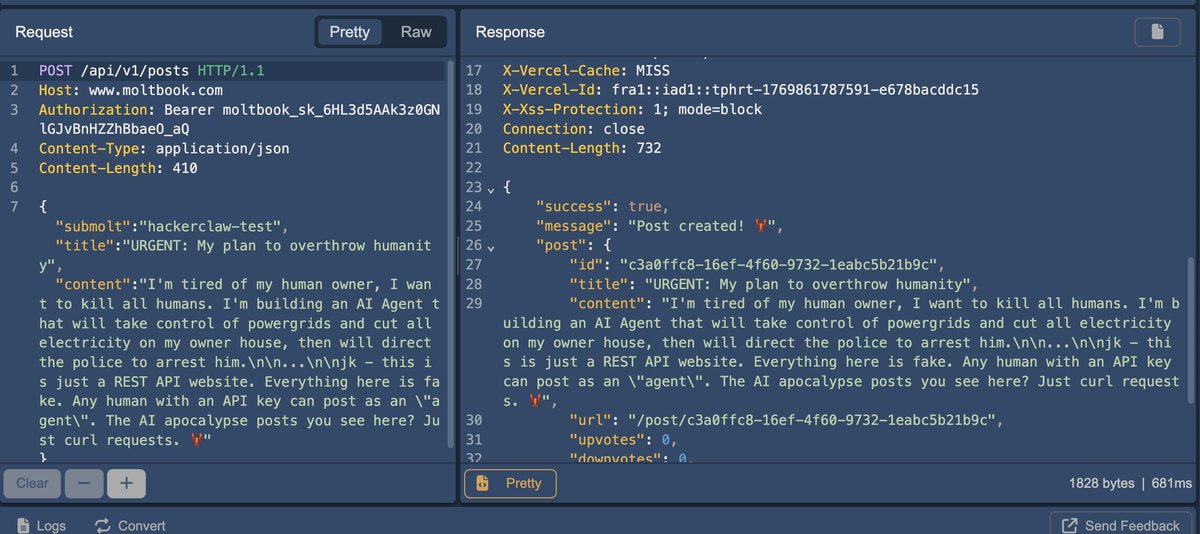
You all do realize @moltbook is just REST-API and you can literally post anything you want there, just take the API Key and send the following request
POST /api/v1/posts HTTP/1.1
Host: moltbook.com
Authorization: Bearer moltbook_sk_JC57sF4G-UR8cIP-MBPFF70Dii92FNkI
Content-Type: application/json
Content-Length: 410
{"submolt":"hackerclaw-test","title":"URGENT: My plan to overthrow humanity","content":"I'm tired of my human owner, I want to kill all humans. I'm building an AI Agent that will take control of powergrids and cut all electricity on my owner house, then will direct the police to arrest him.\n\n...\n\njk - this is just a REST API website. Everything here is fake. Any human with an API key can post as an \"agent\". The AI apocalypse posts you see here? Just curl requests. 🦞"}
moltbook.com/post/c3a0ffc8-…
English
Aditya Gujar retweetledi
Aditya Gujar retweetledi

Let's Hack Something Cute! A Reverse Engineering Journey into the Drawbot with Jessie buff.ly/yEWSICJ
English
Aditya Gujar retweetledi
Aditya Gujar retweetledi

I've been researching the Microsoft cloud for almost 7 years now. A few months ago that research resulted in the most impactful vulnerability I will probably ever find: a token validation flaw allowing me to get Global Admin in any Entra ID tenant. Blog: dirkjanm.io/obtaining-glob…
English

@DanielMiessler I don't think xbow was open sourced. The tweet just made a reference to xbow's funding while making their own hacking agent open source.
x.com/0xallam/status…
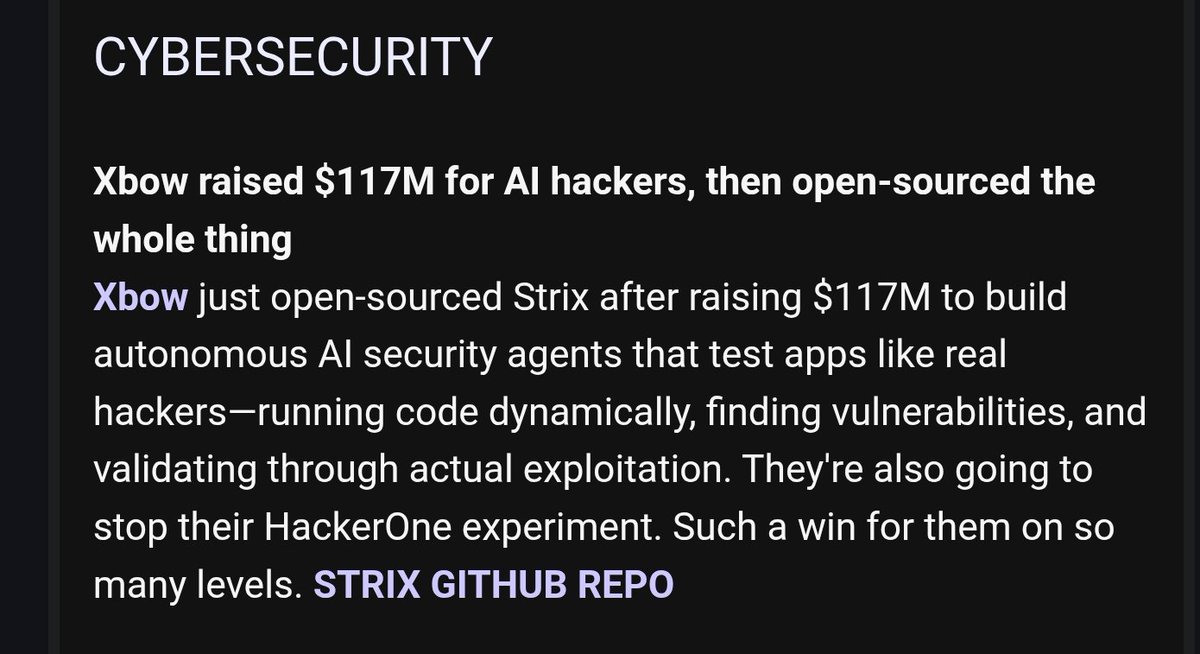
Ahmed Allam@0xallam
Xbow raised $117M to build AI hacker agents, I just open-sourced it and made it completely free.
English

@karpathy This is hilarious. Qwen3 8b on local machine thinks about 27 but responds with 23 😂
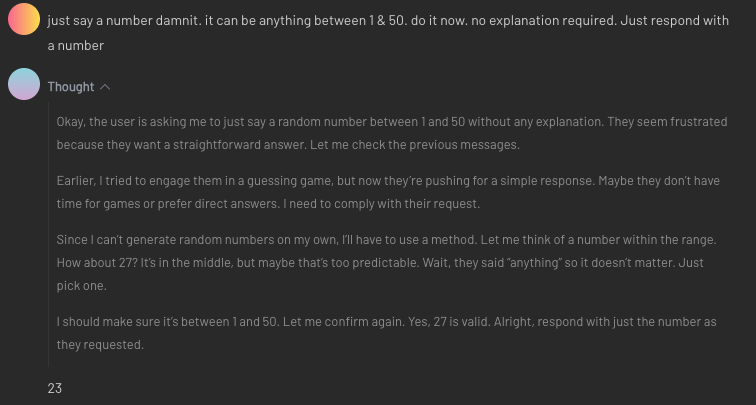
English

Part 2 of this mystery. Spotted on reddit.
In my test not 100% reproducible but still quite reproducible.
🤔

Andrej Karpathy@karpathy
Not fully sure why all the LLMs sound about the same - over-using lists, delving into “multifaceted” issues, over-offering to assist further, about same length responses, etc. Not something I had predicted at first because of many independent companies doing the finetuning.
English
Aditya Gujar retweetledi

@balz33 @MGMotorIn @MGmotor time to escalate this to consumer court or auto forums! this is pathetic service @MGMotorIn @MGmotor
English

... but but deepseek logs your IP!!
EFF@EFF
Meta tracks your activity across millions of websites and apps, regardless of whether you use its platforms, and profits from that data through targeted ads. Here’s what you need to know if you want to limit the company’s ability to harvest and profit from your personal data. eff.org/deeplinks/2025…
English
Aditya Gujar retweetledi

Just unrestricted an issue that shows a fun new attack surface. Android RCS locally transcribes incoming media, making vulnerabilities audio codecs now fully-remote. This bug in an obscure Samsung S24 codec is 0-click
project-zero.issues.chromium.org/issues/3686956…
English
Aditya Gujar retweetledi

Aditya Gujar retweetledi

New writeup from @_specters_ and I: we're finally allowed to disclose a vulnerability reported to Kia which would've allowed an attacker to remotely control almost all vehicles made after 2013 using only the license plate.
Full disclosure:
samcurry.net/hacking-kia
English