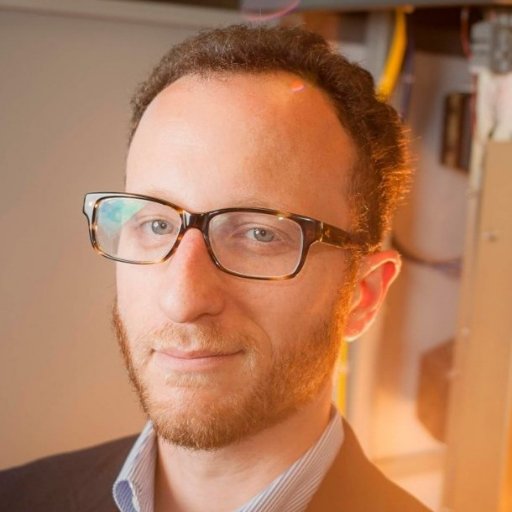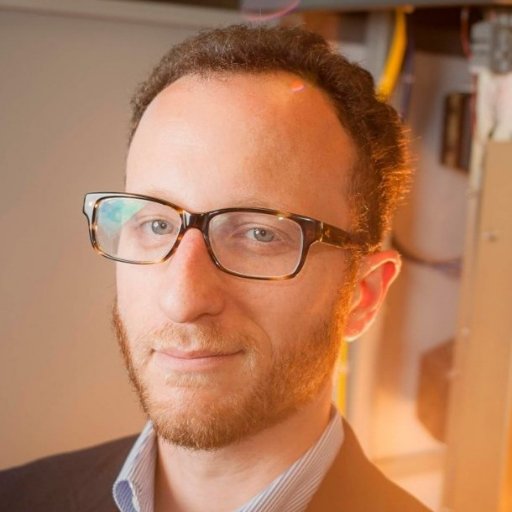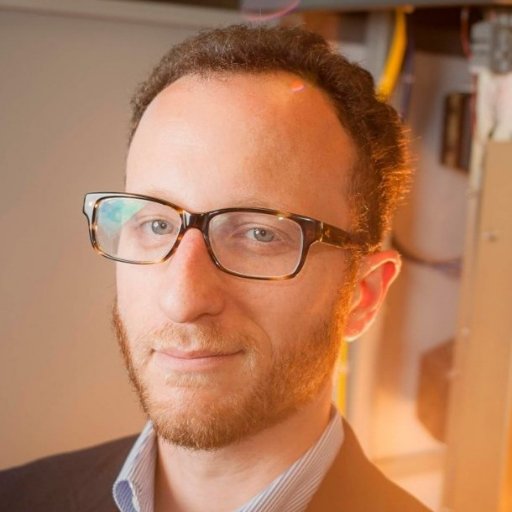
Congratulations to the Test of Time Award winner Hovav Shacham for The Geometry of Innocent Flesh on the Bone: Return-into-libc without Function Calls (on the x86)
Hovav Shacham
1.8K posts

@hovav
Looney Marxist UT professor poisoning the minds of young students about security, privacy, and tech policy.
Congratulations to the Test of Time Award winner Hovav Shacham for The Geometry of Innocent Flesh on the Bone: Return-into-libc without Function Calls (on the x86)

#IEEESecDev Congratulations to the 2022 IEEE Cybersecurity Award for Practice Winners Deian Stefan (@deiandelmars @ucsd_cse) and the team.




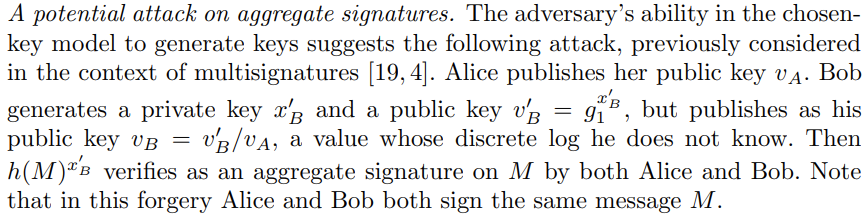

Craaaazy new exploit on smart wallets via BLS aggregations that @ethzed from @sigp_io presented today at @summit_defi You can provide a malicious pub key that sets the whole aggregation to zero and thereby validate anything 😲🤯 drive.google.com/file/d/1-sH-L5…