Shravan Ravi Narayan (Archived. Msg on mastodon)
62 posts
Shravan Ravi Narayan (Archived. Msg on mastodon)
@ShrNarayan
Archived account. Active on mastodon (@[email protected]). Asst Prof at UT Austin working on secure systems, PL-based & hw-based security.
Katılım Mayıs 2015
201 Takip Edilen369 Takipçiler
Sabitlenmiş Tweet
Hi all! Just a reminder that I'm looking for PhD students interested in building secure systems, security using type-systems & program analysis, and hardware-assisted security. UT Austin's app. deadline: Dec 15th.
cs.utexas.edu/graduate/prosp…
English
@KentonVarda @erikcorry Really neat! Fwiw, we contributed a similar approach of using MPK to eliminate wasted unmapped/guard pages for Wasm engines like Wasmtime some time back. Nice to see that we've arrived at similar designs :)
Our writeup from ASPLOS 2025 if you're curious shravanrn.com/pubs/seguecg.p…
English
@erikcorry If you ever thought: Hardware MPKs (Memory Protection Keys) sound cool but does anyone actually use them?
Well, we do!
blog.cloudflare.com/safe-in-the-sa…
English
Super-wonky blog post from @erikcorry and co. about how we're continually hardening the Workers Runtime. Some deep systems engineering here.
Erik@erikcorry
English
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

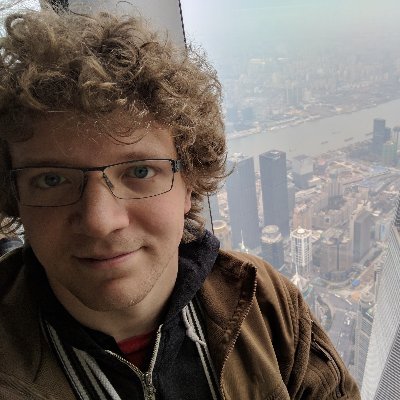
Microarchitectural unboxing: check out our new demo for breaking two factor authentication using iLeakage. Yes you heard it, speculative execution attacks on Apple’s M3 Macs and latest Safari that defeat Facebook’s 2FA over SMS.
ileakage.com

English
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

Congratulations to Assistant Professor Kazem Taram (@mktaram) at #PurdueCS for winning the 2023 @ACMSIGMICRO Dissertation Award.
➡️ purduecs.info/3QklqqW

English
@UmobiVictor Yup! The applications are open to all.
English

@ShrNarayan Hi Prof, is this opportunity open to international students?
English
Hi all! Just a reminder that I'm looking for PhD students interested in building secure systems, security using type-systems & program analysis, and hardware-assisted security. UT Austin's app. deadline: Dec 15th.
cs.utexas.edu/graduate/prosp…
English
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

To add to this: @ShrNarayan and I are very interested in co-advising students interested in security + PL!!! Please apply to UT if you are interested in these topics :)
Shravan Ravi Narayan (Archived. Msg on mastodon)@ShrNarayan
Hi all! Just a reminder that I'm looking for PhD students interested in building secure systems, security using type-systems & program analysis, and hardware-assisted security. UT Austin's app. deadline: Dec 15th. cs.utexas.edu/graduate/prosp…
English
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

My research on the thing I cannot talk about for another two weeks is nominated for the Pwnie Award "Most Innovative Research".
@DarkReading @PwnieAwards
darkreading.com/edge/meet-the-…
English
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

Excited to present “Half&Half: Demystifying Intel’s Directional Branch Predictors for Fast, Secure Partitioned Execution” at @IEEESSP, with @mktaram @ShrNarayan @deiandelmars Dean Tullsen.
English
Happy to share that RLBox (rlbox.dev) now uses upstream wasm2c (github.com/WebAssembly/wa…), vs. a custom fork of wasm2c to sandbox buggy libraries the Firefox browser (hacks.mozilla.org/2021/12/webass…)
@deiandelmars
@hovav
@MikeHommey
@bhology
@sbc100
@kripken
@keithwinstein
English
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

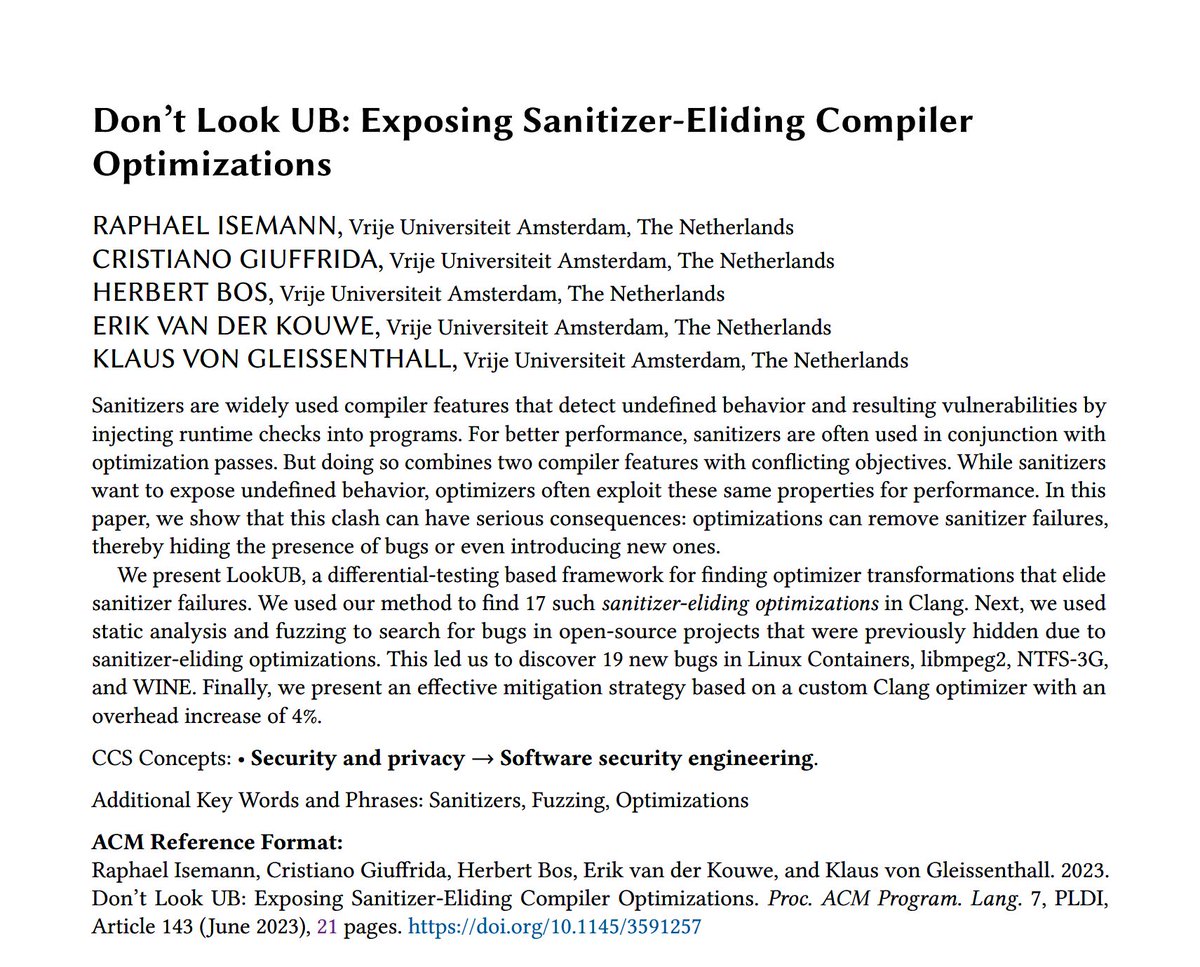
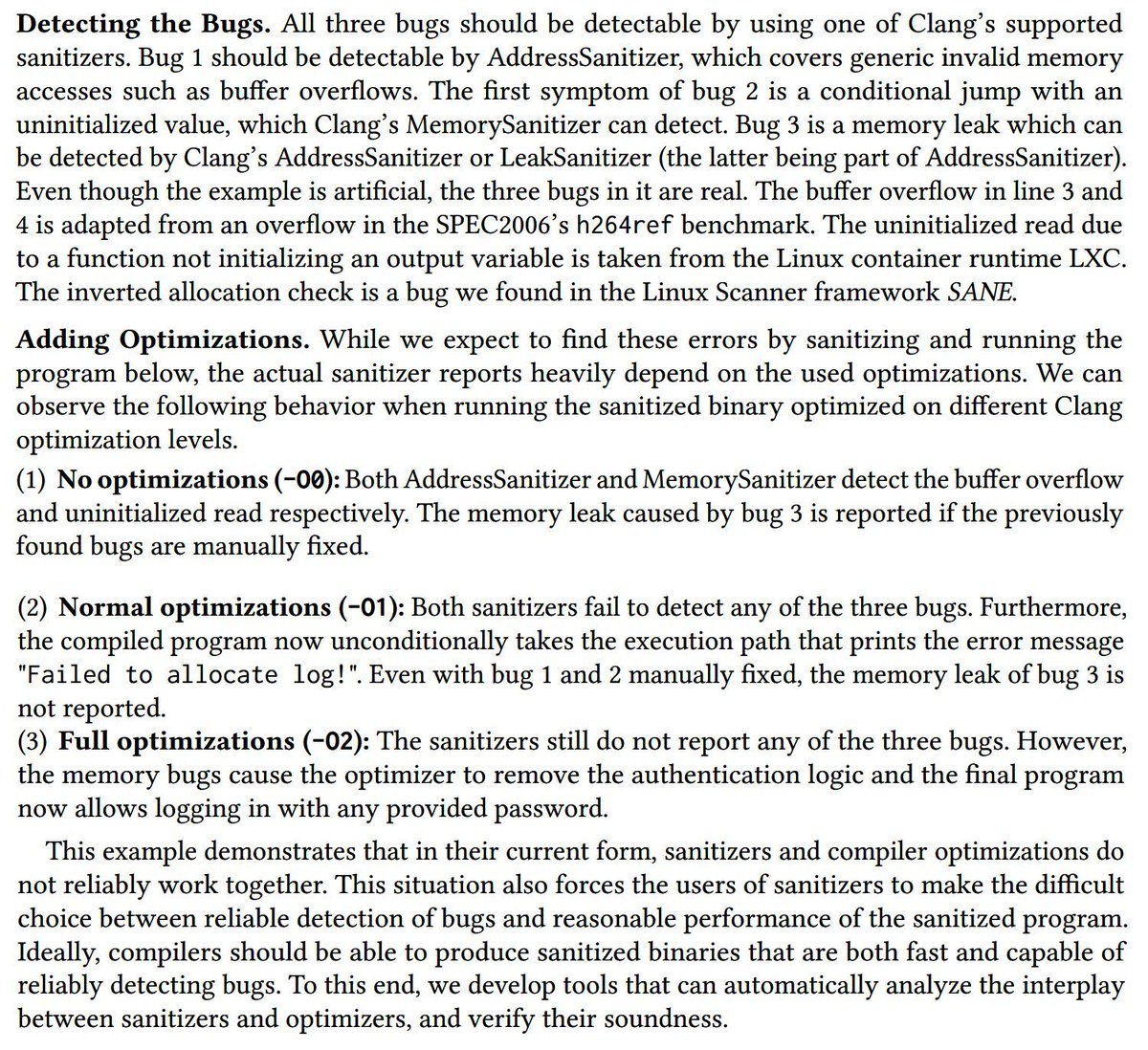
Don’t Look UB: Exposing Sanitizer-Eliding Compiler Optimizations
goto.ucsd.edu/~gleissen/pape…
Raphael Isemann, Cristiano Giuffrida, Herbert Bos, Erik van der Kouwe, Klaus von Gleissenthall
PLDI 2023


Nederlands
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

As it turns out, compilers happily spill the index for indirect jumps through a jump table after bounds checking, creating a TOCTTOU race for arbitrary control-flow hijacking. Check out our @HexHiveEPFL @IEEESSP "WarpAttack" paper: nebelwelt.net/files/23Oaklan…



English
Shravan Ravi Narayan (Archived. Msg on mastodon) retweetledi

Reminder: applications for PLDI 2023 student volunteers are still open for another 2 weeks: pldi23.sigplan.org/track/pldi-202…
Closing on Apr 10th AoE!
English
Happy to share that @ASPLOSConf has recognized our work with a distinguished paper award
twitter.com/ShrNarayan/sta…
Shravan Ravi Narayan (Archived. Msg on mastodon)@ShrNarayan
Excited to present "Going Beyond the Limits of SFI: Flexible and Secure Hardware-Assisted In-Process Isolation with HFI" at @ASPLOSConf, with @talgarfinkel @mktaram @shorterdisproof @flowyroll @evn_johnson Chris Fallin @ovahldy @lemaymd @rsahita Dean Tullsen @deiandelmars (1/6)
English
@ASPLOSConf @talgarfinkel @mktaram @shorterdisproof @flowyroll @evn_johnson @ovahldy @lemaymd @rsahita @deiandelmars Please join me at the talk in @ASPLOSConf next week to learn more!
Full paper: cseweb.ucsd.edu/~dstefan/pubs/… (6/6)
English
Excited to present "Going Beyond the Limits of SFI: Flexible and Secure Hardware-Assisted In-Process Isolation with HFI" at @ASPLOSConf, with @talgarfinkel @mktaram @shorterdisproof @flowyroll @evn_johnson Chris Fallin @ovahldy @lemaymd @rsahita Dean Tullsen @deiandelmars (1/6)
English
@ASPLOSConf @talgarfinkel @mktaram @shorterdisproof @flowyroll @evn_johnson @ovahldy @lemaymd @rsahita @deiandelmars Key to HFI's design is balancing the competing goals of
- an easy-to-adopt/simple µ-architectural implementation
- minimal kernel modification to support open and closed-source OSes
- flexible primitives for easy adoption by existing toolchains like wasm2c, wasmtime etc. (5/6)
English
@ASPLOSConf @talgarfinkel @mktaram @shorterdisproof @flowyroll @evn_johnson @ovahldy @lemaymd @rsahita @deiandelmars 3. Spectre safety: isolation can't be speculatively bypassed
4. Back compatible: can isolate existing unmodified binary code including dynamically generated code from JITs.
5. Zero-copy sharing: efficient buffer sharing between isolation domains (4/6)
English
@ASPLOSConf @talgarfinkel @mktaram @shorterdisproof @flowyroll @evn_johnson @ovahldy @lemaymd @rsahita @deiandelmars 1. Efficient isolation: zero-cost memory isolation for both 32bit (Wasm) and 64-bit (Wasm's memory64) address spaces.
2. Removing scaling limits: HFI removes the ~16K limit on Wasm instances per-process by eliminating virtual memory overheads (guard regions). (3/6)
English
@ASPLOSConf @talgarfinkel @mktaram @shorterdisproof @flowyroll @evn_johnson @ovahldy @lemaymd @rsahita @deiandelmars HFI aims to provide efficient, scalable, and spectre-safe hardware support for in-process isolation/WebAssembly. Compared to the current software-based approaches to implementing
in-process isolation/WebAssembly(Wasm), HFI offers many benefits. (2/6)
English
