Srinivasan retweetledi

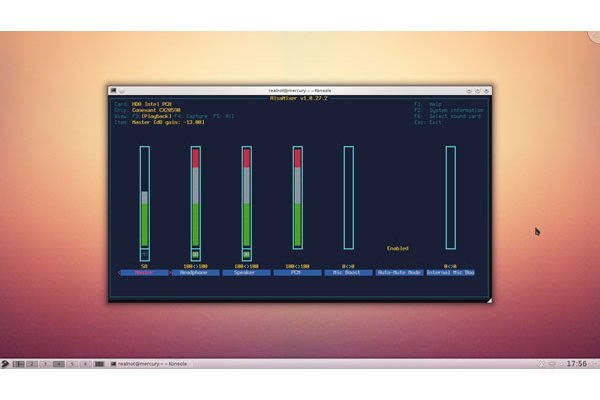
💻 France to Replace Windows with Linux on Government Desktops
Source: cybersecuritynews.com/france-replace…
France has taken a decisive step toward digital sovereignty, announcing plans to migrate government workstations from Microsoft Windows to Linux.
The move was formally declared during an interministerial seminar held on April 8, 2026, organized by the Interministerial Directorate for Digital Affairs (DINUM), the National Cybersecurity Agency of France (ANSSI), the Directorate General for Enterprises (DGE), and the State Procurement Directorate (DAE).
DINUM officially announced its exit from Windows, signaling a full migration to Linux-based workstations across state infrastructure.
#cybersecuritynews

English