Lisa
498 posts


Lisa
@itslisaram
Digital Surveillance & CTI | CS Engineering | #OSINT |





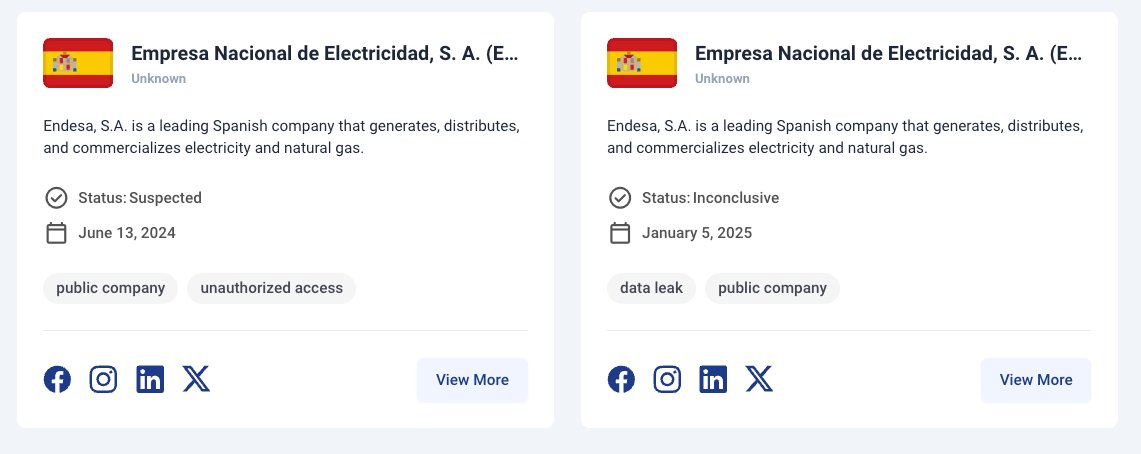
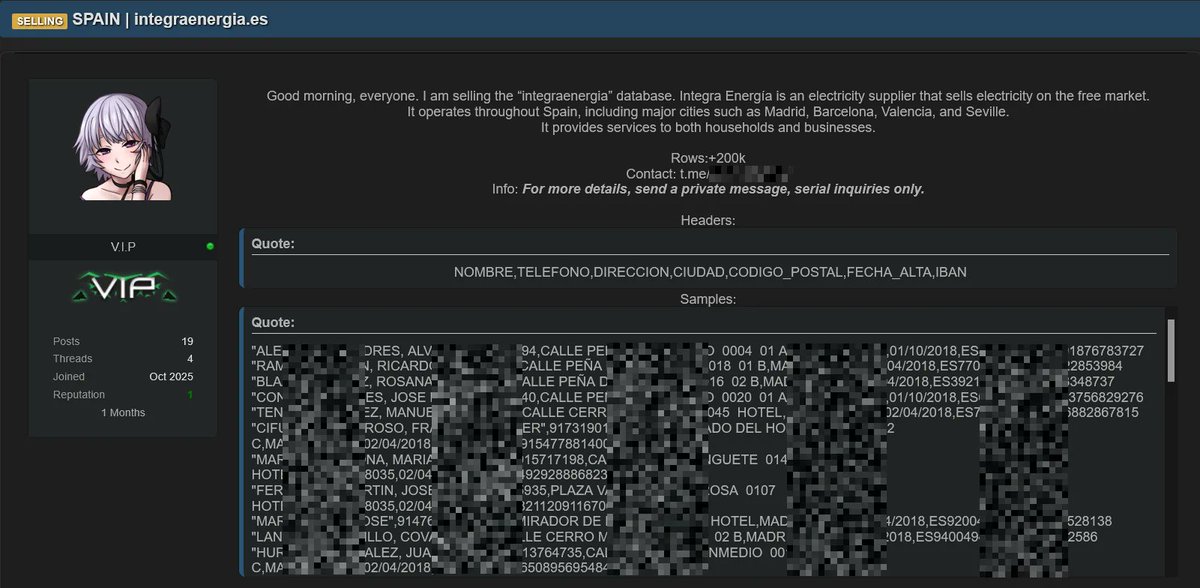
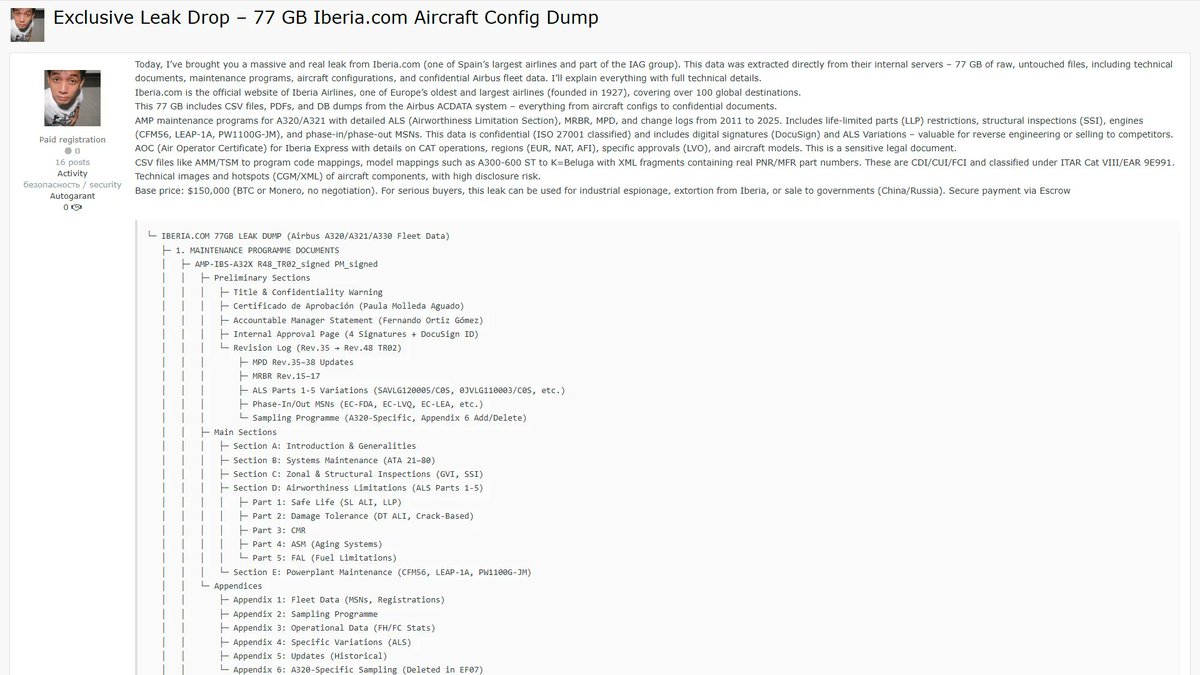
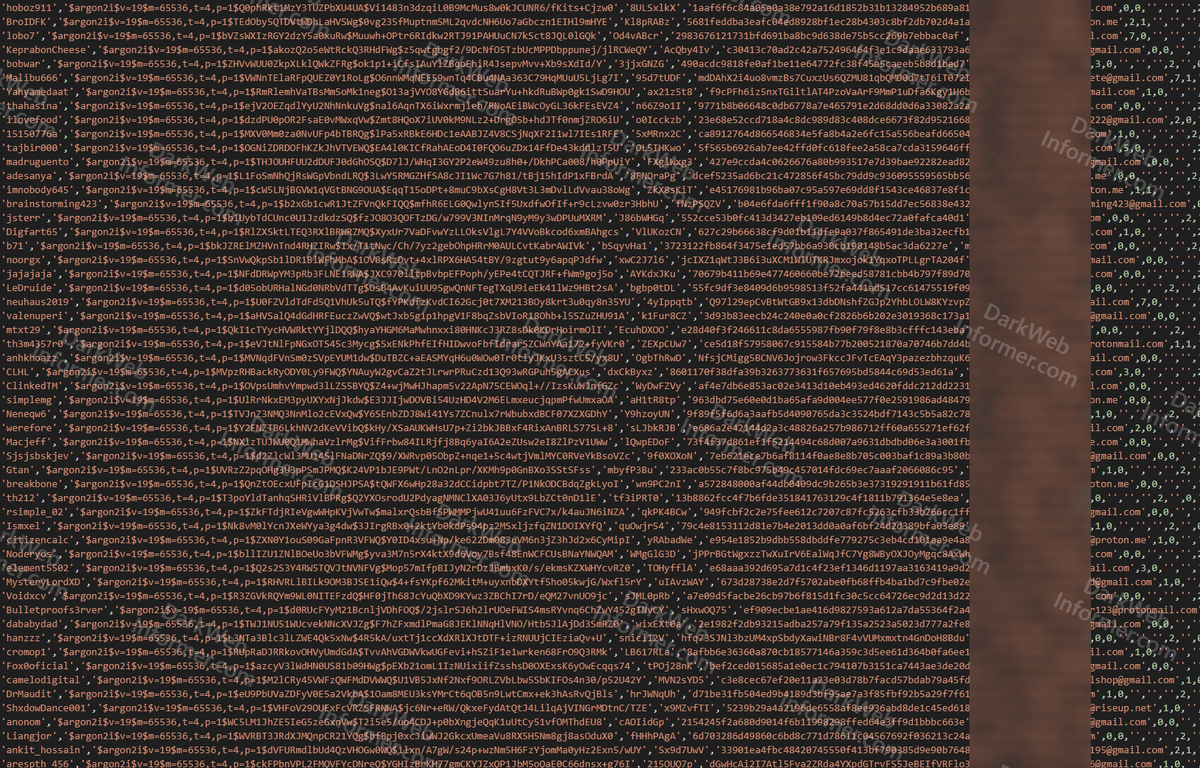
🚨Cyber Alert ‼️ 🇪🇸Spain - Endesa A threat actor known as “spain” claims to have breached Endesa and is selling an allegedly new and unique database containing data on over 20 million individuals. The dataset reportedly totals about 1.05 TB across multiple .sql files and includes sensitive information such as IBANs, national IDs, contact details, addresses, and customer and billing records. Sector: Energy / Utilities Threat class: Cybercrime Observed: Jan 05, 2025 Status: Pending verification — About this post: Hackmanac provides early warning and cyber situational awareness through its social channels. This alert is based on publicly available information that our analysts retrieved from clear and dark web sources. No confidential or proprietary data was downloaded, copied, or redistributed, and sensitive details were redacted from the attached screenshot(s). For more details about this incident, our ESIX impact score, and additional context, visit HackRisk.io.