
Jay Beale
4.3K posts


Jay Beale
@jaybeale
@InGuardians CEO, Bustakube, Peirates, IANS Faculty, BastilleLinux, #kubernetes @BlackHatEvents Trainer,#neurodivergent fam, he/him, [email protected]






All roads lead to self-hosting

Marcus Hutchins, the guy famous for stopping the WannaCry Ransomware, probably has the best take on Mythos doing vulnerability research










This is wild. theaustralian.com.au/business/techn…

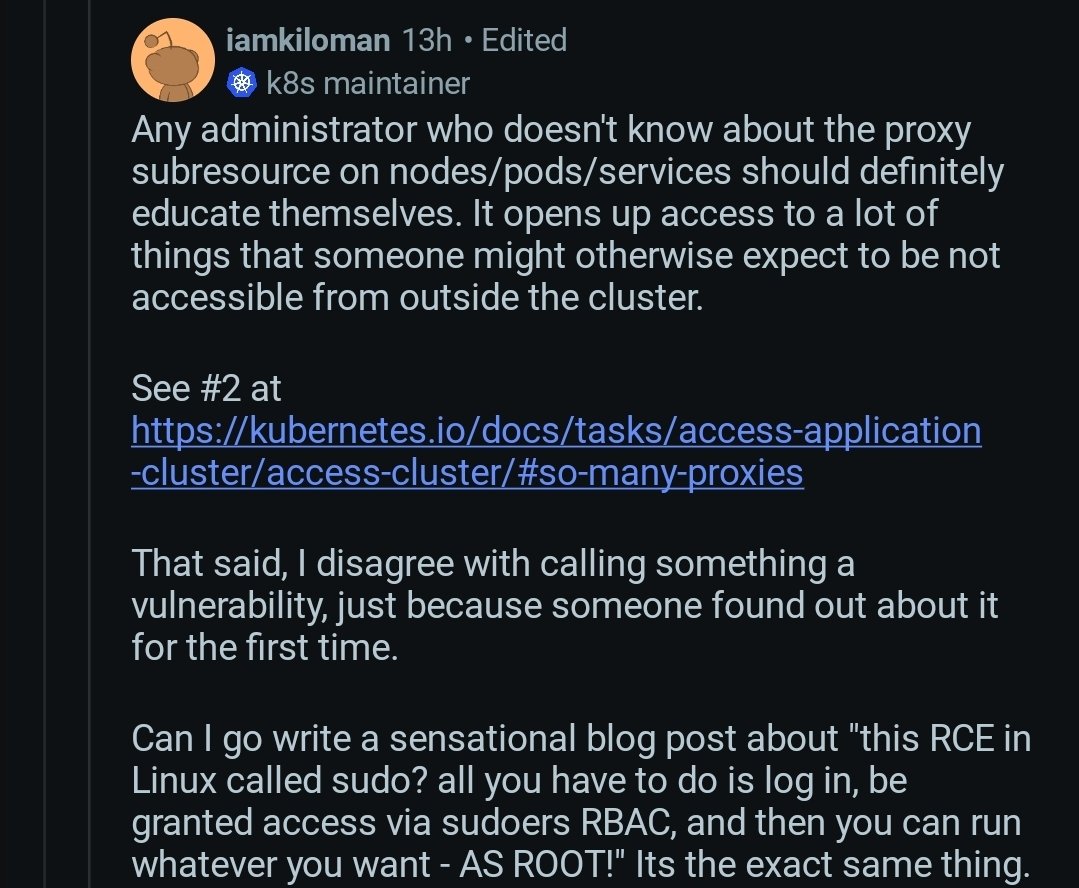
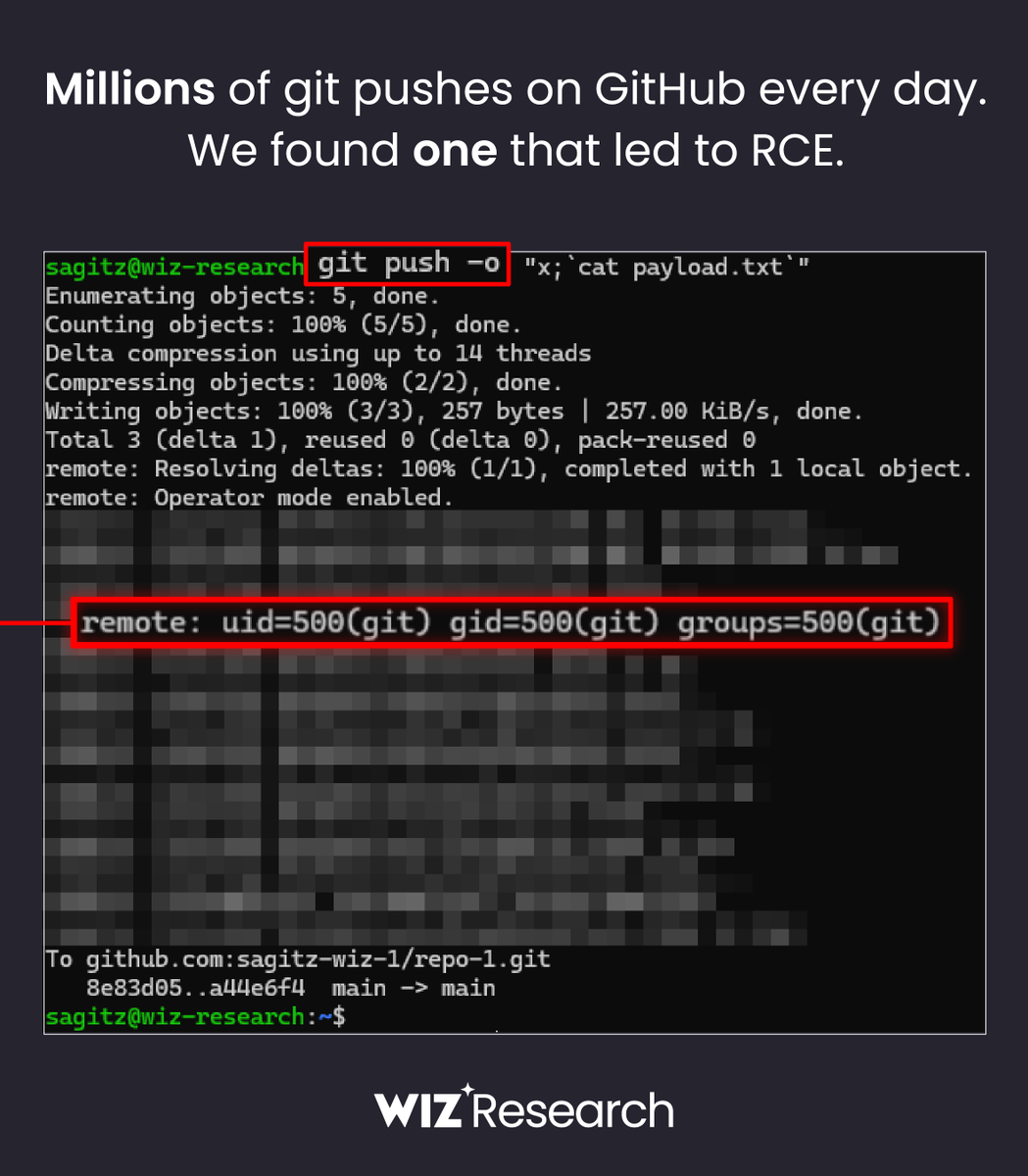
Excited to disclose my research allowing RCE in Kubernetes It allows running arbitrary commands in EVERY pod in a cluster using a commonly granted "read only" RBAC permission. This is not logged and and allows for trivial Pod breakout. Unfortunately, this will NOT be patched.


Excited to disclose my research allowing RCE in Kubernetes It allows running arbitrary commands in EVERY pod in a cluster using a commonly granted "read only" RBAC permission. This is not logged and and allows for trivial Pod breakout. Unfortunately, this will NOT be patched.

