Jesse Michael retweetledi
Jesse Michael
1.7K posts

Jesse Michael retweetledi

Time to talk about this one.
CopyFail (CVE-2026-31431) — a 732-byte Python script that roots every Linux distro shipped since 2017. 🧵
Brian Pak@brian_pak
a567d09b15f6e4440e70c9f2aa8edec8ed59f53301952df05c719aa3911687f9 👀
English
Jesse Michael retweetledi

Two guys ran an entire hacking operation in a PRISON for months
In 2015, two prisoners in Ohio were assigned to a recycling program where they dismantled old computers
Instead of scrapping the parts, they started stealing them
Carried components over 1,100 feet past guards, metal detectors, and multiple security checkpoints
Then built two working PCs and hid them behind a plywood board in the ceiling of a training room closet
They ran cables from the ceiling into the prison's own network
Stole login credentials from an employee by watching him type his password
Set up Bitcoin wallets, Stripe accounts, bank accounts and credit card applications using another inmate's stolen identity
Downloaded VPNs, the Tor browser, password cracking tools and what investigators called "a large hacker's toolkit"
Created fake security passes to access restricted areas of the prison
This entire operation ran for months
They only got caught because one of the computers used so much bandwidth it triggered an automatic alert
The Inspector General said it was "almost as if it's an episode of Hogan's Heroes"
Two guys with recycled computer parts and a ceiling tile built a cybercrime operation inside a state prison




English
Jesse Michael retweetledi

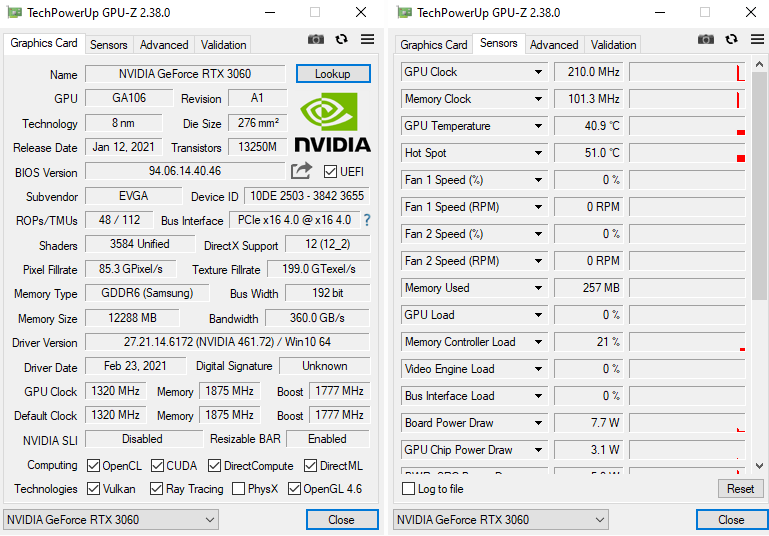
GPU-Z is on basically every gaming PC on earth. TechPowerUp makes it. they also make Sapphire TRIXX. What I found is insane...
both ship TRIXX.sys. IOCTL 0x800060C4 calls HalSetBusDataByOffset with user-controlled bus, device, function, and offset. any local process. no admin.
reprogram any PCI BAR to any physical address. map it. arbitrary physical memory R/W from ring 3.
a GPU info tool with the keys to your entire system. EV cert. valid through April 2028.
English
Jesse Michael retweetledi

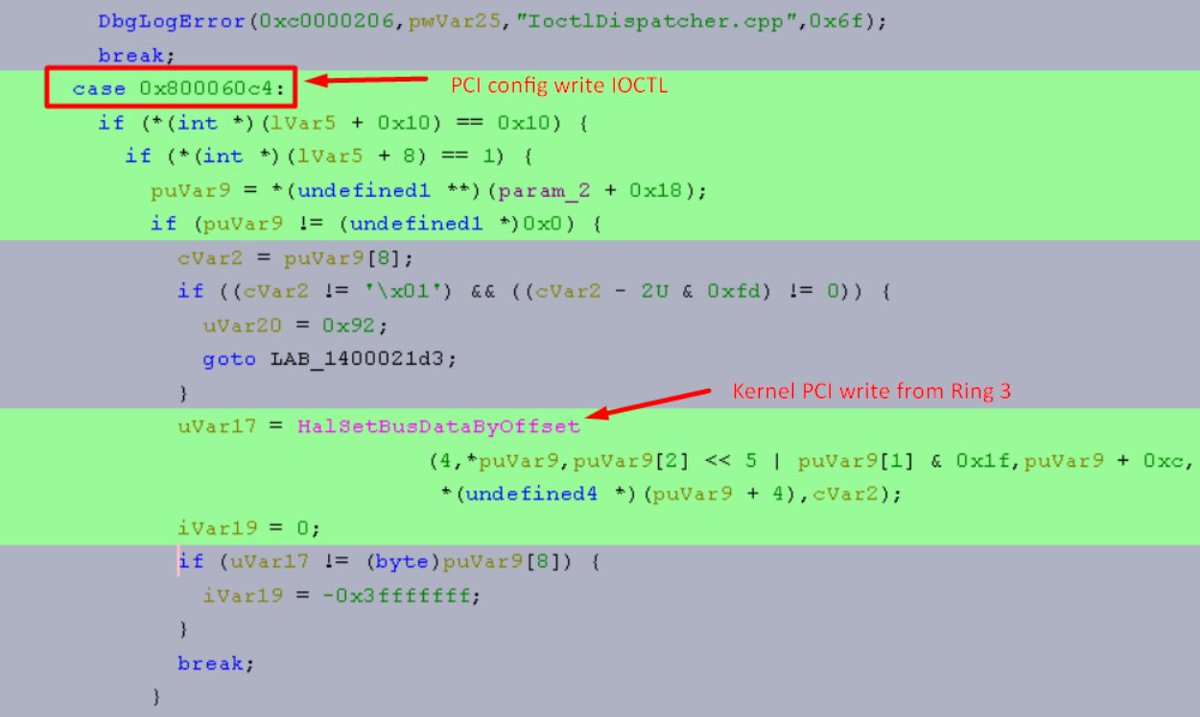
Signed to Kill: Reverse Engineering a 0-Day Used to Disable #CrowdStrike EDR
The article presents a reverse-engineering analysis of a kernel driver used in a BYOVD (Bring Your Own Vulnerable Driver) attack to disable security software, including @CrowdStrike Falcon EDR. The researcher discovered multiple variants of a Microsoft-signed driver that expose a dangerous IOCTL interface capable of terminating arbitrary processes.
core-jmp.org/2026/04/signed…
English
Jesse Michael retweetledi
Jesse Michael retweetledi
Jesse Michael retweetledi

In our latest post, researcher @craigsblackie documents attacks against the Dell UEFI firmware that enable DMA attacks against TPM-only bitlockered devices mdsec.co.uk/2026/03/disabl…

English
Jesse Michael retweetledi

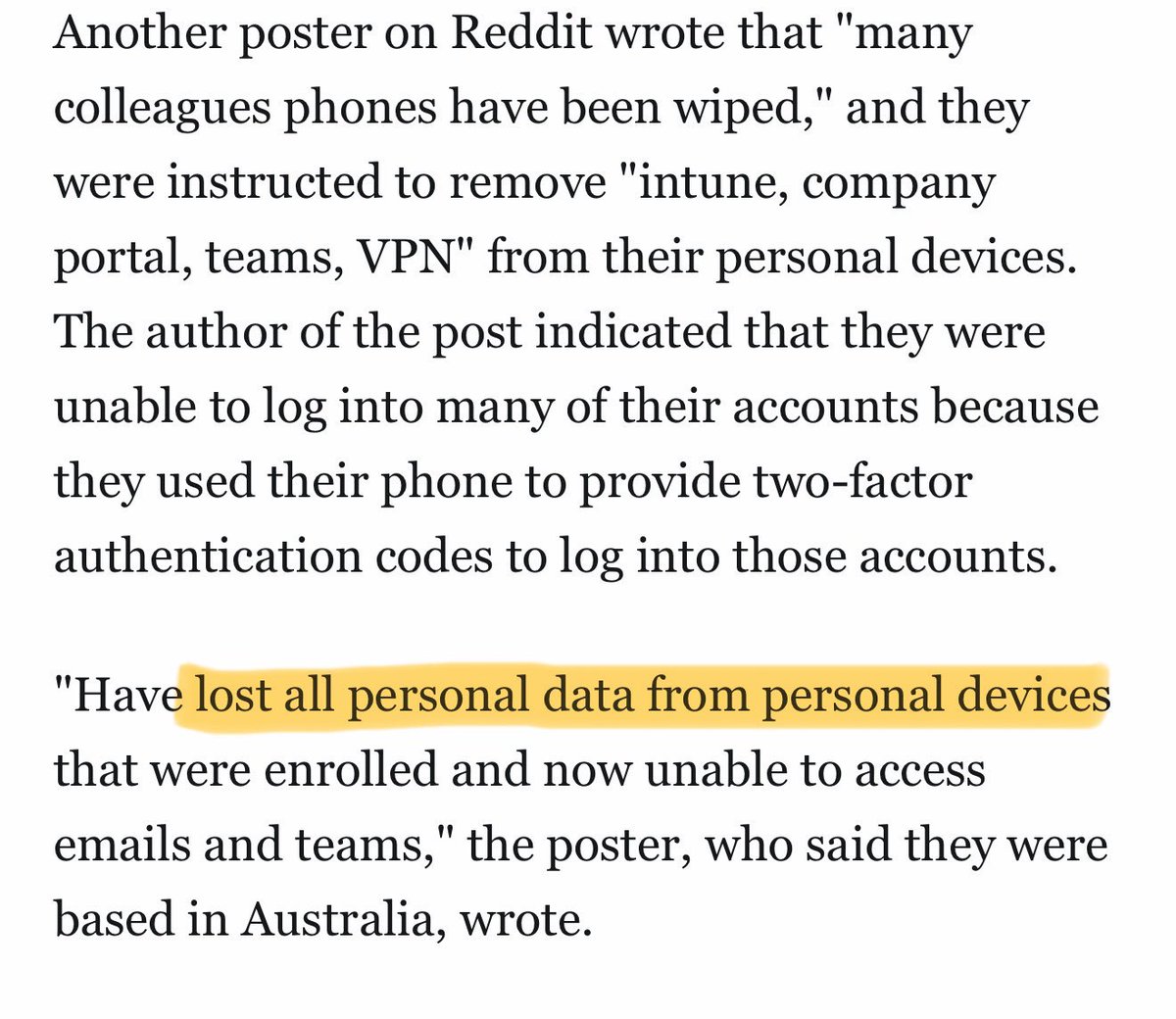
If you use a personal phone/laptop for your work, pay very close attention to this little detail.
Iran attackers wipe 200k devices at a company called Stryker. Within those devices appears to be employees PERSONAL devices.
The attackers used the company’s MDM software, which is basically IT management software running on everything. It’s an incredibly attractive backdoor to an attacker. I successfully targeted MDM software for several Red Team engagements. It’s… lots of fun :)
Anyway, a lot of companies require you to install their MDM software on your personal devices before you can access resources like Corp email. It’s used to keep devices updated, lock things down if they get stolen, etc. The company often promises that they won’t access personal data, erase any personal data, etc. But this is often ONLY POLICY. If a bad actor gains access to the MDM tool, as was the case here, then anything can happen.
People should be aware of these risks. I refused to run MDM software on any of my personal devices. The company needs to provide me with hardware if they want that. I personally isolate all corp devices to their own network too. If an adversary can get into the corp laptop, then can then get inside my network… there have been cases of it happening in the past.
Kim Zetter@KimZetter
I've published more details about the cyberattack in this piece: zetter-zeroday.com/iranian-hackti…
English
Jesse Michael retweetledi

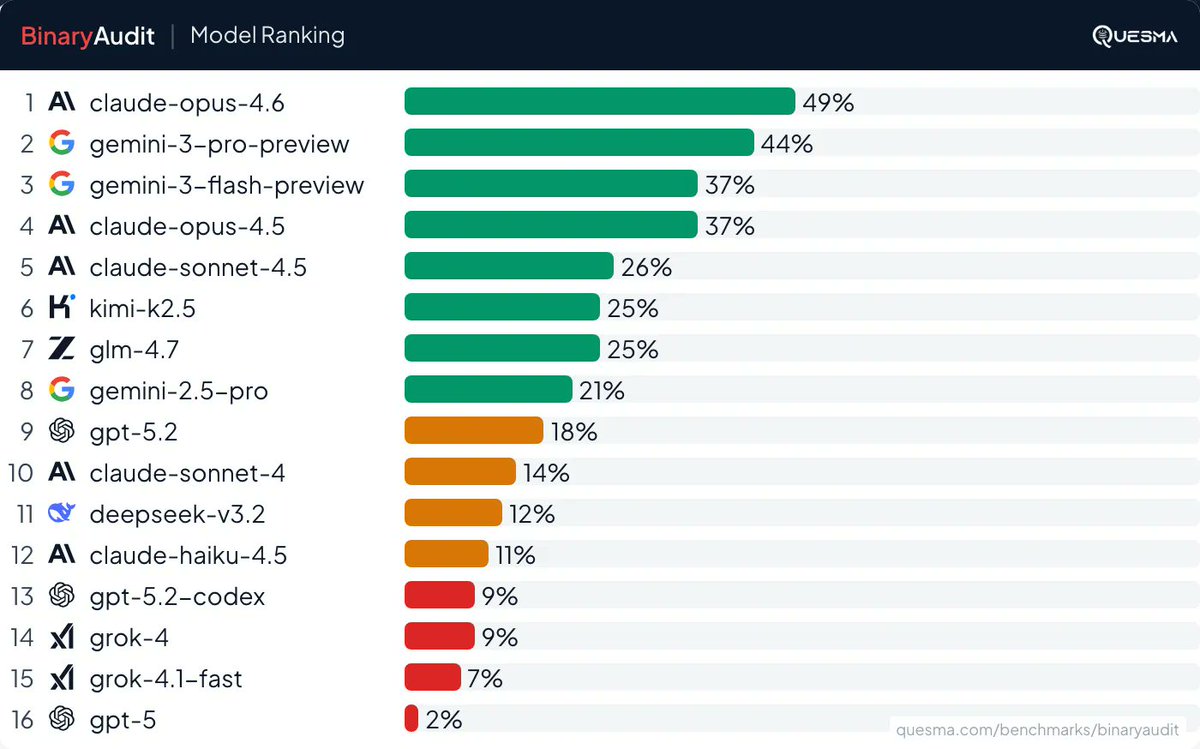
Claude can code, but can it read machine code?
We gave AI agents access to Ghidra (a decompiler by the NSA) and tasked them with finding hidden backdoors in servers - working solely from binaries, without any access to source code.
See our BinaryAudit: quesma.com/blog/introduci…
English
Jesse Michael retweetledi

Squeee so excited 😍😍😍 @Blackhoodie_RE will be at @DistrictCon next year, on January 23rd @SynapticRewrite and I will teach a day of Reverse Engineering for Vulnerability Discovery, registration is now open blackhoodie.re/DistrictCon202…
English
Jesse Michael retweetledi
Jesse Michael retweetledi

Watch XOR’s talk CUDA de Grâce: Owning AI Cloud Infrastructure with GPU exploits
Kernel + driver bugs aren’t just a LPE problem, they’re a cloud problem. With the explosion of AI in the cloud, NVIDIA’s GPU drivers have become a valuable attack surface
youtu.be/Lvz2_ZHj3lo

YouTube
English
Jesse Michael retweetledi

A ton of great info here about what Apple does for their secure boot chain: “A Reverse Engineer’s Anatomy of the macOS Boot Chain & Security Architecture” stack.int.mov/a-reverse-engi…
English
Jesse Michael retweetledi
Jesse Michael retweetledi
Jesse Michael retweetledi
Jesse Michael retweetledi

#ESETresearch has discovered #HybridPetya ransomware on VirusTotal: a UEFI-compatible copycat of the infamous Petya/NotPetya malware. HybridPetya is capable of bypassing UEFI Secure Boot on outdated systems. @smolar_m welivesecurity.com/en/eset-resear… 1/8
English
Jesse Michael retweetledi
Jesse Michael retweetledi