Shane Curran@arcurn
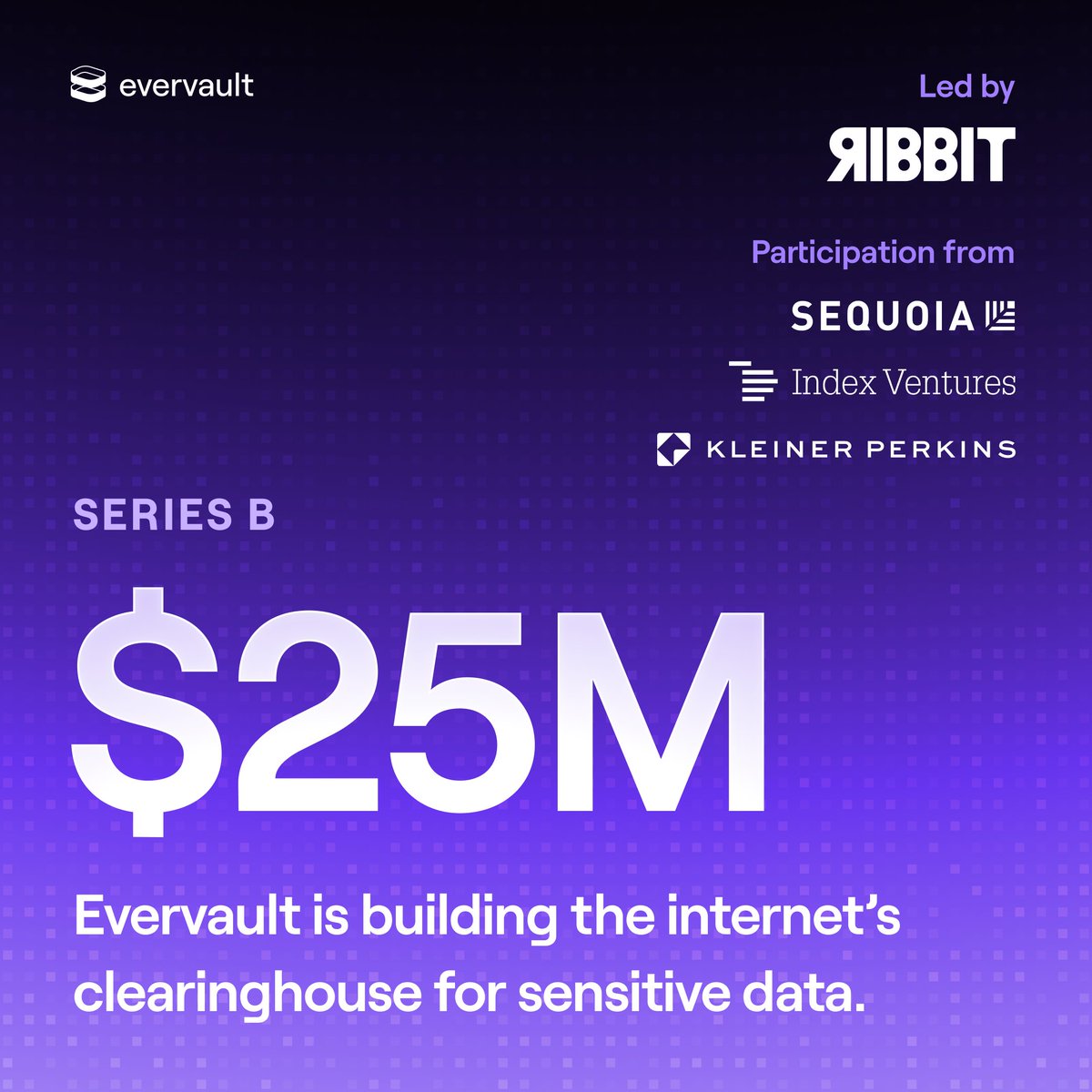
Today, we’re excited to announce @Evervault's $25M Series B, led by Ribbit Capital with continued support from @sequoia, @IndexVentures, @kleinerperkins, and @nextplayVC.
This round comes at a time when sensitive data exchange on the web is going parabolic. Since 2019, we’ve been focused on building durable infrastructure for engineering teams to collect, process, share, and enrich sensitive data -- while keeping it encrypted at all times.
We thought we were making good progress in encrypting the web, helping customers like @tryramp, @Rippling, @finix, @TheOverwolf, @Uniswap, @CarTrawler, and hundreds of others secure more than $5bn/year in payment flows and 100m+ unique tokens per month. But the past year has shown that our enemy -- plaintext data -- is getting stronger and more pervasive.
Our vision is to build the clearinghouse for sensitive data, helping companies exchange sensitive data in a secure and encrypted way. This round helps us encrypt more of the web by further refining our developer experience, building deeper integrations with trusted third-parties, and increasing the value we can offer our customers for more data types.
First and foremost, thank you to our customers. You trusted Evervault to sit directly in the flow of your most sensitive data (payments, identity, financial information, and more) and that trust is not something we take lightly. Your feedback, your requirements, and the problems you bring to us every day are what shape the product and push us forward.
Thank you to the Evervault team. What you’ve built is genuinely special: infrastructure that lets developers process sensitive data without ever having to see it in plaintext. The pace, craft, care, and ambition you bring to work every day are what makes this company what it is.
And thank you to our new investors for believing in the vision of making security architectural rather than procedural. We’re grateful to have partners who understand both the scale of the problem and the opportunity ahead.
The internet still assumes that sensitive data must exist in plaintext somewhere. We’re building the infrastructure to change that.
Onwards!
More here 👉 evervault.com/blog/series-b?…