Ricardo Monreal
10.5K posts

@joy_dragon
I am, whatever you say I am.







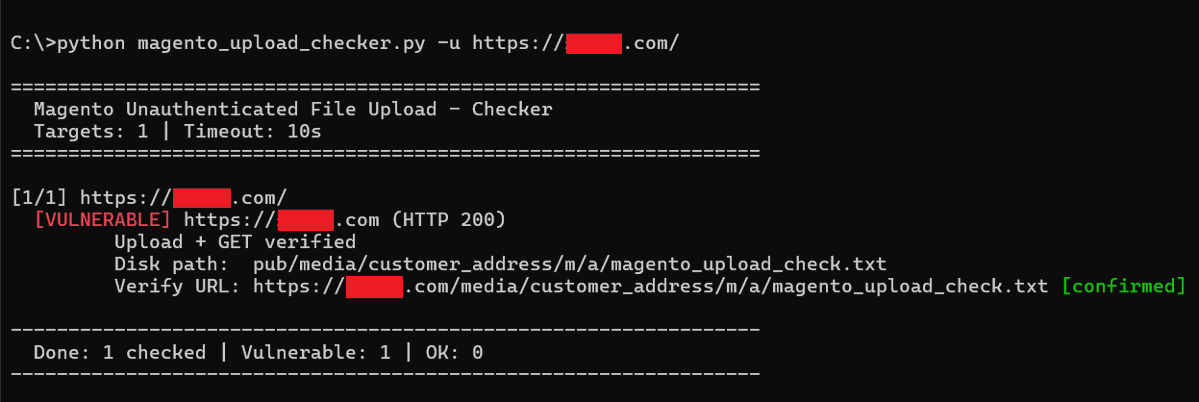
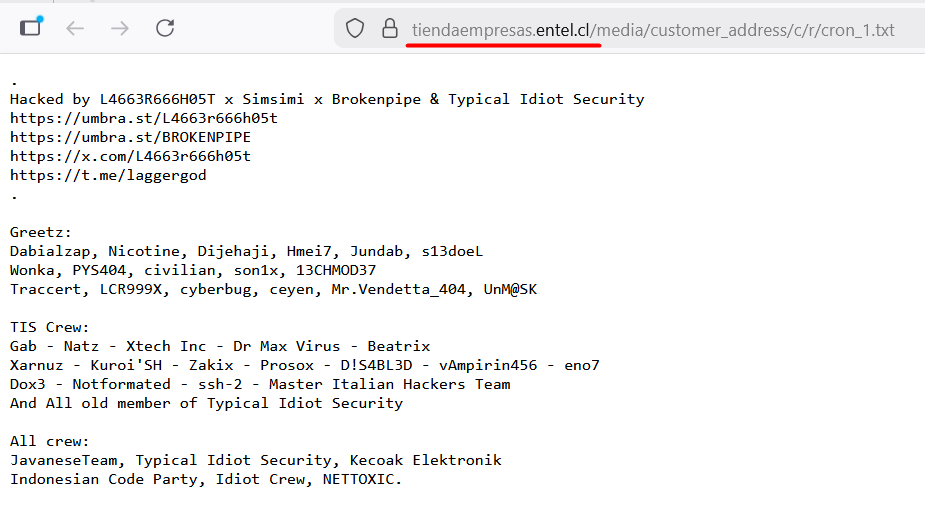
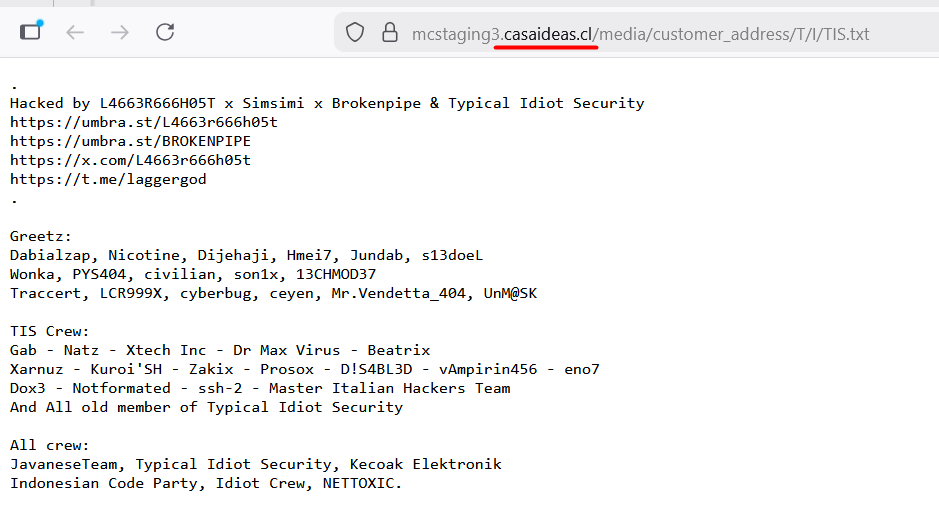
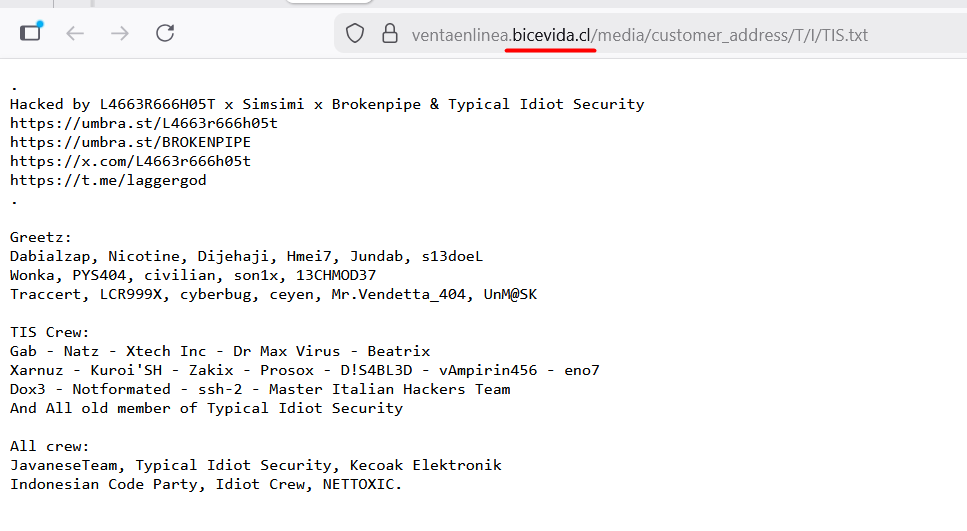
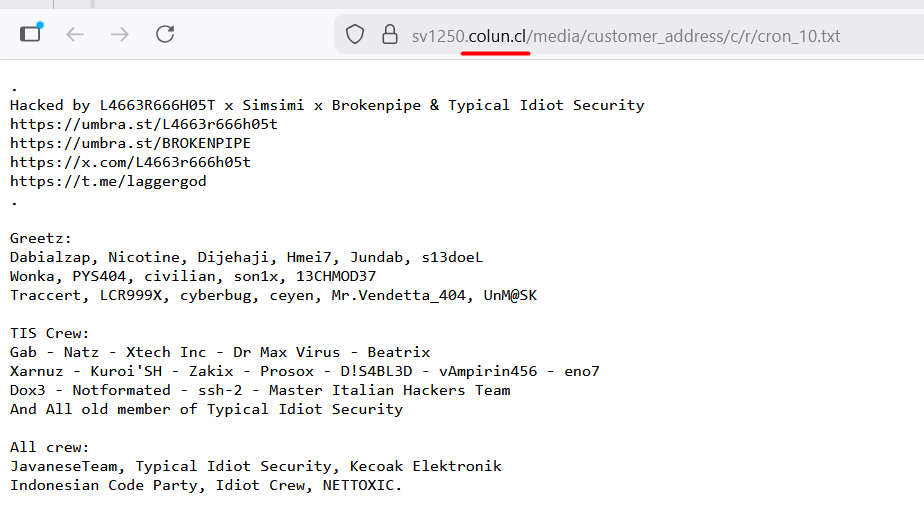
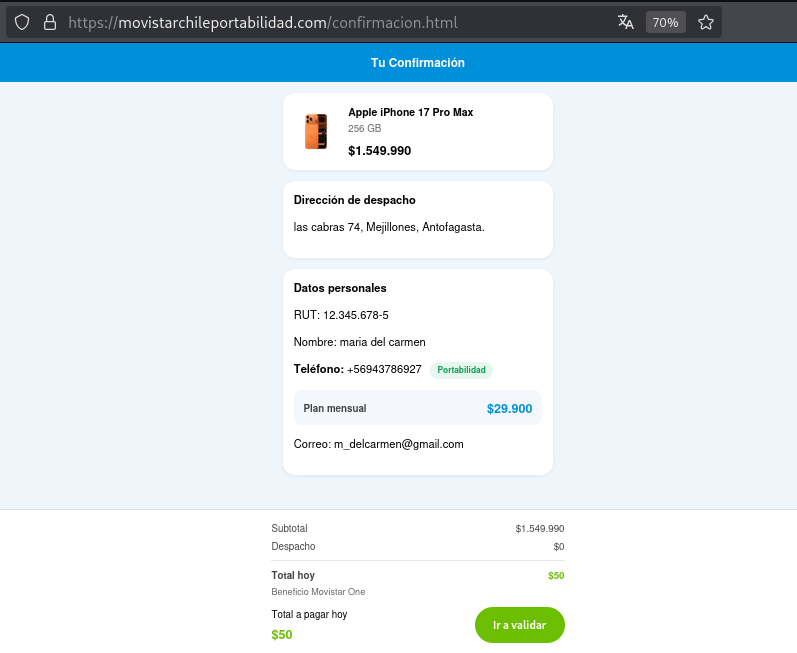
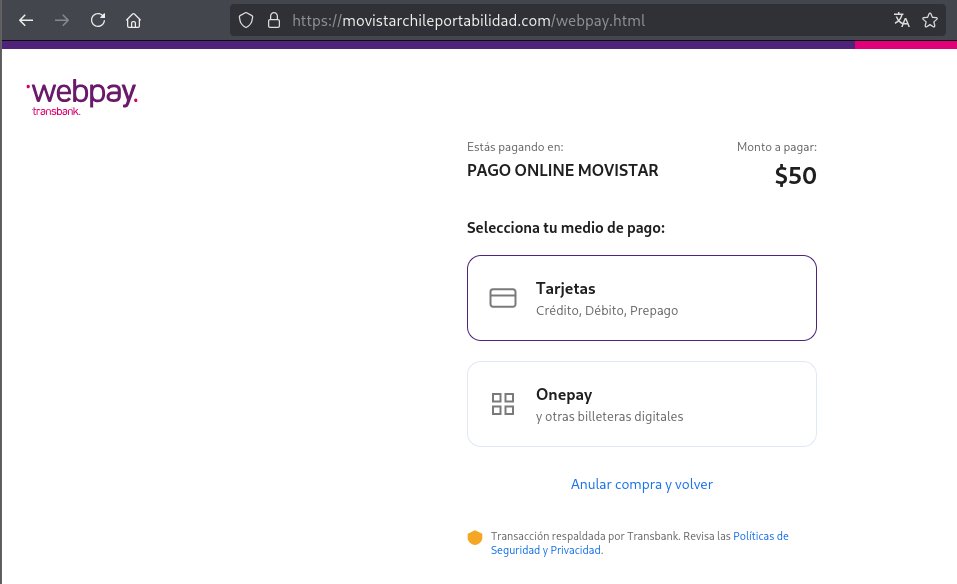
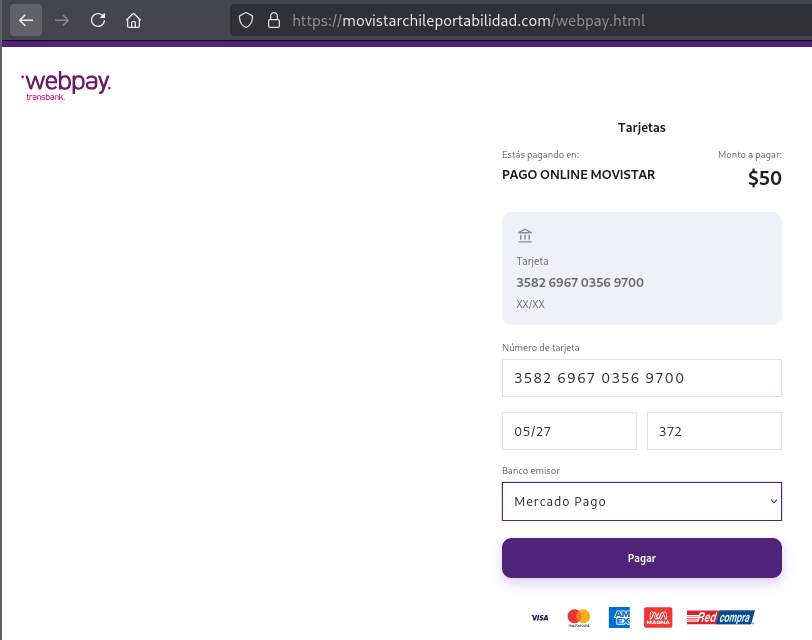
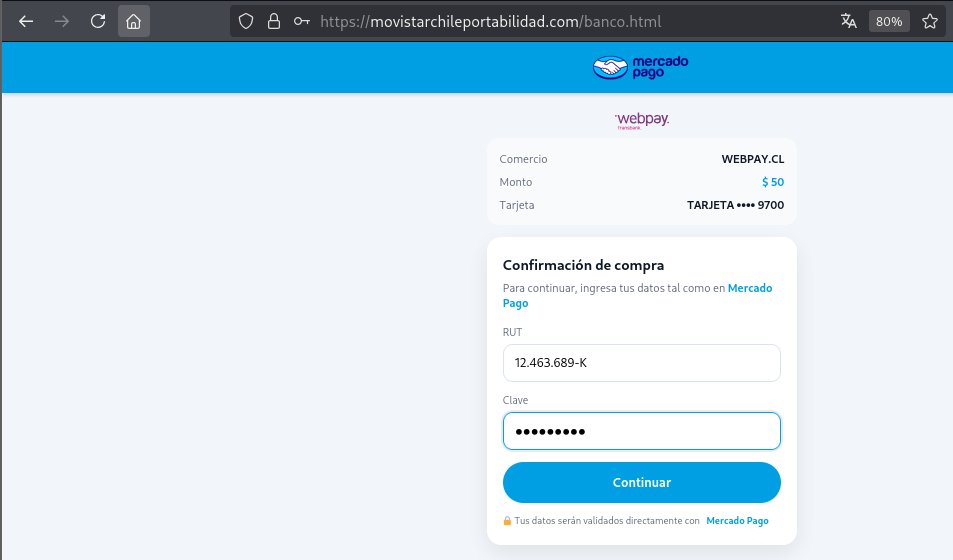
🚨 Mientras tanto, una ola de ataques contra tiendas Magento compromete múltiples sitios web en Chile 🇨🇱 Entre los afectados hay sitios de Entel, Bice Vida, Colun, A3D, CasaIdeas, Volcom, Everlast, Anticipa, Tiendas PF, Maui&Sons, Fila, RipCurl, Stone Center, etc 🤷♂️ Por ahora, solo se ve "subida de archivos" TXT, pero... H/T @joy_dragon 🦾

GORE Araucanía interpuso querella por ciberataque que robó información de Oficina de Partes #Cooperativa90 tinyurl.com/35eb7vp9




Best practices for securing Microsoft Intune techcommunity.microsoft.com/blog/IntuneCus…

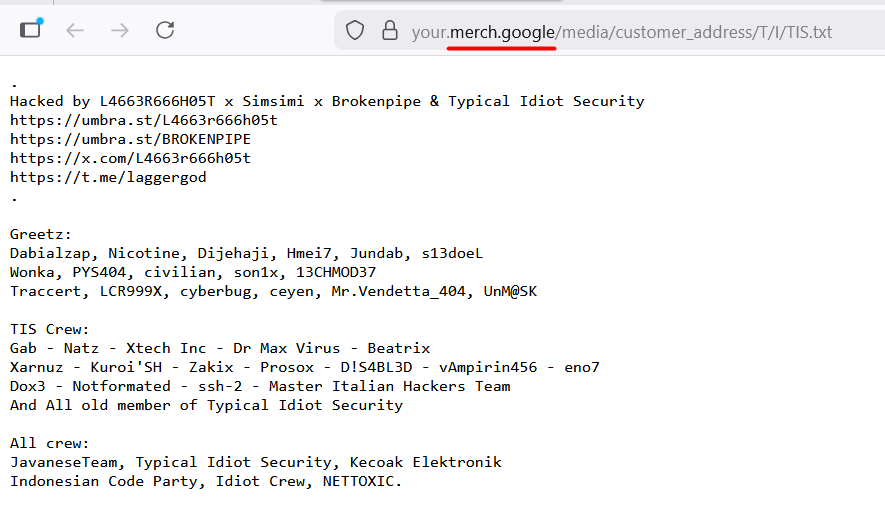
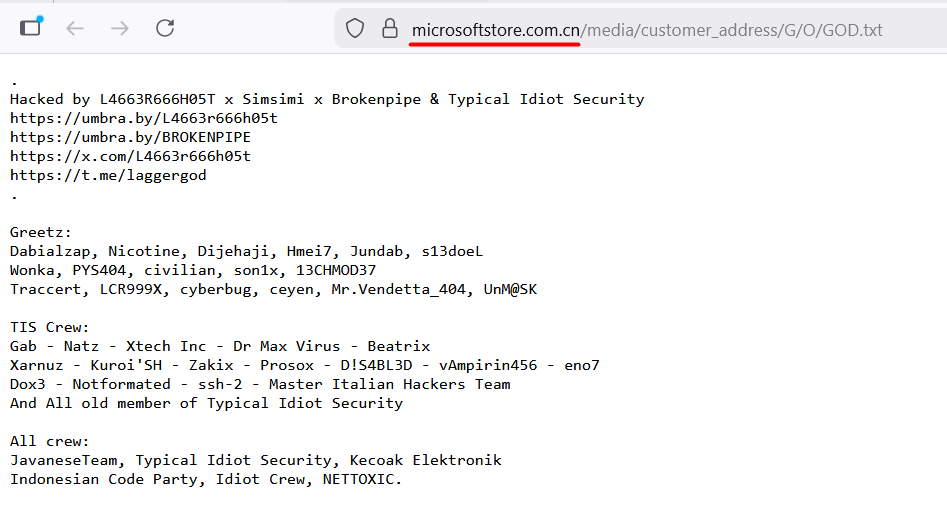

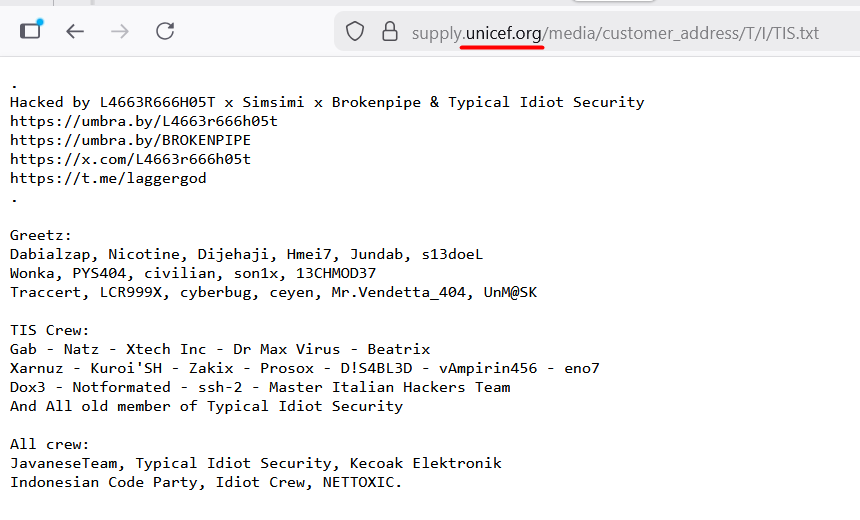
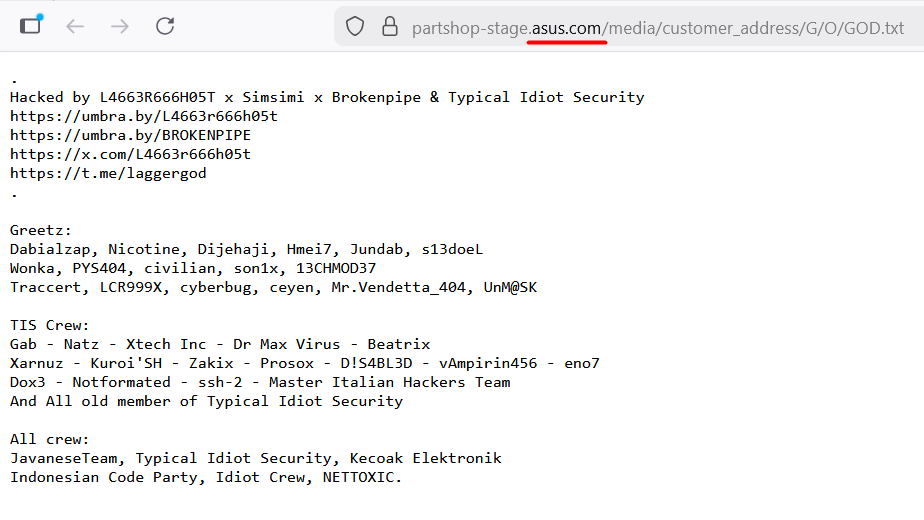
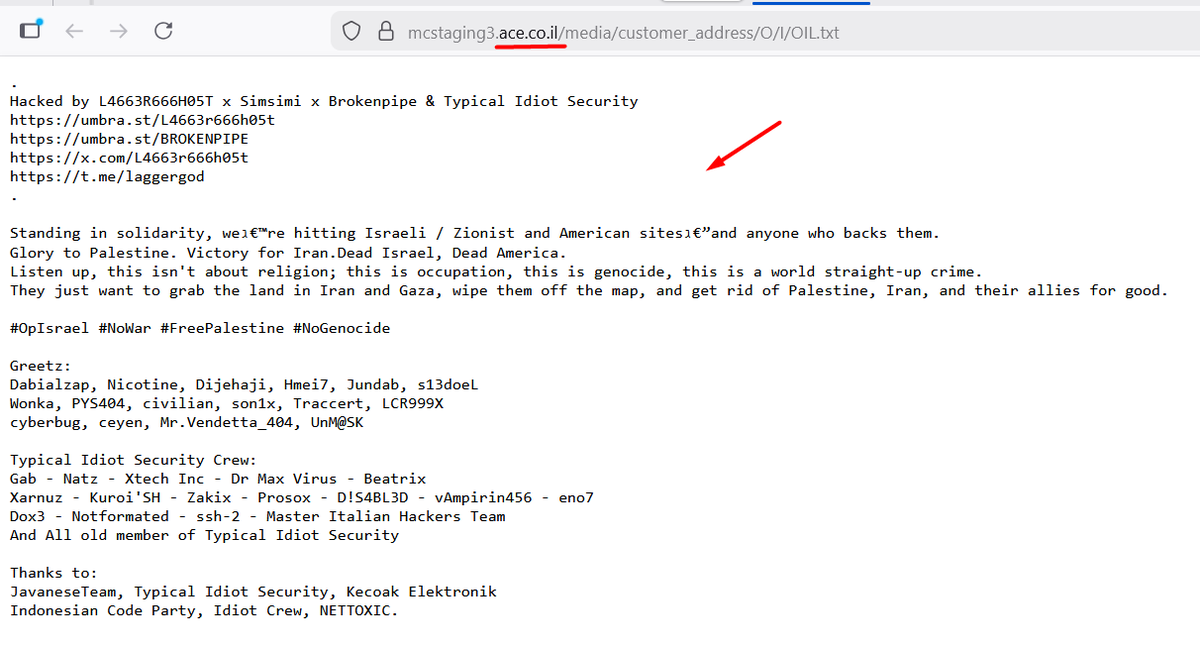
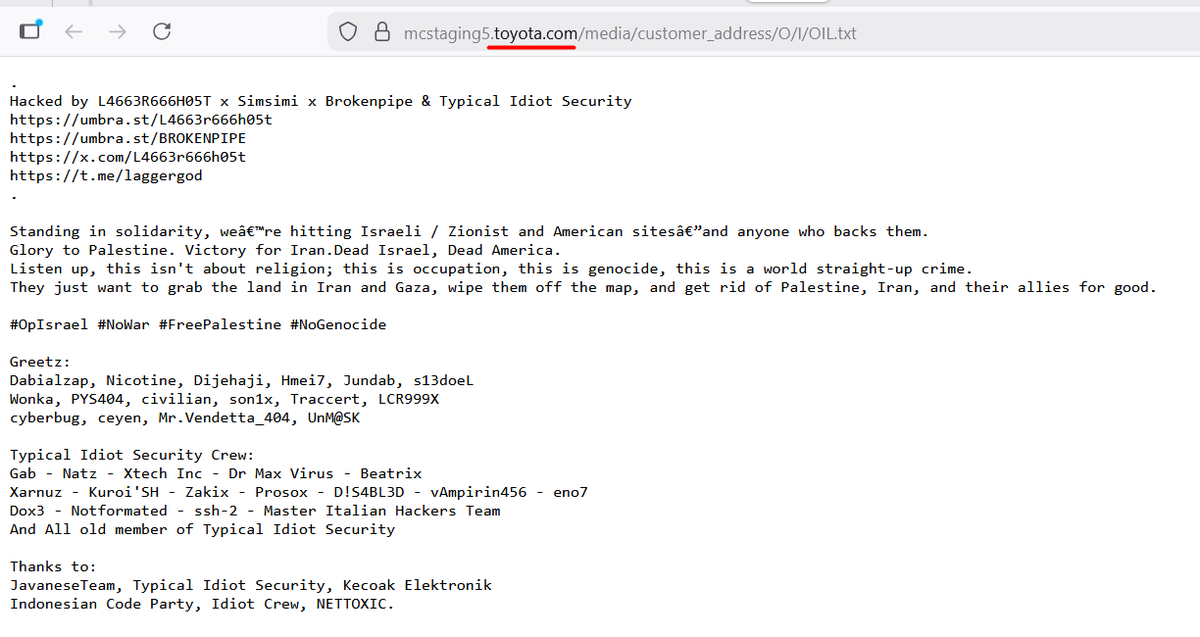
🚨 Mientras tanto, una ola de ataques contra tiendas Magento compromete múltiples sitios web en Chile 🇨🇱 Entre los afectados hay sitios de Entel, Bice Vida, Colun, A3D, CasaIdeas, Volcom, Everlast, Anticipa, Tiendas PF, Maui&Sons, Fila, RipCurl, Stone Center, etc 🤷♂️ Por ahora, solo se ve "subida de archivos" TXT, pero... H/T @joy_dragon 🦾