lazarg retweetledi

If you actually want to work in detection. Please make an effort to understand the data sources you are using.
It's not EventID==X or CommandLine contains Y, just because you executed malware in your lab and checked the event log. 😭
Here a couple to think about
- Understand how event id are not unique across providers
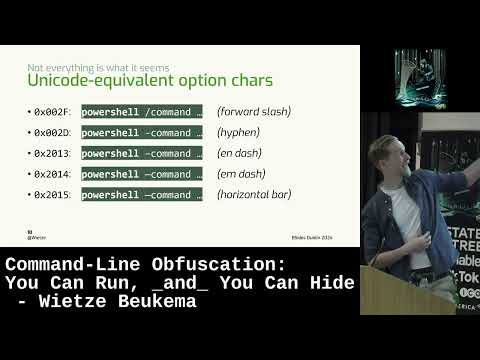
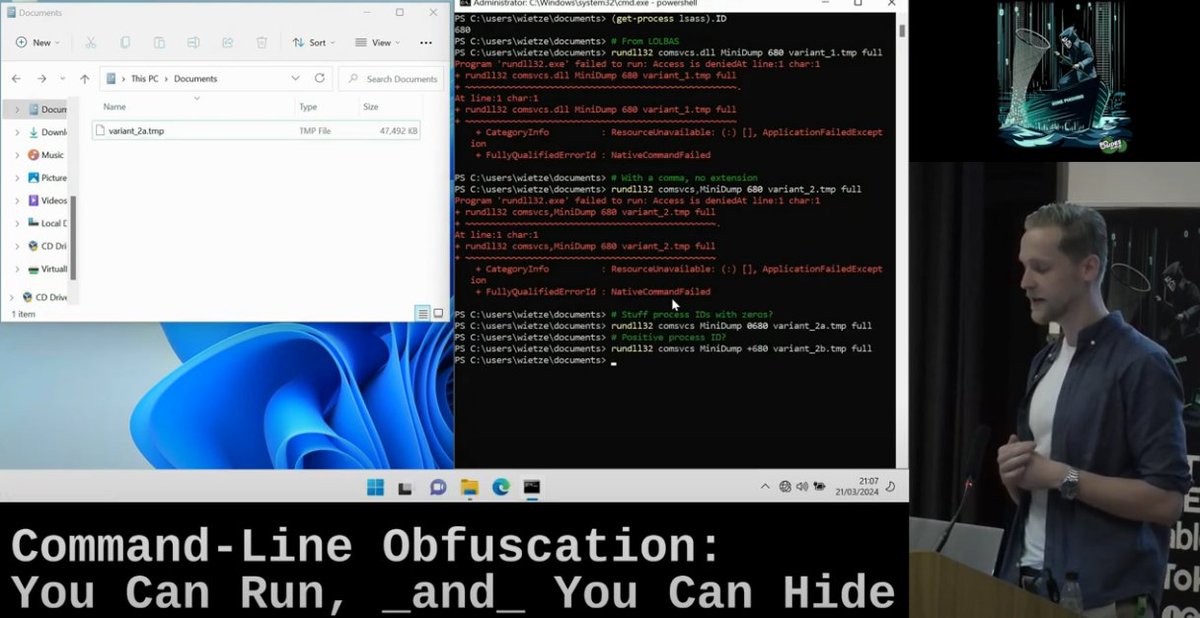
- CommandLine can be spoofed, and you should know how easy it is.
- ETW offers a lot of hidden gems. Learn more and explore it.
- The registry contains a lot of hard to spoof evidence.
- A technique is not linked to a tool
English