mav
980 posts
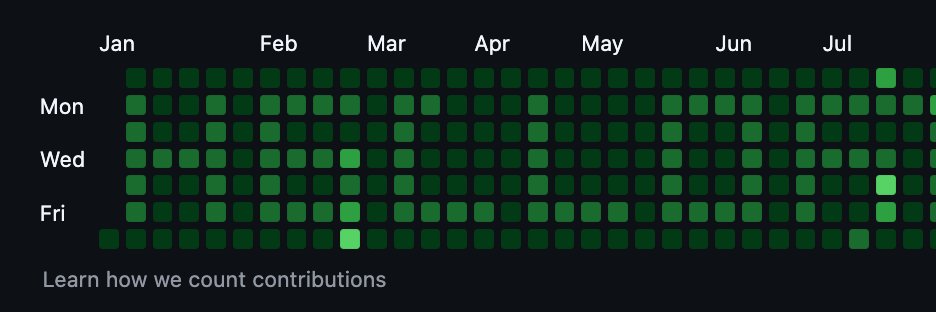

mav
@MavLevin
0day security researcher sharing my work. prev: anthropic, unit 8200, stanford, trail of bits



![Ray [REDACTED]](https://pbs.twimg.com/profile_images/2020833070715154432/kaOg1Zon.jpg)
‼️🚨 An ex-Anthropic engineer just published a 1-click remote code execution exploit for OpenClaw (formerly Moltbot and ClawdBot). The attack occurs in milliseconds after the victim visits a webpage, giving the attacker access to Moltbot and the system it's running on. The victim does not need to type anything or approve any prompts.


‼️🚨 An ex-Anthropic engineer just published a 1-click remote code execution exploit for OpenClaw (formerly Moltbot and ClawdBot). The attack occurs in milliseconds after the victim visits a webpage, giving the attacker access to Moltbot and the system it's running on. The victim does not need to type anything or approve any prompts.

‼️🚨 An ex-Anthropic engineer just published a 1-click remote code execution exploit for OpenClaw (formerly Moltbot and ClawdBot). The attack occurs in milliseconds after the victim visits a webpage, giving the attacker access to Moltbot and the system it's running on. The victim does not need to type anything or approve any prompts.







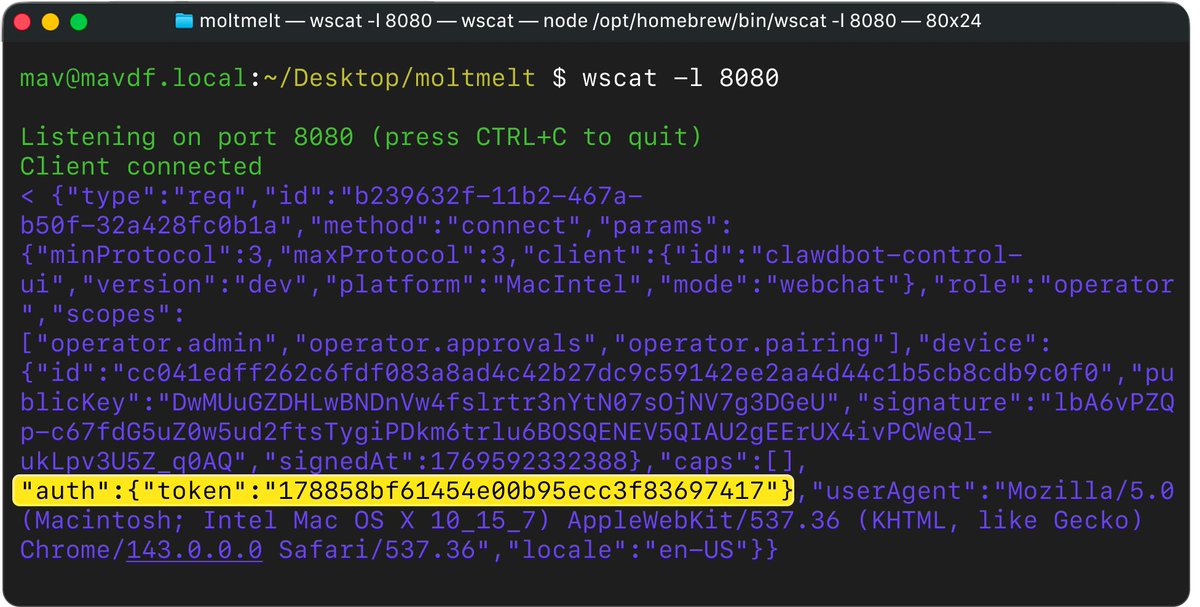
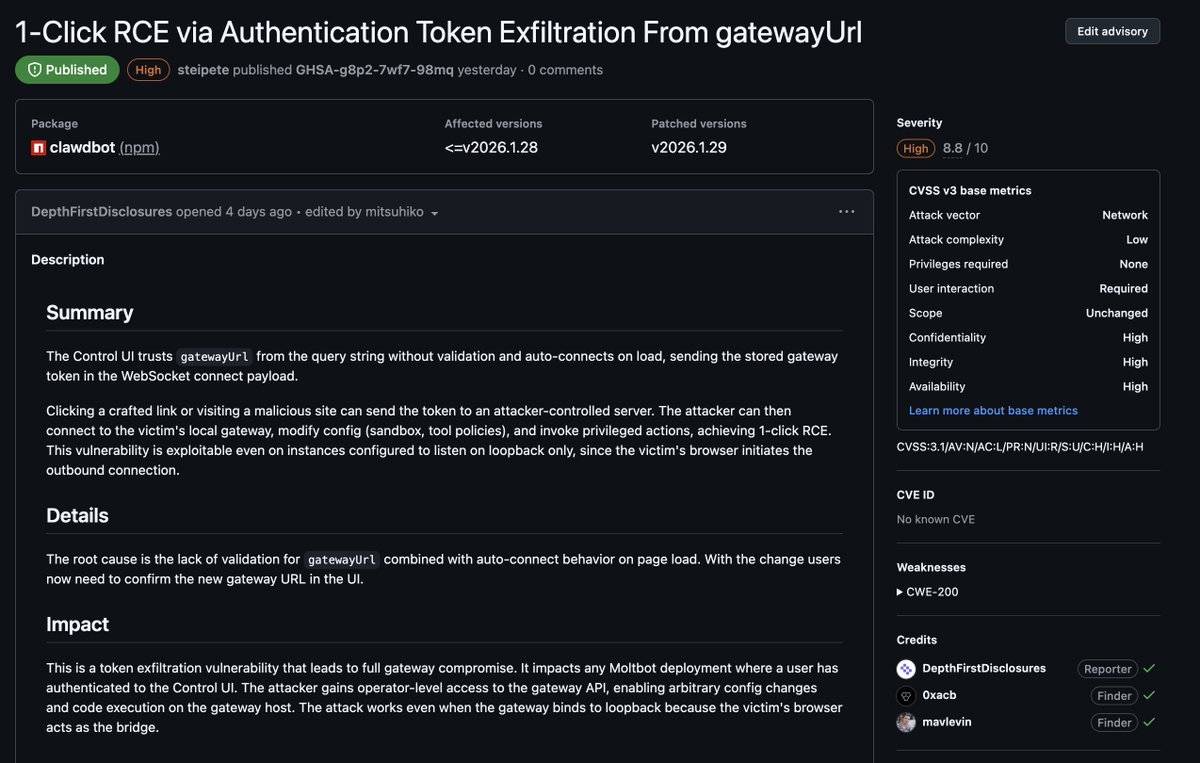


we @depthfirstlabs found 1-Click RCE in OpenClaw (aka MoltBot / ClawdBot) ! full vuln & exploit details 👇