Sabitlenmiş Tweet
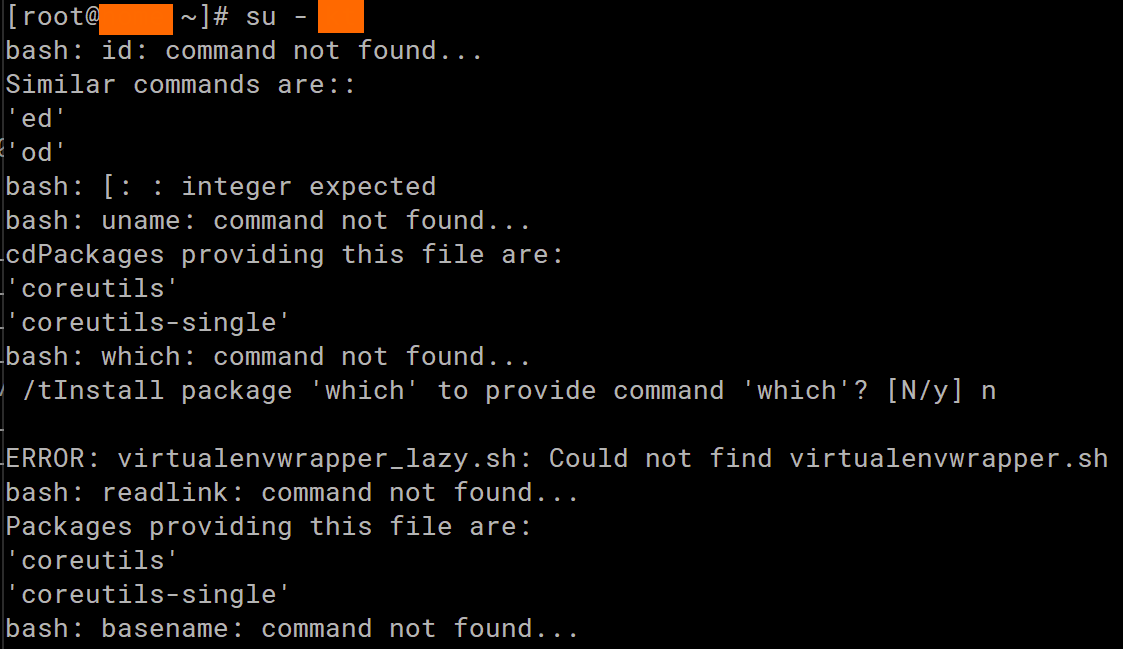
Here's my new article about ClickHouse and #OpenTelemetry for saving storage
Migrating logs stored in #OpenSearch to #ClickHouse and enable #OTel support
cloudnative.quest/posts/observab…
#vector.dev #syslog
English
Patrick Dung
1.7K posts

@mpatdung
🔮Quest to Cloud Native computing ☁⚓☸ https://t.co/oJOt4LoRBp and https://t.co/HKm4MKzMrv Retweets, likes and follow do not mean endorsement. Opinions are my own