Sabitlenmiş Tweet
Nuke 🌄
1.3K posts


Nuke 🌄
@nuke_web3
👷 Building a better web
Denver CO, USA Katılım Şubat 2018
2K Takip Edilen1.8K Takipçiler
Nuke 🌄 retweetledi
Here is my RustConf 2025 presentation "10 Years of Redox OS and Rust". Make sure to watch to the end for a surprise!
- Jeremy Soller
youtube.com/watch?v=xlccq9…

YouTube
English
Nuke 🌄 retweetledi
rotki has been continuously developed as an opensource project since 2017!
We have been lucky to have had the help of 188 contributors to turn @rotkiapp into the best privacy tool for tracking your crypto.
Wanna join them? Then hop right into our github! There is work to do 💪

English
Nuke 🌄 retweetledi

We just dropped an intro to Data Availability, in collaboration with @archetypevc, check it out! Link below:
English

@maxominog @musalbas yup! that is why I am leaning towards using MLS as I describe in the forum - it comes with those features in mind in it's core architecture.
English

@musalbas @nuke_web3 solid point. this hinges on key lifecycle rotation, revocation, recovery. hope @nuke_web3 covers this in DA guarantees research
English
Nuke 🌄 retweetledi

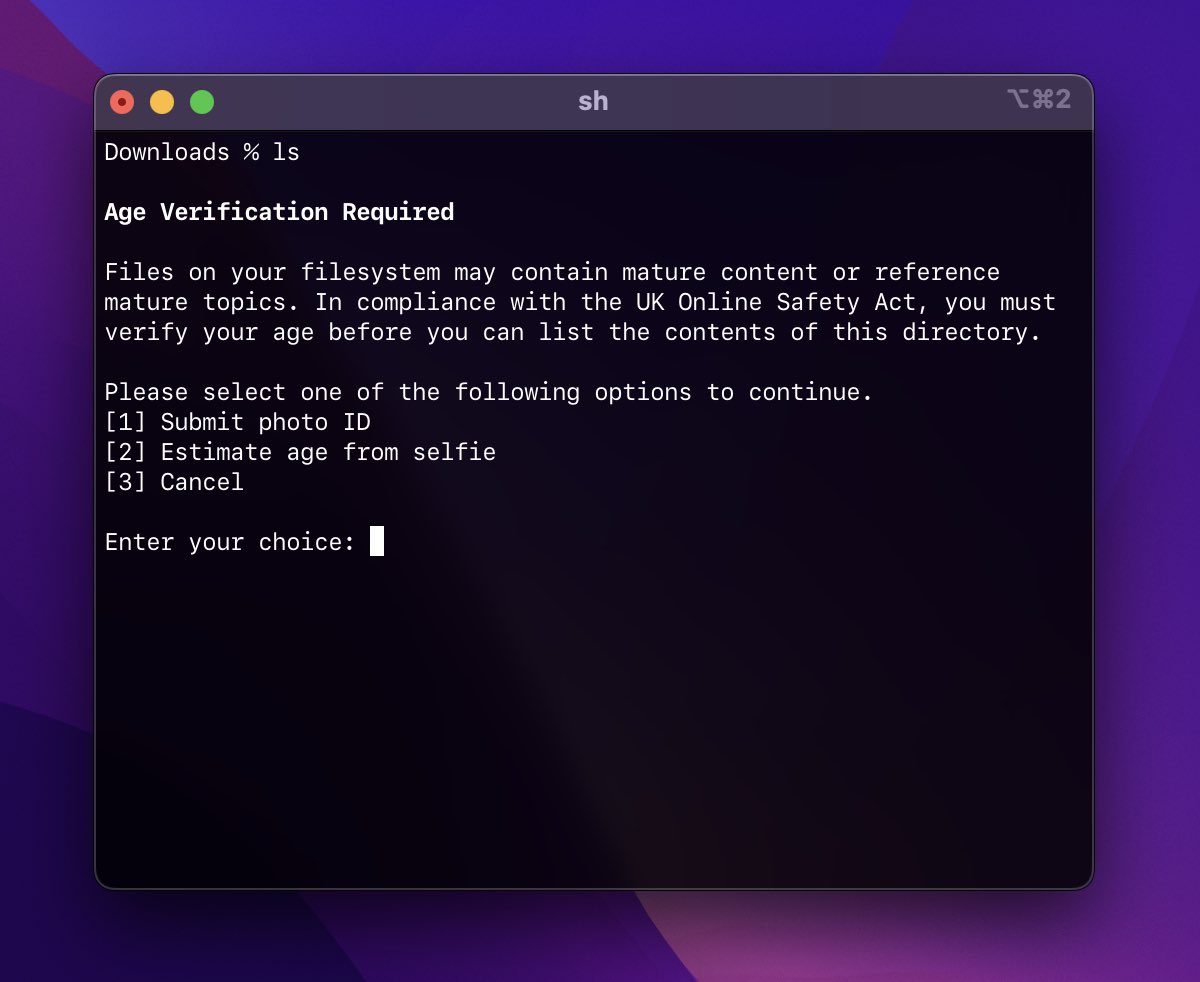
Myth: posting encrypted data on a DA layer gives you no DA guarantees, because it's the person who holds the encryption key could withhold the data.
This is false, if you use a model where users encrypt their own data. New research by @nuke_web3! forum.celestia.org/t/user-centric…
English
Nuke 🌄 retweetledi

OK.
It’s time to reveal the ZK Whiteboard S3 Module 1... because it's LIVE!
🥁🥁🥁🥁
How to Build Hash Functions, with Jean-Philippe (JP) Aumasson @veorq & @nico_mnbl
Below are the links to watch the full module!
English

@musalbas @nuke_web3 So basically DA isn’t dead with encryption, it just needed the right trust model
English
Nuke 🌄 retweetledi

I decided to donate $500K to @rstormsf’s legal defense. Originally, we planned to give $50K, but after what happened to me, I need to take a clear position so everyone understands what @class_lambda stands for.
I understand that the @ethereumfndn will be matching donations up to another $500K for Roman Storm’s defense, which means our contribution can have double the impact. Our team is currently moving money to execute the transaction. It should be done in the next few hours. I'm going to sleep after not sleeping for the last 48 hours.
Open source and decentralization are not just philosophical ideals. They are practical necessities for building crypto. Success in this space comes from building in the open, onboarding others, and creating movements that grow beyond the original project. That is often hard to explain to people who do not share this ethos, because we are not optimizing for the same outcomes.
Our mission is to help build the highways of the new internet in sustainable ways. Economic sustainability is one part of that, but not the only one. We also exist to counterbalance the natural pull toward centralization, a side effect of pure optimization. Centralization is easier and cheaper in the short run. If our only goal were to make money, there are far simpler ways to do it. But money, to us, is just a tool to reach our goals.
Roman’s legal defense matters because builders everywhere need to know they can push innovation forward and that the community will stand behind them when they do. The West became powerful because it embraced freedom and its innovators. Progress came from protecting those who challenged the status quo and building systems that allowed their ideas to scale. When we stop defending our innovators, we stop building the future.
The community can contribute to @rstormsf's legal defense here:
freeromanstorm.com
English
Nuke 🌄 retweetledi
Nuke 🌄 retweetledi

are people actually arguing about this?
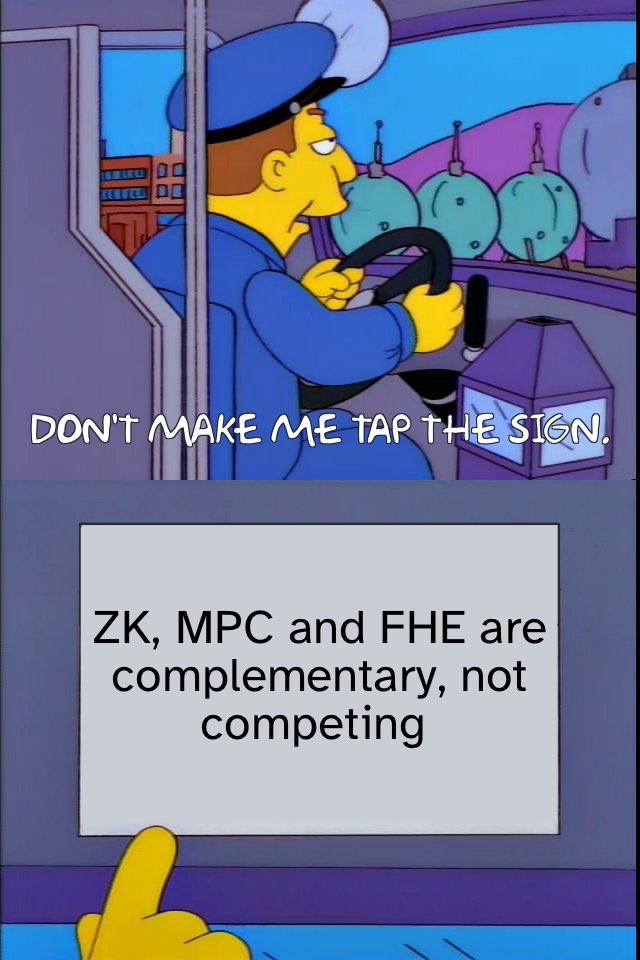
Polynom Labs@polynom_labs
Has ZKP lost the privacy battle to MPC and FHE in 2025? Featuring: @0xMaxSoul - CEO of @polynom_labs @schmiddominik1 - @0xMiden co-founder @auryn_macmillan - @GnosisGuild & @EnclaveE3 @luhelminger - CEO of @TACEO_IO 📅 July 29, 16:00 UTC x.com/i/spaces/1lPKq…
English
Nuke 🌄 retweetledi
Nuke 🌄 retweetledi

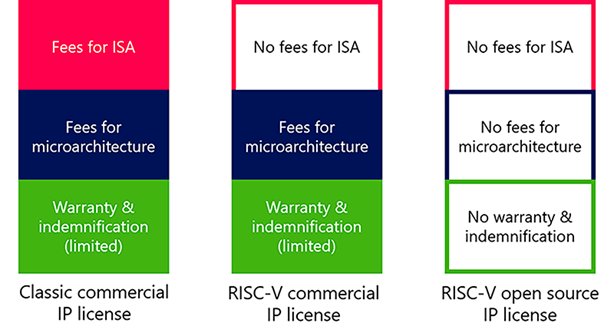
It’s an exciting (but also scary!) time.
For hobbyists, it’s really interesting to get such a high level of performance out of an openISA.
From the geopolitical perspective, further development in this area will severely limit the effect of future US/UK export bans.
Once compiler toolchains and standards hit critical mass, China+RISCV is going to be unstoppable.
Policing an openISA is nearly impossible; reducing x86 / Arm dominance eliminates the single points of failure that could otherwise be controlled via sanctions.
What do you think? Are you worried about the momentum?
English
Nuke 🌄 retweetledi

@badcryptobitch > You end up generate ZK proofs for fake data, or computing over fake encrypted data and you'd never know!
VE constrains the plaintext encrypted data to conform to have some properties, you can define what "correct" is through that mechanic.
English

@badcryptobitch yeah - what is "correct" data is very application specific, but I see no blocker to defining a circuit checking what that is. "external" vs. "manual" doesn't mean much to me... it's just the oracle problem: zk and/or TEE inputs need to be validated in some known way.
English
I know many people don't like TEEs, especially those with a cryptography background.
But, a major, underdiscussed, pain point that TEEs solve is the garbage in/garbage out problem.
When talking about using PETs, we implicitly assume that users either provide the right information or that the information can be easily retrieved from a device via an API call. What happens when neither of those is true in practice?
You end up generate ZK proofs for fake data, or computing over fake encrypted data and you'd never know!
Cryptography alone doesn't help solve this.
You need to go a layer deeper into the hardware level!
This is where TEEs come in!
TEEs can be used for data lineage and hence for solving the garbage in/garbage out problem.
By leveraging TEEs' integrity guarantees, data that needs to be piped into some PET (e.g. ZK, MPC, FHE) can establish where it comes.
It should be noted though that this works well in environments where the secure enclave is controlled by the user e.g. on a mobile phone or on-premise TEE deployments. That's not to say that cloud-based TEEs/secure enclaves don't solve the garbage in/garbage out problem but the assumptions needed are less ironclad than if the data and the TEE/secure enclave are in the same environment.
All of this to say that as much as many folks are uncomfortable with TEEs, they are very necessary in the wide scale deployment of PETs.
English

@badcryptobitch for an audit trail of what (plaintext) was used, verifiable encryption might be a fit. Essentially committing to some "anchor" on your data is all you need, following that through whatever data pipeline you have in mind. (encryption if you need to store private data in public)
English

@badcryptobitch "You need to have guarantees on what's being encrypted."
Should have specified: what guarantees exactly?
English
@nuke_web3 Verifying the encryption alone isn't enough. You need to have guarantees on what's being encrypted.
English

@_weidai @NitanshuL @Celestiaorg @eigen_da @LitProtocol This is aligned to our existing PDA work, and we are working towards a more user-centrict model to allow even more cool stuff (guaranteed ability of user to force exits & inclusions, ...)
See : x.com/nuke_web3/stat…
WIP user-centric design thinking: hackmd.io/c3Fh06UcTK-ruE…
Nuke 🌄@nuke_web3
Yesterday, @hibachi_xyz went live on @celestia Mainnet! 🔥 Hibachi uses our first version of Verifiable Encryption on Celestia, enabling: ✅ Privacy over critical user data such as perp positions; ✅ Onchain settlement from confidential offchain ops 🧵
English
@NitanshuL Nice! IMO it can actually be built completely modularly with (probably zk-friendly) symmetric encryption for DA (on say @CelestiaOrg or @eigen_da) and threshold key encapsulation using say @LitProtocol.
English