phantinuss retweetledi

New Sigma release r2025-12-01 is available for download.
🌟35 New Rules
🛡️21 Rule updates
🔬30 Rule Fixes
Explore the full release -> github.com/SigmaHQ/sigma/…
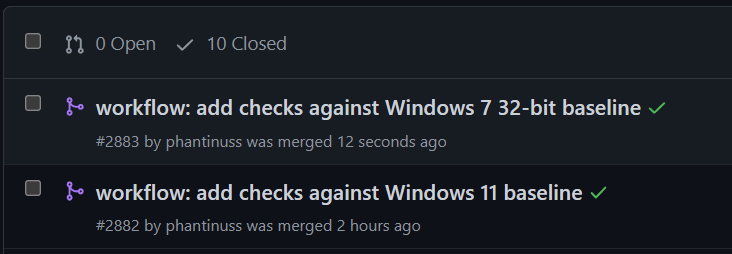
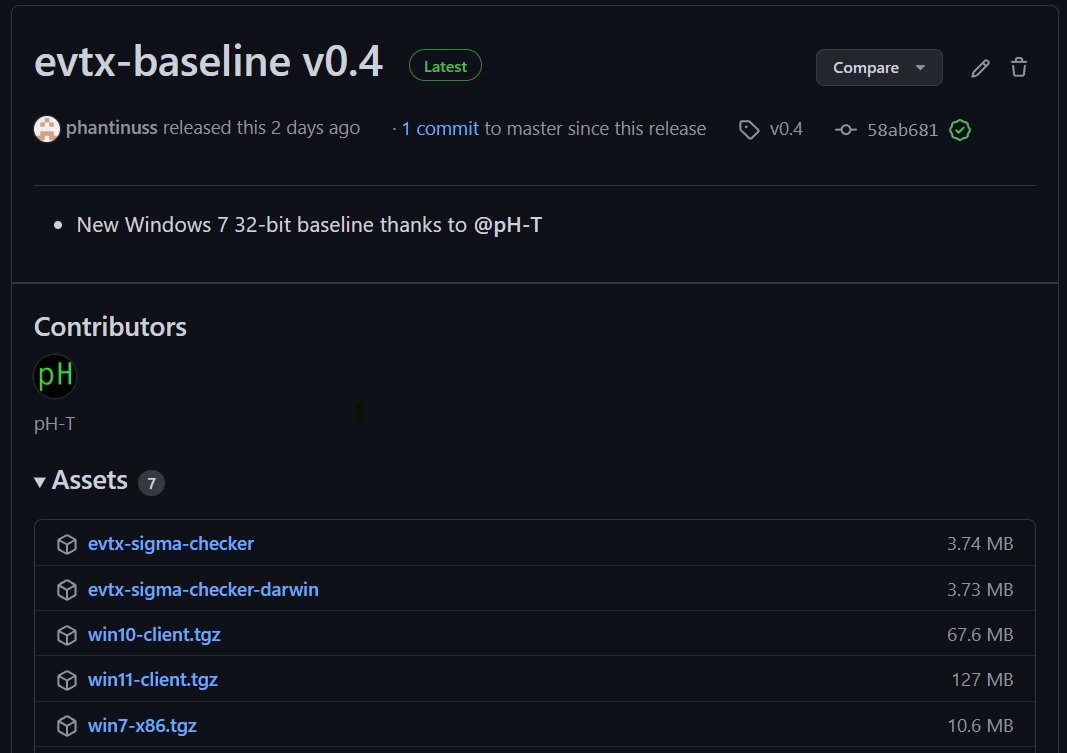
The major update of this release is the introduction of windows regression testing in the CI. We now highly encourage providing evtx files with each PR, and will make mandatory over time.
As always, this release comes with a bunch of new rules and updates. Here are some highlights
- New FortiGate rules, covering the creation of users and modification of firewall objects.
- New rules covering variations of the FileFix/ClickFix technique
- New rules covering Atomic MacOS Stealer, CVE-2025-20333, CVE-2025-59287 and more
- As well as multiple FP fixes and updates.
A special thanks to the many contributors that helped shape this release, specifically
darses, Javier Bruno, @_ezlucky_ @frack113 @hullabrian InTheCyber Group, Tommaso Tosi, JasonPhang98, @Joseliyo_Jstnk @KoifSec Liran Ravich, @_montysecurity @phantinuss, RiqTam, Seth Hanford, suKTech24, @_swachchhanda_, @IntelScott, @Kostastsale, YxinMiracle

English