
Web3Plug (app/acc)
9.4K posts


@plugrel
🔌 plug relations pay anyone 💸 @replydotcash pray anywhere 🕌 @praysap fund anything 🫕 @POTLOCK_ prev @NEARFoundation 🕌 @ummahbuild ummaceleration


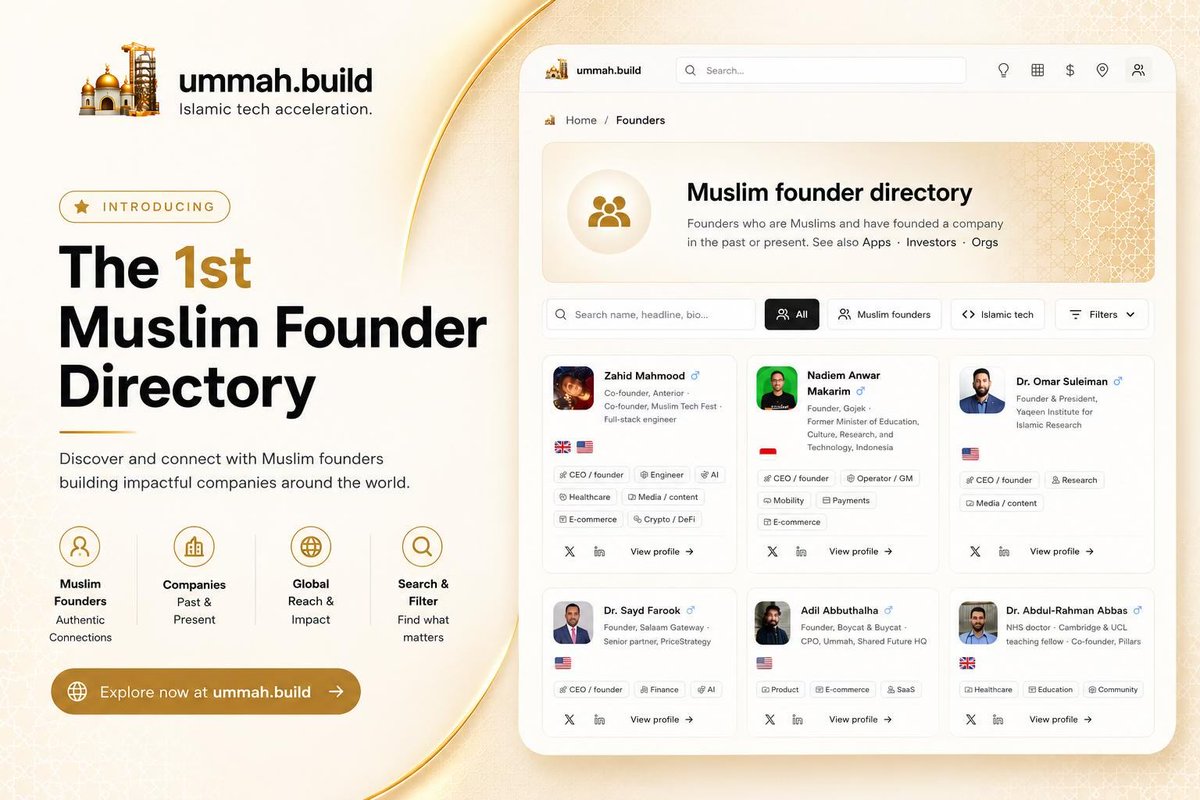



SECURITY ADVISORY — TanStack npm packages A supply-chain compromise affecting 42 @tanstack/* packages (84 versions total) was published to npm earlier today at approximately 19:20 and 19:26 UTC. Two malicious versions per package. Status: ACTIVE — packages are deprecated, npm security engaged, publish path being shut down. Severity: HIGH — payload exfiltrates AWS, GCP, Kubernetes, and Vault credentials, GitHub tokens, .npmrc contents, and SSH keys. If you installed any @tanstack/* package between 19:20 and 19:30 UTC today, treat the host as potentially compromised: • Rotate cloud, GitHub, and SSH credentials immediately • Audit cloud audit logs for the last several hours • Pin to a prior known-good version and reinstall from a clean lockfile Detection — the malicious manifest contains: "optionalDependencies": { "@tanstack/setup": "github:tanstack/router#79ac49ee..." } Any version with this entry is compromised. The payload is delivered via a git-resolved optionalDependency whose prepare script runs router_init.js (~2.3 MB, smuggled into each tarball at the package root). Unpublish is blocked by npm policy for most affected packages due to existing third-party dependents. All 84 versions are being deprecated with a SECURITY warning, and npm security has been engaged to pull tarballs at the registry level. Full technical breakdown, complete package and version list, and rolling status updates: github.com/TanStack/route… Credit to the security researcher for responsible disclosure.


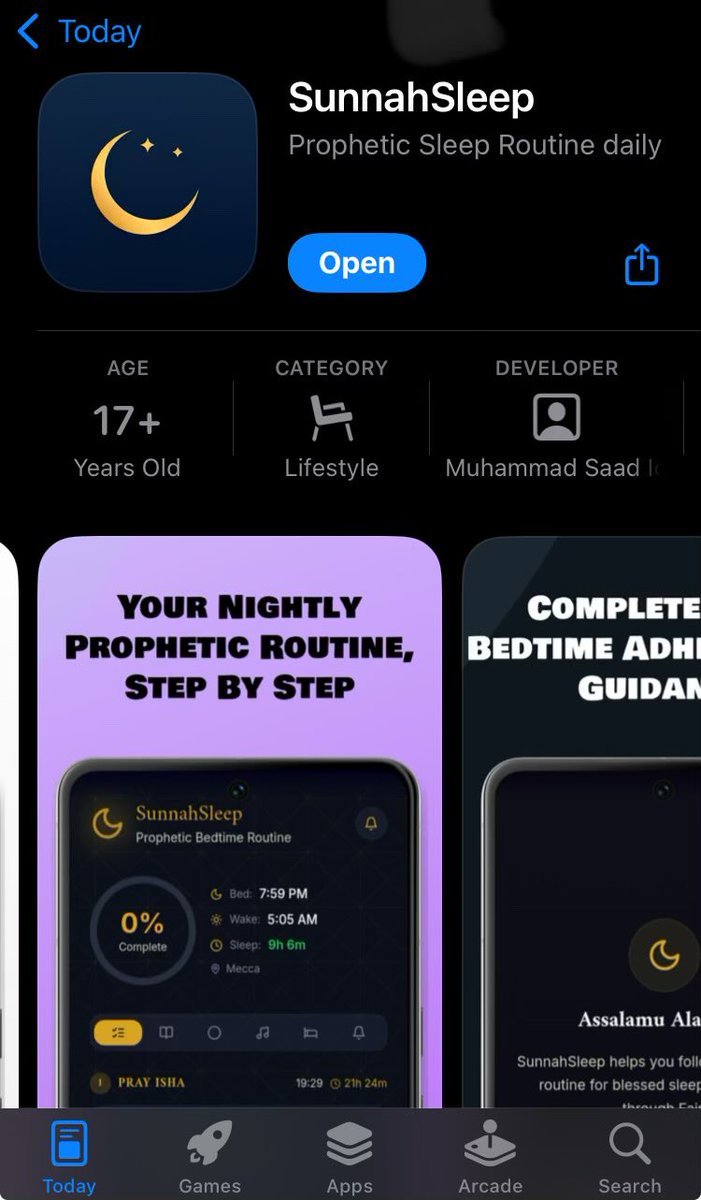
Being a #Muslim founder is more common than we know, it just hasn't been mapped yet. This is why we are proud to announce the 1st Muslim #Founder Directory. Over 200+ Muslim founders 💪 Its time we start competing on every vertical. Check it out ⭐️ ummah.build/founders


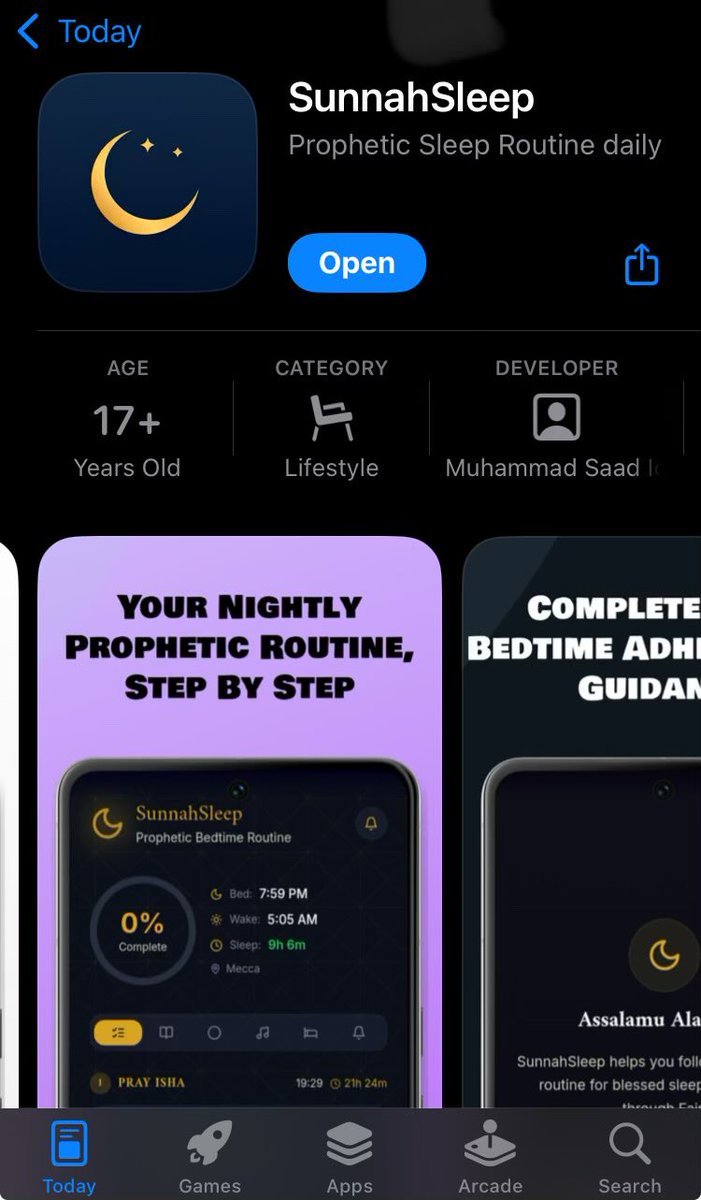
Alhamdulillah — I just launched my Islamic app Serat صراط on the App Store. It took months of work and I built it for every Muslim regardless of language or background. What it does: 🎙️ Voice Dhikr — speak SubhanAllah and it counts automatically 📖 Learn Arabic — all 28 letters with pronunciation feedback 📚 Quran recitation — full Juz Amma with transliteration 🌙 New Muslim guide — complete step-by-step from Shahada to first prayer 🕌 Prayer times — precise, GPS-based, with adhan notifications 👥 Anonymous community — connect with Muslims worldwide Available in 13 languages. Apple Watch included. If this benefits even one person it is sadaqah jariyah for all of us. Please share. 🤲 Download: apps.apple.com/sa/app/serat/i…

1/ This year’s official @consensus2026 closing party by @CoinDesk was a massive step backward. Hosting the flagship event at E11even — a strip club — wasn't just inappropriate; it was incredibly low-brow for an industry trying to grow up. 2/ Let’s be clear: I’m all for alcohol, music, and a good time. Hire a world-class DJ. Throw a massive rave. Go to Club Space. But choosing a strip club as the official venue for a global conference is a choice that reflects poorly on all of us. 3/ Just because this happened in 2021 doesn't mean it should happen in 2026. Back then, Coinbase, FTX and Binance execs were there, but the industry has evolved. We are supposed to be moving toward institutional maturity, not leaning into "bro-culture" clichés. 4/ I’ve always been an advocate for sex work. I have zero issue with women making $40k–$80k on their own terms. The issue is the context. 5/ When an official event for a top-tier conference — filled with institutional partners and people of all genders and religions — centres on women shaking for dollars, it diminishes women to sexual objects and enforces a stale, exclusionary culture. 6/ It’s honestly boring. I guarantee brands like @MetaMask and CoinDesk will one day look back at their logos plastered on those walls with genuine embarrassment. 7/ We had international attendees flying in from across the globe. Is this really the best US crypto has to offer? Working the pole is a skill, but watching it in a professional context just left most people looking dazed and awkward. 8/ The vibe was off. I ran into my banker and some mid-tier hedge fund guys there. We can talk millions on Wall Street or over steak, but meeting at a strip club is unnecessary. We could’ve hit a polo club, a baseball box, or played padel. 9/ Even the economics were a "bear market" vibe. Most people were just watching with a mix of shock and intrigue. The girls weren't making much. They used to take crypto; now they don't. The floor was dry. No fiat moving. Why were we even there? 10/ Seeing a banker film the stage (until security stepped in) while seeing my bankers logos walk around in a strip club is the peak of industry cognitive dissonance. 11/ This industry is capable of so much more, yet we keep tripping over our own feet. We want to be taken seriously on the world stage, but we’re still acting like we’re in a basement. We must do better. Special shoutout to @SolanaFndn, @amystreet, and @SuperteamUSA. Your Accelerate vibe was immaculate, paired with the best Mario Kart-themed afterparty. 🏎️💨 It was the perfect illustration that "crypto culture" doesn’t have to mean "bro culture." You can have high-energy, high-intelligence fun without… whatever E11even was. Let’s talk economics: A single sponsorship for that E11even event costed roughly $90k. The entire Mario Kart event? Maybe $50k. Using a massive brand budget to alienate half your audience is a spectacular waste of capital. 📣📣📣 Conference organizers and sponsors: we have to do better. If we want to move millions on Wall Street, we need to stop acting like we belong in a basement. ✌️

Their status page is also down 😭

are you ready to bet on yourself? bc we're ready to bet $10,000 on you applications open now: forma.city/residency






The classroom changed. The homework changed. How we learn changed. 18 million students already build on Replit and now, there's a dedicated space just for them. No setup. No lectures. Just building. Teachers get free access. Students get 50% off Core. And if you're running a program, we'll help you scale it. Claim yours at replit.com/edu

