Sabitlenmiş Tweet

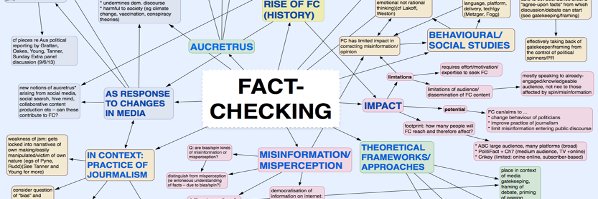
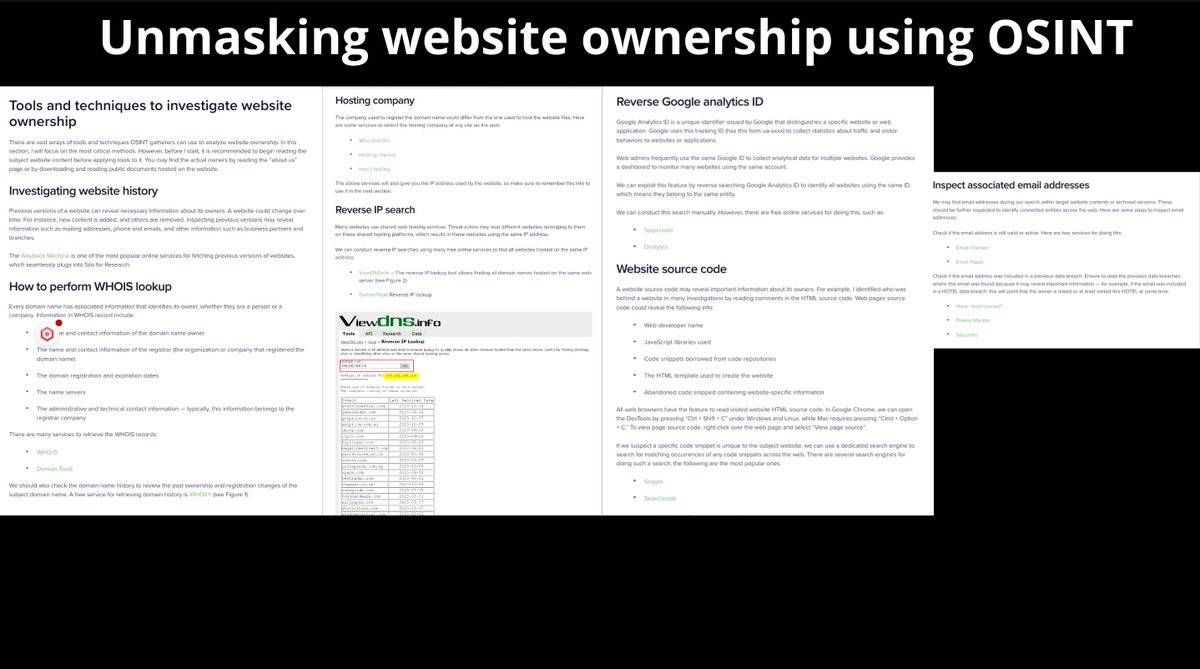
I've put together a beginner's intro to the Open Source Intel field for my #FCnV journalism students.
In the #OSINT community spirit of sharing, I offer it to everyone to use and share.
Feedback/suggested additions welcome.
Hope it's useful.
docs.google.com/document/d/1wn…
Sources follow
English