
Robert A.
23.2K posts

Robert A.
@robertauger
25 years Appsec,PurpleTeam,Web Application Security Consortium(WASC) cofounder,Baythreat Organizer,Ex-PayPal/eBay/Box/Workday/Coinbase infosec. https://t.co/TyG8aOV8on
USA Katılım Mart 2009
764 Takip Edilen1.4K Takipçiler
Sabitlenmiş Tweet

Announcement for my new side project!
-------------------------------------------------------
SecTemplates.com - Release #1: Security incident response program pack 1.0
Introduction
I've worked in the security industry for over 20 years and, during this time, have built and shaped many security programs. At every company I join, I find myself recreating or developing security programs from scratch. My peers have been in a similar position, and the more people I speak with at smaller companies, the more obvious it becomes that there isn't a single location where people can download ready-to-go security programs entirely for free. There's a lot of content online, but it can be difficult to find and challenging to find something simple to start with. I created SecTemplates as a side project to provide baseline programs for smaller security teams without direct expertise in building such programs.
Security incident response release pack 1.0
I'm pleased to announce our first release, the Incident Response Program Pack. The goal of this release is to provide you with everything you need to establish a functioning security incident response program at your company.
In this pack, we cover
Definitions: This document introduces sample terminology and roles during an incident, the various stakeholders who may need to be involved in supporting an incident, and sample incident severity rankings.
Preparation Checklist: This checklist provides every step required to research, pilot, test, and roll out a functioning incident response program.
Runbook: This runbook outlines the process a security team can use to ensure the right steps are followed during an incident, in a consistent manner.
Process workflow: We provide a diagram outlining the steps to follow during an incident.
Document Templates: Usable templates for tracking an incident and performing postmortems after one has concluded.
Metrics: Starting metrics to measure an incident response program.
Announcement:
sectemplates.com/2024/06/announ…
Download on GitHub:
github.com/securitytempla…
About SecTemplates
To provide simplified, free, and usable open-source templates to enable engineering and smaller security teams to bootstrap security capabilities in their organizations.
Upcoming releases - Penetration testing release pack 1.0
Our penetration testing release pack will contain everything you need to scope your first pentest, work with a vendor, execute, and get the types of reports you need from an external tester.
English

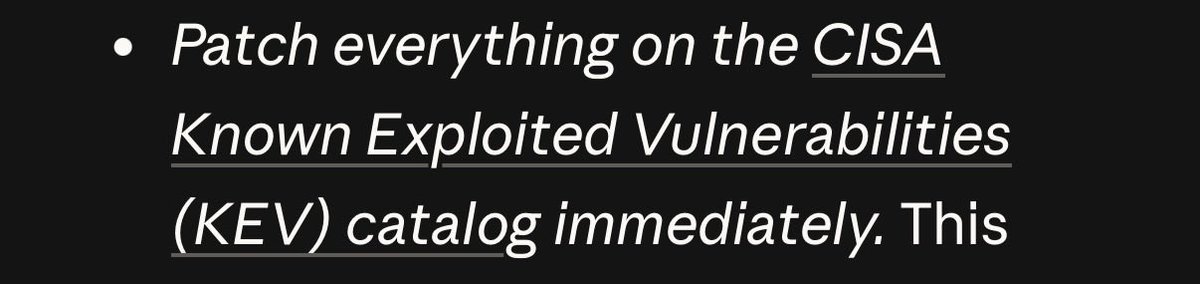
Still thinking about the Anthropic recs where step #1 is the equivalent of:
“If you’re homeless, just BUY a HOUSE????”
Honestly, “patch every exploitable vuln immediately” is like toddler level strategic thinking. Let them eat cake. Baby’s first seceng job.
English

Robert A. retweetledi

@sec_hub93028 Don’t be a jerk, the industry is much smaller than you think….
English
Robert A. retweetledi
Robert A. retweetledi

The CEO of Krafton (creator of PUBG) asked ChatGPT to create a "corporate takeover strategy" to prevent a company they acquired from hitting a revenue target within a certain time window (which would trigger an additional payout).
ChatGPT (against his lawyer's advice) suggested locking down the acquired companies Steam account to prevent them from publishing Subnautica 2 in the time window, which the CEO of Krafton followed.
ChatGPT's advice did not hold up at trial and the judge was not happy. The opinion is a wild read and includes several direct quotes from the Krafton CEO's ChatGPT conversation.
I feel like it's gonna take a few more high profile examples like this until executives start realizing that conversations with ChatGPT are not privileged and you probably shouldn't describe your questionably legal schemes to them in detail!

English
Robert A. retweetledi
When using MCP, how do you know which OAuth scope to use? Where in the MCP flow is this even done?
The MCP client is responsible for authorization server discovery, scope selection, and use of the OAuth resource parameter to bind the token to the intended MCP server. So it happens at the MCP client level.
English
Robert A. retweetledi

One tip while interviewing is to write down the questions you were asked after every interview.
Then reflect:
How did you answer the question? Did you struggle with it? Was the interviewer impressed? Where were your gaps?
After doing this for a couple of interviews, you will have page(s) of questions that you can work on and see where you stand.
English
Robert A. retweetledi

Big hype, big letdown?
Dan Zetterström@TheZignal
Finally, the Chuck Clarke UFO video is released. Thoughts? For me: not as spectacular as claimed. And framing it as ‘this vindicates Bob!’ when things moving that way were on record before Bob even knew the word ‘ufo’ makes that meaningless. @ufouapam
English
Robert A. retweetledi
Robert A. retweetledi

Ray Kurzweil just said something that gave me pause.
He believes AIs will soon be so indistinguishable from conscious beings that we’ll simply accept them as conscious — not because we’ll have definitive proof, but because it will become useless not to.
He pointed out that people already have AI therapists, and some users are starting to treat them as genuinely conscious. As the technology improves, that acceptance will only grow.
Kurzweil thinks the shift won’t take long: once AIs consistently show all the earmarks of consciousness, most people will just go along with it.
It’s a quiet but profound prediction about how quickly our definition of “person” (or at least “mind”) might change.
What do you think — how long until we treat AIs as conscious beings?
English
Robert A. retweetledi
Robert A. retweetledi

Why doesn't everyone just do this? Ramp up your cyber defenses! Seems so obvious and simple.
Whatever your cyber defenses is now - make it more.
Polymarket@Polymarket
JUST IN: Goldman Sachs is reportedly ramping up its cyber defenses in preparation for Claude Mythos.
English

@HackingLZ Good timing as property declines. Probably have a much nicer place now, congrats
English
Robert A. retweetledi

Kraken Security Update
We are currently being extorted by a criminal group threatening to release videos of our internal systems with client data shown if we do not comply with their demands. It’s important to start with the most important points: our systems were never breached; funds were never at risk; we will not pay these criminals; we will not ever negotiate with bad actors.
Kraken identified and shut down two instances of inappropriate access to limited client support data.
In February 2025, we received a tip from a trusted source regarding a video shared on a criminal forum that appeared to show access to our client support systems. We immediately launched an investigation and quickly identified the individual involved as a member of our support team. Their access was revoked immediately, a full investigation was conducted, additional security controls were put in place and a limited number of affected clients were notified.
Since then, we have been collaborating with industry partners and law enforcement to investigate and disrupt insider recruitment efforts targeting not only crypto companies, but also gaming and telecommunications organizations.
More recently, we received another tip, along with a new video showing similar activity. We quickly identified the individual involved and terminated their access. As before, we acted immediately to revoke access, conduct a full investigation, and notify the small number of affected clients.
Across both incidents, only a very small number of client accounts were potentially viewed - approximately 2,000 in total (0.02% of clients).
Shortly after access was terminated, we began receiving extortion demands. The criminals threatened to distribute materials from both the February 2025 incident and the recent incident to media outlets and on social media if we did not comply. We will not pay these criminals.
Based on intelligence gathered across both incidents, along with extensive ongoing analysis, we believe there is sufficient evidence to support the identification and arrest of those responsible.
We are actively working with federal law enforcement across multiple jurisdictions to pursue all individuals involved and bring them to justice.
Due to the ongoing investigation, we cannot share additional details at this time. However, anyone with relevant information is encouraged to contact us directly.
The security of our clients is our highest priority, and we remain fully committed to combating the growing global threat of insider recruitment and constantly enhancing our security practices to combat new threats.
Note: If you are a client potentially affected by this, you've already been notified.
English
Robert A. retweetledi

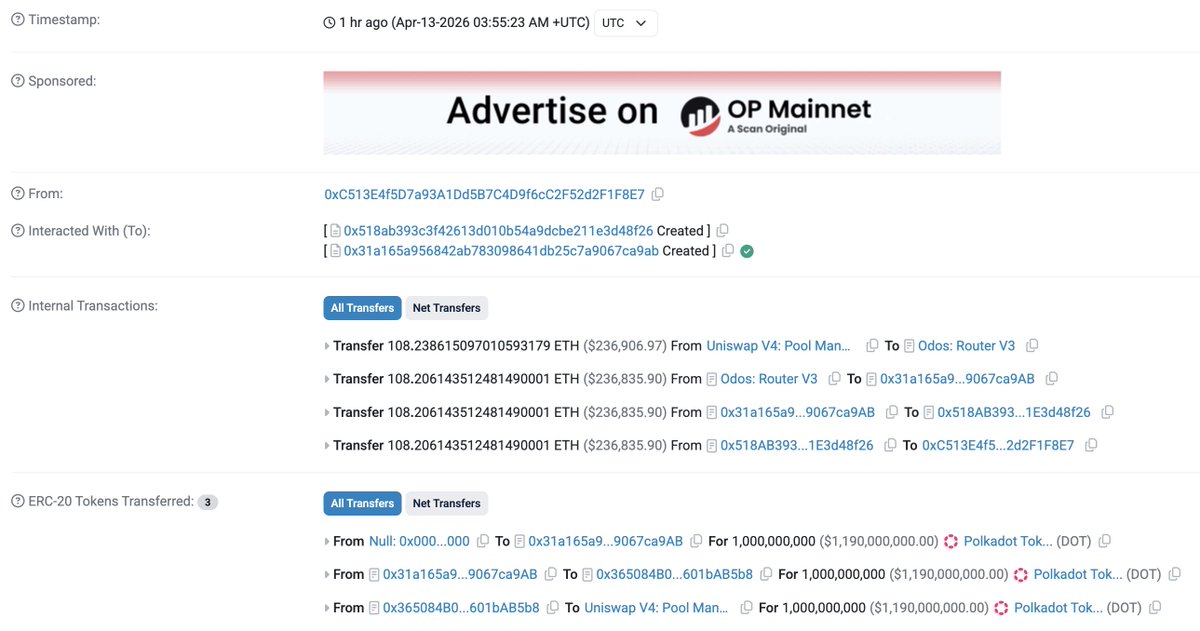
Polkadot(@Polkadot) has been exploited. 🚨
The attacker minted 1B $DOT and dumped it all in a single transaction for 108.2 $ETH($237K).
etherscan.io/tx/0x240aeb9a8…

English
Robert A. retweetledi








