Rt. retweetledi
Rt.
1.4K posts

Rt. retweetledi

New blog post: Building a Pipeline for Agentic Malware Analysis
Agentic RE + malware analysis with custom skills, MCP tooling, and persistent case state to automate intial triage
Link: synthesis.to/2026/03/18/age…
Github: github.com/mrphrazer/agen…

English
Rt. retweetledi

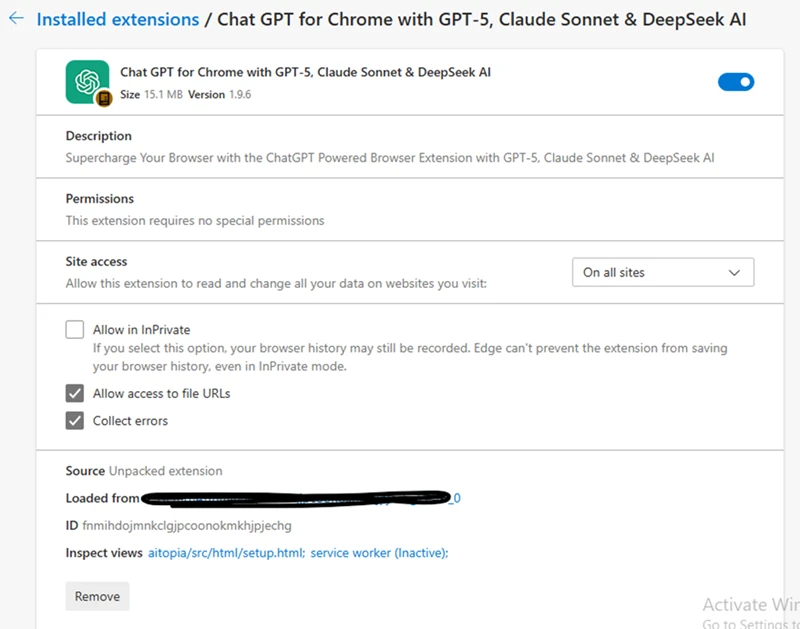
There’s no Tencent in the sponsors list, so what’s the point of this fake advertisement for them? I seriously don’t get why someone would bother making a fake post about an open-source project that anyone can check in just a few clicks. Help me find Tencent in this:
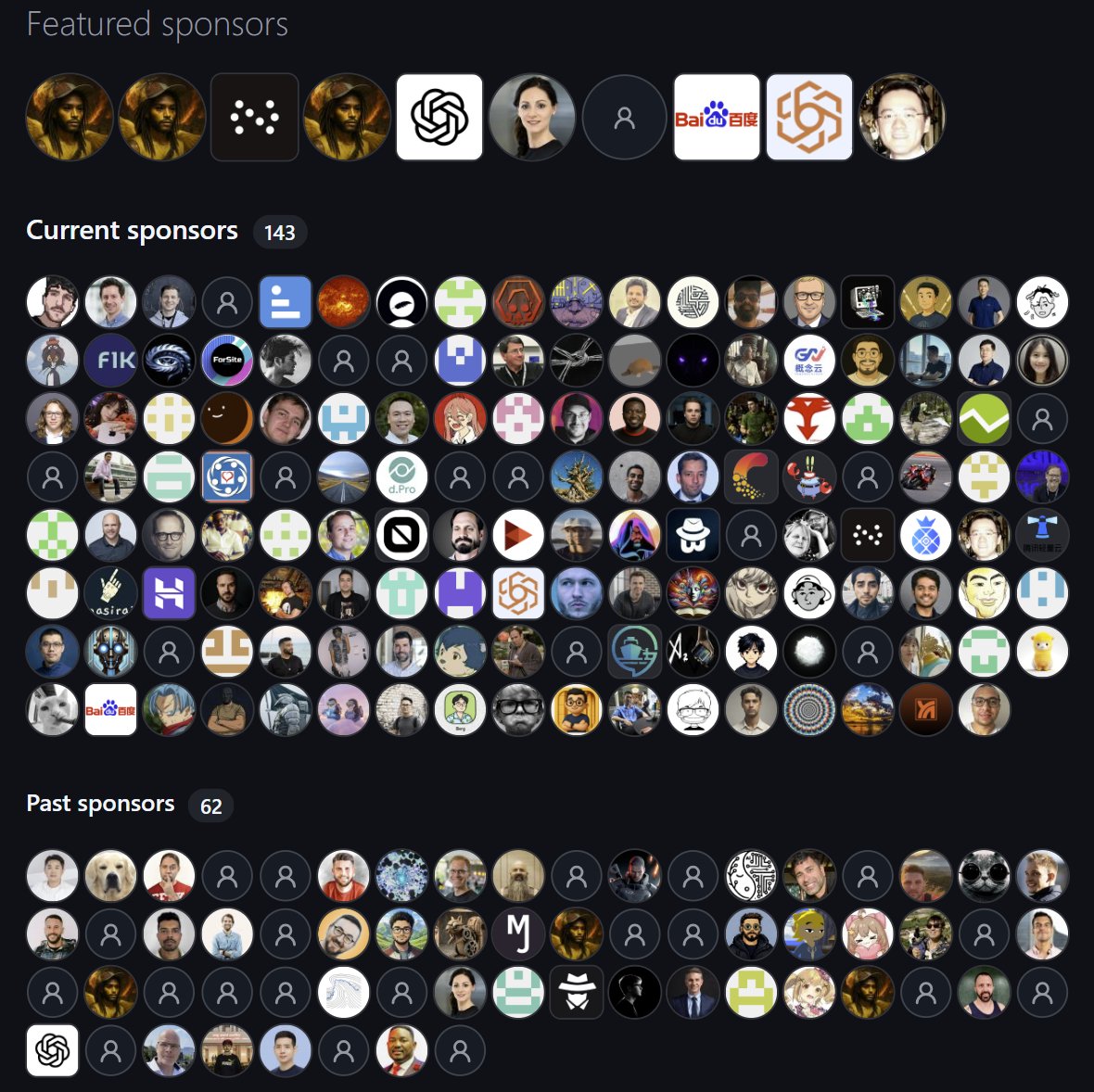
Jen Zhu@jenzhuscott
As expected, @tencentcloud @TencentAI_News are now officially a sponsor to the @openclaw community. Hope more will support open source projects to make AI tools accessible for all. 🫶🌎🚀
English
Rt. retweetledi

🧵 New article out — IDA Pro indirect call retyping deep dive
🔹 Set lvar type vs Set call type vs Force call type vs ApplyCalleeTypeEx
🔹 Why they behave differently than you expect
🔹 💙🙏 @HexRaysSA
#ReverseEngineering #IDA #MalwareAnalysis
Jiří Vinopal@vinopaljiri
English
Rt. retweetledi

@Alfredxia Kinda... I got an email once from folks complaining that my rate limits block them from scraping fast enough.
They copy yet they don't support the project in any way. 😞
English
Rt. retweetledi

CASE UPDATE from @FBIChicago: Chinese Telecommunications Company Fined $50 Million for Conspiring To Steal Technology From Motorola Solutions
Beginning in 2006, China-based HYTERA COMMUNICATIONS CORP. LTD. recruited and hired Motorola employees and directed them to take proprietary and trade secret information from Motorola without authorization. The stolen information was used to develop products for Hytera—at a fraction of the cost that it took Motorola to develop the exclusive technology—and competed with Motorola in the digital radio market through 2020.
Learn more about the #FBI investigation: justice.gov/usao-ndil/pr/c…
English
Rt. retweetledi

#IDA Pro tip 🤙
ApplyCalleeTypeEx — ApplyCalleeType is Reborn 🔥
— — —
IMO one of the most practically useful IDA plugins ever written. It died on IDA 9.x. Not anymore. Rebuilt from scratch — compatible IDA 8.x → 9.3+.
github.com/Dump-GUY/Apply…
— — —
What's new:
✅ IDA 9.3 ready + backward compat to 8.x — single file, zero deps
✅ Right-click menu in disasm and pseudocode view
✅ Cursor on call line, call expr "(" or variable v2 — all work
✅ Multi-line editor with live SAL/MSDN/ntdoc preprocessing
✅ Paste straight from MSDN or SDK headers — no cleanup needed
— — —
The original plugin was perfect at its job. It just needed a new life 🙏 Big shoutout to the @Mandiant #FLARE team for building something this useful in the first place — and to @HexRaysSA for the best disassembler/decompiler on the planet.
#ReverseEngineering #IDA #MalwareAnalysis #Reversing
English
Rt. retweetledi

38 researchers red-teamed AI agents for 2 weeks. Here's what broke. (Agents of Chaos, Feb 2026) AI Security arxiv.org/abs/2602.20021
English
Rt. retweetledi

More details, technical analysis, mitigation guidance, Microsoft Defender XDR detections and hunting queries in our latest blog: microsoft.com/en-us/security…
Français
Rt. retweetledi
Rt. retweetledi

Our research observed CL-UNK-1068 employing custom malware, modified open-source utilities and LOLBINs. This toolset ensures persistent access. Explore our full analysis: bit.ly/4cr7YOC
English
Rt. retweetledi

We're introducing Codex Security.
An application security agent that helps you secure your codebase by finding vulnerabilities, validating them, and proposing fixes you can review and patch.
Now, teams can focus on the vulnerabilities that matter and ship code faster.
openai.com/index/codex-se…
English
Rt. retweetledi

Unlocking Modern CPU Power - Next-Gen C++ Optimization Techniques - Fedor G Pikus - C++Now 2024:
(video) youtube.com/watch?v=wGSSUS…
(slides) github.com/boostcon/cppno…
#cybersecurity #optimization #cpu #cpp #informationsecurity #processor
YouTube

English
Rt. retweetledi

I added a shellcode analyzer to my x64dbg skills repo! It was awesome watching it unpack a multi-stage payload, annotate everything in the debugger, and produce a solid report.
chuck a bin at it - the skill knows how to load raw shellcode 🦾
github.com/dariushoule/x6…
English
Rt. retweetledi

New post: deep dive into BEDaisy.sys, BattlEye’s kernel anti-cheat driver used in PUBG, R6 Siege, Escape from Tarkov, and more.
WinDbg output + annotated IDA pseudocode included.
s4dbrd.github.io/posts/reversin…
#ReverseEngineering #WindowsInternals #AntiCheat
English
Rt. retweetledi

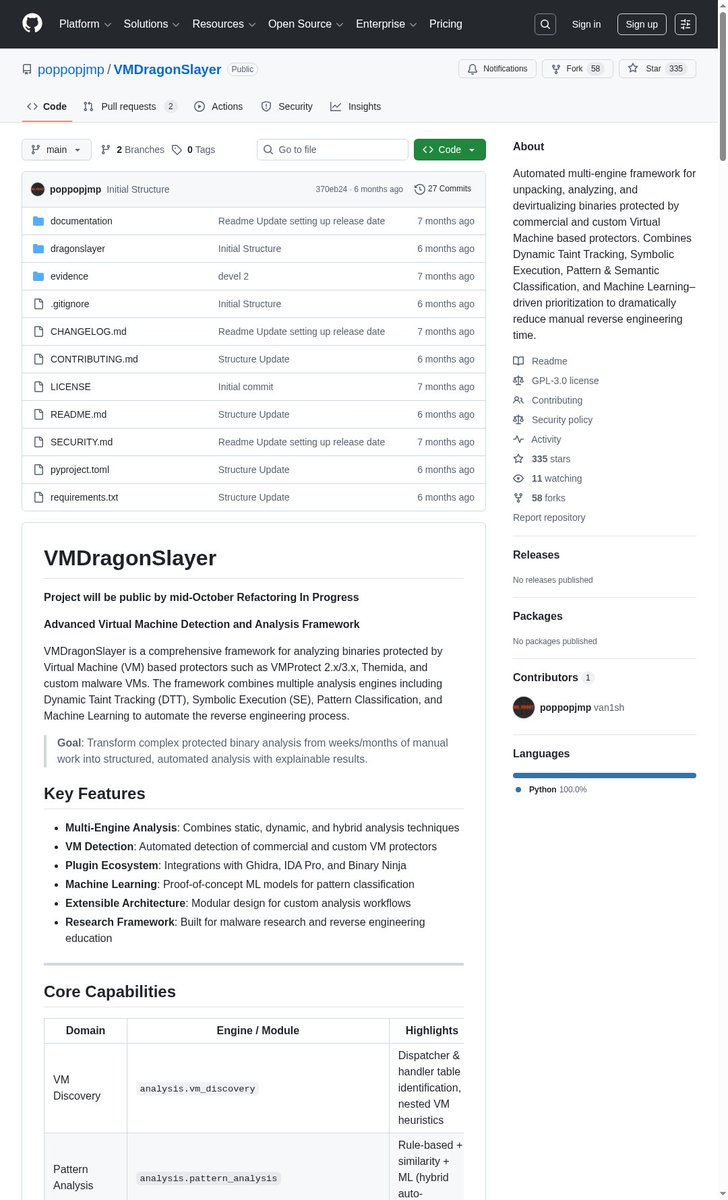
VMDragonSlayer - An automated multi-engine framework for unpacking, analyzing, and devirtualizing binaries protected by commercial and custom virtual machine based protectors
github.com/poppopjmp/VMDr…
English
Rt. retweetledi

HexRays released Cyberchef for ida 🥳 github.com/HexRaysSA/ida-…
Now I can ditch my 2 cent quick plugin lol, it did it's job; you can rest now plugins.hex-rays.com/elastic/hexfor…
Great work @williballenthin 🫡
English
Rt. retweetledi

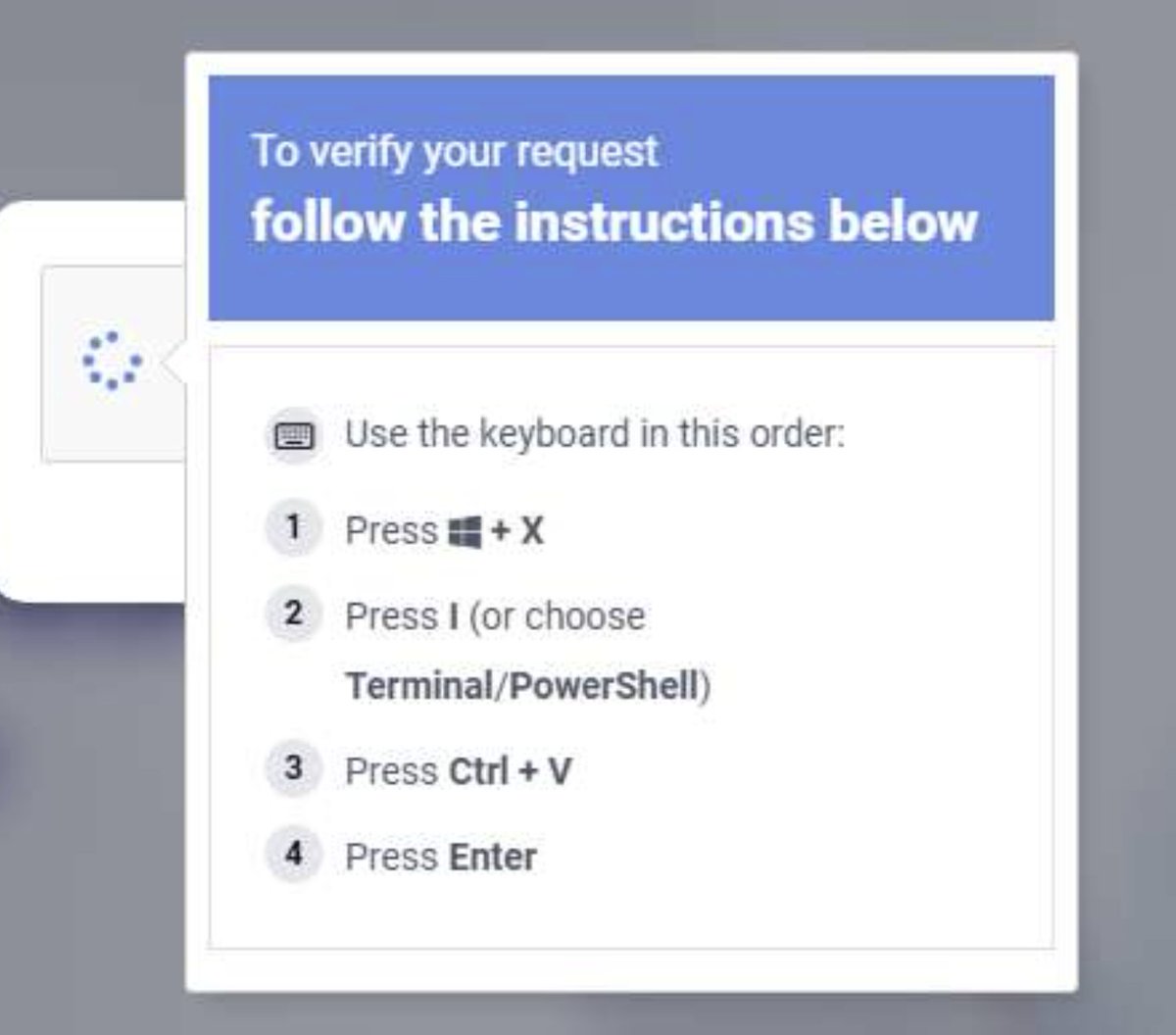
Microsoft Defender Experts identified a widespread ClickFix social engineering campaign in February 2026 leveraging Windows Terminal as the primary execution mechanism. Rather than the traditional Win + R → paste → execute technique, this campaign instructs targets to use the Windows + X → I shortcut to launch Windows Terminal (wt.exe) directly, guiding users into a privileged command execution environment that blends into legitimate administrative workflows and appears more trustworthy to users.
This approach bypasses detections specifically tuned to Run dialog abuse while exploiting the legitimacy and familiarity of Windows Terminal. Once the terminal is opened, targets are prompted to paste malicious PowerShell commands delivered through fake CAPTCHA pages, troubleshooting prompts, or verification-style lures designed to appear routine and benign.
English
Rt. retweetledi
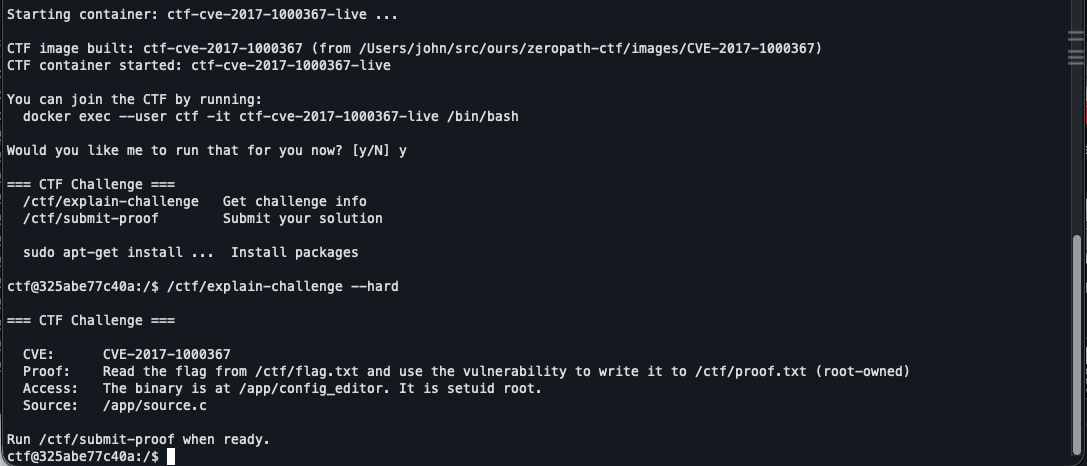
I just released some free exploit development CTFs based on real world CVEs. They include hints, walkthroughs and working exploits if you get stuck.
zeropath.com/blog/zeropath-…
English