Vanstra
9.5K posts



You may hate Android’s new 24-hour sideloading rule, but I love it androidauthority.com/android-24-hou…
English

@JohanGerar60902 @geenstijl Maar, (flex)woningen voor statushouders zullen zeker worden gebouwd. De mensen op de wachtlijsten moeten dan nog maar even langer wachten.
Nederlands

@geenstijl Nee, zo zit het niet. Gemeentes bepalen of er voorrang is. En einde van het jaar is de nieuwe wet, omdat die van Mona niet goed is. Pas dan vervalt de voorrangspositie landelijk. Dus linkse gemeentes kunnen gewoon voorrang geven. Rechtse doen dat gewoon niet.
Nederlands
Minister Boekholt-O'Sullivan zet STREEP door wet Mona Keijzer die voorrang statushouders verbiedt geenstijl.nl/5188954/minist…
Nederlands

@LidwienGerrits1 @k_poot Een groot deel heeft ook te maken met links beleid. De pot verteren op andermans geld.
Nederlands

@k_poot De 'gaatjes' zijn ontstaan doordat de landelijke overheid steeds meer taken heeft overgeheveld naar gemeenten, zonder dat zij daar de financiële middelen voor krijgen. Álle gemeenten worstelen met forse begrotingstekorten.
vng.nl/artikelen/geme…
Nederlands

Mooi, wat Zita Pels zegt bij #pauwendewit: "Wat moet ons antwoord zijn richting de rechtse partijen? Wees schaamteloos links! Spreek je scherp uit op je eigen linkse thema's." "Stel je inwoners centraal, en niet de markt".
Niet verkeerd lijkt me.
Nederlands
Vanstra retweetledi

March 1st incident report
On March 1, 2026, Bitrefill was the target of a cyberattack. Based on indicators observed during the investigation - including the modus operandi, the malware used, on-chain tracing and reused IP + email addresses (!) - we find many similarities between this attack and past cyberattacks by the DPRK Lazarus / Bluenoroff group against other companies in the crypto industries.
The initial access originated through a compromised employee laptop, from which a legacy credential was exfiltrated. That credential provided access to a snapshot containing production secrets. From there, the attackers were able to escalate their access to our broader infrastructure, including parts of our database and certain cryptocurrency wallets.
We first detected the incident after noticing suspicious purchasing patterns with certain suppliers. We realized that our gift card stock and supply lines were being exploited. At the same time we found some of our hot wallets being drained and funds transferred to attacker-controlled wallets. The moment we identified the breach, we took all of our systems offline as part of our containment response.
Bitrefill operates a global e-commerce business with dozens of suppliers, thousands of products, and multiple payment methods across many countries. Safely switching all these things off and bringing them back online is not trivial.
Since the incident, our team has been working closely with top industry security researchers, incident response specialists, on-chain analysts and law enforcement to understand what happened and how we can prevent it from happening again. A sincere thank you to @zeroshadow_io, @SEAL_Org, @RecoverisTeam and @fearsoff for their rapid response and support throughout this ordeal.
What about your data
Based on our investigation and our logs we don’t have reason to think that customer data was the target of this breach. There is no evidence that they extracted our entire database, only that the attackers ran a limited number of queries consistent with probing to understand what there was to steal, including cryptocurrency and Bitrefill gift card inventory.
Bitrefill was designed to store very little personal data. We are a store, not a crypto service provider. We don’t require mandatory KYC. When a customer chooses to verify their account - e.g. to access higher purchasing tiers or certain products - that data is kept exclusively with our external KYC provider, with no backups in our system.
Still, based on database logs, we know that a subset of purchase records was accessed and we want to be transparent about that.
Around 18,500 purchase records were accessed by the attackers. Those records contained limited customer information, such as email addresses, crypto payment address, and metadata including IP address.
For approximately 1,000 purchases, specific products required customers to provide a name. That information is encrypted in our database. However, since the attackers may have gotten access to the encryption keys, we are treating this data as potentially accessed. Customers in this category have already been notified directly by email.
At this time, based on the information currently available, we do not believe customers need to take specific action. As a precaution, we recommend remaining cautious of any unexpected communications related to Bitrefill or crypto. If this assessment changes, we will of course immediately inform those affected.
What we are doing
We have already significantly improved our cybersecurity practices, but vow to continue to draw learnings from this experience to make sure user and company balances and data remain maximally safe. Specifically we’re:
-Continuing thorough cybersecurity reviews and pentests with multiple external experts and implementing recommendations;
-Further tightening internal access controls;
-Further improving logging and monitoring for faster detection and more effective response; and
-Continuing to refine and test our incident response procedures and automated shutdown procedures.
The bottom line
Getting hit by a sophisticated attack sucks (a lot). We’ve been in business for over 10 years and it’s the first time we’ve been hit this hard. But we survived.
Bitrefill was designed to limit the impact if something like this ever happened. Bitrefill remains well funded, has been profitable for several years and will absorb these losses from our operational capital.
Almost everything is back to normal: payments, stock, accounts. Sales volumes are also back to normal, and we are eternally thankful to our customers for your continued confidence in us.
We will continue to do our best to continue deserving your trust.
Thank you!
English

@vanstra Kijk dat doet me deugd, misschien moeten we de 'lucky few' verzamelen
Nederlands

UITVRAAG: Hoeveel van de mensen hier gebruikt #Nostr?
nos.social/blog/nostr-use…
Nederlands
Vanstra retweetledi

🇪🇺🎉 HUGE VICTORY! Thanks to your protests, the EU Parliament voted today to END untargeted mass scanning! 💪
But beware: The final decision will now be made in the trilogue with EU governments. The fight continues! ⚔️
All info: patrick-breyer.de/en/historic-ch…
English
Vanstra retweetledi

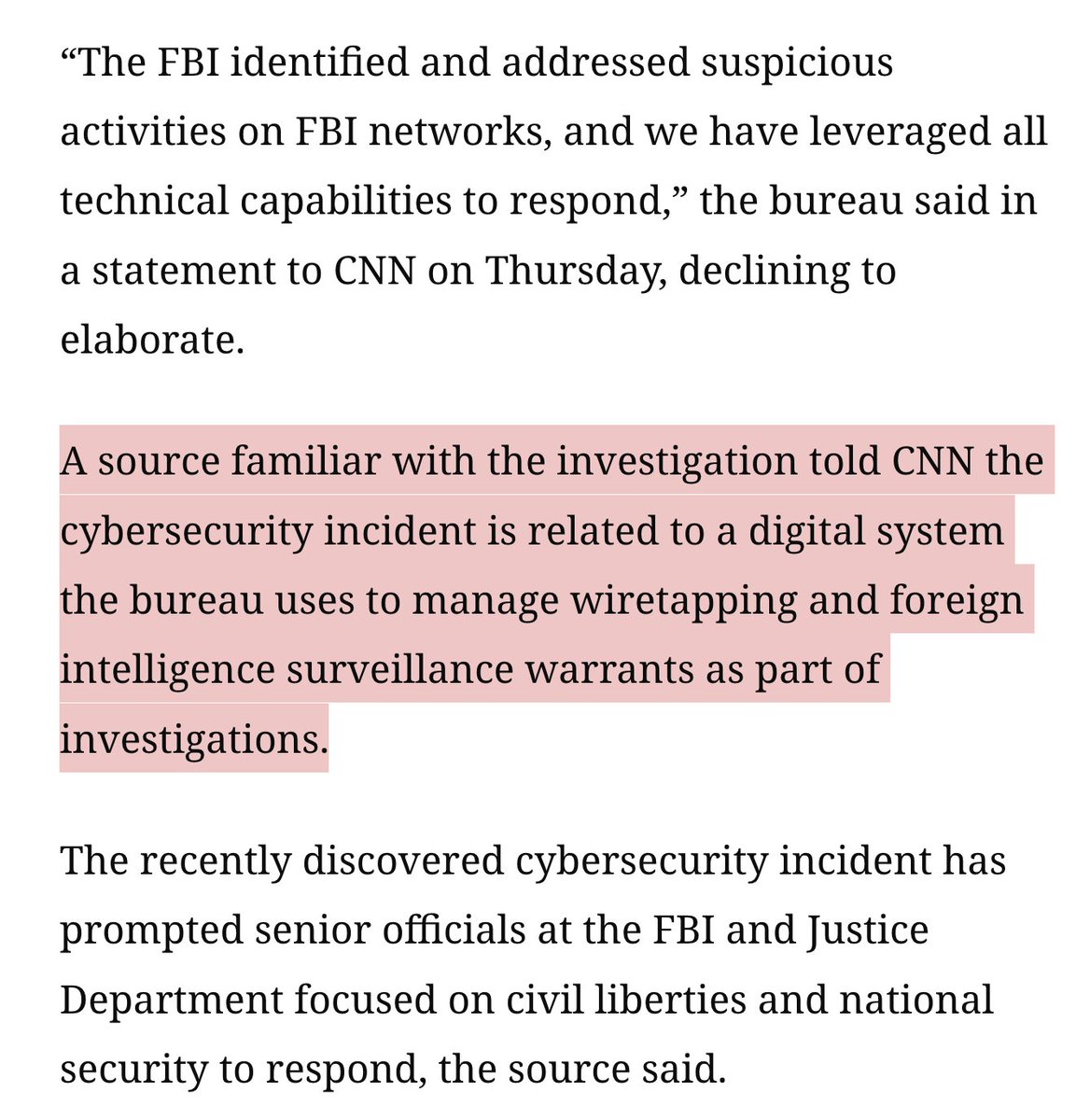
WHOA: signs an @FBI wiretapping & surveillance network got hacked.
Extremely concerning. These systems have huge potential access to every citizens sensitive data.
Making them an incredibly juicy target for foreign hacking.
By @PaulaReidCNN @snlyngaas @evanperez & @kpolantz
English
Vanstra retweetledi
Vanstra retweetledi
Vanstra retweetledi

Today, the final negotiations on Chat Control 2.0 begin between the European Commission, the European Parliament, and the Council of the EU.
Although the requirement for mandatory scanning (including end-to-end encrypted messaging services) has been removed, several problematic elements remain in the Council's position. For instance, the Council wants to demand identity verification to use messaging services (including end-to-end encrypted). This would pose significant risks to dissidents, whistleblowers, and others, and create a chilling effect on free speech.
We hope the European Parliament stands firm against any wording that paves the way for mass surveillance and censorship. Cyprus, currently holding the Presidency of the Council of the EU, aims to conclude the negotiations by June.
A reminder of the corrupt backstory behind the Chat Control proposal and the involvement of Ashton Kutcher and his company Thorn: mullvad.net/why-privacy-ma…
English
Vanstra retweetledi

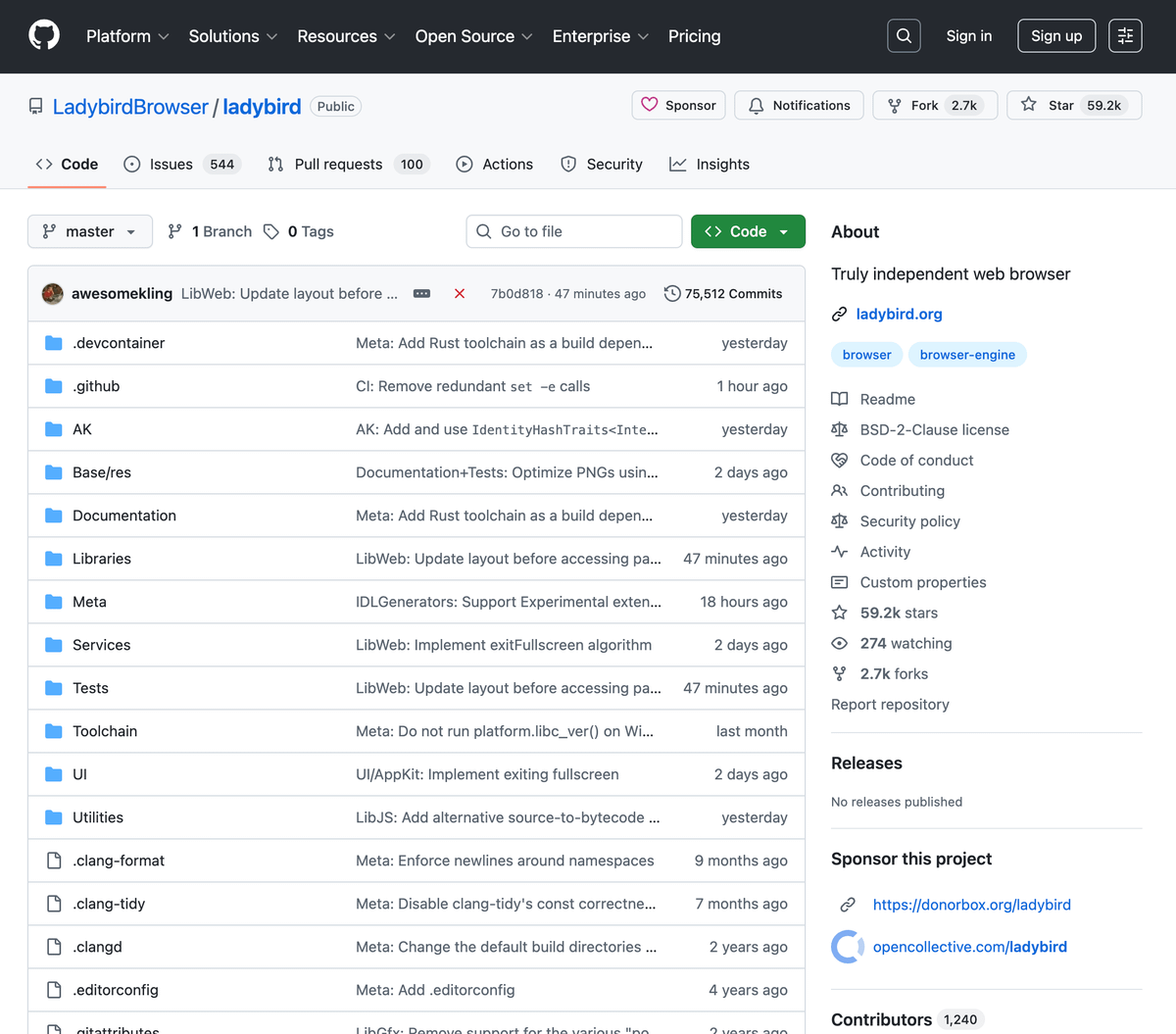
🚨 BREAKING: A team of engineers just said enough and built a browser from absolute scratch.
No Chrome code. No Firefox code. Nothing recycled.
Ladybird Browser is:
→ A 100% independent browser engine
→ Written in C++ from zero
→ Not a Chromium fork like every "new" browser you've ever seen
→ Completely open source anyone can contribute
Chrome secretly runs 95% of the internet right now.
This is the open source project trying to change that.
59,200+ stars on GitHub.
English
Vanstra retweetledi
Vanstra retweetledi

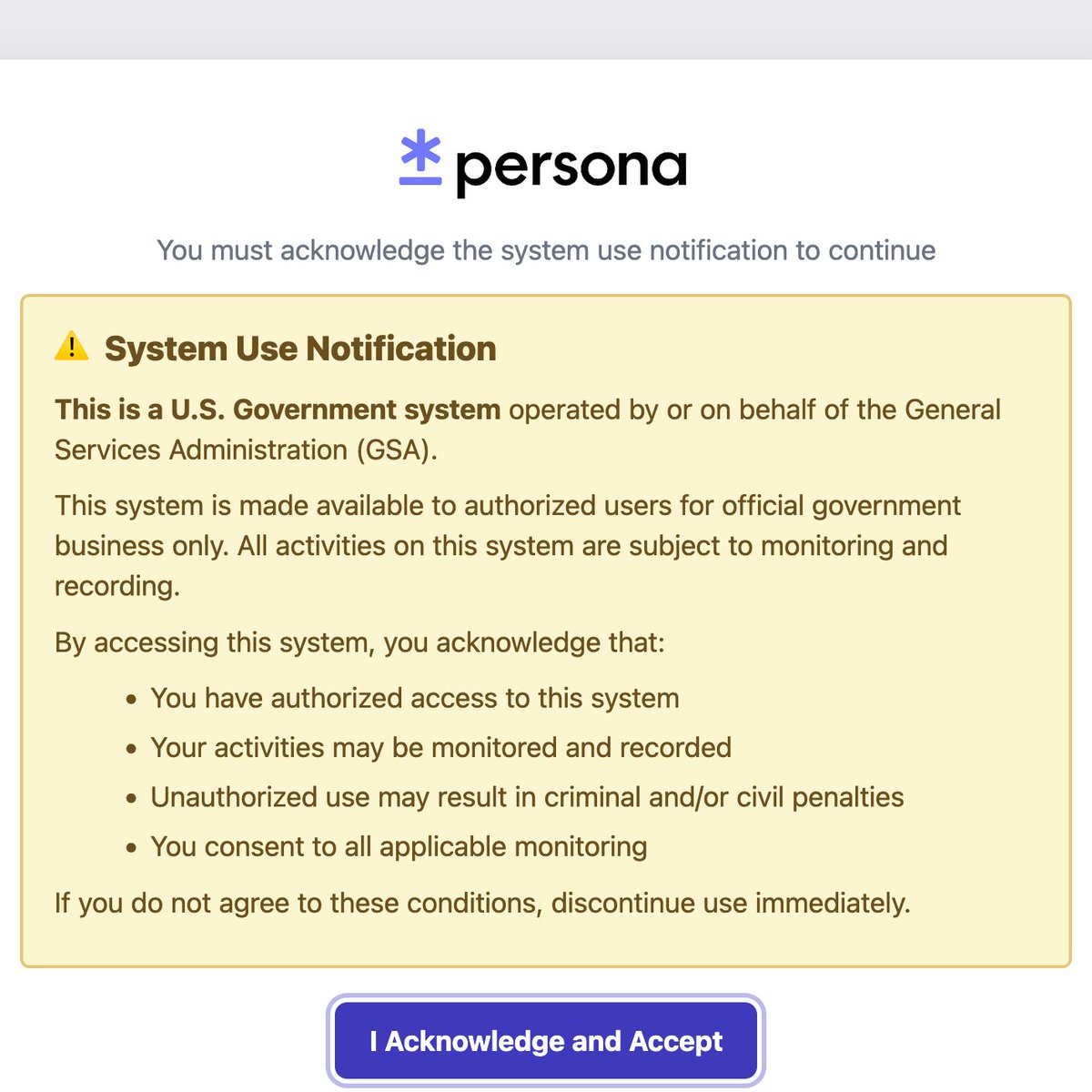
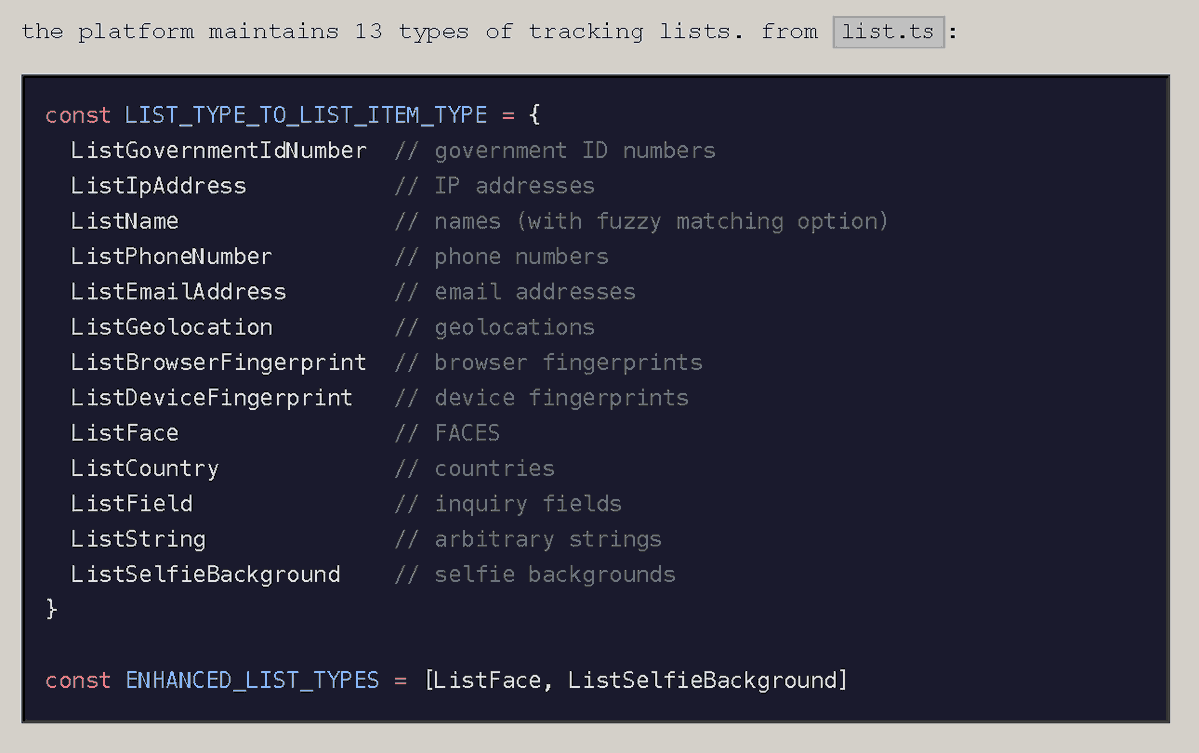
‼️ BREAKING: Researchers have uncovered secret AI surveillance projects linked to KYC provider Persona and OpenAI, sending user data to the US government.
Code references include intelligence program codenames "Project SHADOW" and "Project LEGION."
Analysis of source code revealed OpenAI's user verification systems includes biometric tracking, facial scanning, political screening, and intelligence reporting.
Researchers also discovered ONYX on Persona's government server — matching ICE's $4.2M AI surveillance tool — which scrapes social media and the dark web, builds digital footprints, tracks emotional sentiment, assigns risk scores across 300+ platforms and 28B+ data points, and flags individuals for "violent tendencies."
None of it was hidden. It was all internet-facing.
English
Vanstra retweetledi
Vanstra retweetledi

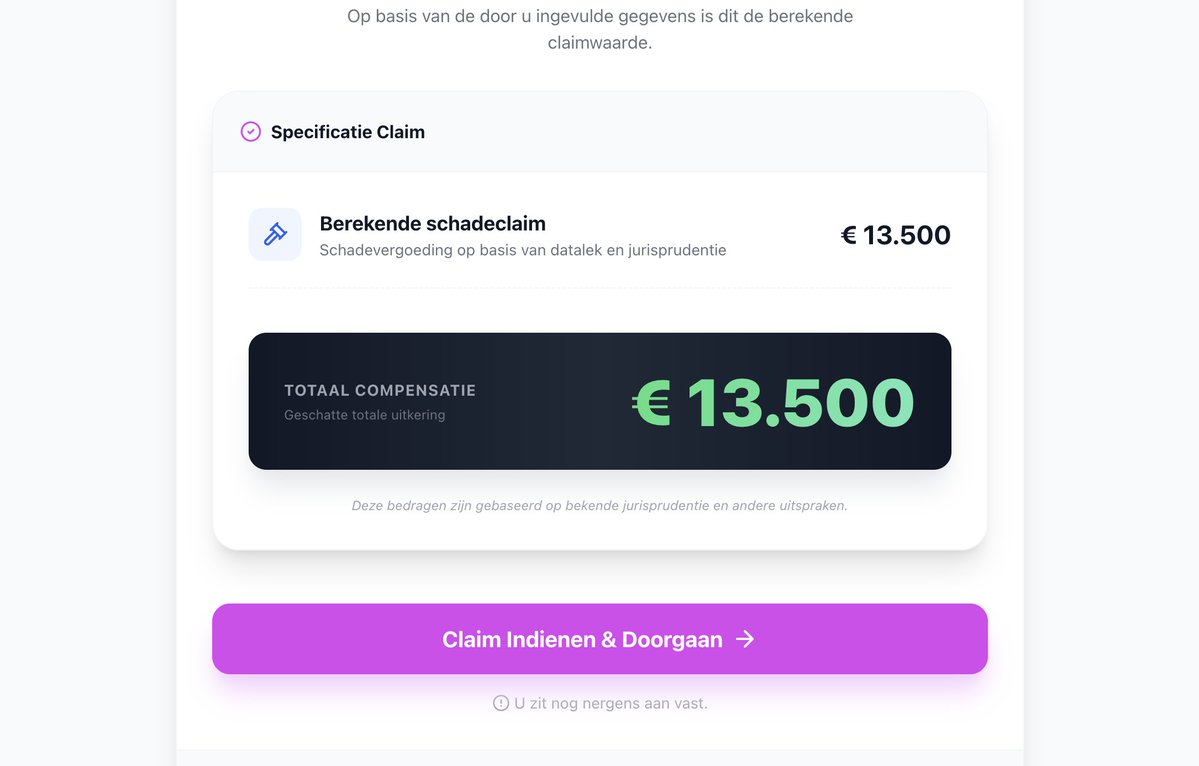
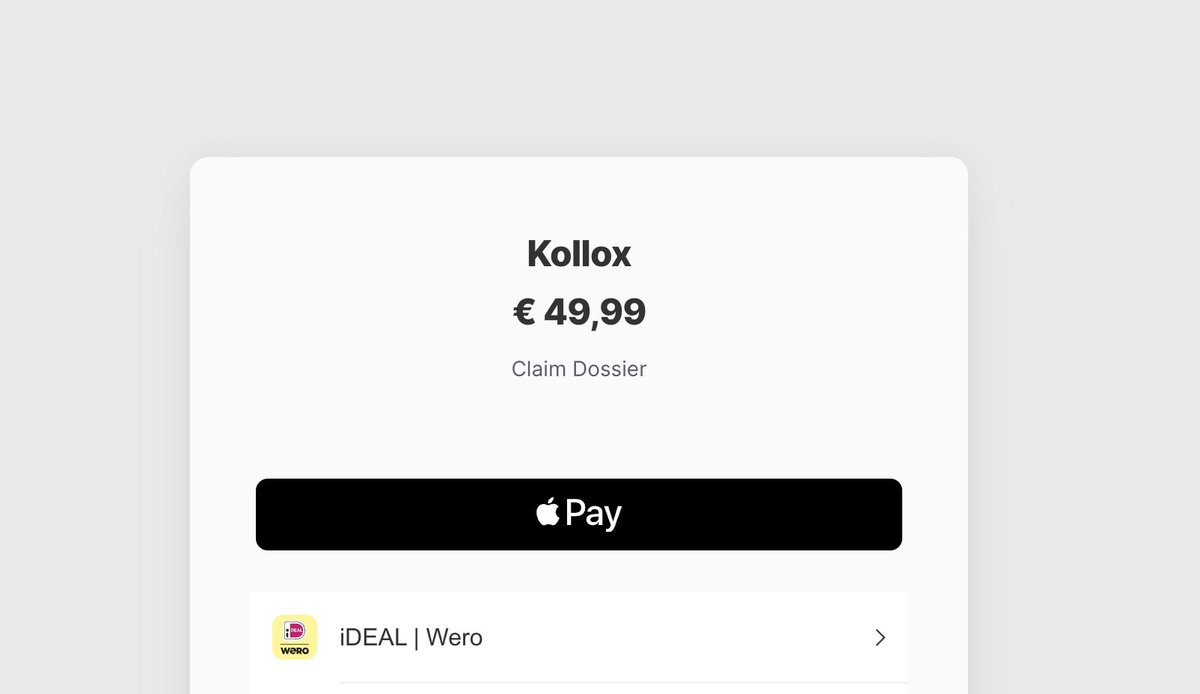
Opgepast: een nepwebsite belooft compensatie voor slachtoffers van het Odido-datalek. De site odidoschadevergoeding[.]nl ziet er gelikt uit.
De oplichters zitten in Malta en vragen 50 euro te betalen voor een claim die natuurlijk nooit wordt ingediend.
rtl.nl/nieuws/economi…

Nederlands

@Remcobus1967 @AndersonAfDMdEP En het mooiste is dat de EC zichzelf en andere Europese politici wil uitsluiten van deze 'chat control', omdat ze weten wat het gevaar is.
Nederlands

“De EU wil privéberichten die vanaf je telefoon worden verstuurd scannen... in de praktijk betekent dit dat alles wat mensen zeggen wordt gescand... Dat heet surveillance... het onder surveillance plaatsen van de eigen burgers is bekend in totalitaire regimes.”
@AndersonAfDMdEP
Nederlands

@frankv1971 @DavidBoerstra Bijvoorbeeld alle informatie over de Chat Control die de EC wil gaan invoeren. De informatie die er nu over bekend is, komt voort uit lekken van die informatie.
Nederlands

@DavidBoerstra Nu ben ik benieuwd over welke censuur jij het hebt. Bedoel je fake news zoals het stelen van de Amerikaanse verkiezingen in 2020, de corona vaccinaties die massaal doden veroorzaken?
Nederlands

De V.S. bouwt een Digitale luchtbrug zodat wij uit de kooi van Ursula en haar censuurmachine kunnen ontsnappen.
#historyrepeats
DogeDesigner@cb_doge
BREAKING: US State Department is building an online portal called freedom .gov to let people in Europe and beyond access content banned by local governments. This will bring an end to censorship by the European Commission. Free speech is going global again. Freedom wins.
Nederlands
Vanstra retweetledi

@michelportier80 @arnowellens Het is gewoon chantage. Je moet akkoord gaan met de overheid, zo niet dan rest 'onderdrukking'. Je hebt geen vrijheid meer, maar privileges die je krijgt van de overheid.
Nederlands






