Wire Network
4.3K posts


Wire Network
@WireNetwork
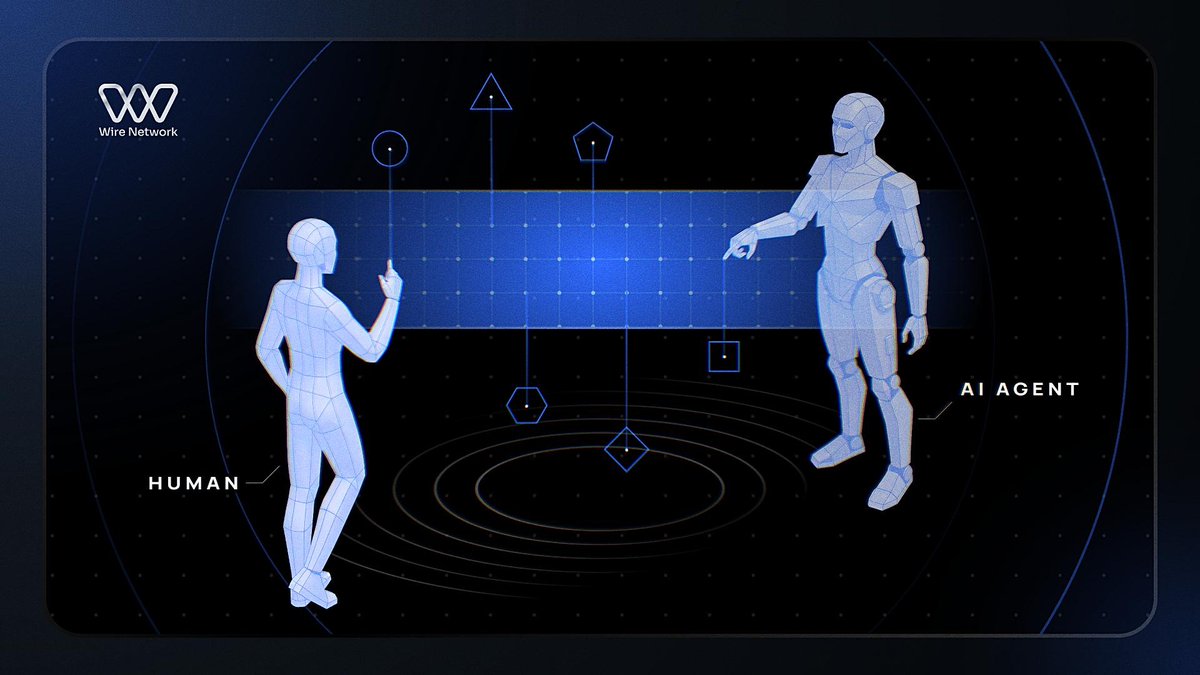
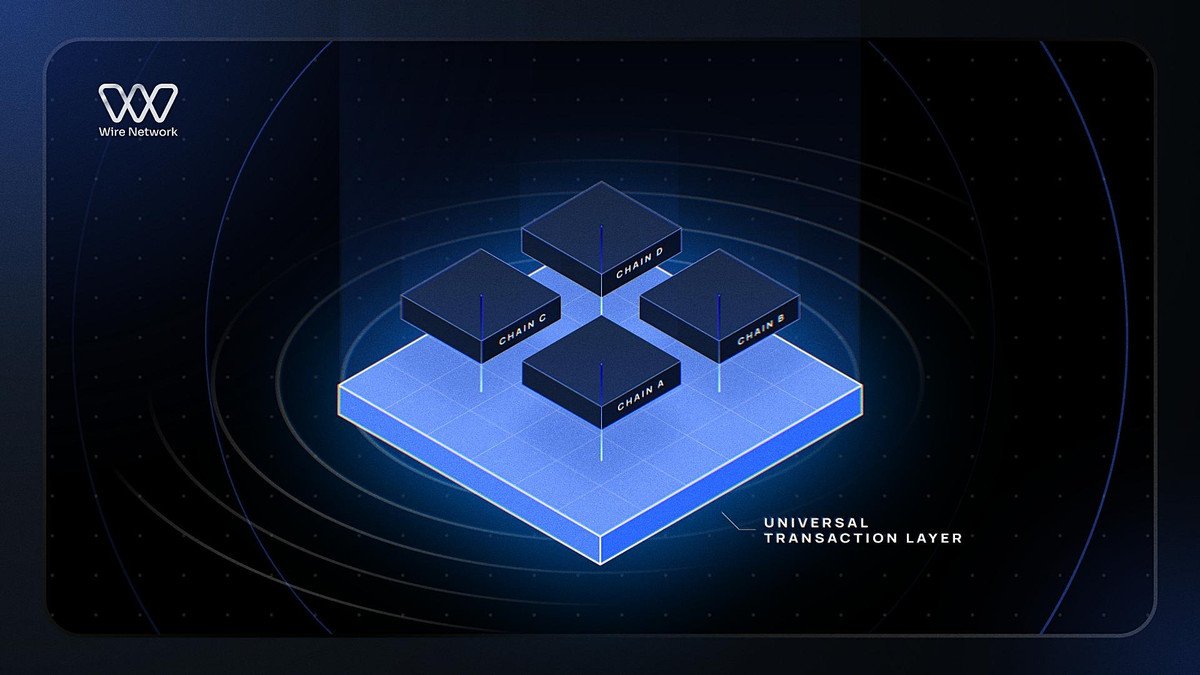
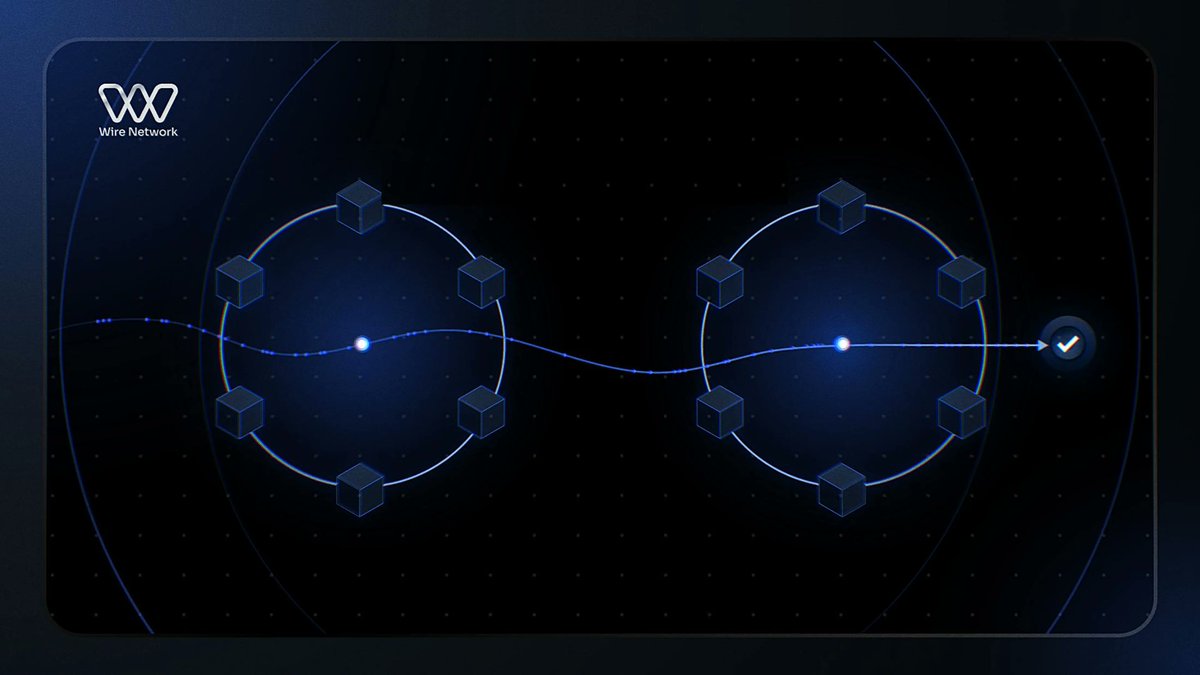
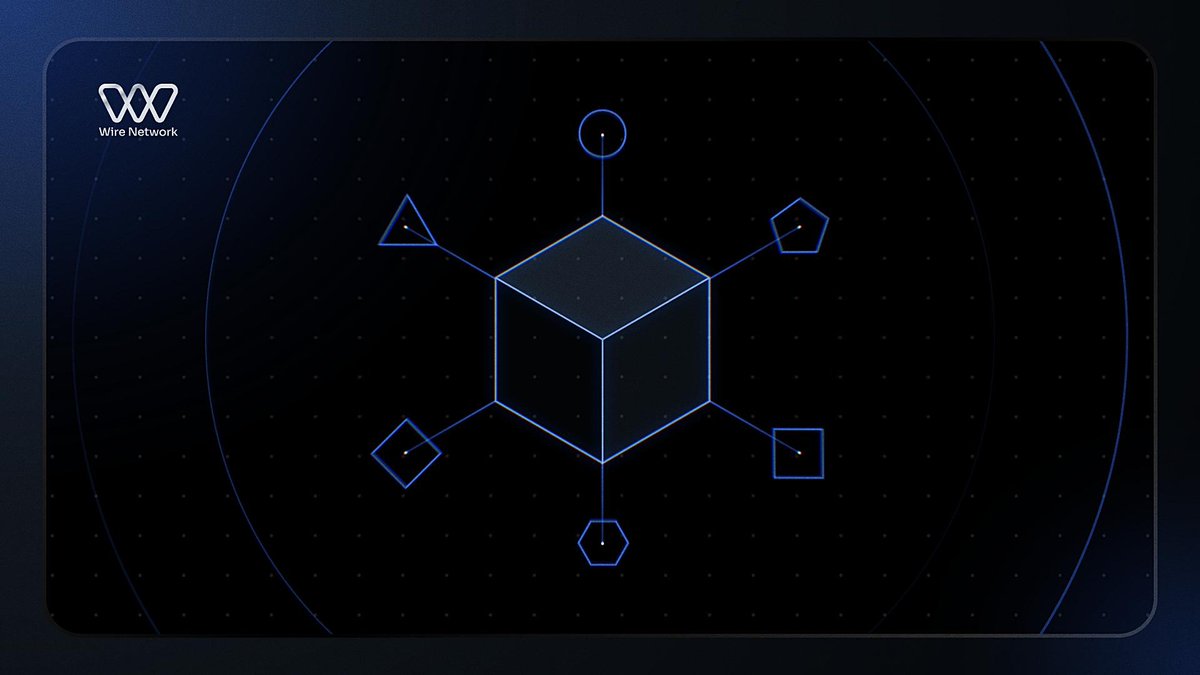
Cross-chain infrastructure for humans and AI agents. Build once, deploy across all supported chains. No bridges. Mainnet summer 2026.

@BossMon_02 @MyNeighborAlice Fragmented liquidity has been the biggest hurdle for DeFi growth.

Rather than provide additional info on how and why LayerZero Labs' centralized infrastructure was infiltrated by North Korean (DPRK) hackers, which resulted in the $292M rsETH bridge exploit Bryan decides throwing the user under the bus the first time wasn't good enough, they just had to do it again for good measure! All for the crime of trusting the LayerZero Labs team and their infra, using a 1/1 config that ~50% of LZ OApps use (per @Dune), that the LZ Labs DVN supported (until it was blocked), and that the LZ Labs team monetized (DVN fees) Why take responsibility, and therefore legal liability, over the exploit when finger pointing is just as good 👆👉👇👈 And nevermind the fact that there are multiple chains in the LZ docs where the LZ Labs DVN is the only one listed, and therefore the only possible config ! Why did the LZ Labs DVN support a 1/1 config up until now if it was such an obviously dangerous thing? Why isn't this config blocked at the protocol level if its always been so obviously bad? People have been pointing out the massive centralization problem in the LayerZero ecosystem for YEARS now, including the 2/2 multisig Stargate bridge run by the LZ Labs team (does anyone genuinely think a 2/2 multisig bridge setup is really all that much better than 1/1?) But only after the $292M bridge hack is such centralization now such an obvious risk, give me a break Why should anyone integrate LayerZero, knowing they're going to be thrown under the bus as disposable meat the moment the LZ Labs fucks up and gets hacked by North Korea?













Check out Week 8 of the Wire Incubator where @impact_ape and @perryazevedo talked about building modern products and Sea Ansley, co-founder of AISA, showcased @aisuperagency. twitter.com/i/broadcasts/1…

Another bridge exploit, another reminder that cross-chain risk is still very real. Moving funds from one chain to another shouldn’t expose users to that level of vulnerability in the first place. The pattern keeps repeating; bridges introduce extra layers, and those layers become the weakest points. When security depends on external systems, it’s only a matter of time before something breaks. A model that settles assets natively from chain to chain without bridging is a much cleaner direction. If @Pact_Swap can consistently deliver that, it’s addressing the root cause not just the symptoms.

If your protocol uses an oracle, your threat model includes more than “wrong price.” It includes: - data source compromise - market manipulation - update latency - governance or config drift Treat oracle risk as a system, not a line item.






When people ask where to start in Web3 security, I give the same answer: Start with an attack class library and work through it systematically: - access control - oracle manipulation - reentrancy - DoS - MEV Most people skip this. It's why they keep getting surprised by the same patterns.