Monerista
374 posts

Monerista
@Ridolfox
Gratuitas Coffee https://t.co/sPSJVyWHfe


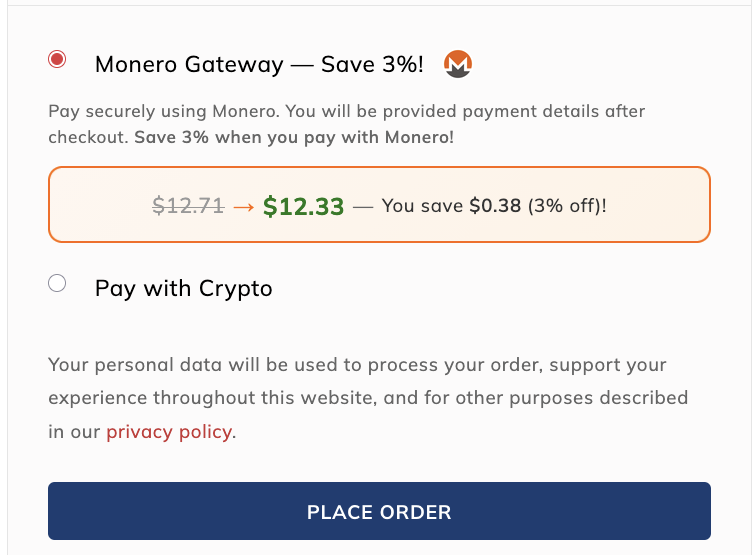
XMR swaps are back ON. We appreciate everyone's patience, we have had to be as cautious as possible. We can't support DPRK to continue getting funding and exploiting more protocols in crypto, as well as their terrible regime that's a cancer to the rest of the civilized world. This policy change only applies to OFAC Sanctioned countries like DPRK. They are a hostile nation state and an enemy to us all. They bankroll their missiles/nukes programs with stolen crypto, use cyberattacks against hospitals and run concentration camps on their own citizens. I hope everyone in crypto comes together to prevent this from continuing. This is decentralization, a group of people who care about this space collectively deciding we don't want to allow such a hostile regime in our system. Decentralization is us choosing together, what we will and won't tolerate. Perhaps I'm being biased here, but they have also repeatedly tried to exploit and infiltrate the Wagyu protocol over the past few months. They have tried to use extremely sophisticated social engineering tactics on my domain host, as well as servers I have been using. I have luckily been able to prevent it (as I am chronically online) and fixed every potential attack vector that they were targeting. You guys have no idea how advanced they are, if you leave them 1cm of space to infiltrate something, they will keep probing and trying until they are successful. Fuck DPRK. They don't have to ruin things for the rest of us. Enjoy swapping guys. wagyu.xyz

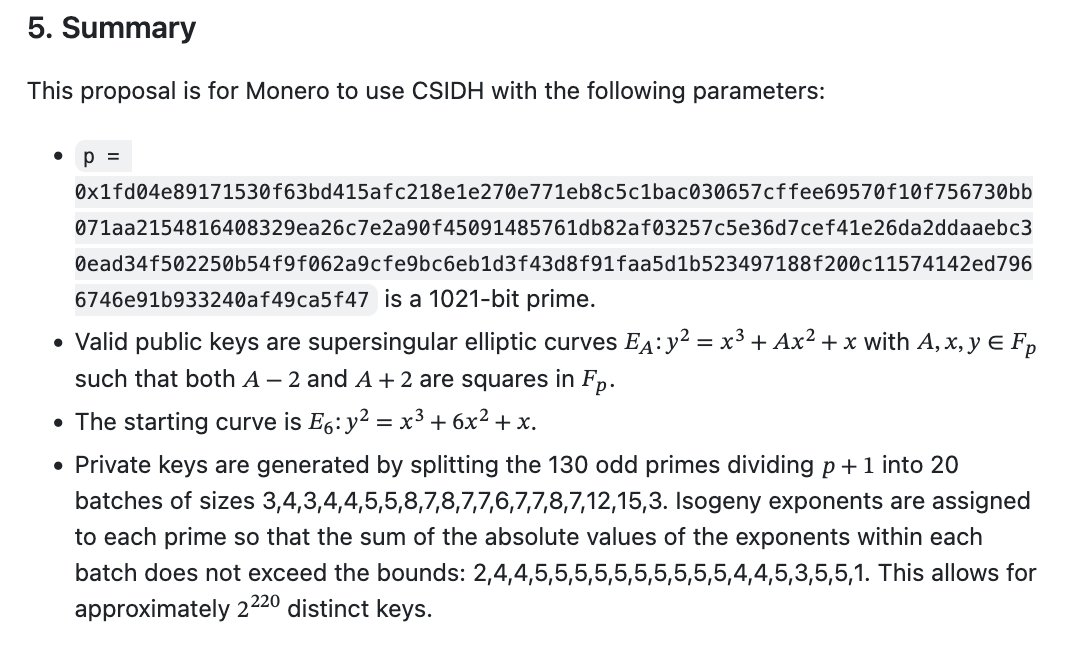
tevador presented a simplified summary of the 7 options (Option A/B combined with CSIDH-512/1024/2048 or NTRU-509) and invited comments on proceeding with BC1024 (CSIDH-1024). The MRL compared it to Zcash’s inferior O(N) scanning approach, examined de-anonymization risks for HD wallets/Carrot addresses/shared view keys, self-sends’ privacy value, and why static reusable addresses remain critical. CSIDH was favored over lattice KEMs like NTRU due to no address-generator collusion risk and better multi-output performance/tx sizes. UX concerns (long addresses ~600+ chars, QR scannability) were tested live with examples; hardware-wallet checksums and merchant/RPC adoption were addressed. No major opposition; further comments welcomed. (See full GitHub thread: #issuecomment-4281932714" target="_blank" rel="nofollow noopener">github.com/monero-project…
and related github.com/monero-project….) tevador: I wrote a simplified summary without any gory math details. The point is to agree on one of the 7 choices. sgp_: Ty tevador for all your work on this and your work organizing this rbrunner: Likewise ofrnxmr: seconded rucknium: Yes, thank you tevador :) tevador: For comparison, Zcash is going with something similar to AN509, but worse, because they will have O(N) scanning time with N = number of addresses. plowsof: +1 tevador: Does anyone have any comments? Any opposition to moving forward with BC1024? rucknium: I am going to ask some noob questions. If a PQ adversary has one of the Carrot addresses of a wallet, they can de-anonymize the txs of the wallet that share a common private key seed, e.g. the Hierarical Deterministic (HD) wallet seed phrase. Is that correct? Then an impractical countermeasure is to eliminate HD wallets and go back use-once private keys for each tx packed into wallet.dat. Would that actually work? tevador: They can deanonymize transactions that share a private view key. You can avoid that by having a different view key for each transaction, but that means O(N) scanning time. tevador: Different view key for every address* jeffro256: rucknium: For the new Carrot key hierarchy, the QA can deanonymize the transaction graph of the output receives externally. They cannot deanonymize the outputs which were self-sended rucknium: Another hypothetical: Why would a party that is cooperating with a PQ adversary set up the infrastructure to send XMR to this special PQ address? Wouldn't they just say "Sorry, you must use the old addresses"? Isn't this a big part of the threat model that these PQ addresses are , um, addressing? tevador: Yes, but self-sends are not very important in practice anyways. jberman: A comment on potentially large (1kb+) address length: perhaps we could implement something like ASCII qr codes? So instead of copying and pasting massive clunky addresses, copy pasting ASCII qr codes. I see that the huge addresses aren't the only downside to the algos with huge addresses (pruned tx sizes seem lager too, which is significant and also affects scan time from downloading), but perhaps there is a solution that renders them not so terrible tevador: If the Monero-RPC accepts the new address format, I don't see a reason for a merchant not to support it. jeffro256: tevador: It is important because it hides where the wallet sent their funds. They would also gain importance once people realize the PQ implications and begin using self-sends as such rucknium: Another question: Do these addresses get Monero closer, at all, to a countermeasure to PQ counterfeiting? I assume no, but I wanted to check. tevador: No, this is purely for PQ privacy jeffro256: A QA can, in many circumstances, calculate the spending location of externally received funds, not just where they were received. So a self-send in between would hide the spend locations of those outputs jeffro256: rucknium: The mitigation of using ephemeral private keys for each tx would work. Note that your wallet scanning time would be O(N) for the number of pairs generated tevador: Yes, but the QA learns the received amounts to the known address in any case, whatever you do afterwards, which is a biggest leak IMO. rucknium: If the keys are designed to be single-use, then you could stop scanning after you found the first receive tx. tevador: Addresses in Monero are not single-use. jeffro256: tevador: Fair rucknium: Going back to 2009 jeffro256: tevador: There could a specific address format which singles "hey don't use this twice please" jeffro256: signals tevador: Single use addresses would prevent the whole-wallet leak, but don't prevent the main problem of leaking the receiving transaction. jeffro256: tevador: It's the biggest leak if trying to conceal income. Not the biggest leak if trying to conceal purchases rucknium: I am developing the hypothetical with the sending adversary you don't trust fully, on privacy at least. So you would stop listening for txs after you got the one from the untrusted party. tevador: I think you can already do this with a throwaway wallet seed. rucknium: Yes. It would be a UX change. jberman: tevador sorry if this is included somewhere, but why is the 2/16 tx size so much larger than the 2/2 tx size for NTRU-509 than it is for the other algos? tevador: How would you do donation addresses with a single-use address format? tevador: jberman: Good question. NTRU needs 16 ciphertexts in that case, but CSIDH needs just 1 shared public key for all 16 outputs in option A. ixr3: It will take on tremendous importance! >

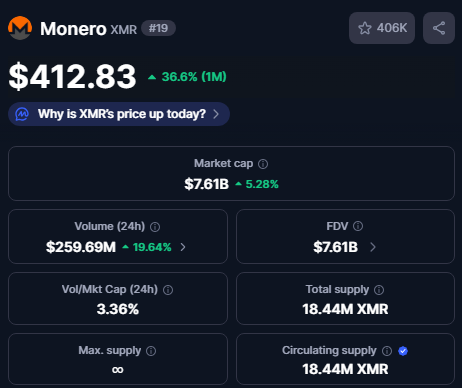
Remember: if your life depended on acquiring or selling Monero, you would be cut off because some spicy bois had the same idea. This is NOT freedom tech.




Austrian right-wing activist @Martin_Sellner, who has been debanked and blocked on CEXs, praises Monero and Cake Wallet.