ทวีตที่ปักหมุด

Digtool: A Virtualization-Based Framework for Detecting Kernel Vulnerabilities
usenix.org/conference/use…
English
TinySec
319 posts


@TinySecEx
Security Researcher. Usenix 2017 ,MSRC top 100 2016/2017/2018. All the tweets are totally my personal opinions, not about any of my current employer stuff.









>Let's hope a bug in some 1990s game codec doesn't get some ffmpeg core developer popped.


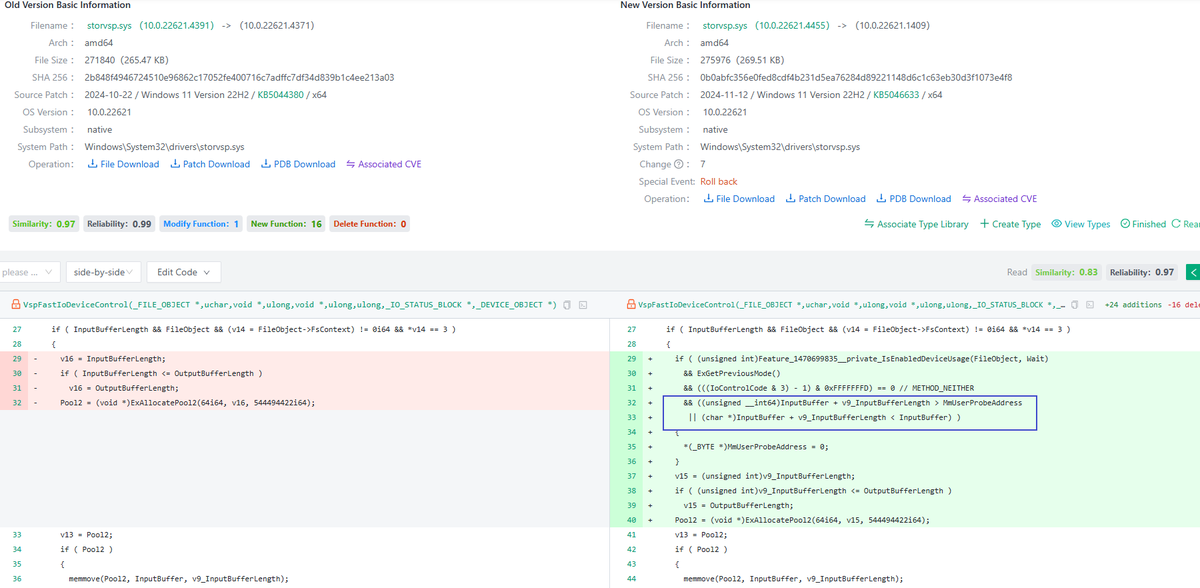
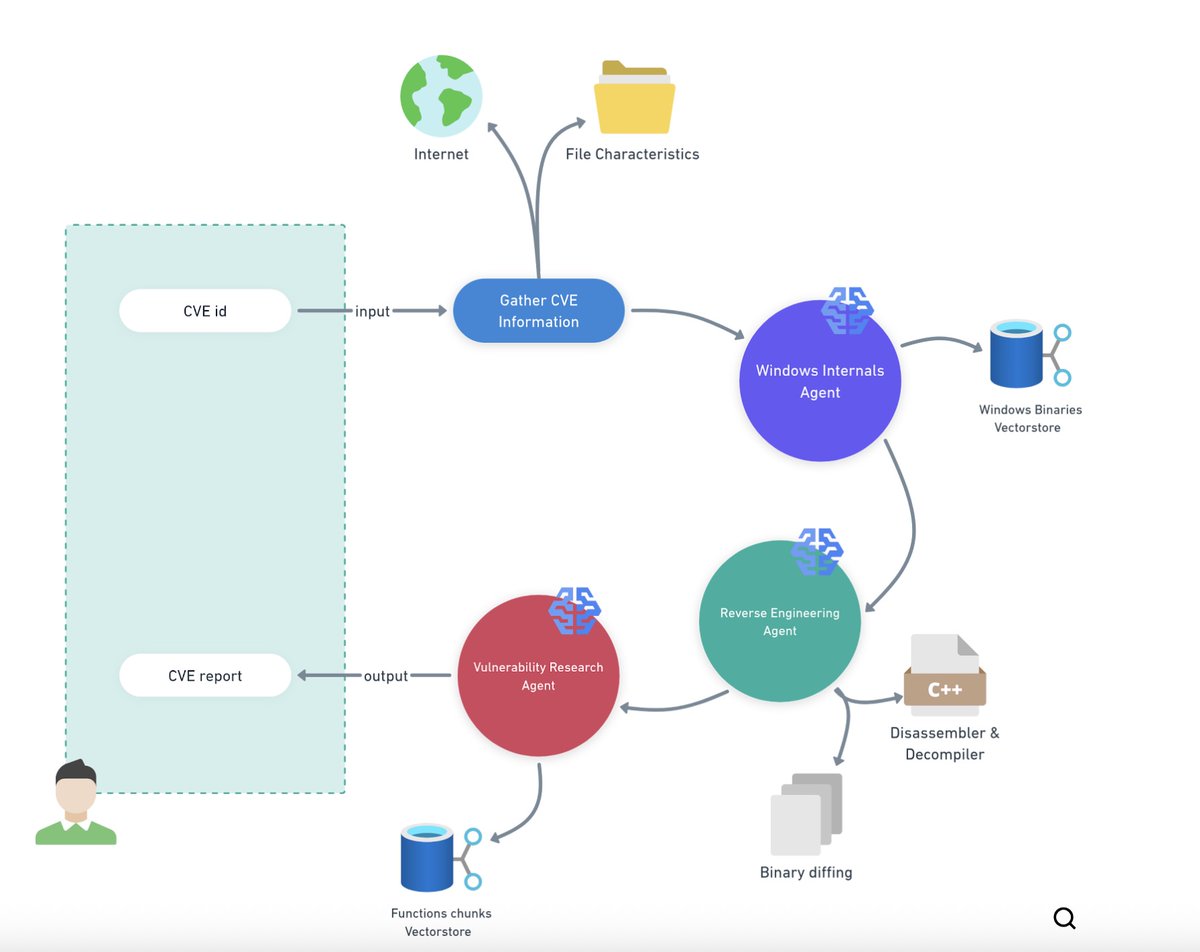
I have posted the slides for the talk @chompie1337 and I gave this past weekend at @h2hconference -> The Kernel Hacker’s Guide to the Galaxy: Automating Exploit Engineering Workflows #H2HC github.com/FuzzySecurity/…