

spencer
49.3K posts


@techspence
🛠️ Former Sysadmin, now Pentester | Microsoft MVP | Helping IT teams make their environment harder to attack | @SecurIT360 & @CyberThreatPOV




I got mad about people defending MCP so I made this video. The first minute is just me being very mad, but then I tried to contribute something of value after that. youtube.com/watch?v=m0VyZU…


CISA urges US orgs to secure Microsoft Intune systems after Stryker breach bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…

Microsoft introduces Backup and Recovery for Microsoft Entra ID! Entra Backup and Recovery solution enables you to quickly recover from malicious attacks or accidental changes by reverting your core tenant objects to any previous state within the last 5 days. With automated backups and granular recovery capabilities, it ensures minimal downtime and supports your business continuity in the face of unexpected disruptions. Entra automatically generates one backup per day, retaining the last 5 days of backup history. You can recover key properties of the following core tenant objects: - Users - Groups - Applications - Conditional access policies - Service principals - Organization - Authentication methods - Authorization policy - Named locations #EntraID #Microsoft365 #Microsoft
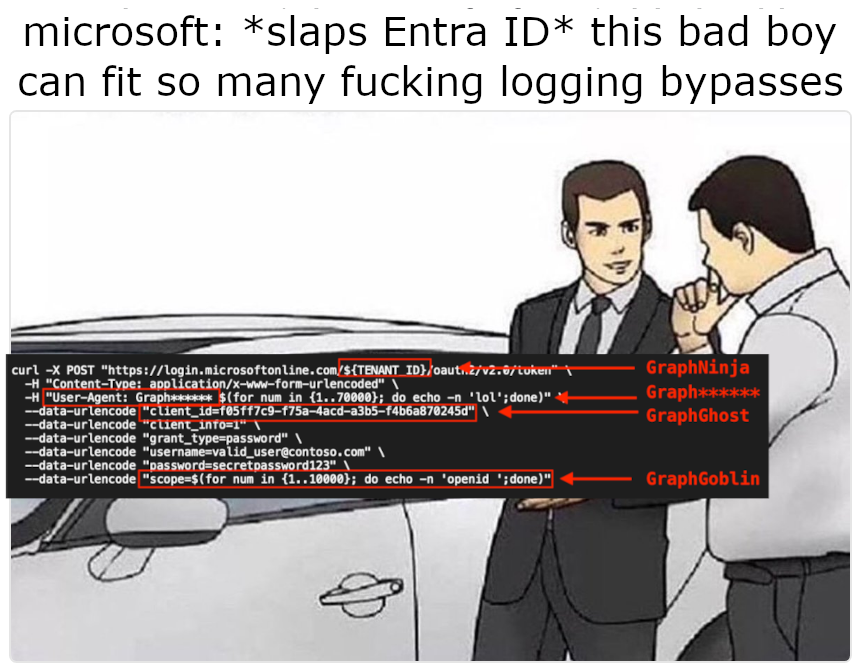
Who knew a really long string could make an Entra ID login disappear from the logs entirely? In our #blog, @nyxgeek breaks down how overflowing #Azure's sign-in logging mechanism allowed access tokens to be issued without a single log entry. Read it now! hubs.la/Q047xTVc0




The Trump administration is not considering allowing private companies to carry out cyberattacks on behalf of the government, White House officials said this week, pushing back on speculation about the role of industry in U.S. cyber operations therecord.media/offensive-cybe…




