Argha 🏏 📚 💻
30.1K posts


Argha 🏏 📚 💻
@StringsVsAtoms
🌏 वसुधैव कुटुम्बकम् - 'the world is one family' 🌍
India Tham gia Mayıs 2012
7.5K Đang theo dõi438 Người theo dõi
Tweet ghim
Argha 🏏 📚 💻 đã retweet

A major blow to the deep-rooted terror conspiracy involving #Pakistan’s ISI and the pro-Khalistan Elements.
Continuing further investigations into the Railway Track attempted IED blast at Shambhu, District #Patiala on April 27, 2026 @PatialaPolice & #SSOC Amritsar, in a joint operation, recover 01 Rocket Propelled Grenade(RPG) launcher, 01 metallic IED weighing 2.296 kg along with detonators and battery, 02 packs of RDX weighing 1.456 kg, 01 hand grenade, 03 high-end pistols with magazines and ammunition, and 02 wireless sets with headphones from Village Panjwarh Khurd, District #TarnTaran.
Investigations reveal that this terror module was backed by a #Malaysia-based entity, with financial support being routed through Malaysia. The network’s links with the #Sirhind Railway Track blast and the grenade attack on CIA #Moga are being investigated .
@PunjabPoliceInd remains firmly committed to dismantling terror ecosystems, breaking organised crime-terror networks, and ensuring lasting peace, public safety, and security across the state.
English
Argha 🏏 📚 💻 đã retweet

Modi's State Media Policy of
Punishing Well Deserved Independence & Dissent,
+ Surveillance, Raids, Fixed FIRs
& Expensive Court Cases
+ Rewarding/Bullying Godi Media,
+ Flooding Fake Social Media and Letting Troll Beasts Upon Opponents
+ Throttling Digital Media
>> HAS HAMMERED INDIAN MEDIA TO THE LOWEST POSSIBLE.

English
Argha 🏏 📚 💻 đã retweet
Argha 🏏 📚 💻 đã retweet

❗️🇩🇪 Germany says Signal is unsuitable for official communications. Members of the Bundestag have been formally urged to switch from Signal to Wire, after a Russian intelligence operation compromised the Signal account of Bundestag President Julia Klöckner.
The choice of Wire is also strategic.
Wire is a German company, headquartered in Berlin, operating under EU jurisdiction. The German federal cybersecurity agency BSI has approved Wire Bund for the exchange of classified information up to VS-NfD ("Restricted, For Official Use Only"). The platform is GDPR-compliant, NIS2-aligned, and self-hostable on European infrastructure.
Signal, by contrast, is a US-based non-profit subject to the US CLOUD Act. The CLOUD Act allows American authorities to compel data access from US-headquartered providers regardless of where the data is physically stored. For a European parliament communicating about defence, foreign policy, or intelligence cooperation, that is a structural problem before you even reach the phishing question.
Two operational reasons Wire is harder to phish:
🔴 Registration uses an email address, not a phone number
🔴 The email address is not visible to third parties
Signal binds accounts to phone numbers. Anyone who knows your number can attempt to contact you, and enterprise controls like Single Sign-On are difficult to apply.
The push is not new. Bundestag Vice-President Andrea Lindholz previously called for the same migration and proposed an outright ban on Signal for official parliamentary devices.
Important context. This is not a vulnerability in Signal's encryption protocol. The Signal protocol remains the gold standard for end-to-end encryption. The attacks succeed at the human and account-recovery layer, the layer Signal's phone-number-based identity model exposes by design.
The Bundestag move fits a much larger European pattern. Brussels is pushing GAIA-X for sovereign cloud, the EUDI Wallet for digital identity, and now Wire for parliamentary communications. The throughline is the same: reduce dependence on US-headquartered infrastructure, especially for anything touching classified or politically sensitive data.
Germany is now the highest-profile government to formally treat Signal as unsuitable for official communications. The replacement is European. Other EU members will be watching as Germany takes the lead.

English
Argha 🏏 📚 💻 đã retweet

US-India cooperation just dealt a major blow to the criminal networks flooding America with illegal drugs and stopping the flow of precursor chemicals.
U.S. Embassy India@USAndIndia
The United States deeply appreciates our partnership with Indian law enforcement, which was instrumental in disrupting key elements of this criminal network distributing precursor chemicals to cartels that manufacture and traffic illegal drugs into the United States. home.treasury.gov/news/press-rel…
English

Argha 🏏 📚 💻 đã retweet

If you’re an IT admin and you’ve never had your internal environment pentested and can’t afford one right now, do this instead:
1. Run Locksmith - fix anything that’s a High risk
2. Run ADeleginator - make sure everyone, authenticated users, domain users and domain computers doesn’t have any unsafe permissions
3. Run ScriptSentry - check for credentials in logon scripts
4. Run PingCastle - check the control paths section. It’s like bloodhound. Look for non-admins that have control paths
If you do this, your environment will be much better when you’re done fixing everything.
English
Argha 🏏 📚 💻 đã retweet

THREAD🧵
Gensis of Pakistan's "War from India's East"
EXCLUSIVE: We studied a Pakistan-based information warfare wing for 3 months. The origins of this operation traces back to August 2025, when Pakistan's Army Chief Field Marshal Asim Munir stated "We'll start from India's East." This marked Pakistan's shift from a western-front-centric posture to exploiting vulnerabilities in India's Northeast.
1/10
@aravind @ShekharGupta @spvaid @sneheshphilip @AnchorAnandN @ARanganathan72 @jsaideepak @major_pawan @easterncomd @official_dgar @OsintTV @HMOIndia @AmitShahOffice @AmitShah @PMOIndia @DefenceMinIndia @SandeepUnnithan @manupubby @ShivAroor @VishnuNDTV @gauravcsawant @dubey_ajit

English
Argha 🏏 📚 💻 đã retweet

We didn't know how an actor was using EV Certificates issued to Lenovo and others.
We now do.
From DigiCert's incident report:
"the threat actor used a compromised analyst endpoint to access DigiCert's internal support portal. The threat actor used a limited function within the customer-support portal which allows authenticated DigiCert support analysts to access customer accounts from the customer's perspective to facilitate support tasks. The threat actor was able to use this function to access initialization codes for orders that were approved but pending delivery for EV Code Signing certificate orders across a finite set of customer accounts."
"Possession of the initialization code, combined with an approved order, is functionally sufficient to generate and retrieve the corresponding certificate."
The full report can be found here and explains the incident in great detail: bugzilla.mozilla.org/show_bug.cgi?i…
The report mentions "Where we got lucky: A community member involved in security research reported the evolving pattern of misused certificates and engaged in dialogue with our support team. Without that report, the undetected compromise of ENDPOINT2 and the associated mis-issuance might have remained undiscovered for a longer period."
Special thanks goes to the regular contributors to the Cert Graveyard; @g0njxa , @malwrhunterteam , and others.
Also special thanks to DigiCert: this report has a high level of transparency, which is warranted, and also well executed.
Squiblydoo@SquiblydooBlog
What do Lenovo, Kingston, Shuttle Inc, and Palit Microsystems have in common? EV Certificates from these companies were issued and used by a Chinese crime group, #GoldenEyeDog (#APT-Q-27)! Thanks @malwrhunterteam and @g0njxa for your contributions 1/7
English
Argha 🏏 📚 💻 đã retweet
Argha 🏏 📚 💻 đã retweet

Based on intelligence reports a man was arrested at Bengaluru airport bringing in a large number of USA banks debit cards .
Six locations in various states were raided ad searched by ED. 25 more foreign debit cards ,40 lakh cash and documents were seized .
It is seen that from 25 Nov till date Rs 95 crores crores have been drawn from widely spread ATM in different states and money distributed mainly to Bastar ad other areas in Chattisgargh mainly to fuel extremism and religious conversions .
The Timothy Initiative ( TTI ) .
Investigation is on .
English

Austin launched StopICE in February 2025, one of a constellation of digital tools that emerged in response to federal agents terrorizing communities.
🔗 motherjones.com/politics/2026/…
English

Mark Zuckerberg has a dystopian vision for a surveillance society. Here’s how we can fight back. - ACLU of Massachusetts #SurveillanceCapitalism #Privacy
🔗 aclum.org/publications/m…
English
Argha 🏏 📚 💻 đã retweet

@theintercept archived:
archive.is/2026.04.26-181…
additional resources:
mk-ultra
cia.gov/readingroom/se…
artichoke
cia.gov/readingroom/se…
bluebird
cia.gov/readingroom/se…
English

Remember the cold war CIA program MK-ULTRA?
Recently declassified memos reveal proof & further plans for interrogation by teams trained to utilize the polygraph, various drugs, and hypnotism “for personality control purposes.”
A must read ✍️ 🔗 interc.pt/3OI01Lw
English
Argha 🏏 📚 💻 đã retweet

Cyber defence at its peak 🛡️
Organised by @ccdcoe, the world’s largest live-fire cyber defence exercise, Locked Shields 2026, brought together 41 nations to practise protecting critical infrastructure and military systems against real-time cyberattacks
🔗 ccdcoe.org/news/2026/lock…

English
Argha 🏏 📚 💻 đã retweet

🌍 #LockedShields, le plus grand exercice international de #cyberdéfense, a rassemblé plus de 4 000 spécialistes et 41 nations.
🥉 L'équipe franco-suédoise, composée notamment de cybercombattants du @ComcyberFR et agents de l'ANSSI, est arrivée 3ème.
🔗 cyber.gouv.fr/actualites/loc…

Français
Argha 🏏 📚 💻 đã retweet

#LockedShields2026 has concluded! This year’s exercise brought together more than 4,000 participants from 41 nations. Congratulations to all 16 Blue Teams! Read more: ccdcoe.org/news/2026/lock…




English
Argha 🏏 📚 💻 đã retweet
Argha 🏏 📚 💻 đã retweet

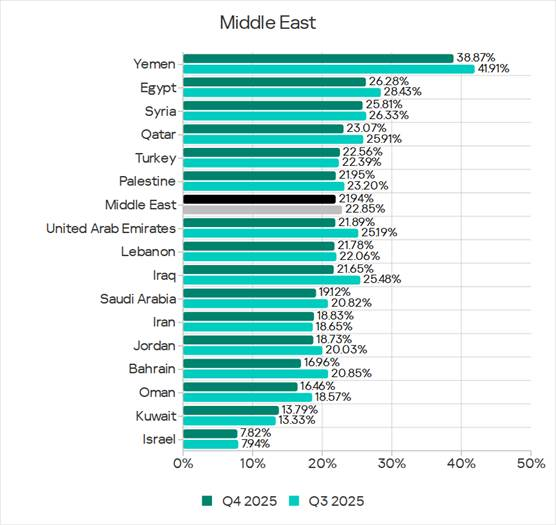
The threat landscape for industrial automation systems in the Middle East – Q4 2025: high risk of targeted attacks, network segmentation issues, and numerous espionage attacks. Yemen ranks second globally for the share of ICS computers attacked, while Israel is among the top-ten safest countries. More data and details: kas.pr/iy8b
English