Daniel Rabinovich
173 posts


Daniel Rabinovich
@blownapp
Founding GTM @ Mindfort (YC X25)






Congrats to @mindfort on their $3M seed! They're building autonomous AI agents that find, validate, and patch vulnerabilities in production software. Their agents run pentests on every CI/CD push, chain vulnerabilities into working proofs of exploit, and ship fixes as pull requests. mindfort.ai/blog/seed-anno…








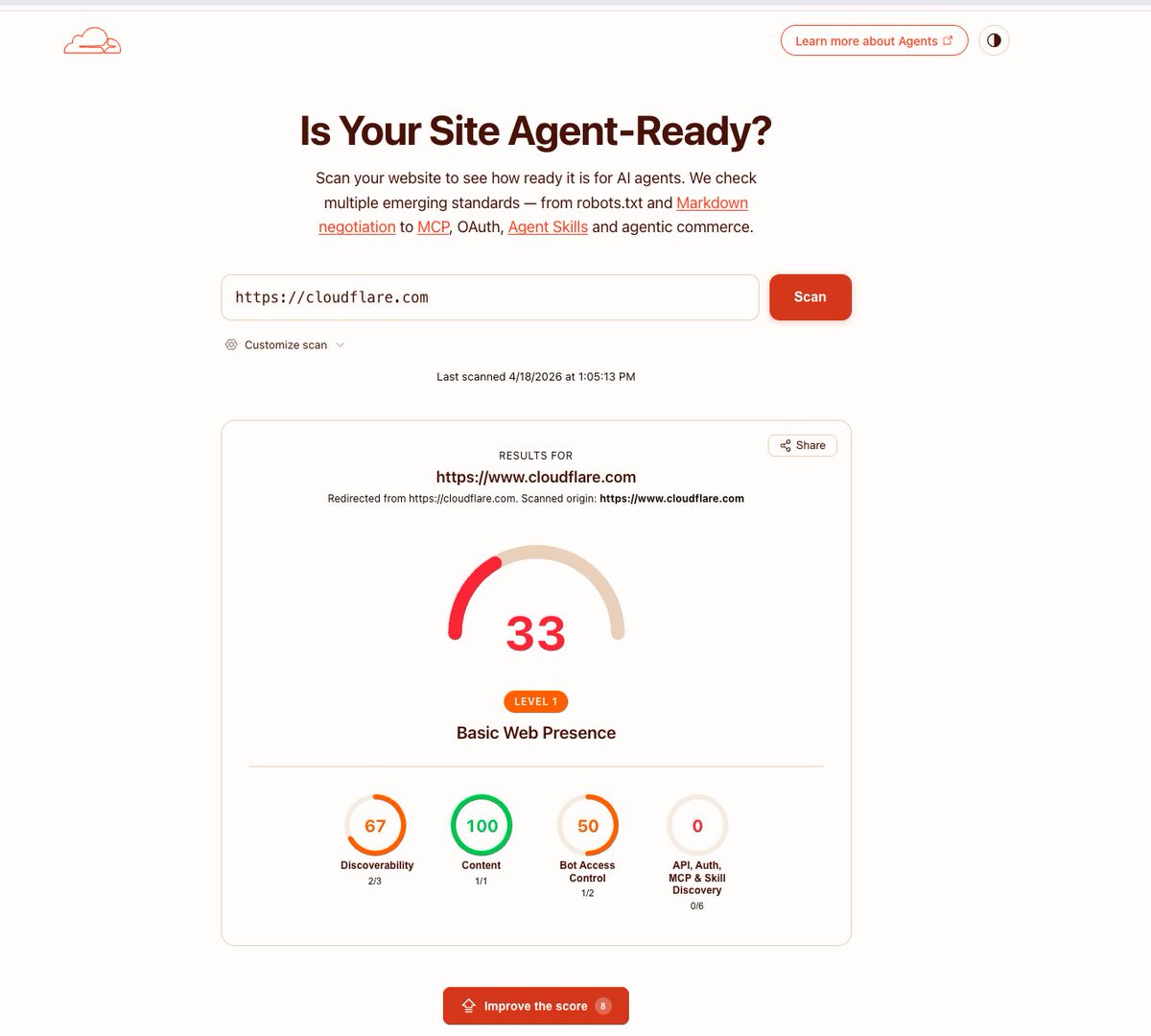
Lovable has a mass data breach affecting every project created before november 2025. I made a lovable account today and was able to access another users source code, database credentials, AI chat histories, and customer data are all readable by any free account. nvidia, microsoft, uber, and spotify employees all have accounts. the bug was reported 48 days ago. its not fixed. They marked it as duplicate and left it open.




We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: vercel.com/kb/bulletin/ve…