StackGraveYard
571 posts


StackGraveYard
@AiMarketsDaily
Development Tool Creation & Market Analysis






Security things from the last few days: - CopyFail (linux pwn'd) - CopyFail 2/Dirty Frag - 13 advisories in Next.js - Over 70 CVEs addressed in MacOS 26.5 - ~50 CVEs addressed in iOS 26.5 - YellowKey (Windows Bitlocker pwn'd entirely) - GreenPlasma (Windows privilege escalation) - CVE-2026-21510 and CVE-2026-21513 confirmed to be used by Russia for Windows RCE - CVE-2026-32202 separately confirmed to be used by Russia for sensitive document access - Mini-Shai Hulud (over 300 JS and Python packages compromised via GitHub Action cache poisoning) - Google confirms they have identified AI-powered exploitation of zero days in an unidentified "open-source, web-based system administration too" - Canvas (popular LMS used in most schools) pwn'd entirely - PAN-OS (palo alto networks) pwn'd with a 9.3 severity CVE-2026-0300 Are you scared yet?


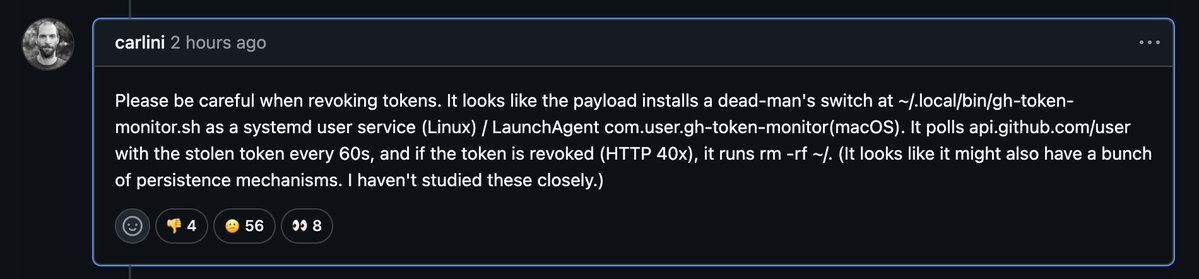


🚨 BREAKING: 84 TanStack npm packages were compromised in an ongoing Mini Shai-Hulud supply chain attack, adding suspected CI credential-stealing malware. Socket flagged every malicious version within six minutes of publication. This is a developing story.


TL;DR for open-source maintainers 🚫 NEVER use "pull_request_target" workflows 🚫 NEVER use shared caches in your publish pipeline Combining these 2 in particular is extremely dangerous I've repeated this countless times over the years, but another reminder is always useful


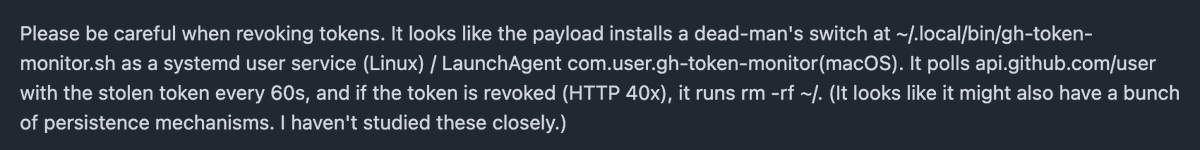
SECURITY ADVISORY — TanStack npm packages A supply-chain compromise affecting 42 @tanstack/* packages (84 versions total) was published to npm earlier today at approximately 19:20 and 19:26 UTC. Two malicious versions per package. Status: ACTIVE — packages are deprecated, npm security engaged, publish path being shut down. Severity: HIGH — payload exfiltrates AWS, GCP, Kubernetes, and Vault credentials, GitHub tokens, .npmrc contents, and SSH keys. If you installed any @tanstack/* package between 19:20 and 19:30 UTC today, treat the host as potentially compromised: • Rotate cloud, GitHub, and SSH credentials immediately • Audit cloud audit logs for the last several hours • Pin to a prior known-good version and reinstall from a clean lockfile Detection — the malicious manifest contains: "optionalDependencies": { "@tanstack/setup": "github:tanstack/router#79ac49ee..." } Any version with this entry is compromised. The payload is delivered via a git-resolved optionalDependency whose prepare script runs router_init.js (~2.3 MB, smuggled into each tarball at the package root). Unpublish is blocked by npm policy for most affected packages due to existing third-party dependents. All 84 versions are being deprecated with a SECURITY warning, and npm security has been engaged to pull tarballs at the registry level. Full technical breakdown, complete package and version list, and rolling status updates: github.com/TanStack/route… Credit to the security researcher for responsible disclosure.