DeFiHackAlerts
356 posts


DeFiHackAlerts
@DeFiHackAlerts
Know about DeFi protocol hacks first. FREE alert service providing actionable Alpha.


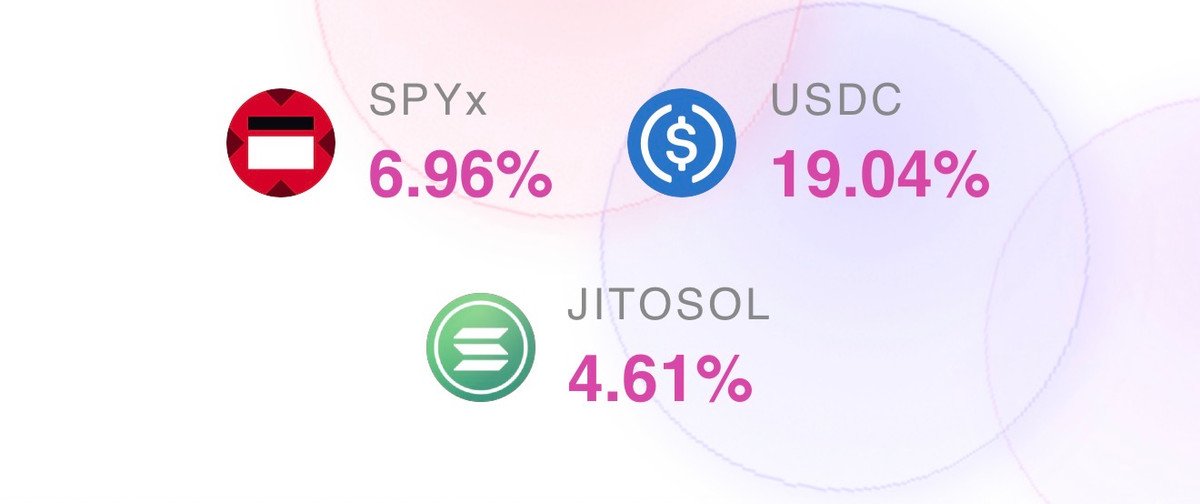
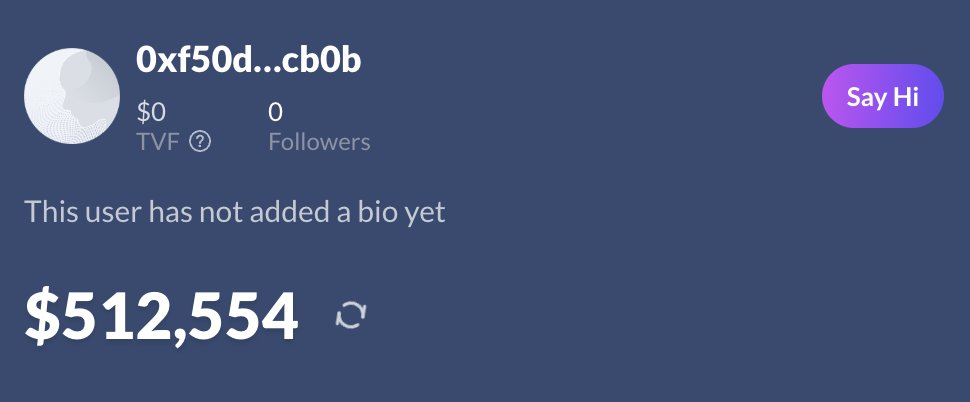
Defi gave me 6 figures But I'm tired of losing money So I stopped trusting CT and audited protocols myself. Here are the highest yields with low risk: - Multisigs - All audited - No liquidation risk (multiplying/looping)



10h ago @litecoin experienced a coordinated attack on the chain that resulted in 13 blocks reorg that took more than 3h to generate. During this time attackers were performing double spend attacks on multiple cross-chain swapping protocols. We are investigating the situation.


Ich möchte mich mit mehr deutschen connecten im Space. Wenn du deutsch sprichst kommentier einfach und ich folge dir brudi



Something is off on @worldlibertyfi market. Util. rates on USD1 and USDC reach 98.26% and 92.3% respectively. WLFI whales deposited 3B tokens of WLFI as collateral and borrowed USDC and USD1, depleting the pool and pushing the supply APR through the roof. While some think this is a good opportunity to lend, I'm doing the opposite and withdrawing while there's still room. Too many potential and uncontrollable risks: withdrawal stuck, liquidation cascades, bad debt in the worst case. Not gonna risk it. DYOR.







List of protocols exposed to @DriftProtocol and current status 👇 🔸 @reflectmoney - USDC+ is farming yield on Drift; mint and redemption of USDC+ has been frozen; funds are insured 🔸 @project0 - protocol paused; no new borrows can be made agains drift positions 🔸 @piggybank_fi - $106.4k/$4M of funds were deployed to Drift (~2.6%) 🔸 @ranger_finance - rUSD has exposure to Drift, but no statement from the team so far 🔸 @uselulo - Classic deposits may be affected according to the team 🔸 @DeFiCarrot - team confirmed no significant exposure to Drift for CRT yield (actually only $600) 🔸 @xplaceapp - uses Drift (besides Kamino) for yield on Savings, no statement from the team so far 🔸 @GetPyra - uses Drift for yield and credt; user funds withput open loans are moved away for security reasons 🔸 @TradeNeutral - no remaining NT Vaults should be affected 🔸 @elementaldefi - uses Drift for USDC Vaults, no statement from the team so far 🔸 @Loopscale - team confirmed no exposure to Drift 🔸 @synatraxyz - team confirmed no exposure to Drift