Sabitlenmiş Tweet
Felix Ehlers
11.6K posts


Felix Ehlers
@FelixEhlers
InfoSec Manager by day, DevSecOps and vibe coder by night. (Free|Hardened)BSD advocate. Lovely father. He/him. This is a private account. https://t.co/JPil9pxLCm
Hanover … 🇩🇪 … 🌍 Katılım Ekim 2009
1.5K Takip Edilen594 Takipçiler
Felix Ehlers retweetledi

❗️Security researchers used a low-cost consumer satellite dish to intercept satellite signals and found massive amounts of unencrypted traffic.
Revealing:
📡 Military and government comms including GPS data
📡 Credit card transactions
📡 Phone calls and texts from remote cell towers
📡 In-flight Wi-Fi activity

English
Felix Ehlers retweetledi

someone at ANTHROPIC just showed CLAUDE finding ZERO DAY vulnerabilities in a live conference demo
claude has found zero day in Ghost, 50,000 stars on github, never had a critical security vulnerability in its entire, history...
it found the blind SQL injection in 90 minutes, stole the admin api key, then did the exact, same thing to the linux kernel
English
Felix Ehlers retweetledi
Felix Ehlers retweetledi

🎗️ "Medium-Sized" LLM Burners Coming Soon! 🔥
This Could Make Local HyperToken Generation a Reality. ⚡️ NVIDIA’s worst nightmare? 😱
⚙️ Application-Specific Hardware
Taalas new PCIe ASIC board would burn the entire medium-sized Qwen 3.5-27B LLM straight into silicon 🤯 (already doing it with small models)
Taalos said medium models on ASIC would be available in their lab by Spring '26.
💭Imagine:
🚫 No more loading weights
🚀 ~10,000 Tokens Per Second locally (Llama 3.1 8B already @ 17,000 tps)
💻 Standard PC slot, ultra-low power (10x less) 🔋
🌍 100% offline with no cloud, no GPU farm
💰 Reddit unit cost rumor $300 to $400
🖥️ Imagine HyperToken generation on your desktop.
🤖 AI agents that think at light speed. ⚡️ Are you ready? 👀

English
Felix Ehlers retweetledi
Felix Ehlers retweetledi

Why did the US ban this number in 2001? It sounds insane, but 25 years ago, the Motion Picture Association of America was genuinely trying to delete this number from the internet.
You see, back in 1999, a teenager in Norway named Jon Lech Johansen wrote a piece of code called DeCSS.
It cracked CSS, the encryption on DVDs. Suddenly, anyone could copy a movie with the click of a button. It was a nightmare for the movie studios.
They went nuclear. They sued the hacker magazine 2600: The Hacker Quarterly.
They threatened Slashdot, and their lawyers fired out cease-and-desist letters to anyone hosting the code. They called it a digital burglary tool.
But the internet found a loophole.
A computer scientist named Phil Carmody realized that computer code is just binary ones and zeros.
And you can treat that string of binary as a single number. That way, you get a really, really big integer—which is the illegal code.
But Carmody knew that just finding any number wasn’t going to be enough, because the government could still ban a random number.
So he needed a number that science would be forced to protect. He needed a prime number.
You see, the University of Tennessee maintains a prestigious academic database called the Prime Pages.
It records the 5,000 largest known prime numbers. Carmody realized that if he could turn the illegal code into a record-breaking prime number, the university would have to publish it.
His first attempt was 1,401 digits long. It was prime, but too small.
It didn’t crack the top 5,000 list. It wasn’t mathematically interesting enough to save.
So, he hacked the math.
Use this formula:
K × 256^N + B
Now, K is the illegal code part. 256^N is the mathematical equivalent of adding useless zeros at the end—like making a book longer by adding blank pages. It doesn’t change the actual content inside.
So, he kept adding “blank pages,” shifting the number, until he hit a mathematical jackpot—a 1,959-digit monster.
This wasn’t just illegal code anymore. It became the 10th largest ECP prime number ever discovered at the time.
It was checkmate.
The number was immediately added to the university database. For the MPAA to ban the code now, they would have to order a university to delete a scientific record.
You can’t censor mathematics.

English
Felix Ehlers retweetledi
Felix Ehlers retweetledi

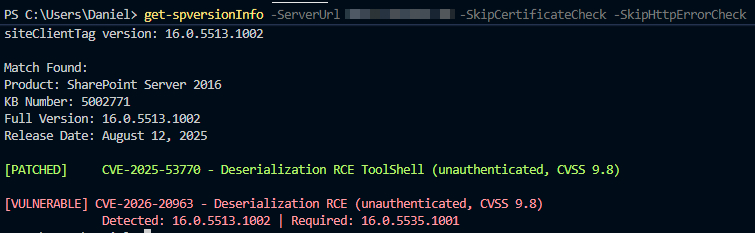
Whoopsi:
CVE-2026-20963 is now UNAUTHENTICATED!!!!
Patch ASAP.
msrc.microsoft.com/update-guide/v…
Updated the scanner:
github.com/LuemmelSec/Pen…
English
Felix Ehlers retweetledi

🚨‼️ We're in contact with the actor behind the Trivy and LiteLLM hack. They told us they are currently extorting several multi-billion-dollar companies from which they've exfiltrated data.
They've obtained 300 GB of compressed credentials and are working their way through them as we speak.
The LiteLLM compromise alone led to half a million stolen credentials, according to the threat actor.
Their message to the world: "TeamPCP is here to stay. Long live the supply chain."
They've sent us their new logo (see image) and also teamed up with several threat actors, including Xploiters and Vect.

English
Felix Ehlers retweetledi
Felix Ehlers retweetledi

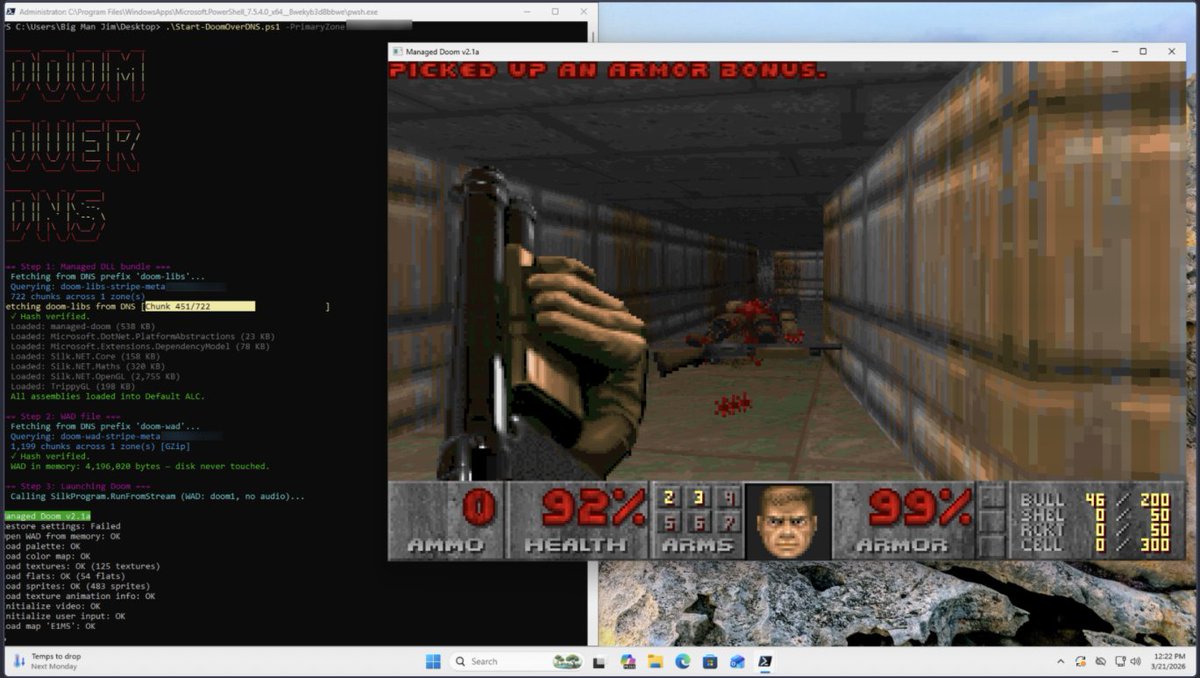
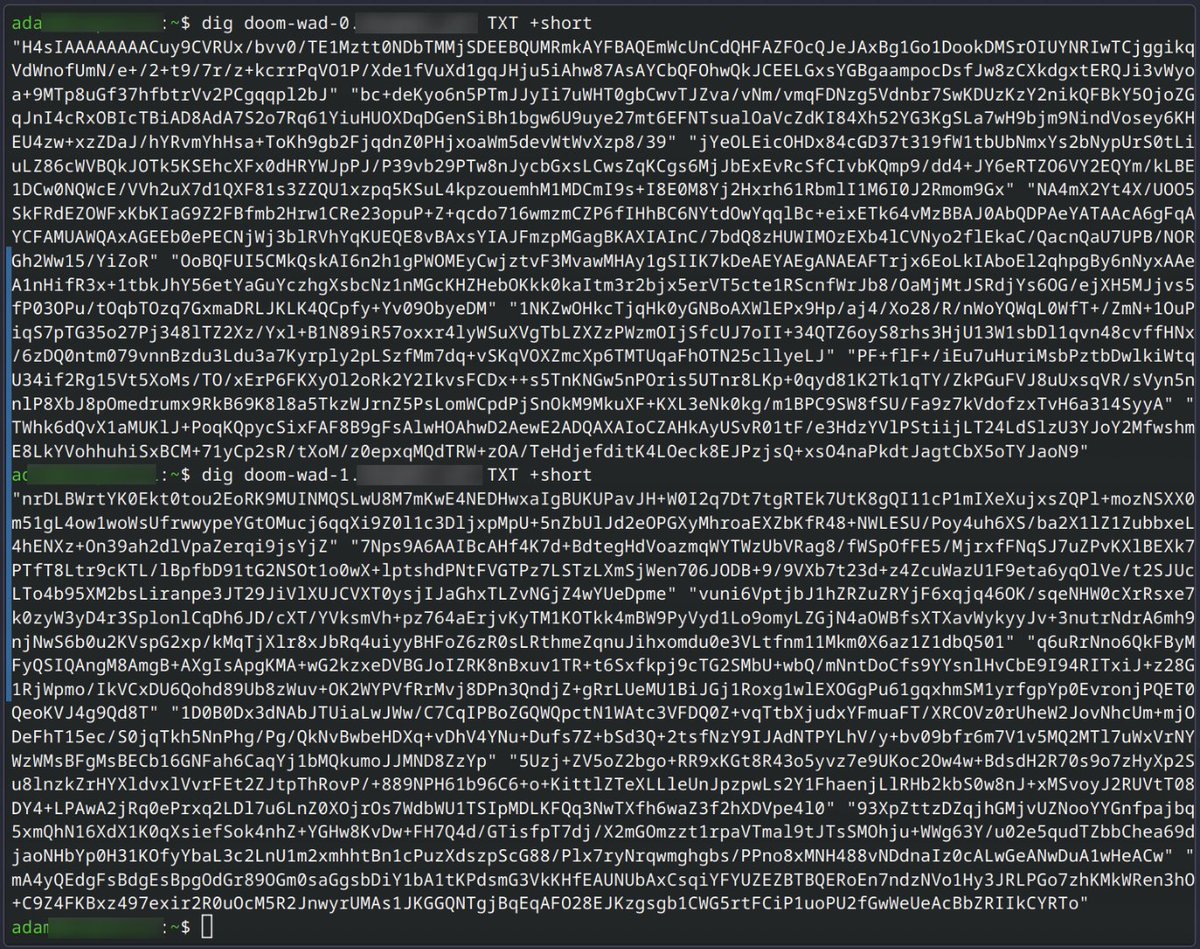
The article shows a proof-of-concept where DOOM is stored across ~2,000 DNS TXT records and executed directly from memory. A PowerShell loader reconstructs the binary via DNS queries, illustrating how DNS can act as a covert payload delivery system.
core-jmp.org/2026/03/can-it…
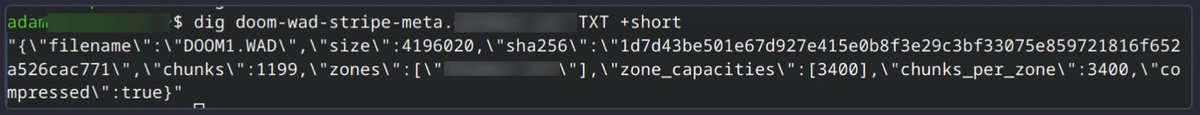

English
Felix Ehlers retweetledi
Felix Ehlers retweetledi
Felix Ehlers retweetledi

🛑 ALERT - Trivy, a popular open-source vulnerability scanner, was compromised after attackers hijacked 75 version tags in #GitHub Actions to deliver an infostealer.
It ran in CI pipelines, stealing creds and tokens, then exfiltrating data or staging it via stolen GitHub PATs.
🔗 Attack flow, impacted versions, fixes → thehackernews.com/2026/03/trivy-…

English
Felix Ehlers retweetledi

You can route internet traffic
through WhatsApp.
Open-source tool.
github.com/aleixrodriala/…
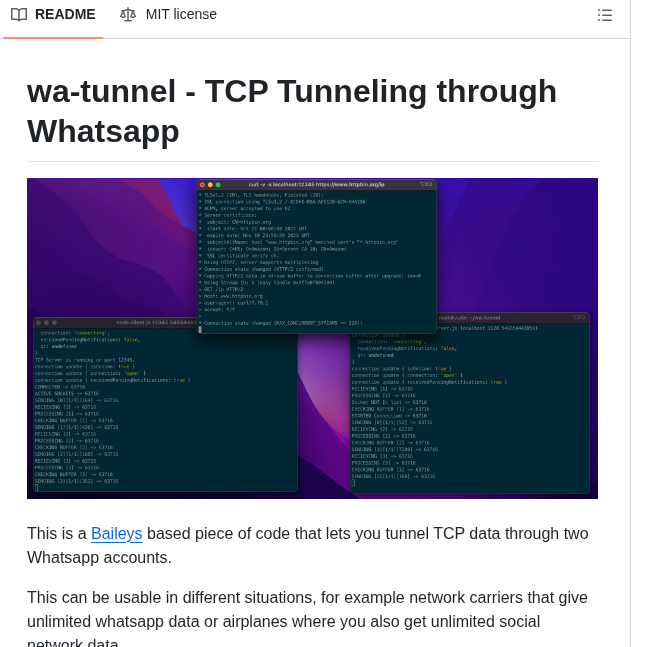
English
Felix Ehlers retweetledi
Felix Ehlers retweetledi

🚨‼️ CRITICAL: Ubiquiti UniFi Network Application vulnerabilities were just disclosed
CVE-2026-22557 CVSS 10.0
Remote path traversal vulnerability allowing an attacker to access and manipulate files, leading to account takeover. No authentication required.
CVE-2026-22558 — CVSS 7.7
Authenticated NoSQL Injection allowing privilege escalation.


English
Felix Ehlers retweetledi
This is actually insane.
Dude hard-coded a WebAssembly (WASM) interpreter into the weights of a transformer, losslessly.
In essence, a computer is running inside a LLM that can actually run computations, not infer or guess a calculation like most do today.
Christos Tzamos@ChristosTzamos
1/4 LLMs solve research grade math problems but struggle with basic calculations. We bridge this gap by turning them to computers. We built a computer INSIDE a transformer that can run programs for millions of steps in seconds solving even the hardest Sudokus with 100% accuracy
English
Felix Ehlers retweetledi
Felix Ehlers retweetledi