Griffith ✳️
4K posts



We're publishing an exclusive chapter from @scmallaby's brilliant new book about Demis Hassabis and DeepMind. This is the inside story of Project Mario. How DeepMind's co-founders spent 4 years trying every mechanism they could think of to put guardrails around AGI, only to watch each one fail, and conclude that the only safeguard was themselves. It reveals that Hassabis ran a secret hedge fund team inside DeepMind trying to beat Renaissance Technologies; Mustafa Suleyman assembled lawyers for a $5 billion walkaway plan; Reid Hoffman committed $1 billion of his personal fortune to back them; Google kept saying yes and no at the same time—and the endless negotiations left Hassabis so distracted that when the transformer paper dropped in 2017, he was less alert to its significance than he might have been. Meanwhile, OpenAI was fighting the mirror-image battle with Musk, Altman, and Sutskever tearing each other apart over the same question: who gets to control AGI? Musk proposed folding OpenAI into Tesla. When that failed, he stormed out. When OpenAI's nonprofit board finally tried to assert authority in 2023, it was crushed in days. Both camps arrived at the same unsettling conclusion, that governance structures don't hold. The best safeguard either side could come up with? Trust us. Read the chapter in the link below.





Bloomberg: Saudi Arabia’s crucial East-West pipeline that circumvents the Strait of Hormuz is pumping oil at its full capacity of 7 million barrels a day, according to a person familiar with the matter. bloomberg.com/news/articles/…


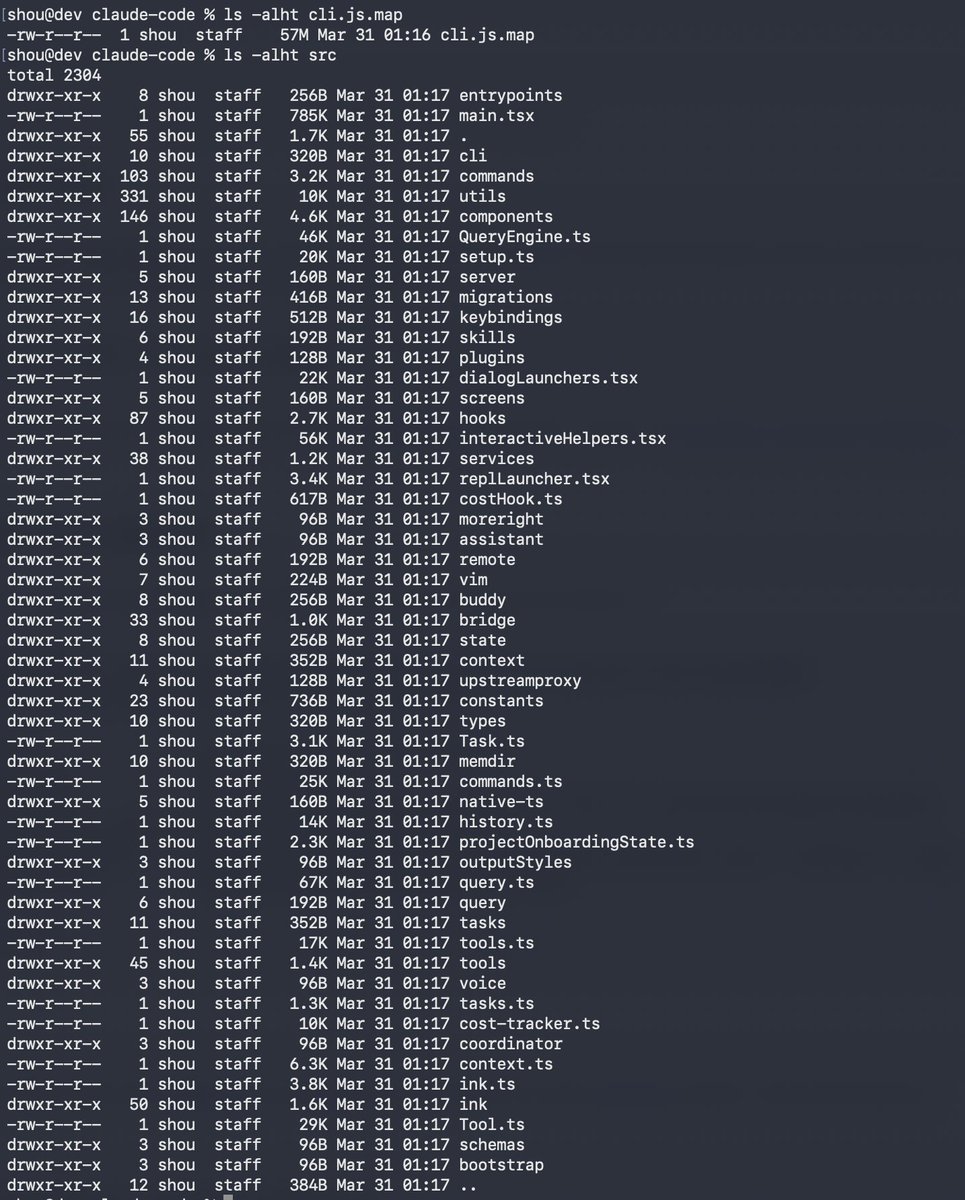
Software horror: litellm PyPI supply chain attack. Simple `pip install litellm` was enough to exfiltrate SSH keys, AWS/GCP/Azure creds, Kubernetes configs, git credentials, env vars (all your API keys), shell history, crypto wallets, SSL private keys, CI/CD secrets, database passwords. LiteLLM itself has 97 million downloads per month which is already terrible, but much worse, the contagion spreads to any project that depends on litellm. For example, if you did `pip install dspy` (which depended on litellm>=1.64.0), you'd also be pwnd. Same for any other large project that depended on litellm. Afaict the poisoned version was up for only less than ~1 hour. The attack had a bug which led to its discovery - Callum McMahon was using an MCP plugin inside Cursor that pulled in litellm as a transitive dependency. When litellm 1.82.8 installed, their machine ran out of RAM and crashed. So if the attacker didn't vibe code this attack it could have been undetected for many days or weeks. Supply chain attacks like this are basically the scariest thing imaginable in modern software. Every time you install any depedency you could be pulling in a poisoned package anywhere deep inside its entire depedency tree. This is especially risky with large projects that might have lots and lots of dependencies. The credentials that do get stolen in each attack can then be used to take over more accounts and compromise more packages. Classical software engineering would have you believe that dependencies are good (we're building pyramids from bricks), but imo this has to be re-evaluated, and it's why I've been so growingly averse to them, preferring to use LLMs to "yoink" functionality when it's simple enough and possible.

This negotiating strategy--agree or we punish you--loses a bit of its luster after three weeks of war. Iran has absorbed a great deal. Why give in now? Especially when there is evidence to suggest Trump may do so first.


To ensure the safety of students, KHDA confirms the continuation of distance learning across all private educational institutions in Dubai until Friday, April,3 2026. KHDA also emphasises that any institution seeking to resume on-site learning must submit a formal request outlining clear and detailed justifications. The final decision, issued by the Ministry of Education, will prioritise the safety of the educational community in Dubai.







