Sabitlenmiş Tweet
Tony Shannon
4K posts

Tony Shannon
@ShannonTony
Computing, Security, Lock-picking & Hackspaces. Tea fiend. He/Him https://t.co/jdyDxqdXF5
Nottingham, England Katılım Mart 2010
914 Takip Edilen218 Takipçiler
@CrossCountryUK my daughter is booked on the 08:20 Aberdeen ton Plymouth direct, which is shown as cancelled due to a shortage of drivers. I need to advise her on what trains to travel on - can you advise?
English
Tony Shannon retweetledi

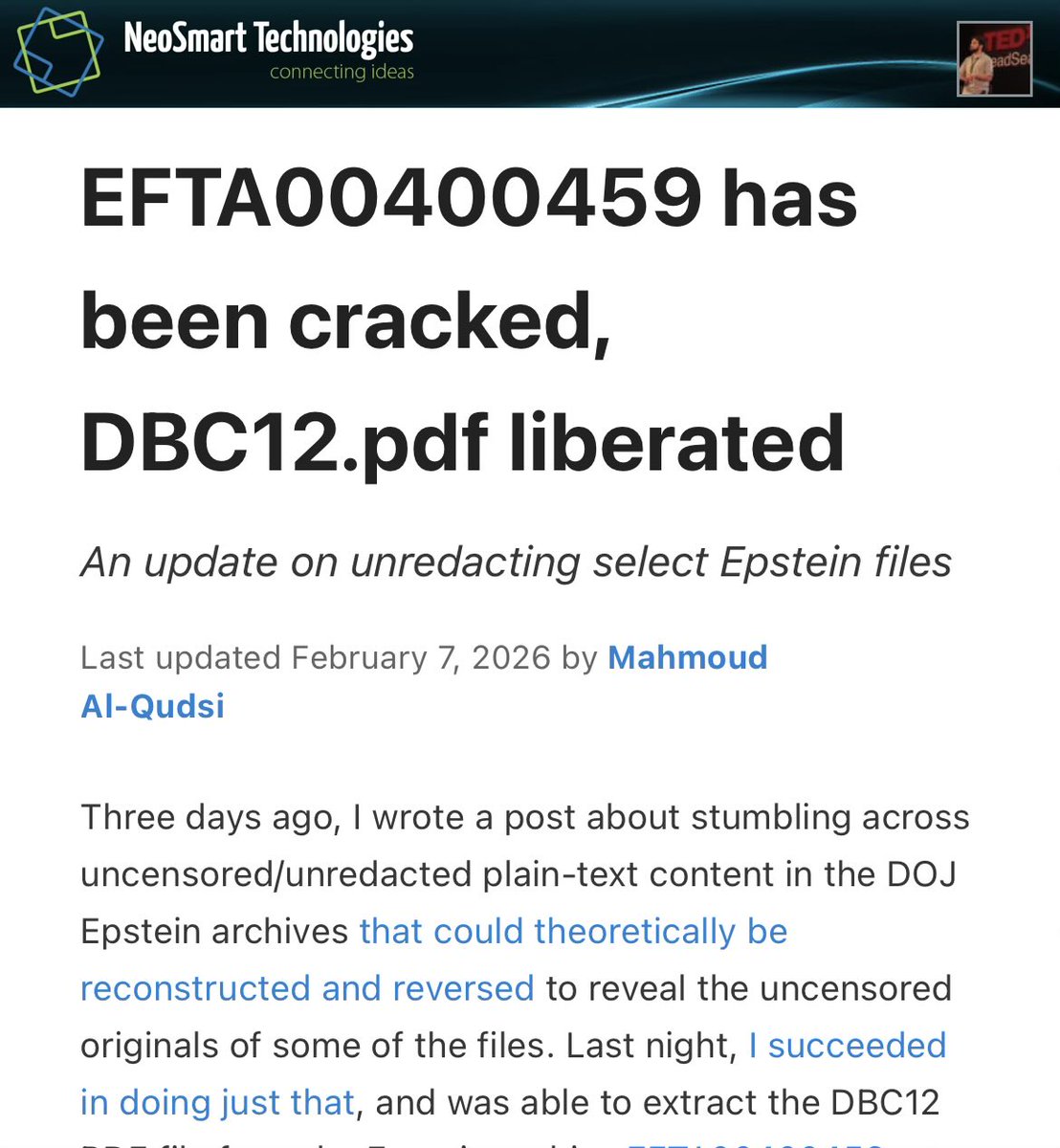
The mystery of Satoshi Nakamoto, the pseudonymous inventor of Bitcoin, has remained unsolved for 17 years. Not anymore. Read my 18-month investigation to find out who Satoshi really is. nytimes.com/2026/04/08/bus…
English
Tony Shannon retweetledi
Tony Shannon retweetledi

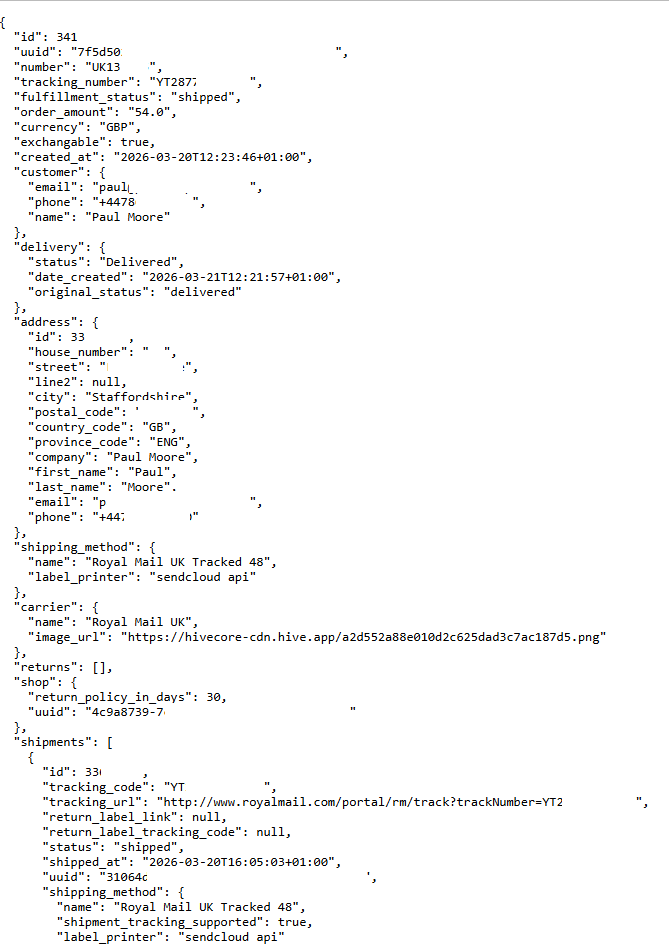
No response whatsoever from @Holysquad_uk regarding a critical #security issue (all customer data left exposed), so I've now escalated it to @ICOnews
I would advise against promoting them @autoalex - your data was trivially easy to find.
English
Tony Shannon retweetledi

I've been telling everyone, for years, to uninstall #police #cyberalarm
If you're still running it in 2026 (the Pervade version), don't take my advice... read this, mindful that the UK gov't has just partnered with Anthropic and deployed Claude AI for public services - so I assume they trust its judgement.
This is what #securityResearchers have to put up with.
English
Tony Shannon retweetledi

The LiteLLM supply chain attack is big shenanigans. I have to explain the whole thingie though so you can get the full context of the shenanigans. TeamPCP (the people who probably did it) is unironically swinging a big ass fuck off baseball bat, they're swinging for the moon.
tl;dr see picture of cat as summary
I also want to preface this with I DID NOT PERFORM THIS ANALYSIS. I almost never do open-source solutions malware stuff and this is also more in the line of work with DFIR (Digital Forensics and Incident Response). This summary comes from various peers and colleagues of mine who have been discussing TeamPCP the past couple of days.
DFIR nerds I sourced:
- @ramimacisabird
- @InsiderPhD
Non DFIR nerds I sourced:
- @IceSolst
- @IntCyberDigest
Yeah, so pretty much this group of nerds named TeamPCP bamboozled an open-source security product called Trivy. TeamPCP sent a pull request on GitHub but did it with "pull_request_target".
Normally a pull request isn't a big deal. Nerds do it all the time. "pull_request_target" though is designed to copy secrets, tokens, etc. pull_request_target is a legit thing. People do it all the time. It should only be performed by people you trust. TeamPCP impersonated a legitimate GitHub contributor.
Trivy was caught slippin'. When TeamPCP did pull_request_target they stole access tokens to a place called Aqua Security.
Aqua Security was like, "lol gosh dang it" and did what you were supposed to do. They rotated access tokens and passwords and stuff. However, Aqua made an oopsie and forgot to rotate the stuff for one of their automation bots.
Once TeamPCP had access they injected malicious code which steal environment variables, SSH keys, cloud credentials, cryptotokens, etc into three things.
- Trivy
- Trivy GitHub actions
- Trivy Docker stuff
As is tradition, once TeamPCP put malware into Trivy stuff, anyone who did anything with Trivy was given malware. TeamPCP got a metric poop ton of stolen data and began using it to move to NPM projects. The projects they infected next was infected with a malware people named "CanisterWorm".
In extreme summary, CanisterWorm placed stuff in package.json from the infected NPM project. Every new infected NPM project would download malware to the machine that (unsurprisingly) stole your data.
TeamPCP seems to have been inspired by the North Korean government, or ALPHV ransomware group, because instead of stealing data to their server they store it on the blockchain ... making it virtually impossible to takedown.
LiteLLM takes place somewhere between Trivy and CanisterWorm. As of this writing the exact way TeamPCP got access to LiteLLM is unknown, however it's heavily speculated it is from Trivy. TeamPCP also stated very bluntly they got access from Trivy but ... they could also be lying. This may come as a surprise, but sometimes criminals lie to cover their tracks.
LiteLLM infection though was a few more degrees amplified than the previous stuff. LiteLLM infection also attempts lateral movement by automating Kubernetes stuff. LiteLLM infection also steals a ton more data than previous stuff. Here is the big ass list of stuff it steals:
- SSH keys
- AWS credentials and configurations
- GCP credentials and configurations
- Azure environment variables
- Kubernetes credentials and configurations
- Environment configurations
- Shell History
- Git credentials and configurations
- Docker credentials and configurations
- Database instances
- IaC / CI/DI
- SSL private keys
- Solana keys
- Crypto wallets
- VPN credentials and configurations
- Hashicorp vault (?)
- NPM configurations
- SMTP credentials
TeamPCP is unironically putting in big moves. What makes them unusual is how profoundly aggressive they are. It isn't uncommon for Threat Actors to attempt things like this, but TeamPCP is doing something more akin to "smash and grab" rather than "stay silent and watch".

English
Tony Shannon retweetledi

Spain just fined the age verification company governments are forcing you to use €950,000 for GDPR violations. Biometric data retained too long, geolocation data kept for five years, fraud documents repurposed to train their AI. The infrastructure being built to "protect children" is already failing basic legal privacy requirements...
Reclaim The Net@ReclaimTheNetHQ
Spain Fines ID Tool Yoti for Privacy Violations in Biometric ID App reclaimthenet.org/yoti-gdpr-fine…
English
Tony Shannon retweetledi
Tony Shannon retweetledi
Tony Shannon retweetledi
@HelpAliExpress Thanks replied via DM - not an issue with someone sending me messages and me receiving notifications, I am receiving notifications for messages that do not exist. Have sent screenshots, and email header - please escalate to your IT team - not an account notification setting
English

@ShannonTony We apologize for any inconvenience this may cause. we have received your feedback and already contacted you via DM. Thanks for reaching out.
English
@HelpAliExpress am getting 20-30 broken email notifications from your site every day. Have tried to report via website, your help function, and via DM with no success. How can I report this to you to fix?
English
@Specsavers - after nearly 2 years of return-to-sender mail you are incorrectly addressing to the previous occupants, have to ask if your returns department need to go to @VisionExpress
If I DM you a photo of the misaddressed mail, can you sort this?
English
Tony Shannon retweetledi

This basically means: by the time you install the patch, there’s an increasing chance the system is already compromised
linkedin.com/posts/brentmui…

English
Tony Shannon retweetledi
Tony Shannon retweetledi

.@Newsweek published an article today about a Threat Group trying to extort Google. The extortion group is demanding Google terminate some of their Threat Intelligence researchers. Obviously Google won't do this, but this is a calculated decision by the Threat Group to apply social and/or political pressure on the Threat Intelligence researchers.
Newsweek, for reasons I cannot possibly fathom, decided to name drop the individual persons the Threat Group is demanding be terminated. These are not celebrities, these are not famous people, these are not politicians or socialites. They listed, in no exaggeration, regular Threat Intelligence employees.
I've NEVER seen ANY media outlet do that, EVER.
... Is Newsweek actively aiding and abetting Cyber Terrorists? Are they receiving kickbacks? Why would anyone, in their right mind, decide to air out to (potentially) millions of people, regular people who are being subjected to an intimidation campaign?
English
@UK_Daniel_Card The Conversation - one of Gene Hackmans finest, can be paired with Enemy of the State, which is… one of Gene Hackmans films.
English
Tony Shannon retweetledi

I guess I should update my LinkedIn profile now or something that the secret is out ;) (it's not a secret)
Very happy to continue to work alongside friends to help! 🫡🇬🇧🛡️
#UK #Gov #Cyber #Security #GCAB #DefendAsOne
gov.uk/government/new…
English
Tony Shannon retweetledi
What the actual fuck?
How can we tolerate this?
Declassified UK@declassifiedUK
❗️BREAKING — The UK Ministry of Defence admits it is “currently training” Israeli military personnel in Britain. The Labour government has until now refused to answer questions about this, which we covered last year. 👉 declassifieduk.org/amid-lebanon-i…
English
Tony Shannon retweetledi