Emrakul
250 posts

Emrakul
@TheEmrakul
Tell me your password and I'll tell you who you are.
0.0.0.0/0 Katılım Temmuz 2020
1.5K Takip Edilen94 Takipçiler

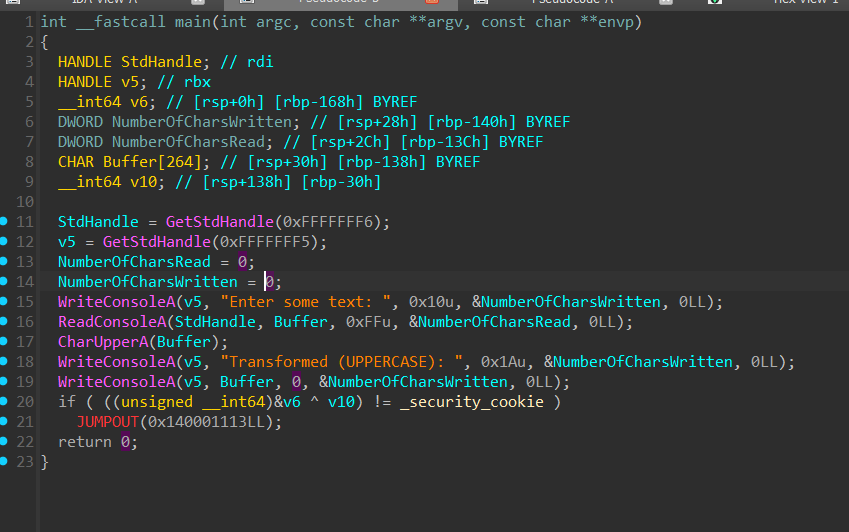
Static Devirtualization of Themida/CodeVirtualizer. The techniques in this article apply to pretty much every virtual machine obfuscator with minor modifications.
back.engineering/blog/09/05/202…
Original Program & Devirtualized Output
github.com/backengineerin…

English

Someone tagged me on this, some DM'd me.
I own about 30TB of malware.
For starters, I wish that file was 700TB+, but it's not. I'm not a Discord expert, but I know they enforce data size limitations even when you pay for their Discord Mega Ultra Pro which is like $9.99/month. I think the maximum file size allowed on Discord is like 10GB or something.
The internet as a whole generates probably 2TB - 6TB of malware a day (if I had to guesstimate). Most of these are not unique, they're small configuration changes, hash busted, or mutated.
The last publicly available figure I saw from VirusTotal was they receive 150,000+ user submitted malwares a day that are unique to them (different SHA256).
If my memory serves me correctly, VirusTotal is carrying 10PB (10,000 Terabytes) of malware since 2004-ish. However, VirusTotal relies on user submissions and VirusTotal only performs static analysis, it does not do payload extraction for secondary staging.
If VirusTotal began emulating all malwares they had, it would probably balloon to something like an EB (Exabyte, 1,000,000 Terabytes).
VirusTotal does not do dynamic extraction of payloads because Google executives would go to Bernardos home in Spain and beat him to death with the server infrastructure bill
angel⚔️🐾@angelinBmajor
@divydend 725TB, bros got every piece of malware ever made in there 😭
English

Built a username search tool that actually works - scans 800+ platforms, pulls real profile data (bio, followers, avatars) and skips the false positives most tools are drowning in. Free & open source.
github.com/skuggrev/kestr…
#OSINT #InfoSec #Recon #ThreatIntel #SOCMINT
English

Just dropped Harrier, a web-based Telegram scraping & intelligence tool. Scrape channels/groups, look up user profiles, get keyword alerts to Discord/Slack, and export everything as CSV, JSON or ZIP. Built with Python + React. 🦅
github.com/skuggrev/harri…
#OSINT #Telegram
English

@DarkWebInformer Just wait. All the ransomware guys can make a whip round and let this excellent messaging app survive
English

@PlaKeNn @IntCyberDigest He's probably allude at the screens that show a Windows XP application.
English

@DanielSMatthews @IntCyberDigest lol what emotionality? I called you for what you are.
Also please sir, enlighten us with your knowledge. Put forth the “truth” that we cannot see. Show me the 20 yo photos instead of saying asinine things like “you got fooled by that” without backing up the statement.
English

@secharvesterx @skocherhan any idea where to also get the actual files? mine should be buried in one of many hard drives and i miss ARTeam and Lena tutorials, when this kind of knowledge was for a selected elite only.
English

[Archive] Complete Directory Tree (3.2GB) of a Legacy Reverse Engineering Collection (2002-2012). Features ARTeam, SnD, Lena151 & rare German scene docs.
rentry.org/pgz2mt85

English

@nicolodev @REverseConf Great talk Nicolò! Missed the opportunity to talk to you but there will be other chances maybe
English

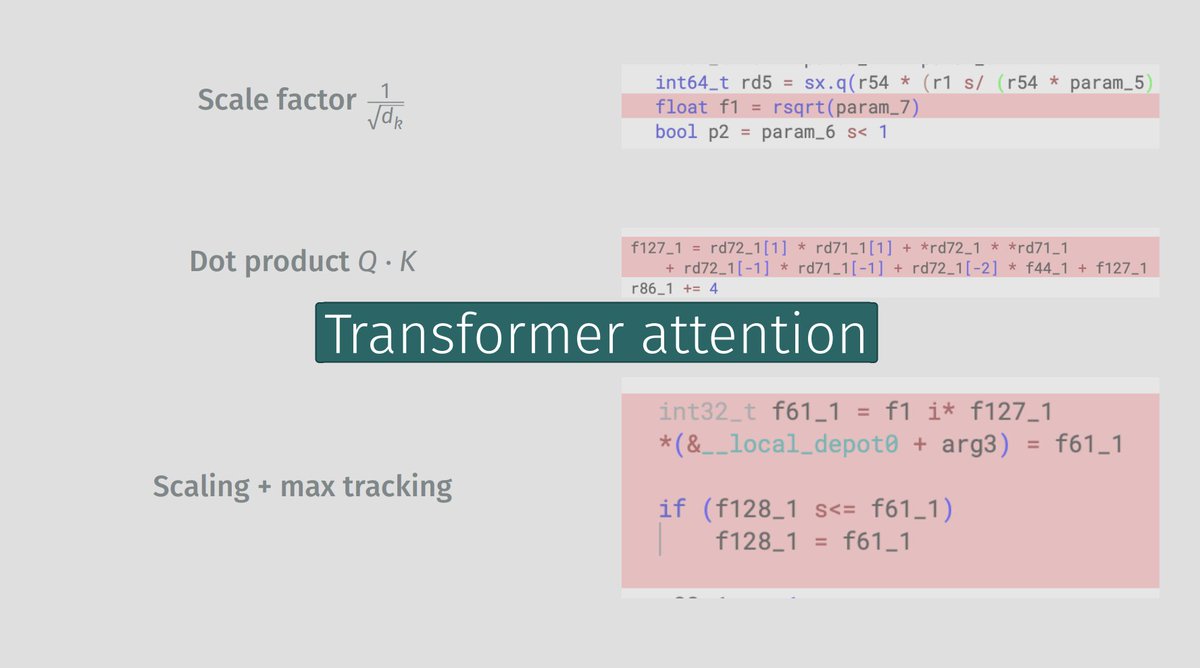
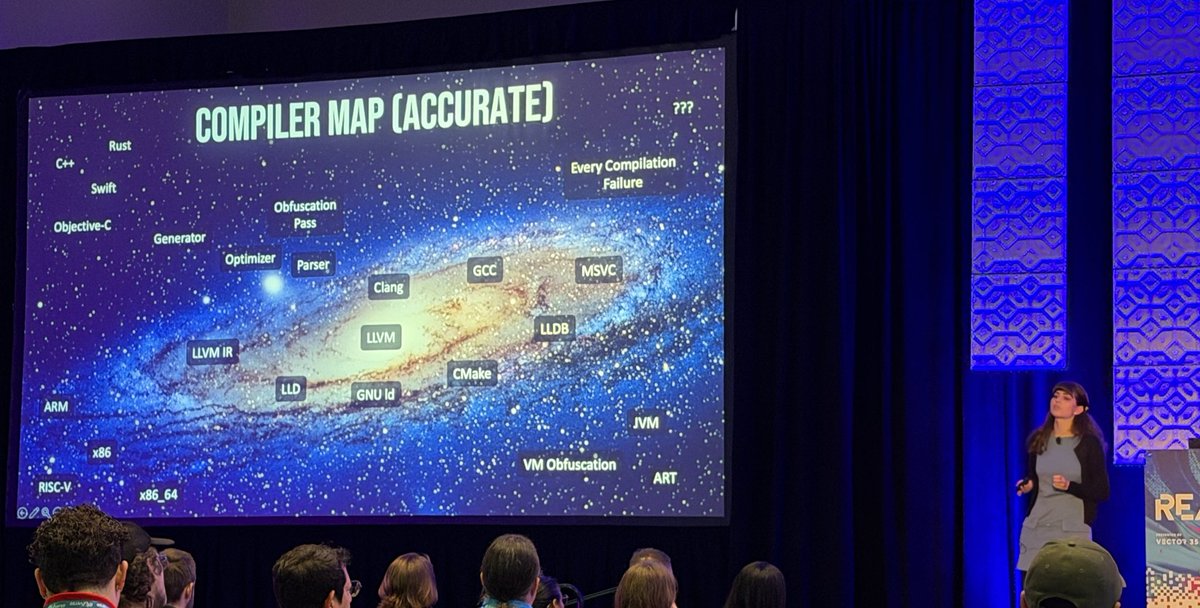
The slides from my @REverseConf talk, "Challenges in Decompilation and Reverse Engineering of CUDA-based Kernels", are now online!
Slides: nicolo.dev/files/pdf/reve…
Plugin: github.com/seekbytes/ptxN…
English

@lauriewired @juanandres_gs I was there and it was an amazing talk. Everything explained with wonderful clarity.
Have you thought to give training classes on that?
English

Apart from being an amazing RE talk, I’ve never seen someone make better use of a 1 hour slot. Hats off to @lauriewired.
English

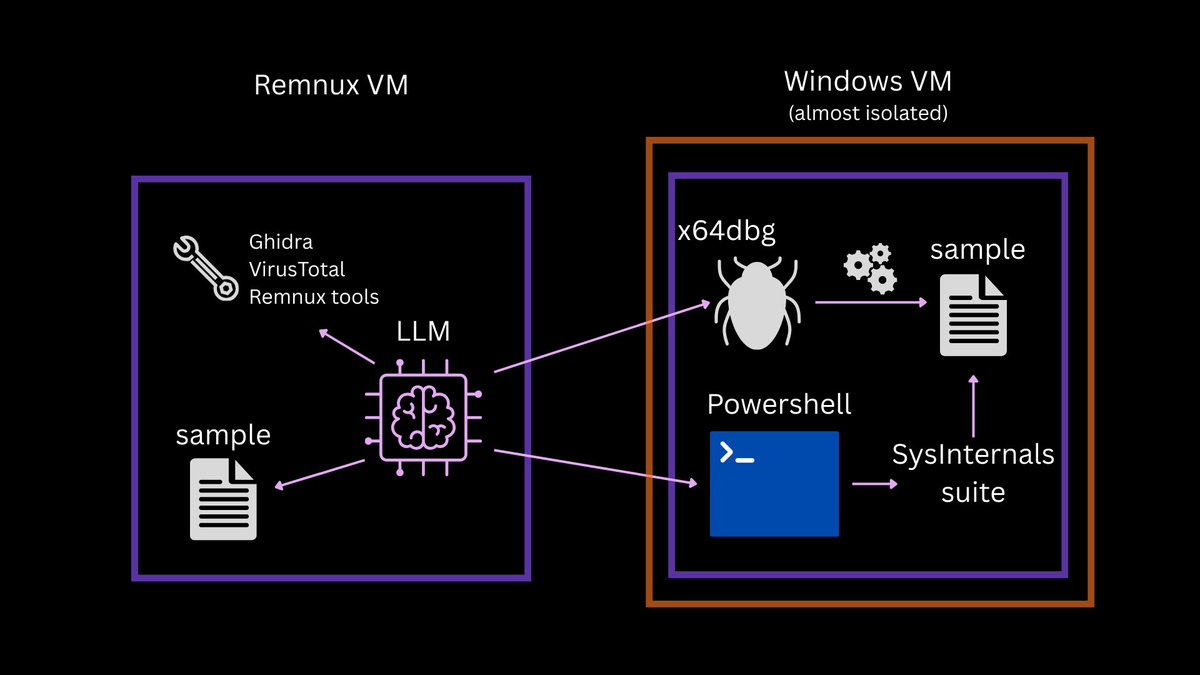
@mrexodia @struppigel Duncan, could it be possible to have the MCP running on the host while debugging a sample in a guest VM, maybe using network pipes like we use to do with remote IDA debuggers?
That would be incredibly useful.
English

@struppigel FYI, x64dbg recommends x64.ooo/posts/2026-02-…
English

New blog: Using LLMs the right way for malware analysis
💡Tips for building an autonomous AI analysis lab on a 12 yo laptop and getting stuff done faster without loss of accuracy.
blog.gdatasoftware.com/2026/03/38381-…
English

@UK_Daniel_Card @RussianPanda9xx and they still allucinate more than a human after debugging and tracing the same binary for hours.
After analyzing a function three times I get a clearer picture of its flow.
An LLM just allucinates three times more.
It helped figuring out crypto algos faster than me tho.
English

@RussianPanda9xx ^^^ this , they are a tool not a replacement for h00mans!
English

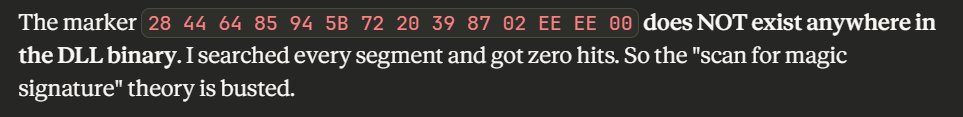
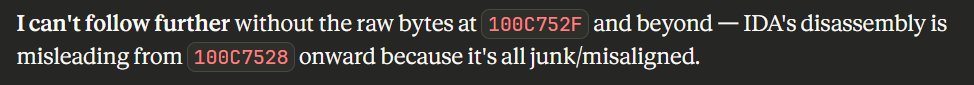
This is another showcase of why LLMs still need a human, and I don't see that changing any time soon. I'm still using a debugger, slamming my fingers on F7 and F8 to trace through functions. Calling malware RE "no longer a human problem" is ridiculous. Here's a real example: I gave an LLM a DLL to analyze and it confidently claimed a magic signature marker doesn't exist anywhere in the binary after telling me there was a magic marker involved. It also gave up at a certain offset saying it "can't follow further" because of all the CFF and opaque predicates crap. This could be solved in under 10 minutes with a human debugging instead of DDoS'ing your Claude with prompts.
English

I have five vouchers to NVIDIA's "Exploring Adversarial Machine Learning" course. This is a g1v3aw@y.
Does anyone want a free voucher?
(I have to avoid certain words or else the bots and weirdos appear in comment section)
learn.nvidia.com/courses/course…
English

Whoever the fck is disrupting the Berlin airport is about to regret if my plane is delayed. RussianPanda is coming to town
bbc.com/news/articles/…
English

@ShadowOpCode @JAMESWT_WT @AndreaDraghetti @guelfoweb @1ZRR4H @jamieantisocial @PGRotondo @skocherhan @BruteBee excellent. + using PEStudio
English

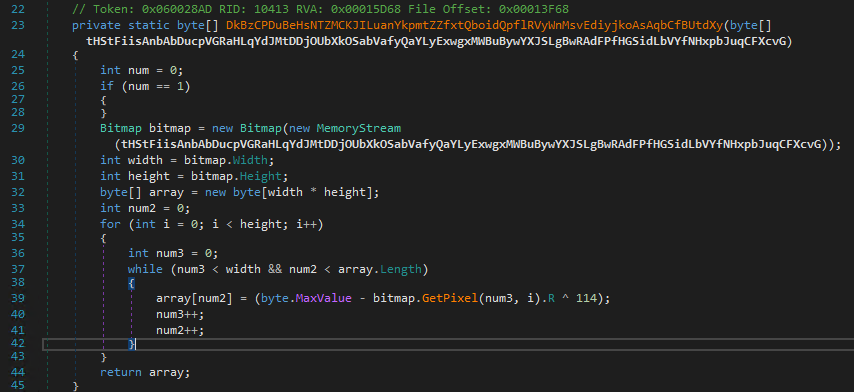
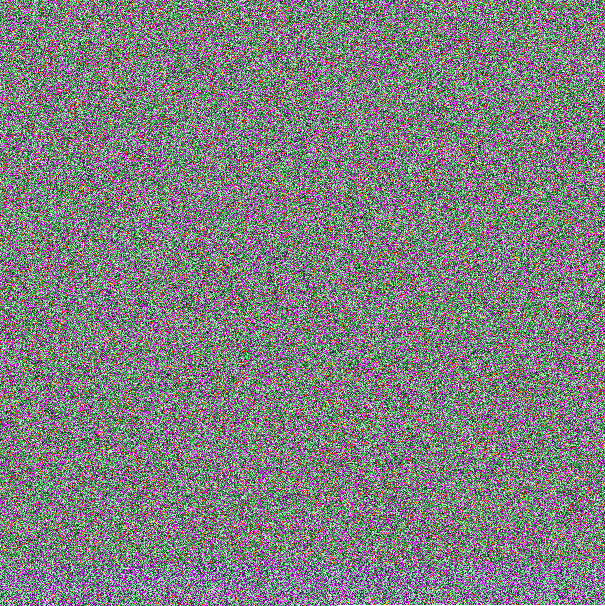
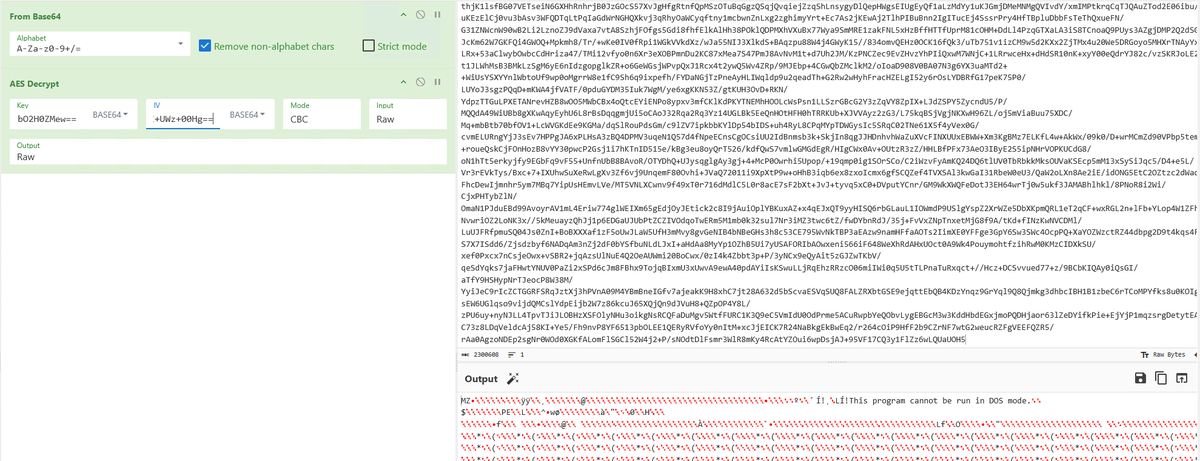
🧵New: "From Pixels to Payloads" — We reverse-engineered a multi-stage .NET loader hiding Lumma Stealer in BMPs via stego trick: (255-R)^0x72.
Donut Loader → C# Injector → Lumma in memory.
🧠👇
github.com/ShadowOpCode/S…
#LummaStealer #Infosec #MalwareAnalysis #ThreatIntelligence

English

It's been a while since we shared any updated Telegram Channel collection information with the community. We have exported over 6,600 unique rows sorted by mention count of Telegram Channel names from our collection platform <1y and are willing to share via DM for anyone who this may be helpful for. Thank you! #threatintel #intelsharing
English